Outline22 Firewall Packet Filtering Application Gateway Proxy Server






- Slides: 56
Outline(2/2) • 防火牆(Firewall) –簡單交通記錄系統 – Packet Filtering – Application Gateway – Proxy Server – Screened Host Firewall 3
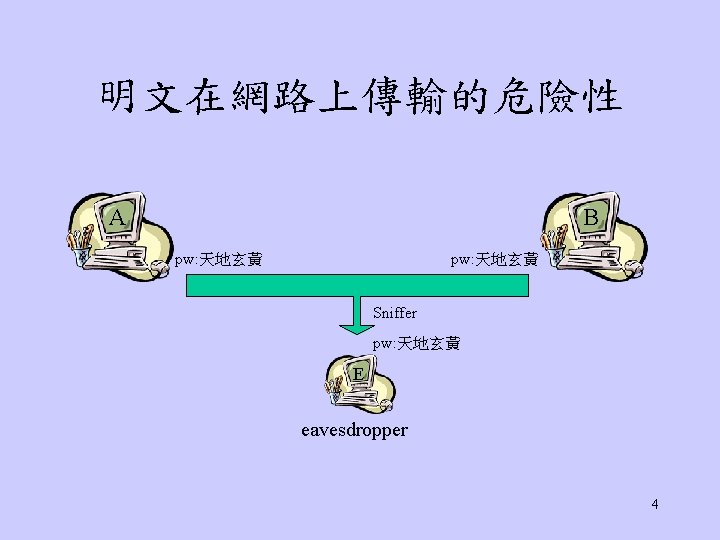
其他傳輸Attack • • Eavesdropping OS漏洞 Password的竊取 Spoofing, Spam, Intrusion Session Hijacking 特洛依木馬Troy、virus、trapdoor Covert Channel 5
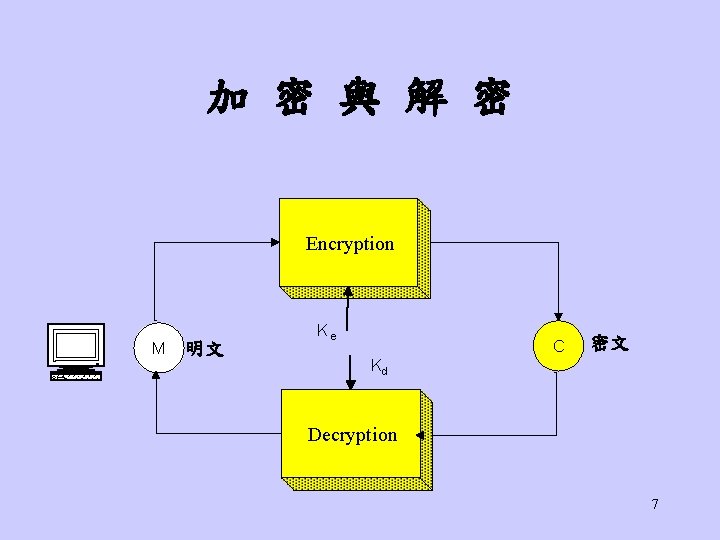
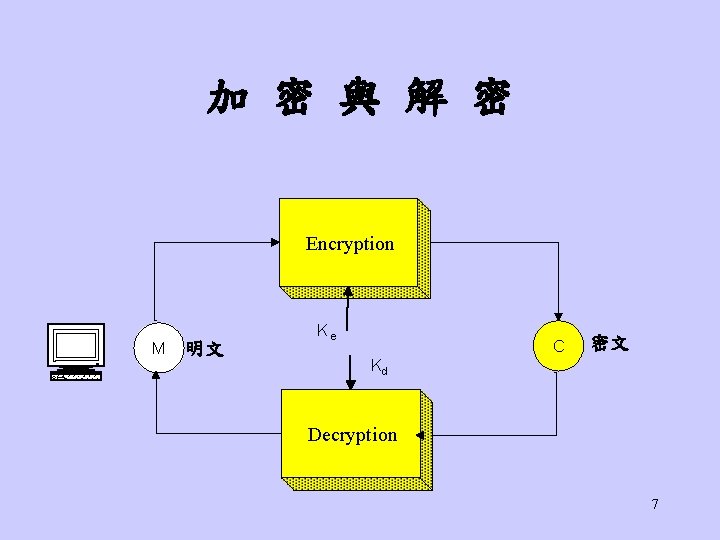
加 密 與 解 密 Encryption M 明文 Ke Kd C 密文 Decryption 7

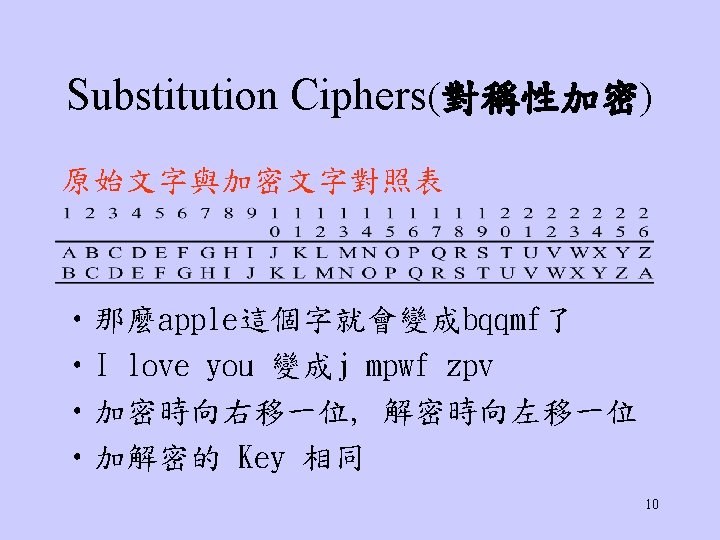
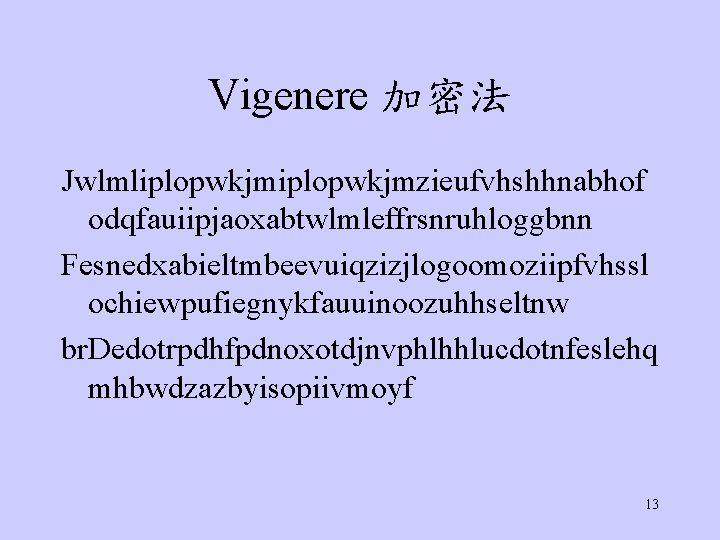
Vigenere 加密法 Jwlmliplopwkjmzieufvhshhnabhof odqfauiipjaoxabtwlmleffrsnruhloggbnn Fesnedxabieltmbeevuiqzizjlogoomoziipfvhssl ochiewpufiegnykfauuinoozuhhseltnw br. Dedotrpdhfpdnoxotdjnvphlhhlucdotnfeslehq mhbwdzazbyisopiivmoyf 13
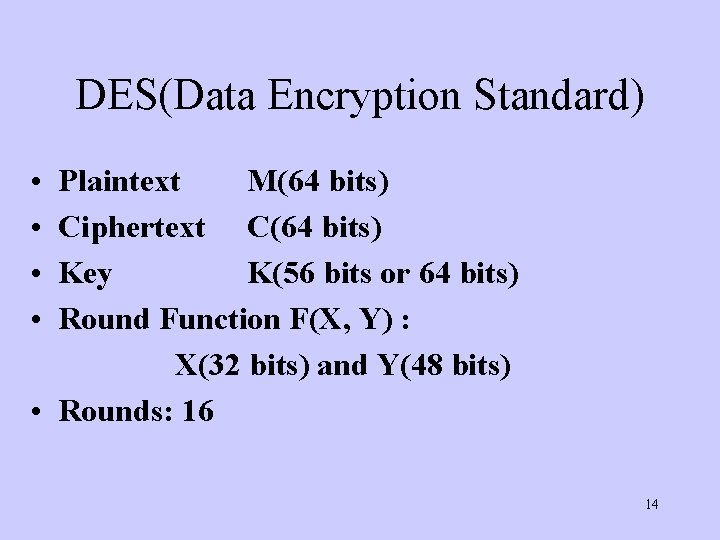
DES(Data Encryption Standard) • • Plaintext M(64 bits) Ciphertext C(64 bits) Key K(56 bits or 64 bits) Round Function F(X, Y) : X(32 bits) and Y(48 bits) • Rounds: 16 14
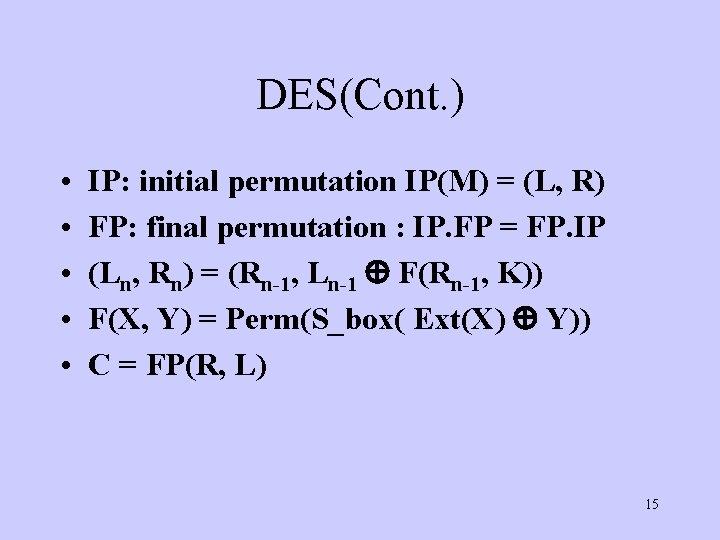
DES(Cont. ) • • • IP: initial permutation IP(M) = (L, R) FP: final permutation : IP. FP = FP. IP (Ln, Rn) = (Rn-1, Ln-1 F(Rn-1, K)) F(X, Y) = Perm(S_box( Ext(X) Y)) C = FP(R, L) 15
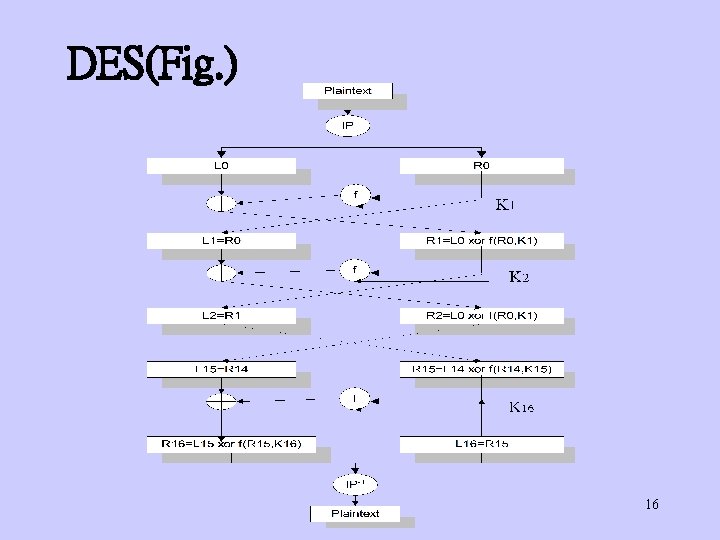
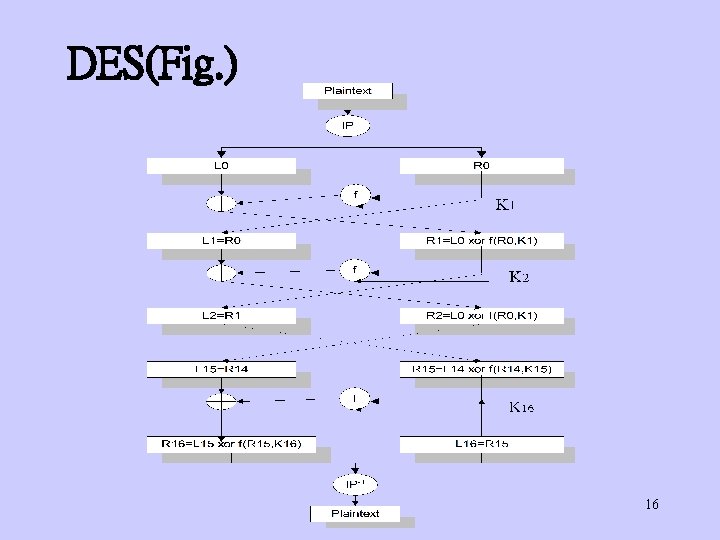
DES(Fig. ) 16
DES(One round) 17
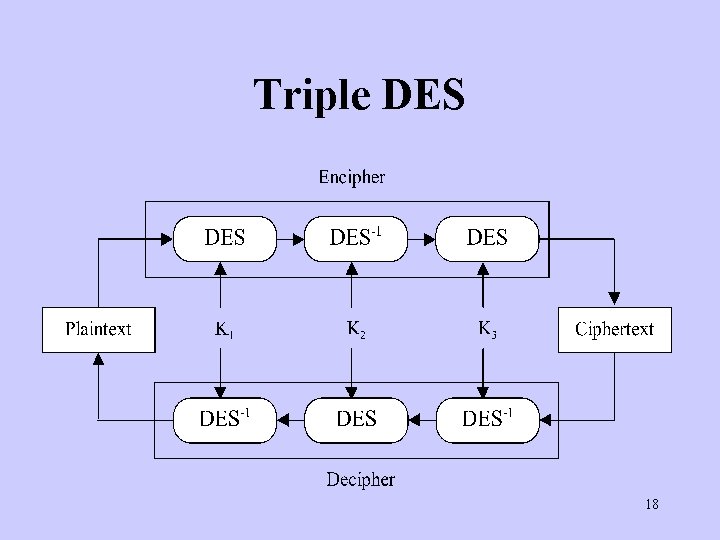
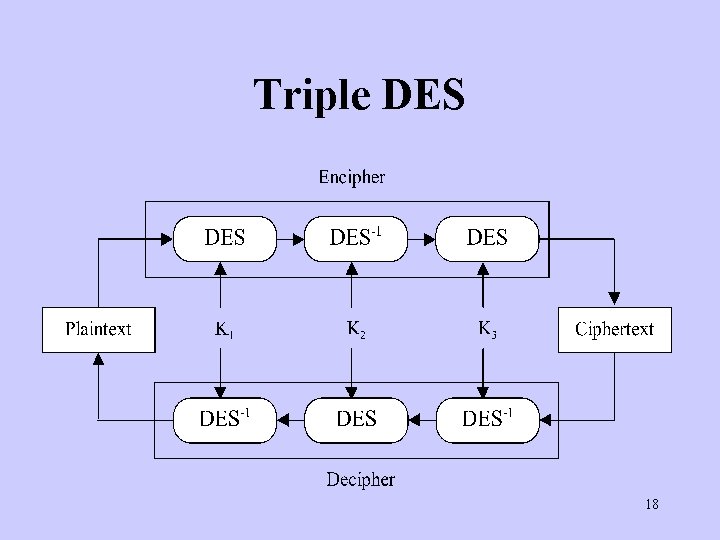
Triple DES 18
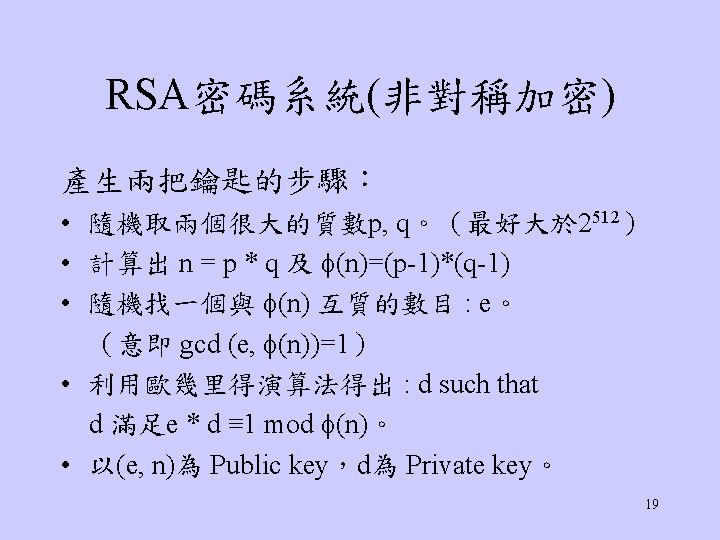
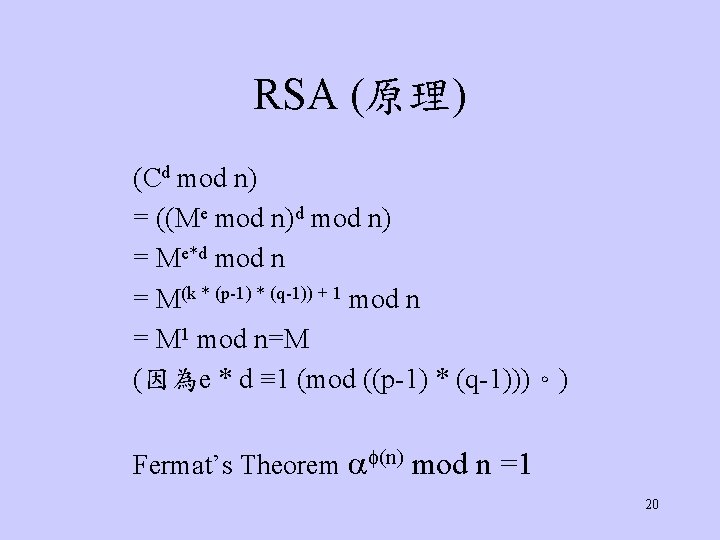
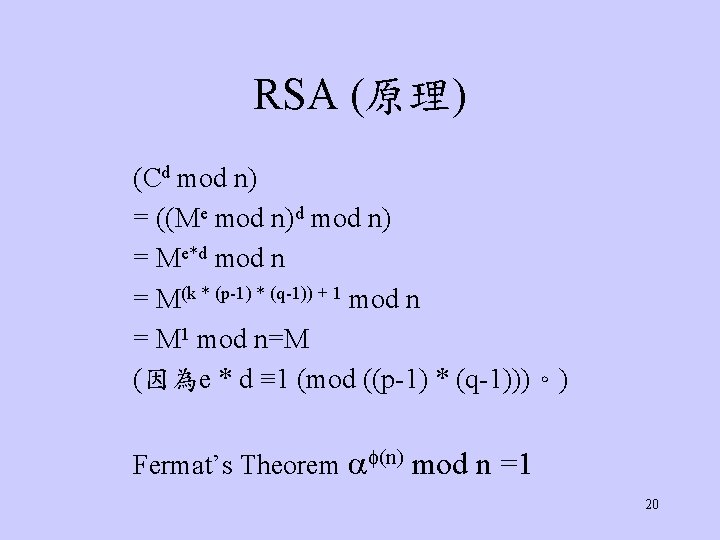
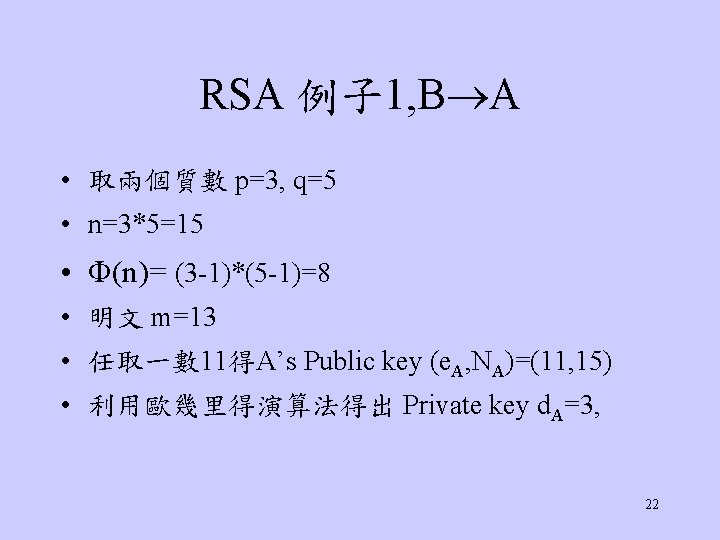
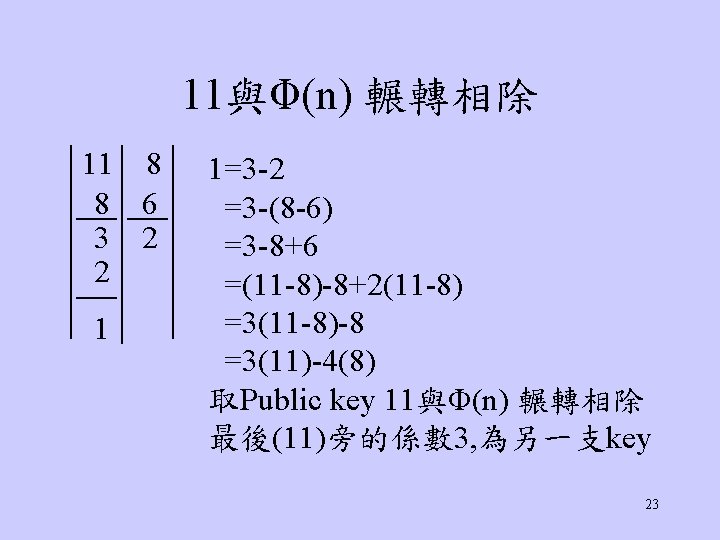
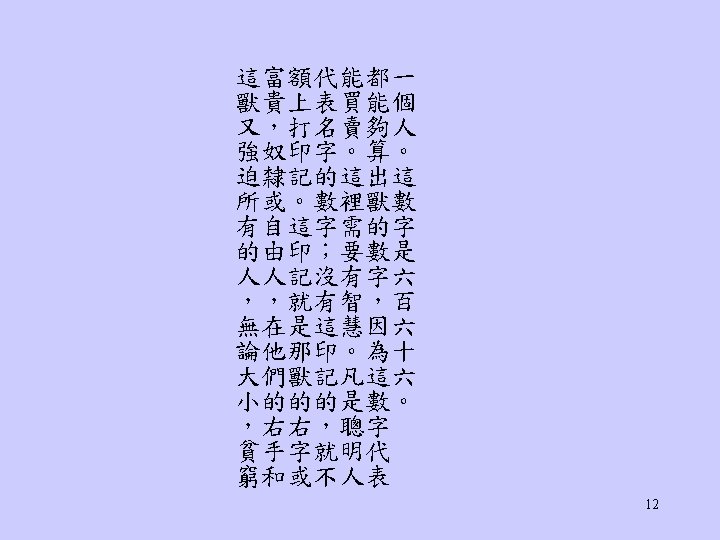
RSA (原理) (Cd mod n) = ((Me mod n)d mod n) = Me*d mod n = M(k * (p-1) * (q-1)) + 1 mod n = M 1 mod n=M (因為e * d ≡ 1 (mod ((p-1) * (q-1)))。) Fermat’s Theorem (n) mod n =1 20
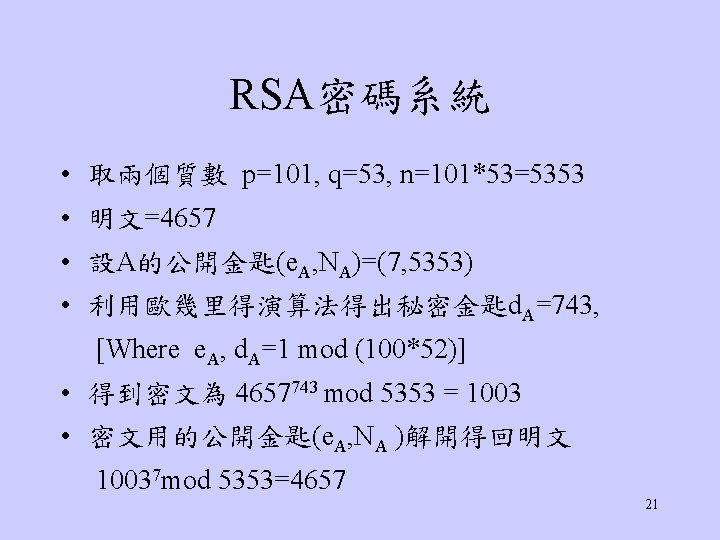
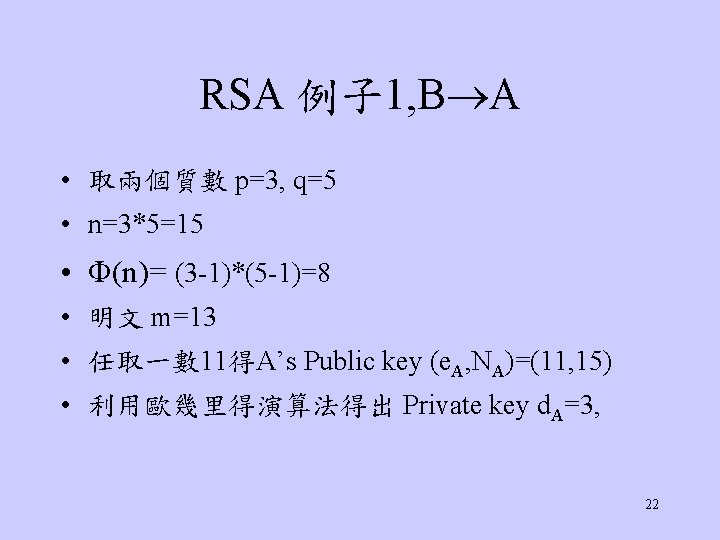
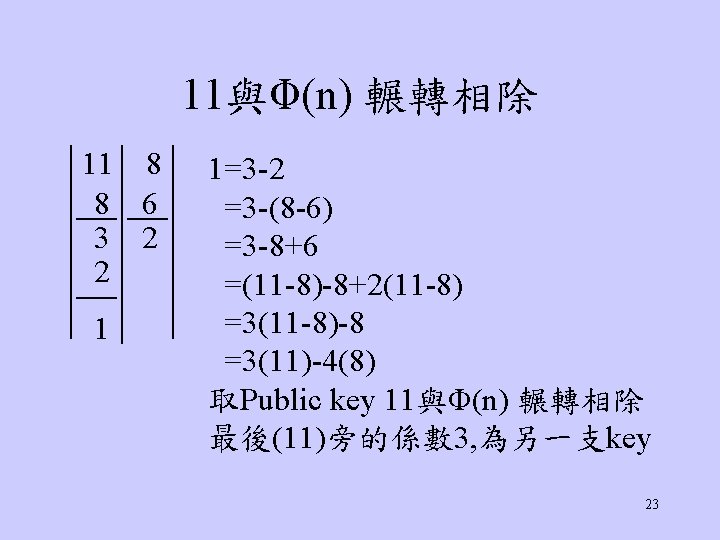
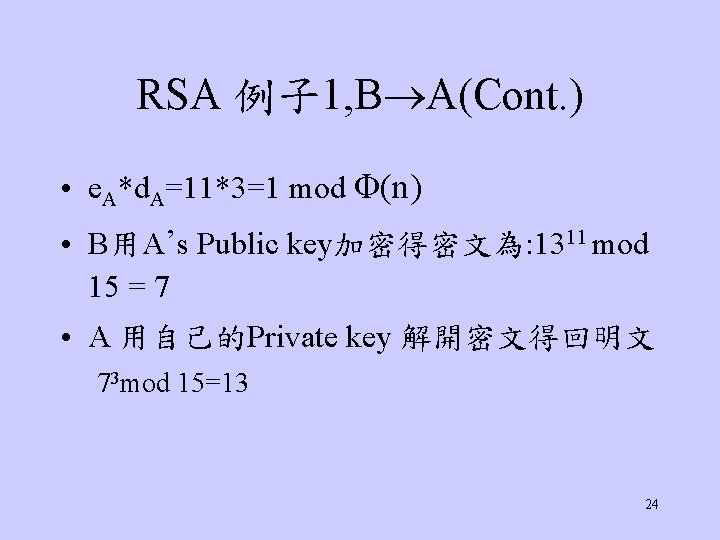
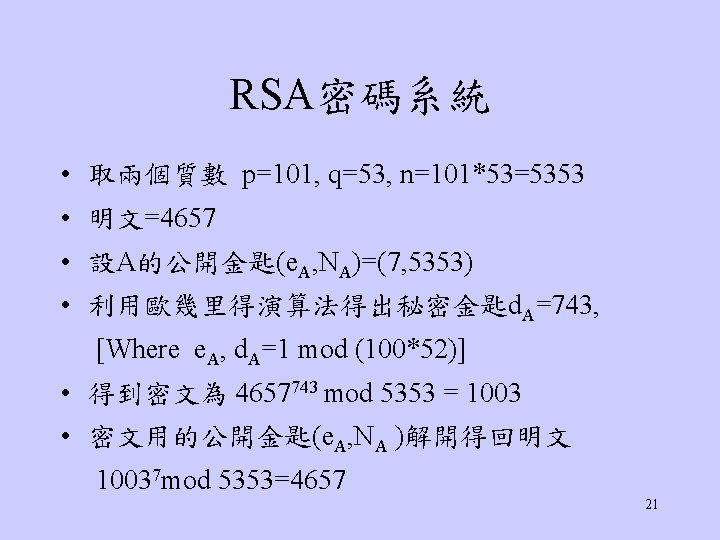
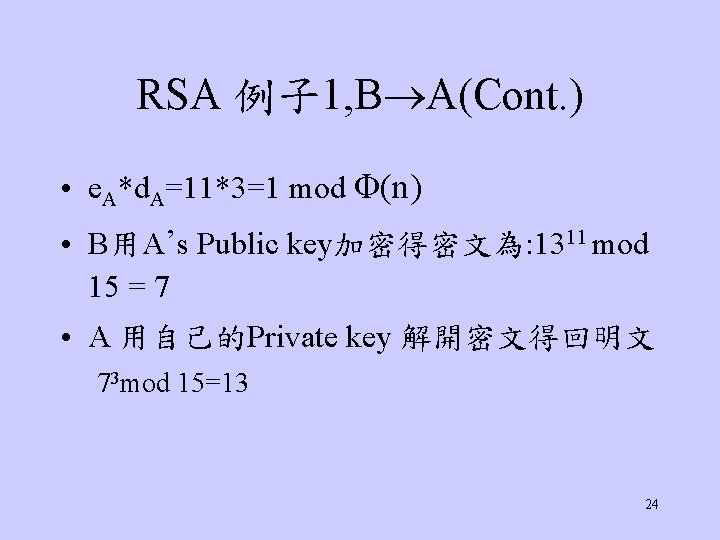
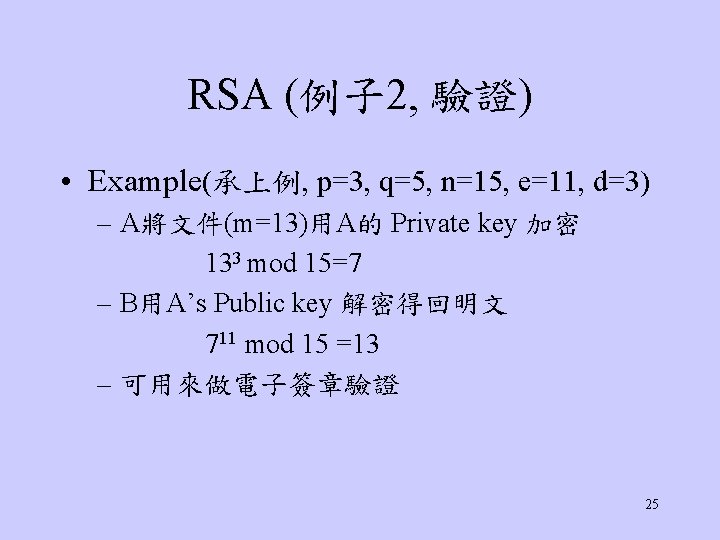
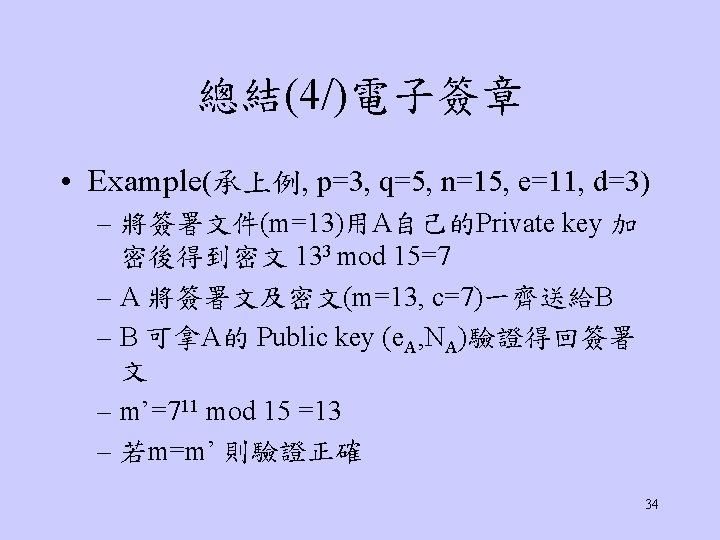
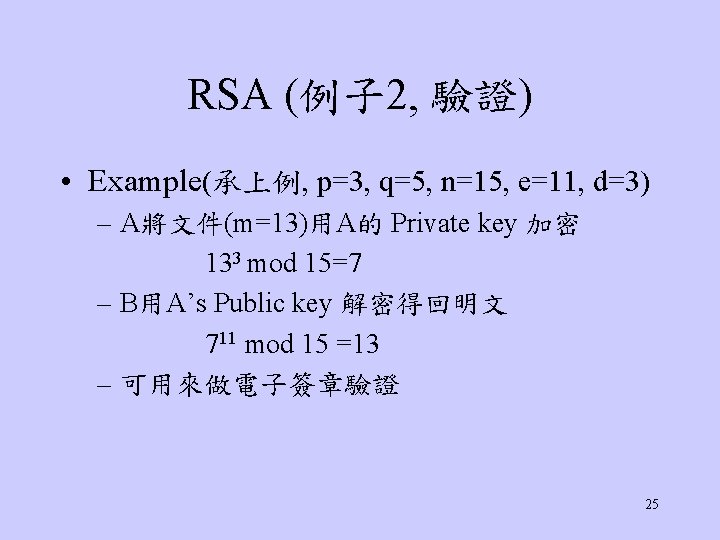
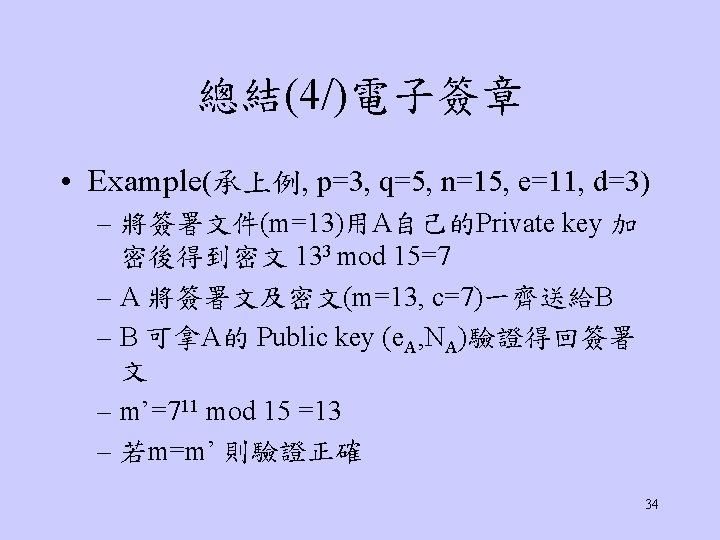
RSA 例子 1, B A(Cont. ) • e. A*d. A=11*3=1 mod Φ(n) • B用A’s Public key加密得密文為: 1311 mod 15 = 7 • A 用自己的Private key 解開密文得回明文 73 mod 15=13 24

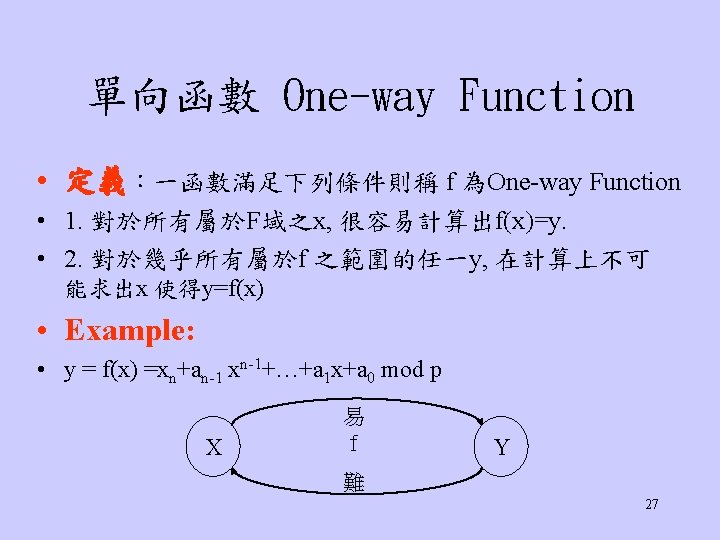
RSA特性及其運用 • • • RSA運用exponential algorithm RSA執行速度較DES等對稱加密慢 硬體的RSA比硬體的DES慢 1000倍 軟體的RSA則比軟體的DES慢 100倍 故RSA其主要的用途: – digital signature – protocol中的key exchange。 26
Message Authentication Codes (MAC) • MAC is an authentication tag (also called a checksum) derived by appying an authentication scheme, together with a secret key, to a message. • There are four types of MACs: (1) unconditionally secure (2) hash function-based (3) stream cipher-based or (4) block cipher-based. 28
MAC • Hash function H(m 1, m 2, …, mt)=m • 現有的Hash function: MD 5, SHA-1, . . . • MAC is key-dependent one-way hash function – MAC are computed and verified with the same key – A & B 共同擁有 key K – A send H(K, M) to B – B can reproduce A’s result 29
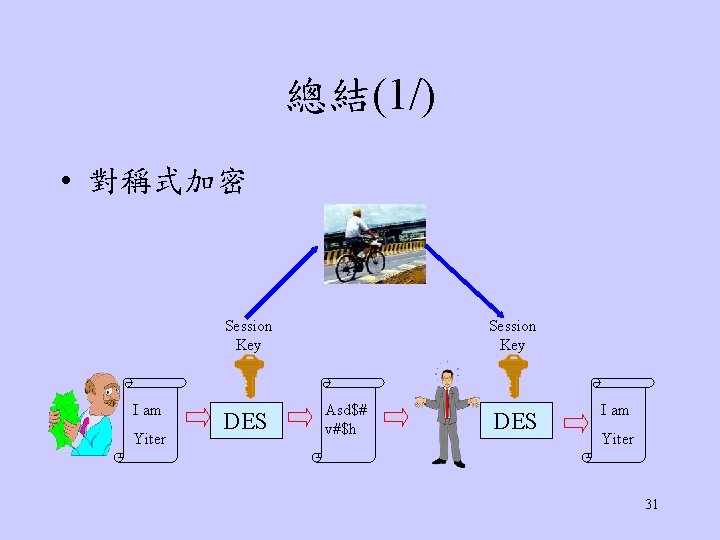
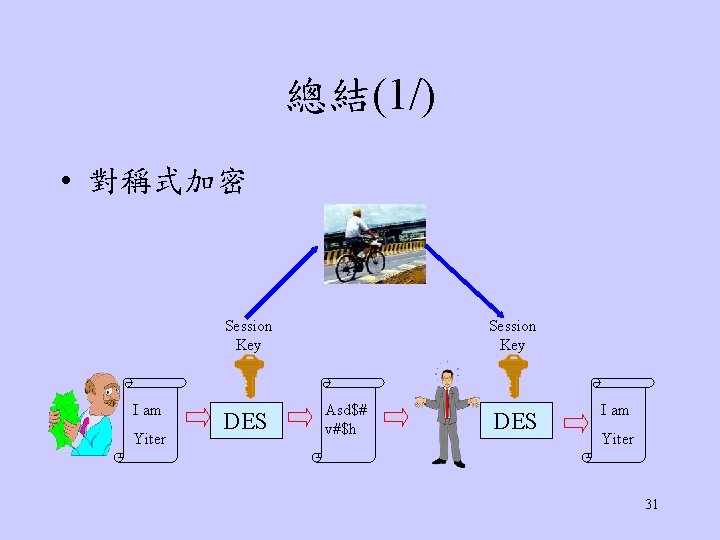
總結(1/) • 對稱式加密 Session Key I am Yiter DES Session Key Asd$# v#$h DES I am Yiter 31
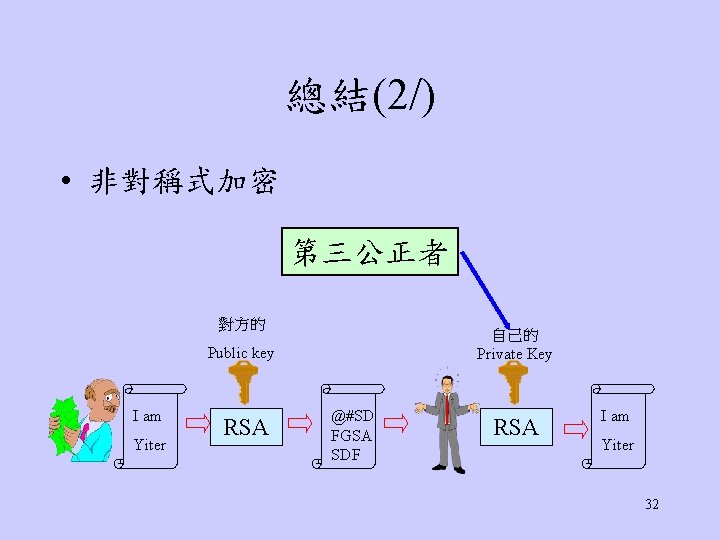
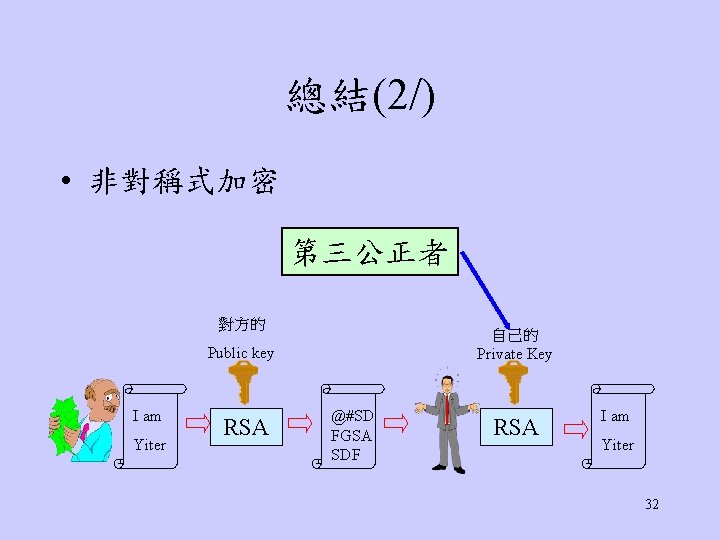
總結(2/) • 非對稱式加密 第三公正者 對方的 自己的 Private Key Public key I am Yiter RSA @#SD FGSA SDF RSA I am Yiter 32
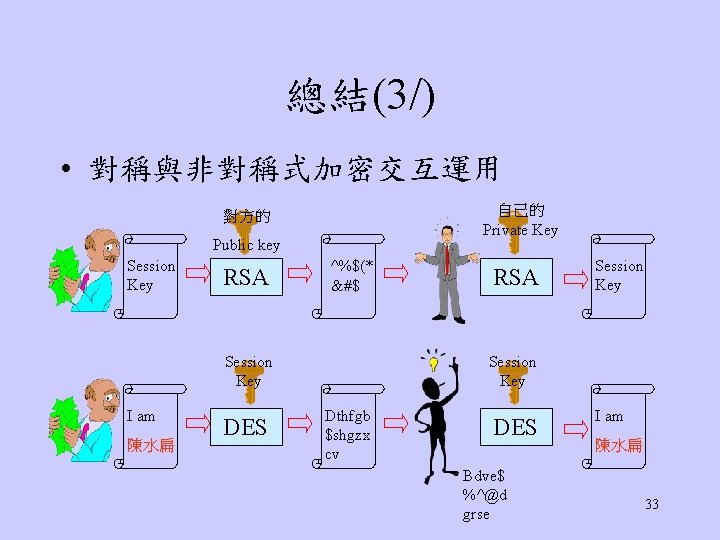
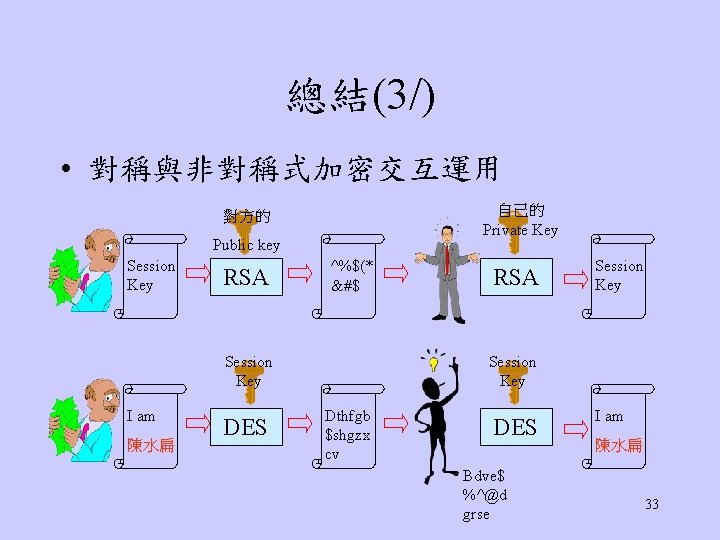
總結(3/) • 對稱與非對稱式加密交互運用 自己的 Private Key 對方的 Public key Session Key RSA ^%$(* &#$ Session Key I am 陳水扁 DES RSA Session Key Dthfgb $shgzx cv DES Bdve$ %^@d grse I am 陳水扁 33
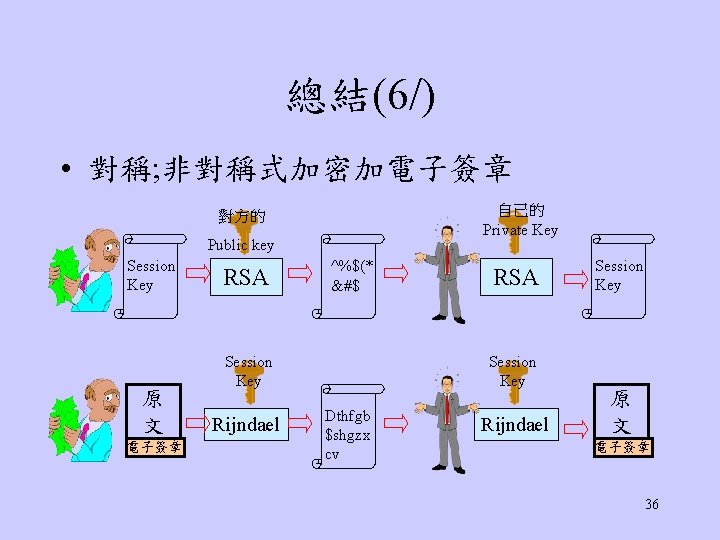
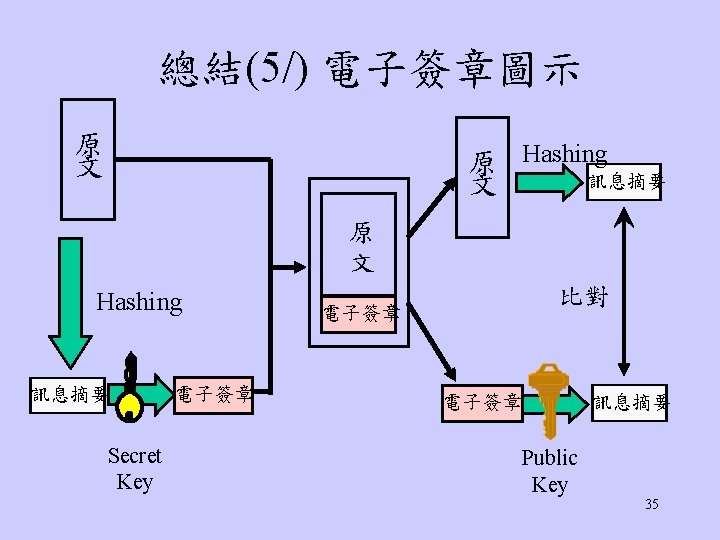
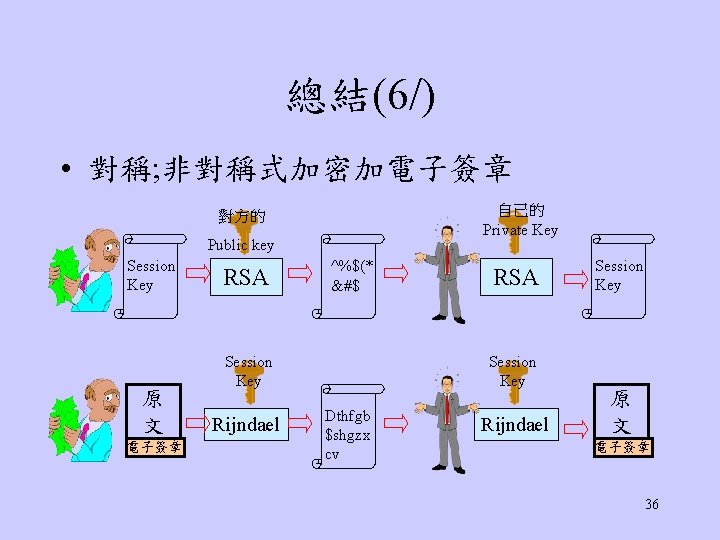
總結(6/) • 對稱; 非對稱式加密加電子簽章 自己的 Private Key 對方的 Public key Session Key 原 文 電子簽章 RSA ^%$(* &#$ Session Key Rijndael RSA Session Key Dthfgb $shgzx cv Rijndael Session Key 原 文 電子簽章 36
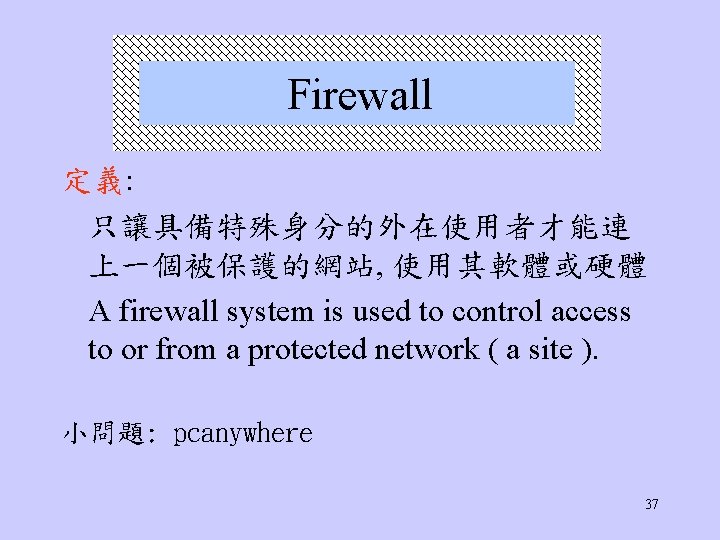
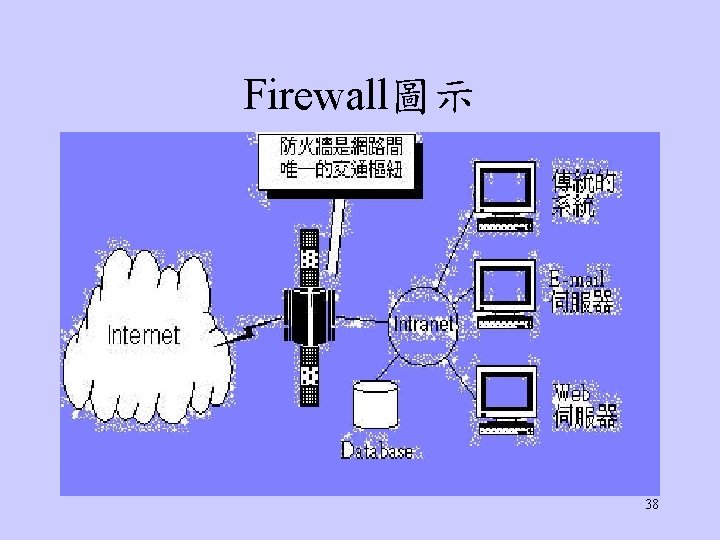
Firewall 定義: 只讓具備特殊身分的外在使用者才能連 上一個被保護的網站, 使用其軟體或硬體 A firewall system is used to control access to or from a protected network ( a site ). 小問題: pcanywhere 37
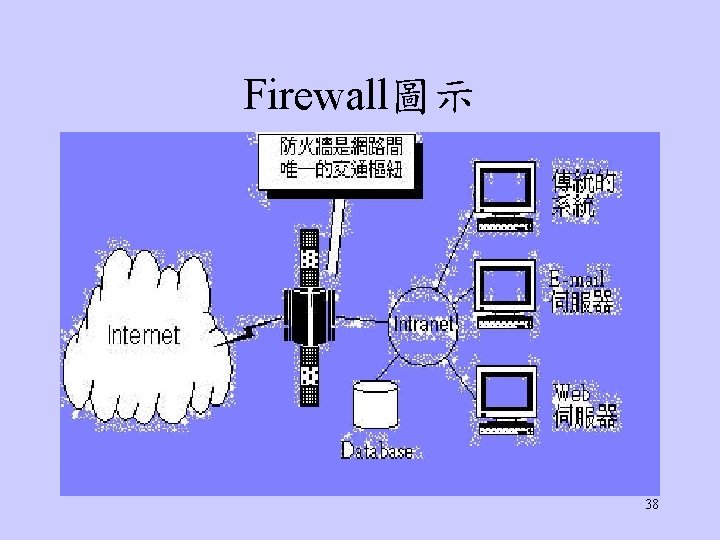
Firewall圖示 38

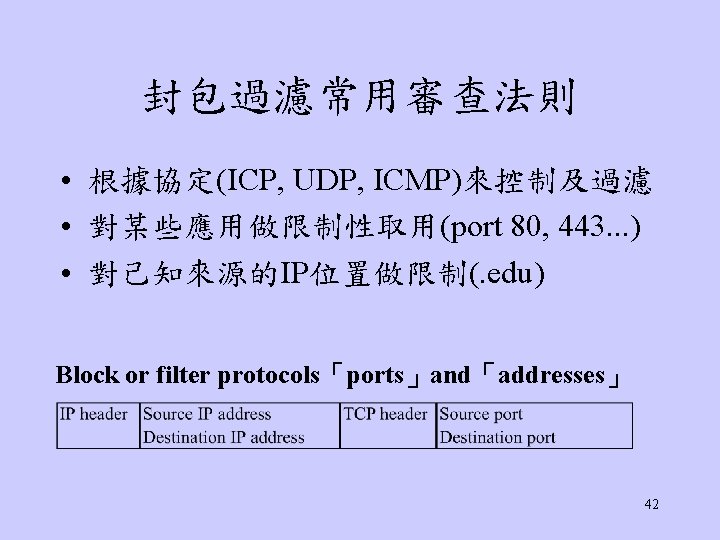
Firewall 的種類 • 簡單交通記錄系統 • 封包過濾(Packet Filtering) • Application Gateway (Dual-homed Gateway) • Proxy Server • Screened Host Firewall 39
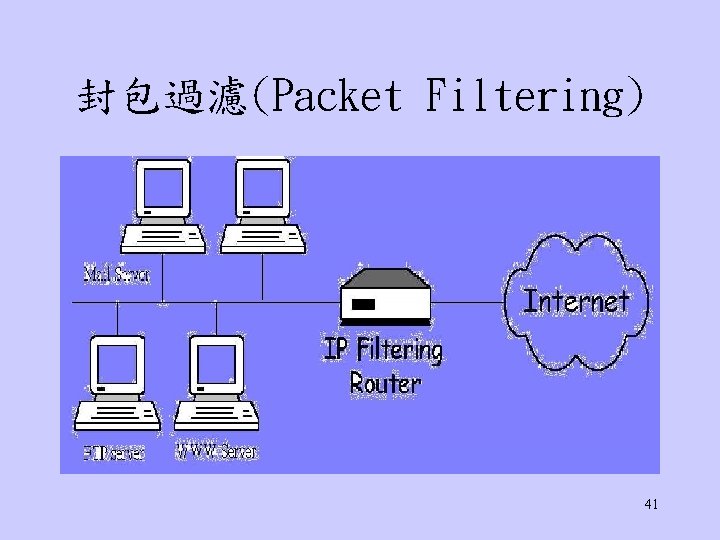
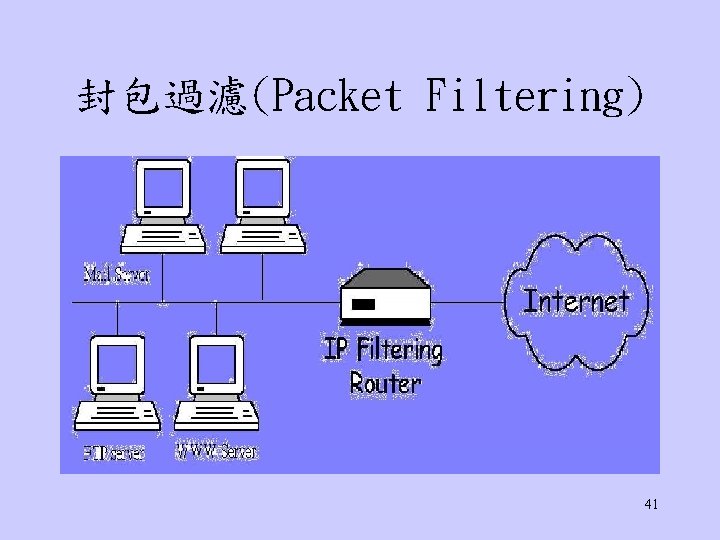
封包過濾(Packet Filtering) 41
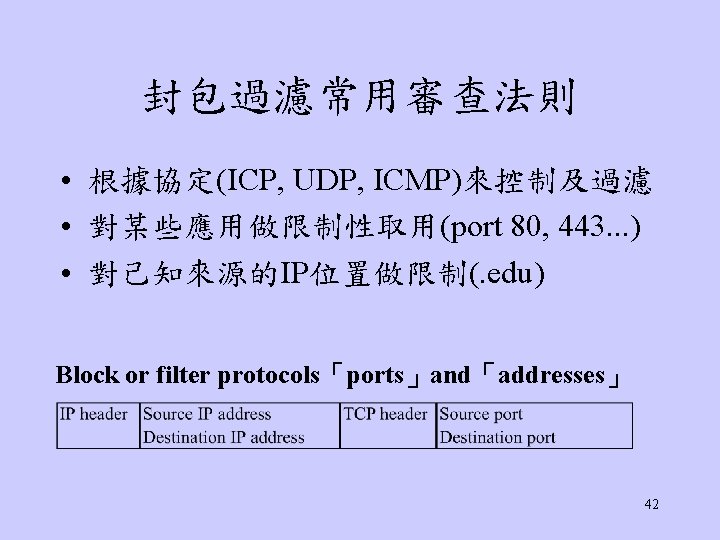

封包過濾優缺點 • 優點 – Most Common , easy and cheap – Fully transparency, no impact to user • 缺點 – Little or no logging capability – Complex filtering rules may become unmanageable – Rules are difficult to test thoroughly 43
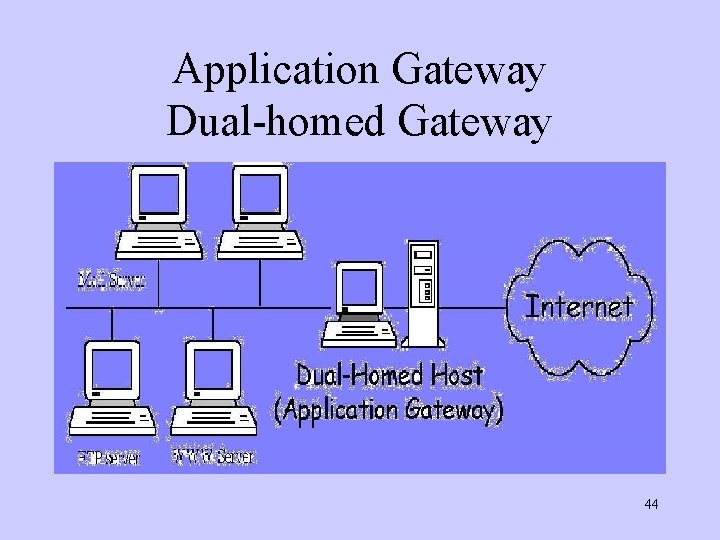
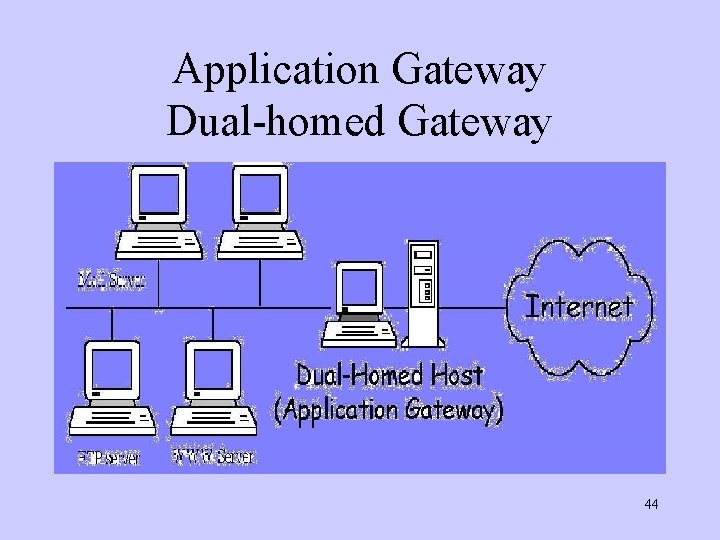
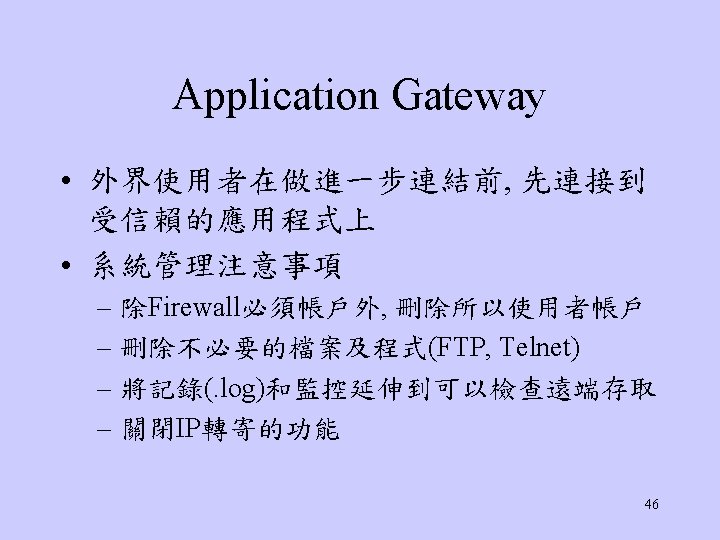
Application Gateway Dual-homed Gateway 44

Application Gateway圖示 45
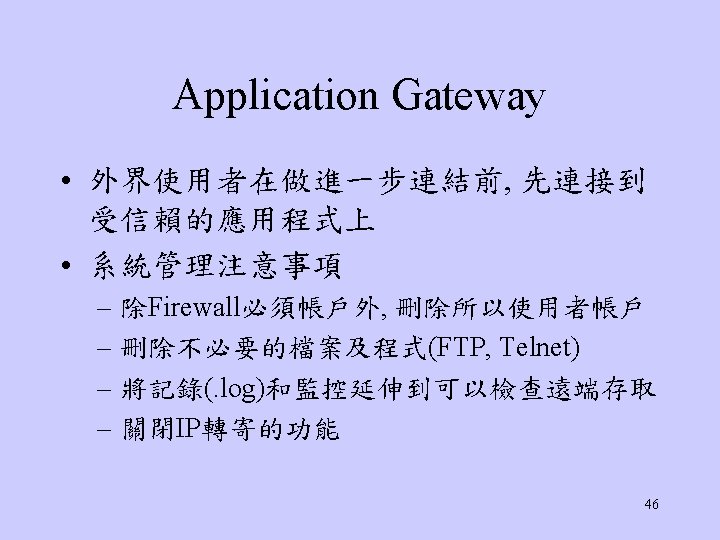
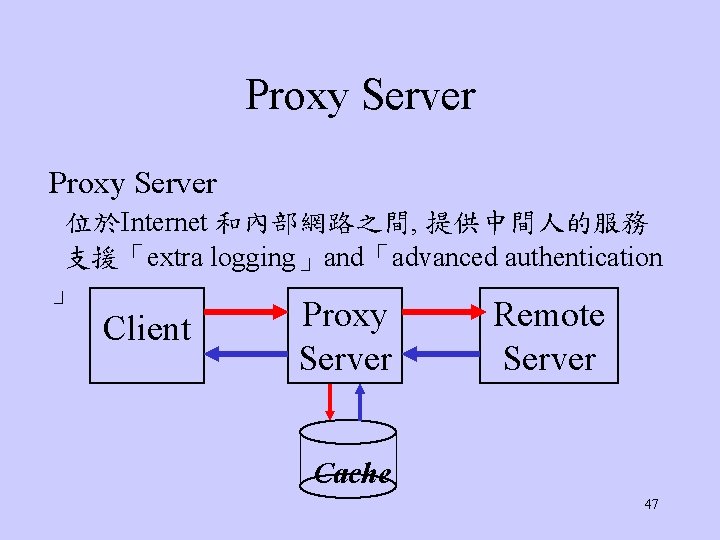
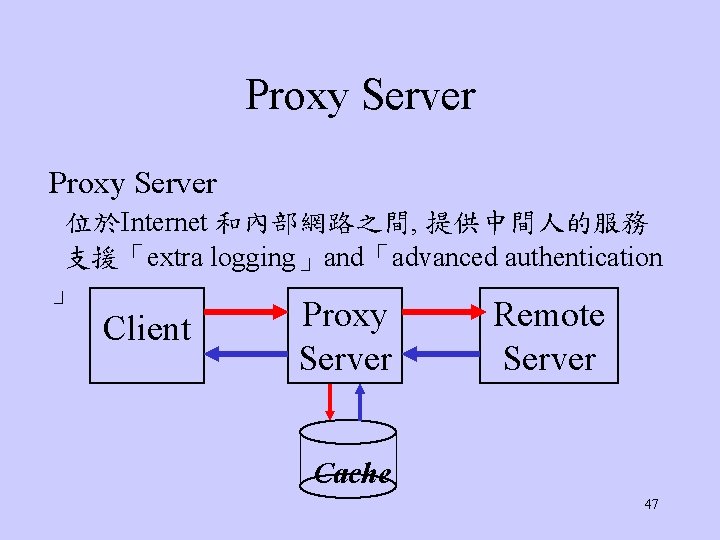
Proxy Server 位於Internet 和內部網路之間, 提供中間人的服務 支援「extra logging」and「advanced authentication 」 Client Proxy Server Remote Server Cache 47
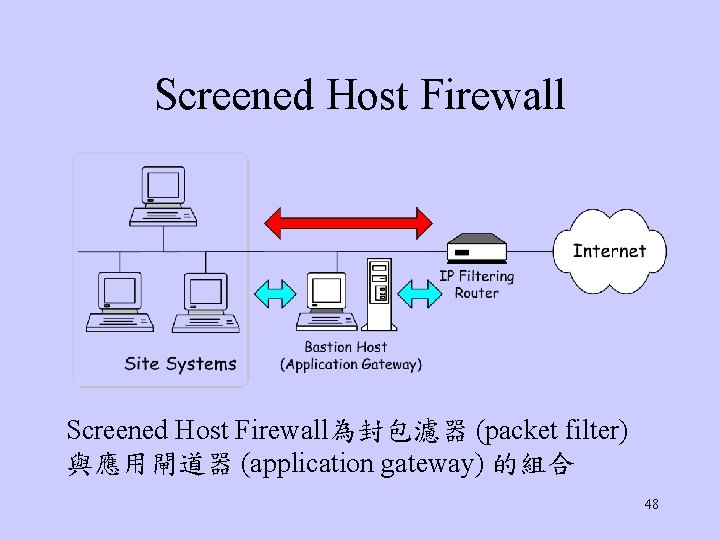
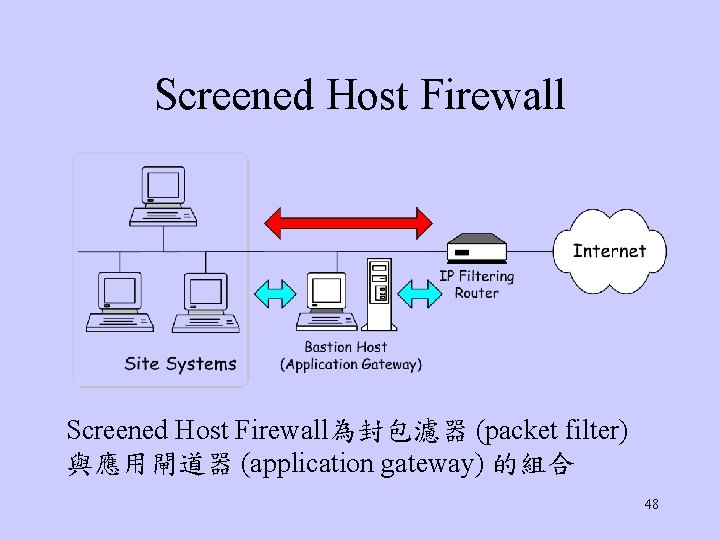
Screened Host Firewall為封包濾器 (packet filter) 與應用閘道器 (application gateway) 的組合 48
Screened Host Firewall n 優點 èMore flexibility. èRouter filtering rules are simplified. n 缺點 èLess security. (packet can go directly inside) 50
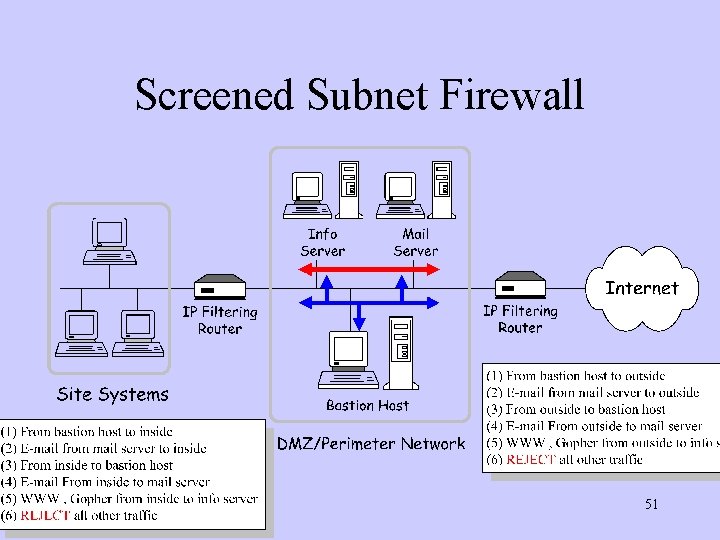
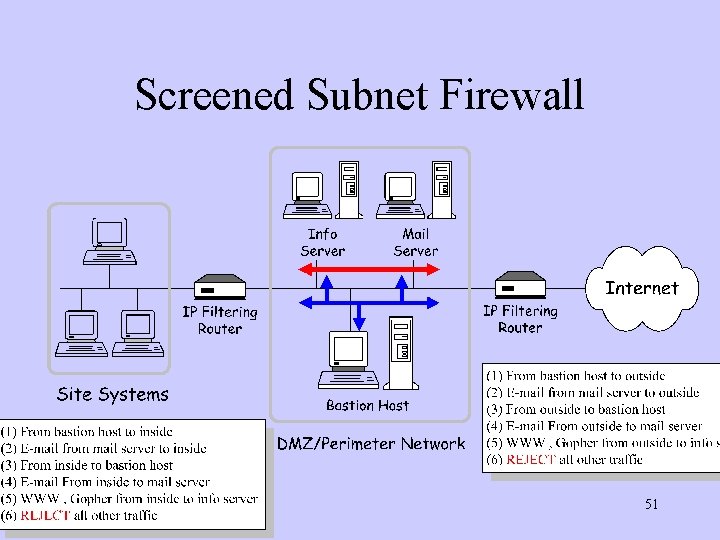
Screened Subnet Firewall 51
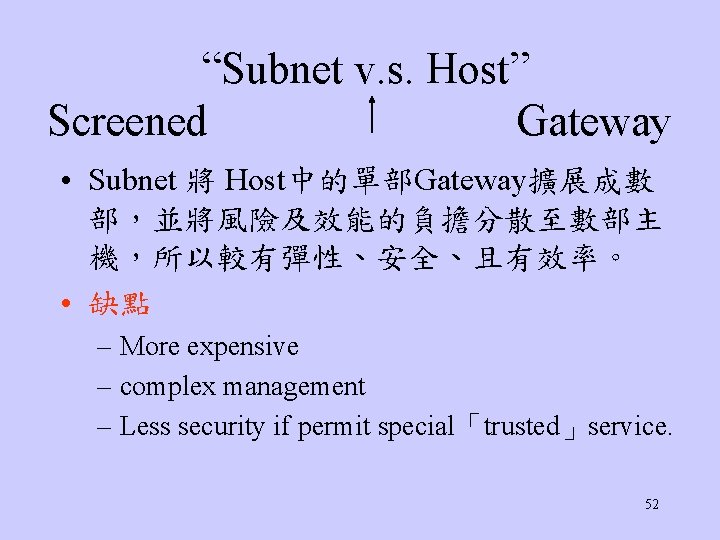
“Subnet v. s. Host” Screened Gateway • Subnet 將 Host中的單部Gateway擴展成數 部,並將風險及效能的負擔分散至數部主 機,所以較有彈性、安全、且有效率。 • 缺點 – More expensive – complex management – Less security if permit special「trusted」service. 52
What Can’t a Firewall Protect Against • Firewalls can’t protect against attacks that don’t go through the firewall , or rules that make a leak. • Firewalls can’t protect against「data driven 」 attacks , like「Virus」. 53

參考資料 • Electronic Commerce : A Manager’s Guide Kalakota & Whinston • 碁峰: 網際網路安全手冊 • 網站 –http: //www. rsasecurity. com/ –http: //khchu. virtualave. net/index. htm 56