Project Part III Double Deuce Jibran Ilyas Frank
Project Part III Double Deuce Jibran Ilyas, Frank La. Sota, Paul Lowder, Juan Mendez 1
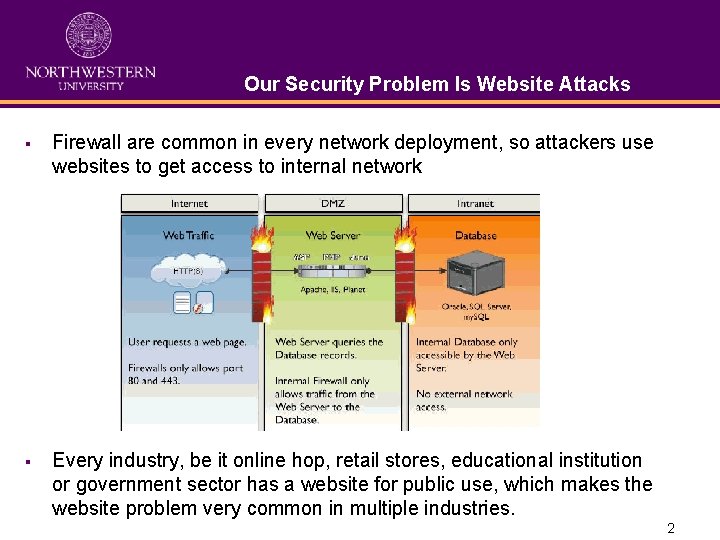
Our Security Problem Is Website Attacks § Firewall are common in every network deployment, so attackers use websites to get access to internal network § Every industry, be it online hop, retail stores, educational institution or government sector has a website for public use, which makes the website problem very common in multiple industries. 2
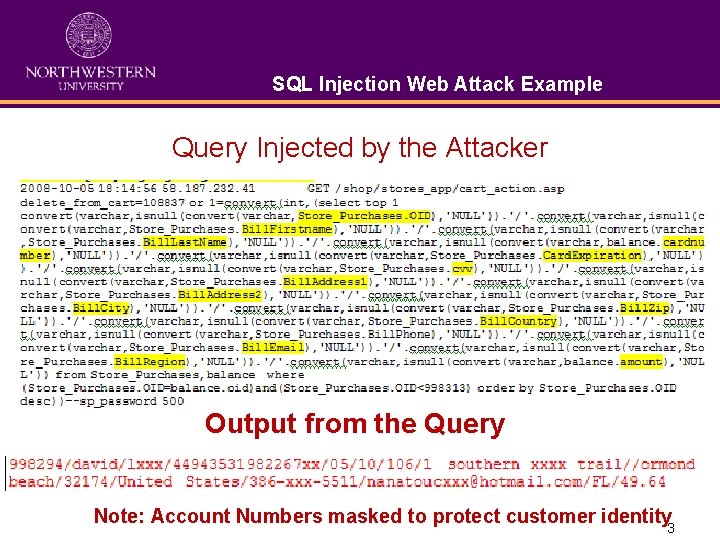
SQL Injection Web Attack Example Query Injected by the Attacker Output from the Query Note: Account Numbers masked to protect customer identity 3
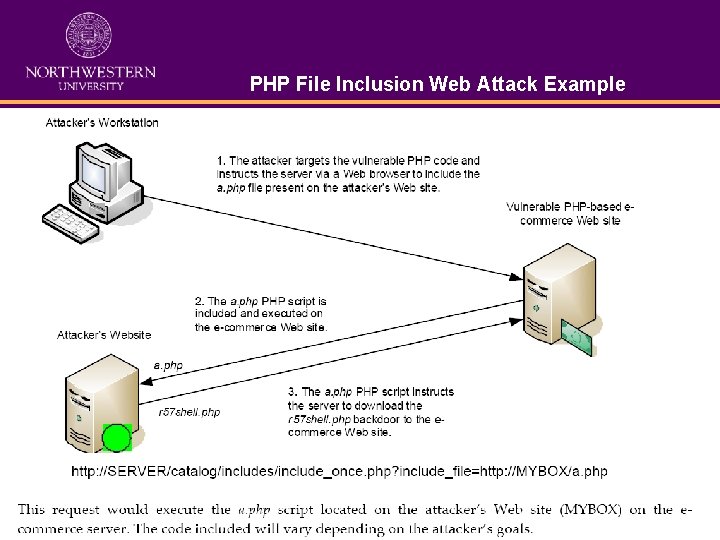
PHP File Inclusion Web Attack Example 4
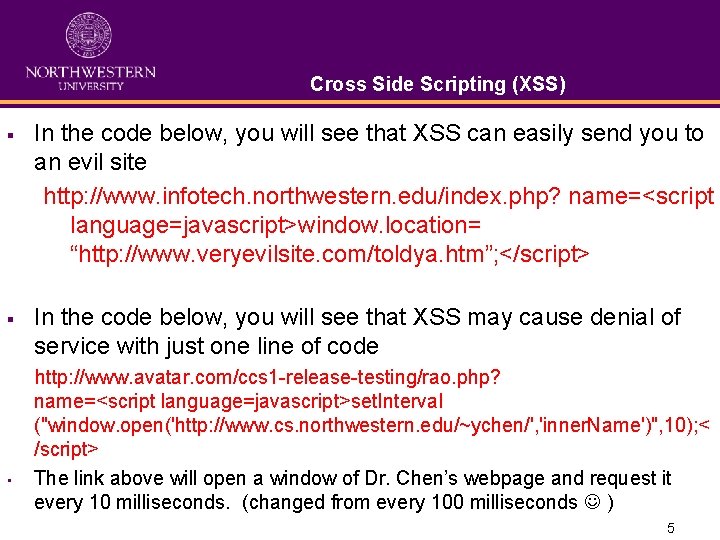
Cross Side Scripting (XSS) § In the code below, you will see that XSS can easily send you to an evil site http: //www. infotech. northwestern. edu/index. php? name=<script language=javascript>window. location= “http: //www. veryevilsite. com/toldya. htm”; </script> § In the code below, you will see that XSS may cause denial of service with just one line of code • http: //www. avatar. com/ccs 1 -release-testing/rao. php? name=<script language=javascript>set. Interval ("window. open('http: //www. cs. northwestern. edu/~ychen/', 'inner. Name')", 10); < /script> The link above will open a window of Dr. Chen’s webpage and request it every 10 milliseconds. (changed from every 100 milliseconds ) 5
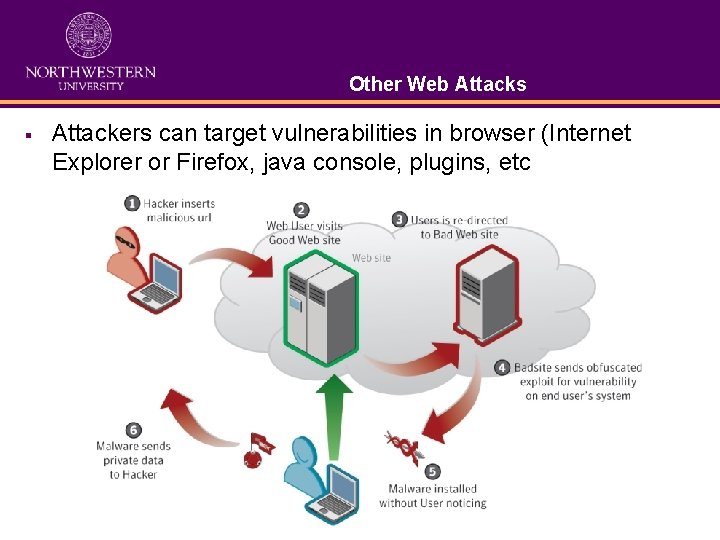
Other Web Attacks § Attackers can target vulnerabilities in browser (Internet Explorer or Firefox, java console, plugins, etc 6
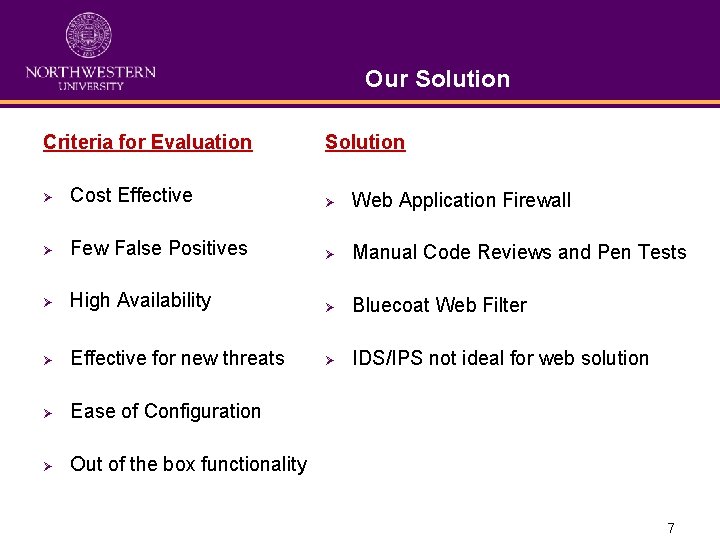
Our Solution Criteria for Evaluation Solution Ø Cost Effective Ø Web Application Firewall Ø Few False Positives Ø Manual Code Reviews and Pen Tests Ø High Availability Ø Bluecoat Web Filter Ø Effective for new threats Ø IDS/IPS not ideal for web solution Ø Ease of Configuration Ø Out of the box functionality 7
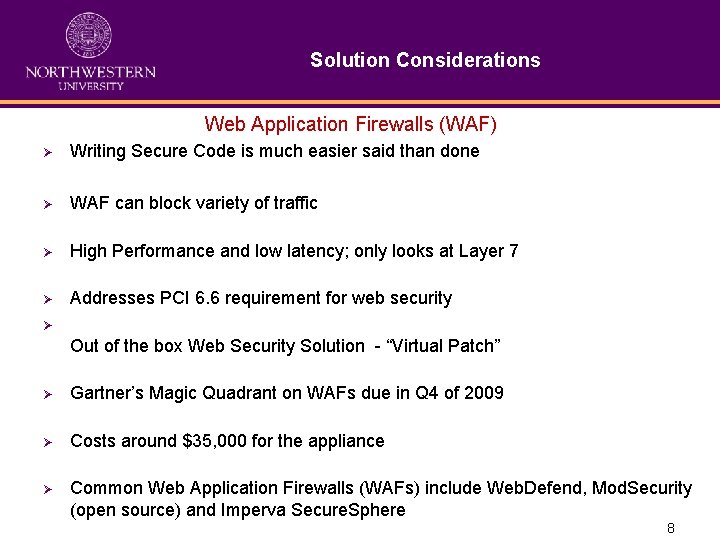
Solution Considerations Web Application Firewalls (WAF) Ø Writing Secure Code is much easier said than done Ø WAF can block variety of traffic Ø High Performance and low latency; only looks at Layer 7 Ø Addresses PCI 6. 6 requirement for web security Ø Out of the box Web Security Solution - “Virtual Patch” Ø Gartner’s Magic Quadrant on WAFs due in Q 4 of 2009 Ø Costs around $35, 000 for the appliance Ø Common Web Application Firewalls (WAFs) include Web. Defend, Mod. Security (open source) and Imperva Secure. Sphere 8
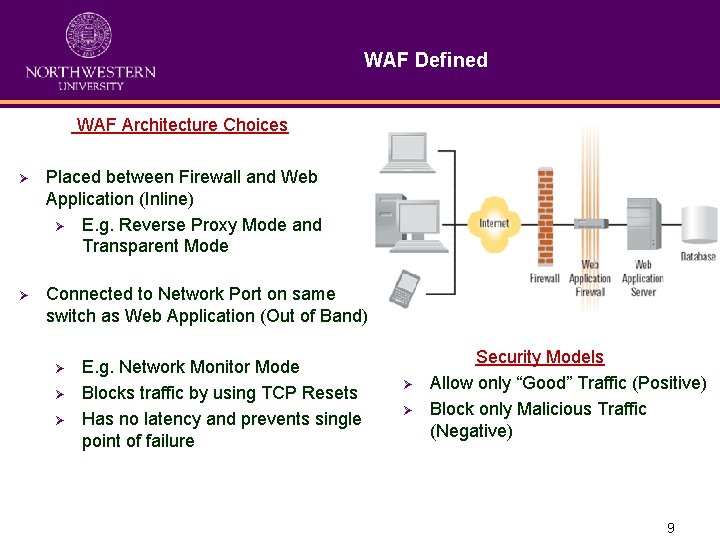
WAF Defined WAF Architecture Choices Ø Placed between Firewall and Web Application (Inline) Ø E. g. Reverse Proxy Mode and Transparent Mode Ø Connected to Network Port on same switch as Web Application (Out of Band) Ø Ø Ø E. g. Network Monitor Mode Blocks traffic by using TCP Resets Has no latency and prevents single point of failure Ø Ø Security Models Allow only “Good” Traffic (Positive) Block only Malicious Traffic (Negative) 9
How WAF does the job? Ø Dynamic Profiling (Automated Application Learning) Ø Session Protecting Engine Ø SSL Decryption Ø Data leakage protection 10
Manual Code Reviews and Application Pen Tests Ø Best Defense of Websites Ø Manual tests done by experts Ø Whitebox testing available Ø Costs are $300 per 500 lines of code Ø Average Web Application Code Review costs $30, 000 (50, 000 lines of code) 11
Bluecoat Web Filter Defined Ø Blue Coat Web. Filter is an “on-proxy” web filtering solution that protects internal users from Ø Spyware Ø Phishing attacks Ø P 2 P Ø IM and streaming traffic Ø Adult content (sorry) Ø Botnets (yayy) Ø Appliance starts at $10, 000 12
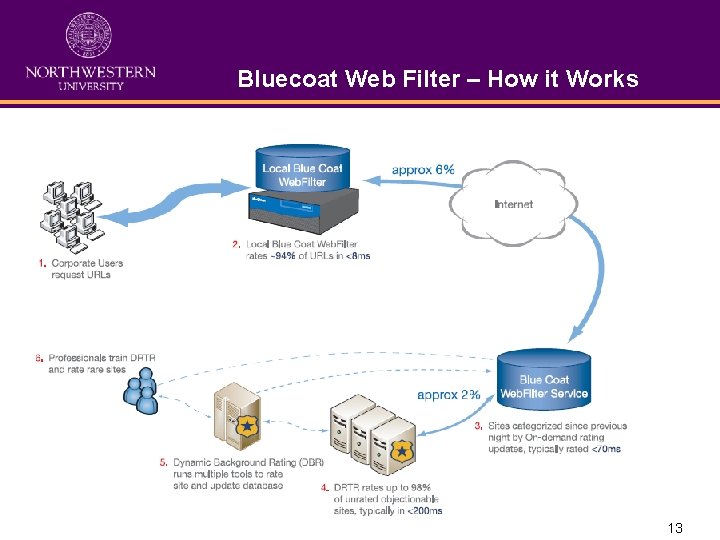
Bluecoat Web Filter – How it Works 13
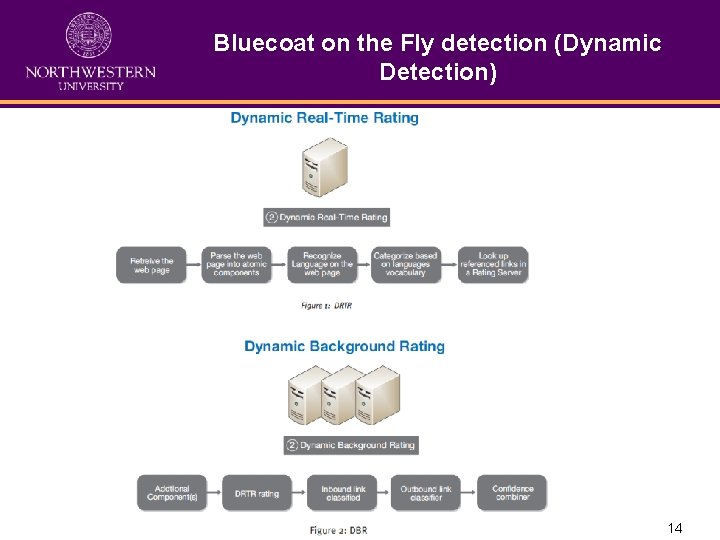
Bluecoat on the Fly detection (Dynamic Detection) 14
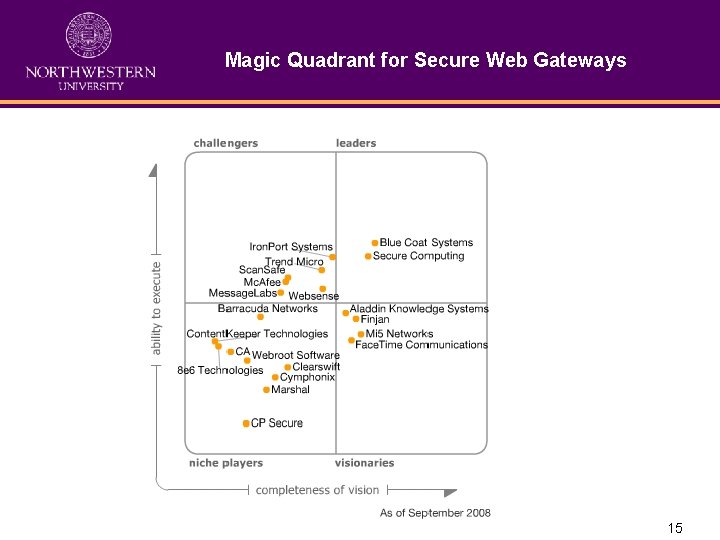
Magic Quadrant for Secure Web Gateways 15
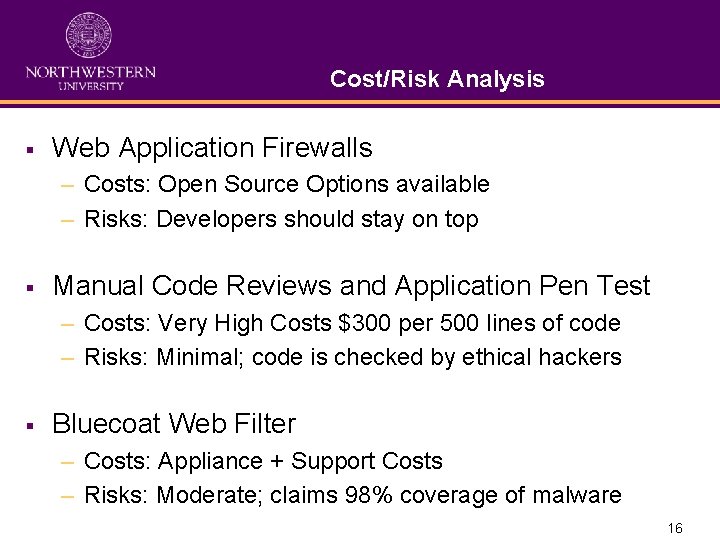
Cost/Risk Analysis § Web Application Firewalls – Costs: Open Source Options available – Risks: Developers should stay on top § Manual Code Reviews and Application Pen Test – Costs: Very High Costs $300 per 500 lines of code – Risks: Minimal; code is checked by ethical hackers § Bluecoat Web Filter – Costs: Appliance + Support Costs – Risks: Moderate; claims 98% coverage of malware 16
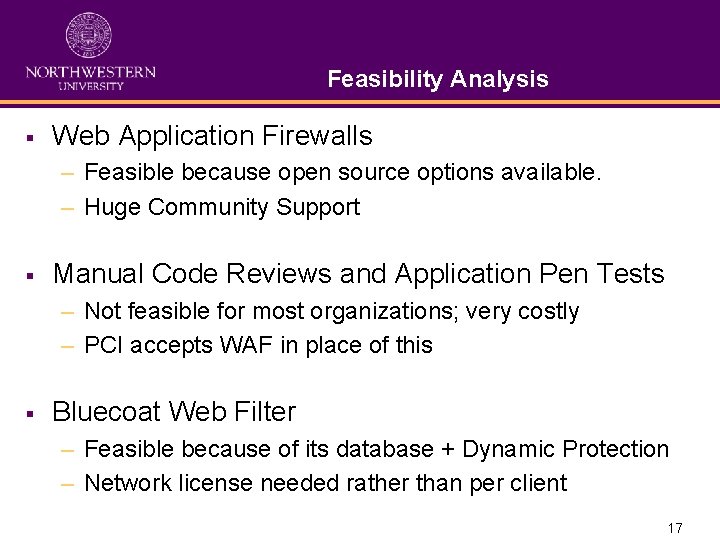
Feasibility Analysis § Web Application Firewalls – Feasible because open source options available. – Huge Community Support § Manual Code Reviews and Application Pen Tests – Not feasible for most organizations; very costly – PCI accepts WAF in place of this § Bluecoat Web Filter – Feasible because of its database + Dynamic Protection – Network license needed rather than per client 17
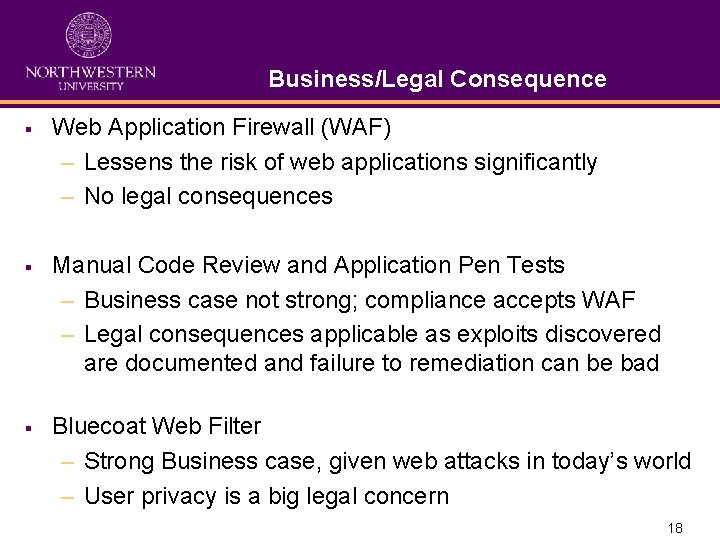
Business/Legal Consequence § Web Application Firewall (WAF) – Lessens the risk of web applications significantly – No legal consequences § Manual Code Review and Application Pen Tests – Business case not strong; compliance accepts WAF – Legal consequences applicable as exploits discovered are documented and failure to remediation can be bad § Bluecoat Web Filter – Strong Business case, given web attacks in today’s world – User privacy is a big legal concern 18
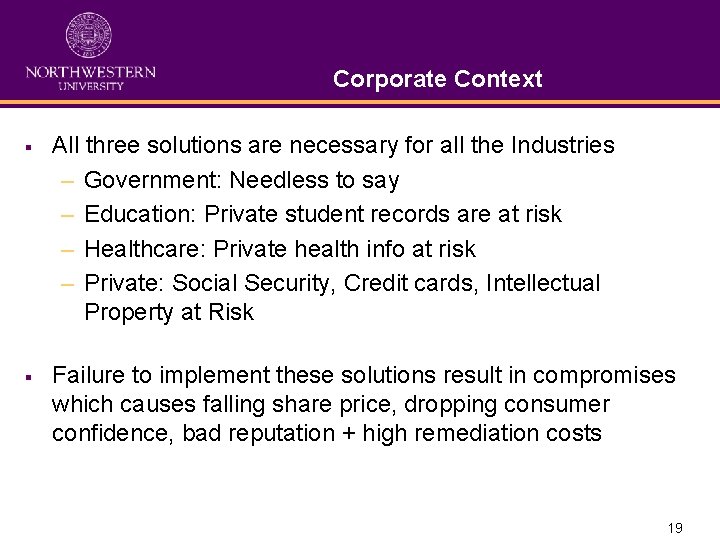
Corporate Context § All three solutions are necessary for all the Industries – Government: Needless to say – Education: Private student records are at risk – Healthcare: Private health info at risk – Private: Social Security, Credit cards, Intellectual Property at Risk § Failure to implement these solutions result in compromises which causes falling share price, dropping consumer confidence, bad reputation + high remediation costs 19
Related Work and Research in This Area § SANS Paper on Web Based Threats – http: //www. sans. org/reading_room/whitepapers/application/web_based_attack s_2053? show=2053. php&cat=application § Symantec’s Paper on Web Based Threats – http: //eval. symantec. com/mktginfo/enterprise/white_papers/bwhitepaper_web_based_attacks_03 -2009. en-us. pdf § Dev. Shed. com’s Cross Side Scripting Paper – http: //www. devshed. com/c/a/Security/A-Quick-Look-at-Cross-Site-Scripting/1/ § Bluecoat Webfilter datasheet – http: //www. bluecoat. com/doc/direct/789 § Web Application Firewall – http: //www. owasp. org/index. php/Web_Application_Firewall 20

Thank You Jibran Ilyas Frank La. Sota Paul Lowder Juan Mendez 21
- Slides: 21