PeertoPeer Protocol P 2 PP Salman Baset Henning
Peer-to-Peer Protocol (P 2 PP) Salman Baset, Henning Schulzrinne Columbia University
Agenda • Motivation • Practical issues in peer-to-peer systems • Peer-to-peer systems – file sharing – Vo. IP – streaming • • Peer-to-Peer Protocol (P 2 PP) P 2 PP design issues Related work Implementation
Motivation • Build a peer-to-peer application • Where to start? • Too many p 2 p protocols – is there a best one? • Too many design choices
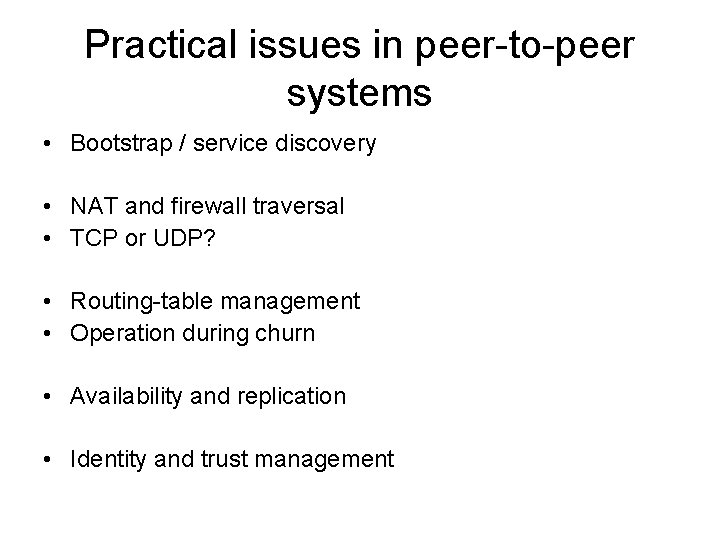
Practical issues in peer-to-peer systems • Bootstrap / service discovery • NAT and firewall traversal • TCP or UDP? • Routing-table management • Operation during churn • Availability and replication • Identity and trust management
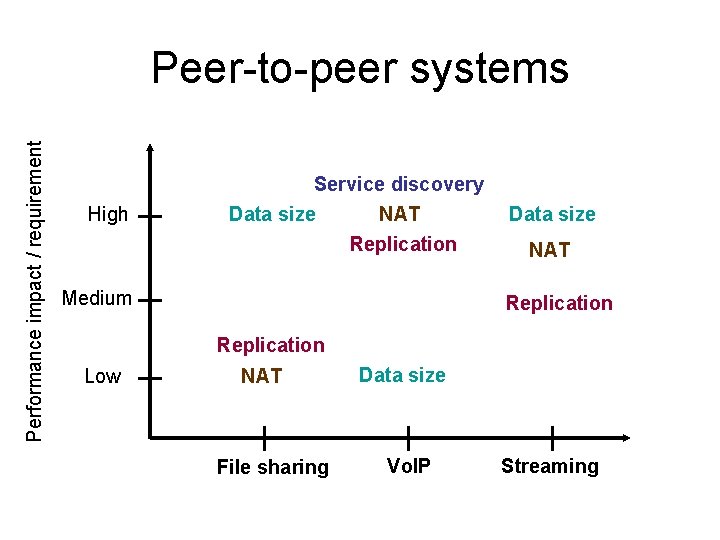
Performance impact / requirement Peer-to-peer systems High Service discovery Data size NAT Replication Medium Data size NAT Replication Low NAT File sharing Data size Vo. IP Streaming
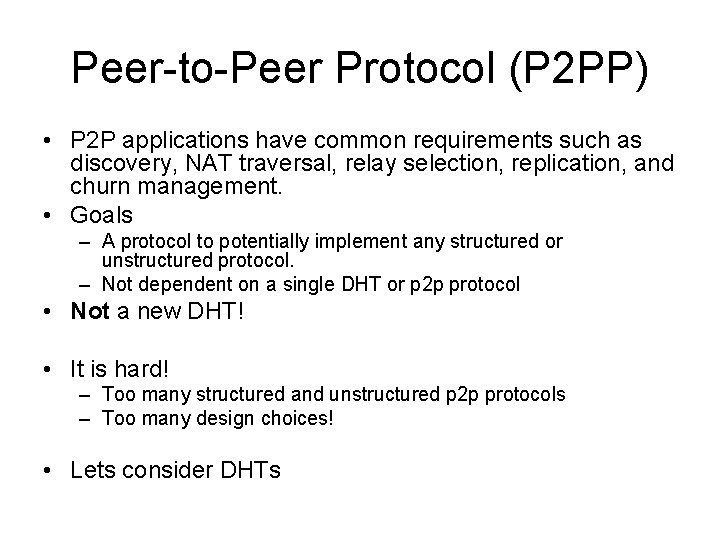
Peer-to-Peer Protocol (P 2 PP) • P 2 P applications have common requirements such as discovery, NAT traversal, relay selection, replication, and churn management. • Goals – A protocol to potentially implement any structured or unstructured protocol. – Not dependent on a single DHT or p 2 p protocol • Not a new DHT! • It is hard! – Too many structured and unstructured p 2 p protocols – Too many design choices! • Lets consider DHTs
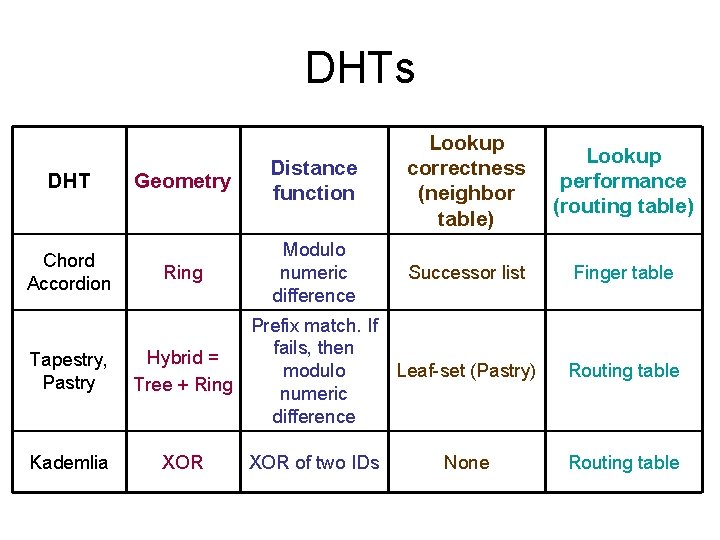
DHTs DHT Chord Accordion Tapestry, Pastry Kademlia Geometry Distance function Lookup correctness (neighbor table) Lookup performance (routing table) Ring Modulo numeric difference Successor list Finger table Leaf-set (Pastry) Routing table None Routing table Prefix match. If fails, then Hybrid = modulo Tree + Ring numeric difference XOR of two IDs
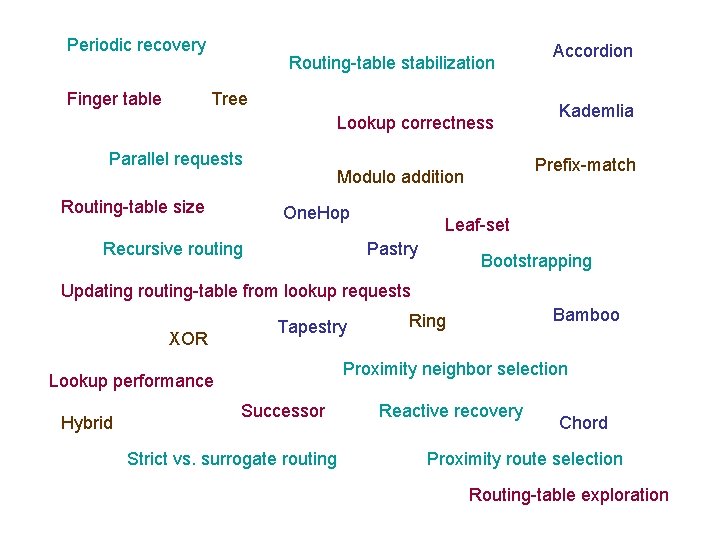
Periodic recovery Finger table Routing-table stabilization Tree Lookup correctness Parallel requests Routing-table size Recursive routing Kademlia Prefix-match Modulo addition One. Hop Accordion Leaf-set Pastry Bootstrapping Updating routing-table from lookup requests XOR Tapestry Proximity neighbor selection Lookup performance Hybrid Bamboo Ring Successor Strict vs. surrogate routing Reactive recovery Chord Proximity route selection Routing-table exploration
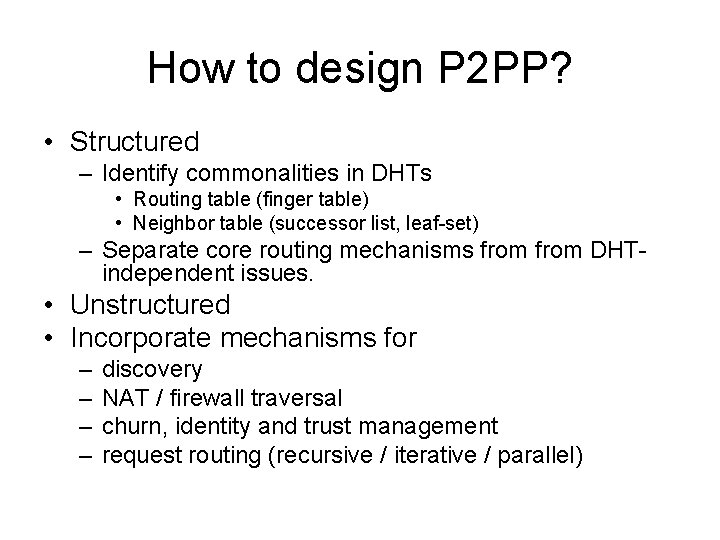
How to design P 2 PP? • Structured – Identify commonalities in DHTs • Routing table (finger table) • Neighbor table (successor list, leaf-set) – Separate core routing mechanisms from DHTindependent issues. • Unstructured • Incorporate mechanisms for – – discovery NAT / firewall traversal churn, identity and trust management request routing (recursive / iterative / parallel)
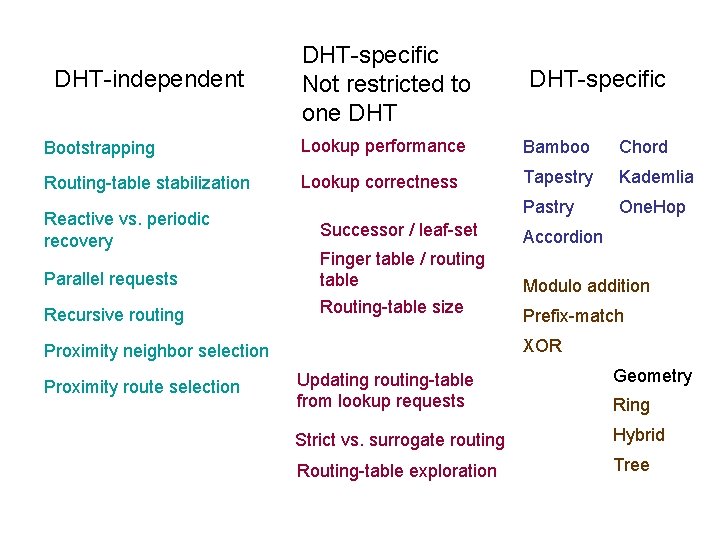
DHT-independent DHT-specific Not restricted to one DHT-specific Bootstrapping Lookup performance Bamboo Chord Routing-table stabilization Lookup correctness Tapestry Kademlia Pastry One. Hop Reactive vs. periodic recovery Parallel requests Recursive routing Successor / leaf-set Accordion Finger table / routing table Routing-table size Modulo addition XOR Proximity neighbor selection Proximity route selection Prefix-match Updating routing-table from lookup requests Geometry Strict vs. surrogate routing Hybrid Routing-table exploration Tree Ring
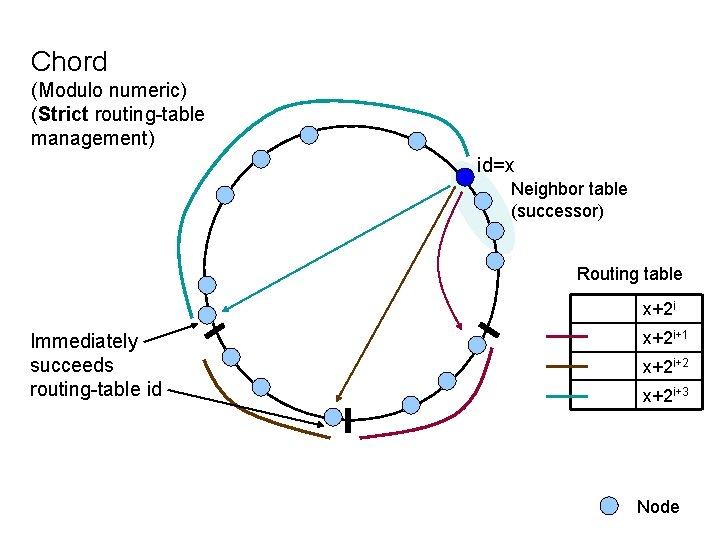
Chord (Modulo numeric) (Strict routing-table management) id=x Neighbor table (successor) Routing table x+2 i Immediately succeeds routing-table id x+2 i+1 x+2 i+2 x+2 i+3 Node
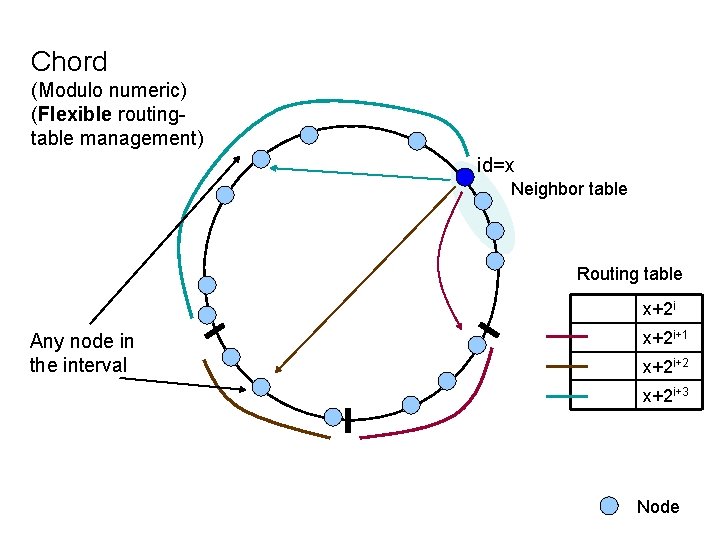
Chord (Modulo numeric) (Flexible routingtable management) id=x Neighbor table Routing table x+2 i Any node in the interval x+2 i+1 x+2 i+2 x+2 i+3 Node
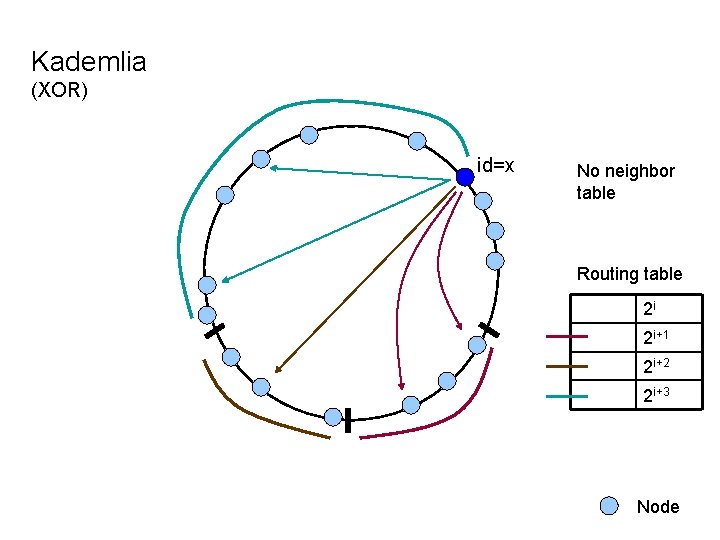
Kademlia (XOR) id=x No neighbor table Routing table 2 i 2 i+1 2 i+2 2 i+3 Node
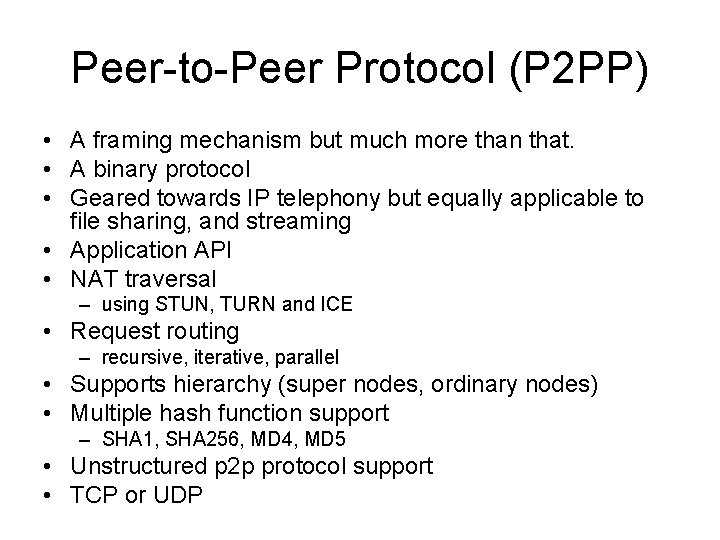
Peer-to-Peer Protocol (P 2 PP) • A framing mechanism but much more than that. • A binary protocol • Geared towards IP telephony but equally applicable to file sharing, and streaming • Application API • NAT traversal – using STUN, TURN and ICE • Request routing – recursive, iterative, parallel • Supports hierarchy (super nodes, ordinary nodes) • Multiple hash function support – SHA 1, SHA 256, MD 4, MD 5 • Unstructured p 2 p protocol support • TCP or UDP
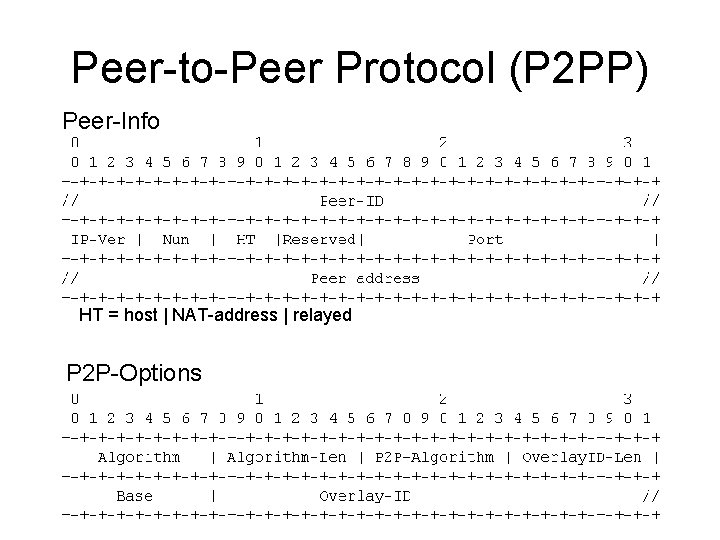
Peer-to-Peer Protocol (P 2 PP) Peer-Info HT = host | NAT-address | relayed P 2 P-Options
Related work • Towards a common API for structured peer-to-peer overlays • A performance vs. cost framework for evaluating DHT design tradeoffs under churn
Implementation • • Chord, Kademlia SHA 1, SHA 256, MD 5, MD 4 Windows, Linux Integrated with Open. Wengo (Vo. IP phone)
Questions? • I use Skype. Why should I use this protocol?
- Slides: 18