LowCost Untraceable Authentication Protocols for RFID Yong Ki
Low-Cost Untraceable Authentication Protocols for RFID Yong Ki Lee, Lejla Batina, Dave Singelée, Ingrid Verbauwhede BCRYPT workshop on RFID Security February 5, 2010, Leuven
Outline of the talk n Challenges in RFID networks n n n n Security problems Privacy problems Cryptographic building blocks ECC-based authentication protocols Search protocol Hardware architecture Conclusion

RFID technology n 1. 2. 3. Radio Frequency Identification as we explain it to Dave’s tech-savvy grandmother: Passive tag Battery assisted (BAP) Active tag with onboard power source
RFID applications n n n n Asset tracking Barcode replacement RFID passports Mobile credit card payment systems Transportation payment systems Sporting events (timing / tracing) Animal identification …
RFID security problems (I) n Impersonation attacks n n Genuine readers Malicious tags => Tag-to-server authentication
RFID security problems (II) n n n Eavesdropping Replay attacks Man-in-the-middle attacks Cloning Side-channel attacks …
![RFID privacy problems (I) Mr. Jones in 2020 [A. Juels. RSA Laboratories] RFID privacy problems (I) Mr. Jones in 2020 [A. Juels. RSA Laboratories]](http://slidetodoc.com/presentation_image_h2/a981b9bb1263f5be40154dc16e1d1d8c/image-7.jpg)
RFID privacy problems (I) Mr. Jones in 2020 [A. Juels. RSA Laboratories]
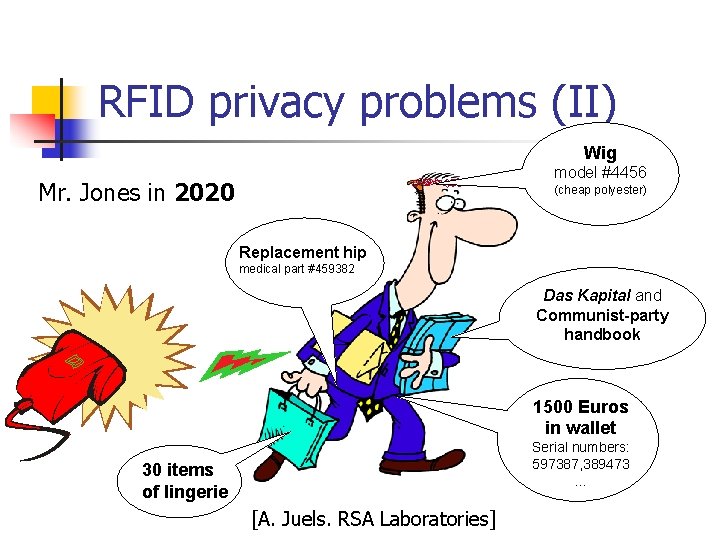
RFID privacy problems (II) Wig model #4456 Mr. Jones in 2020 (cheap polyester) Replacement hip medical part #459382 Das Kapital and Communist-party handbook 1500 Euros in wallet Serial numbers: 597387, 389473 … 30 items of lingerie [A. Juels. RSA Laboratories]
RFID privacy problems (III) n RFID Privacy problem n n Malicious readers Genuine tags => Untraceability
RFID privacy problems (IV) n Untraceability n n Inequality of two tags: the (in)equality of two tags must be impossible to determine Theoretical framework of Vaudenay [ASIACRYPT ‘ 07]: n n Narrow vs wide privacy Weak vs strong privacy
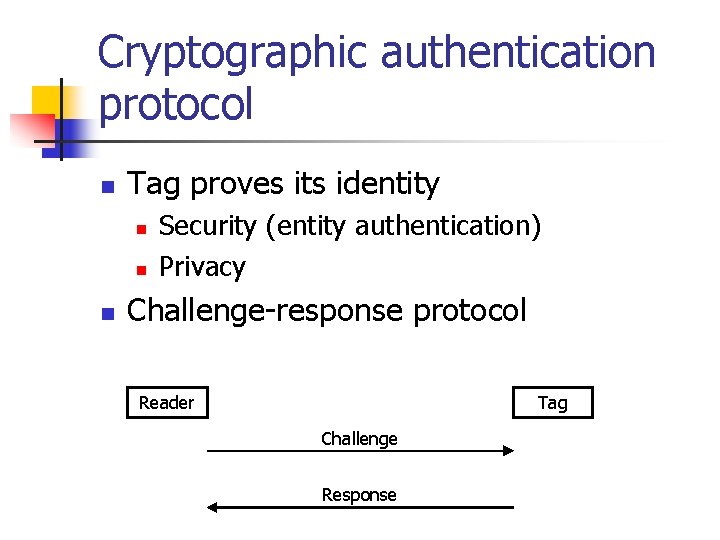
Cryptographic authentication protocol n Tag proves its identity n n n Security (entity authentication) Privacy Challenge-response protocol Reader Tag Challenge Response
Technological requirements n n Scalability Implementation issues n Cheap implementation n n Memory Gate area Lightweight Efficient => Influence on cryptographic building blocks
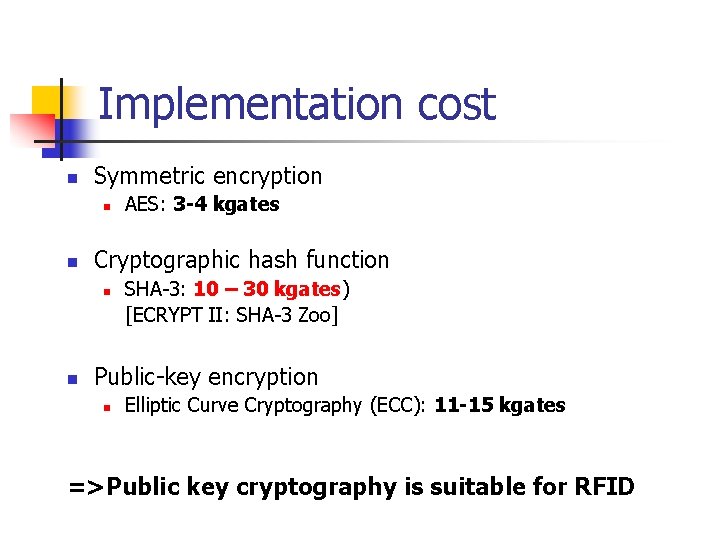
Implementation cost n Symmetric encryption n n Cryptographic hash function n n AES: 3 -4 kgates SHA-3: 10 – 30 kgates) [ECRYPT II: SHA-3 Zoo] Public-key encryption n Elliptic Curve Cryptography (ECC): 11 -15 kgates =>Public key cryptography is suitable for RFID
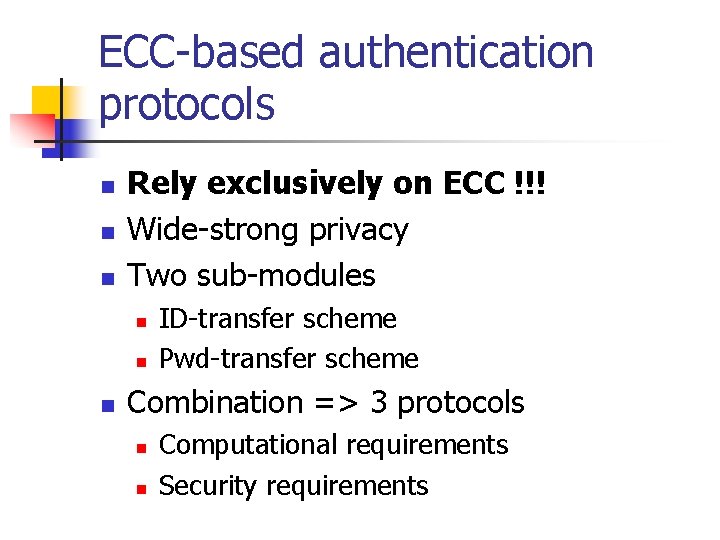
ECC-based authentication protocols n n n Rely exclusively on ECC !!! Wide-strong privacy Two sub-modules n n n ID-transfer scheme Pwd-transfer scheme Combination => 3 protocols n n Computational requirements Security requirements
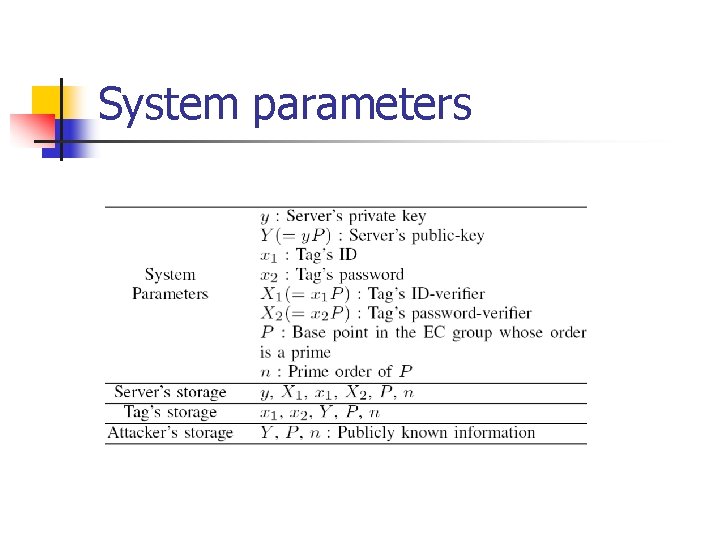
System parameters
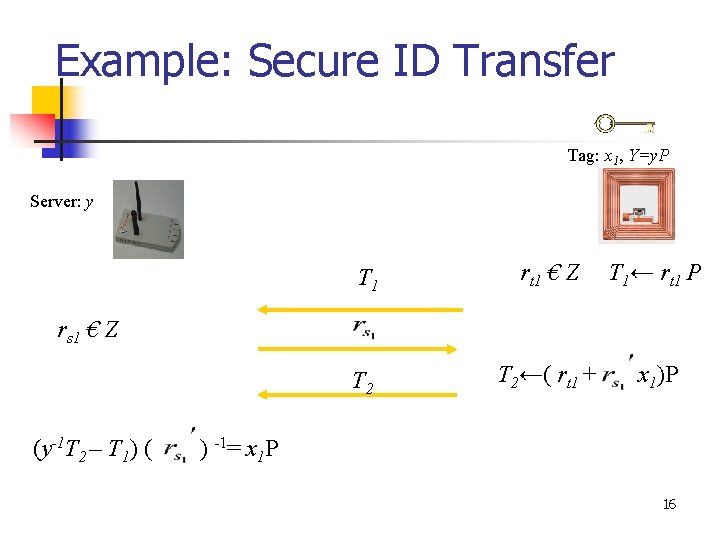
Example: Secure ID Transfer Tag: x 1, Y=y. P Server: y T 1 rt 1 € Z T 1← rt 1 P T 2←( rt 1 + x 1)P rs 1 € Z (y-1 T 2 – T 1) ( ) -1= x 1 P 16
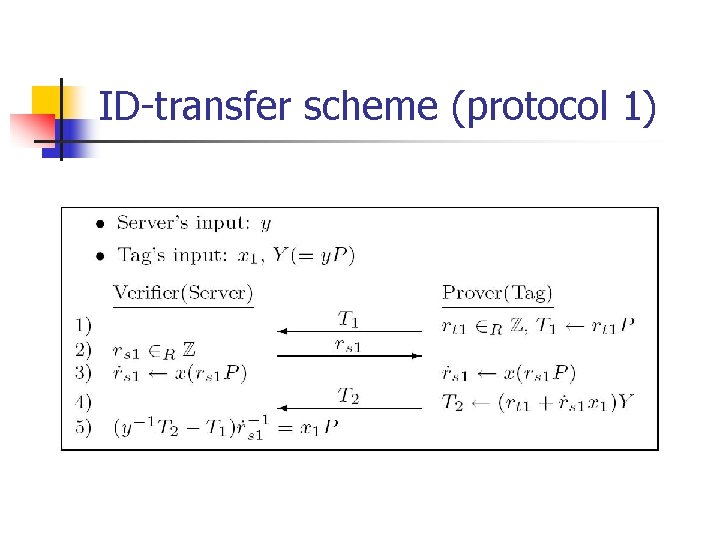
ID-transfer scheme (protocol 1)
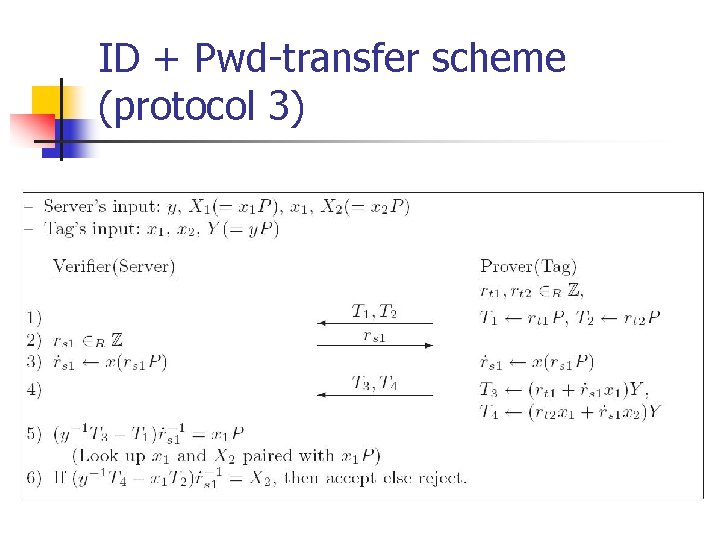
ID + Pwd-transfer scheme (protocol 3)
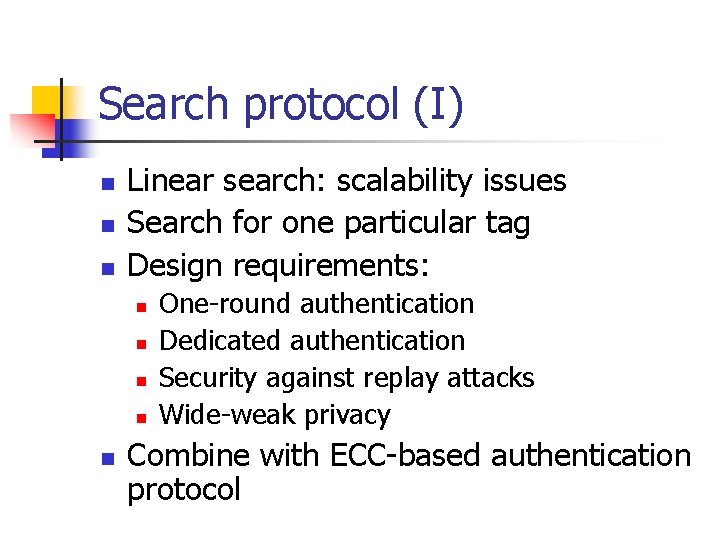
Search protocol (I) n n n Linear search: scalability issues Search for one particular tag Design requirements: n n n One-round authentication Dedicated authentication Security against replay attacks Wide-weak privacy Combine with ECC-based authentication protocol
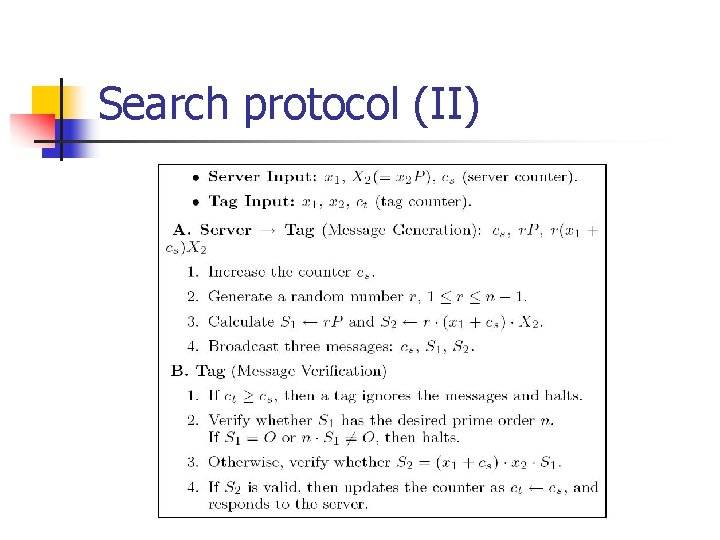
Search protocol (II)
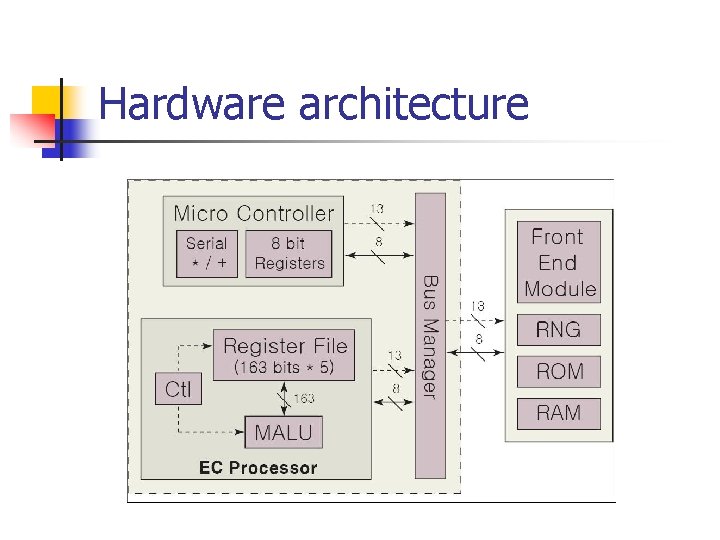
Hardware architecture
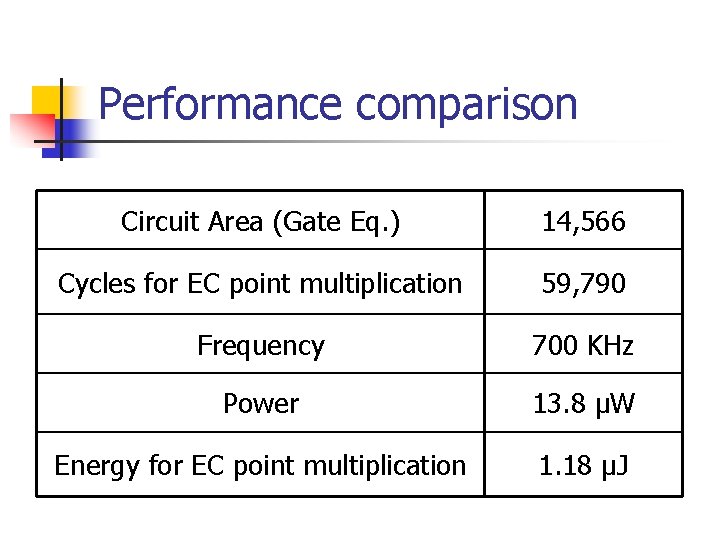
Performance comparison Circuit Area (Gate Eq. ) 14, 566 Cycles for EC point multiplication 59, 790 Frequency 700 KHz Power 13. 8 µW Energy for EC point multiplication 1. 18 µJ
Conclusion n n n Security & privacy in RFID networks Challenging research problem Public-key cryptography is suitable for RFID tags ECC hardware implementation Wide-strong authentication protocols Search protocol
Questions? ?
EXTRA SLIDES
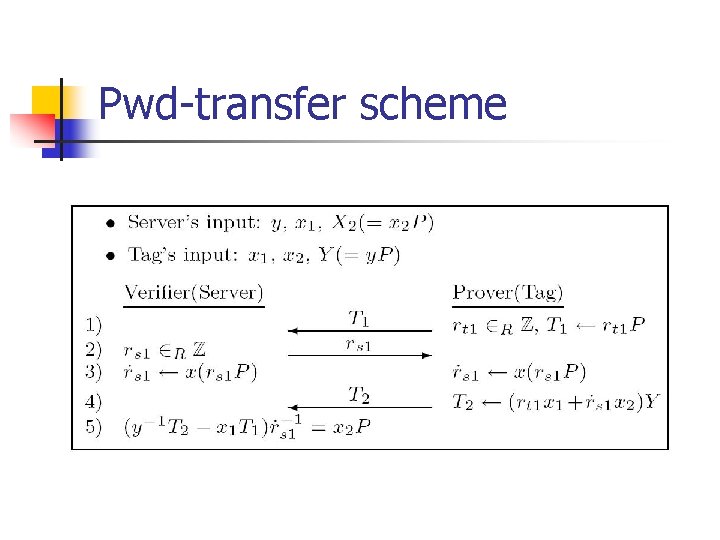
Pwd-transfer scheme
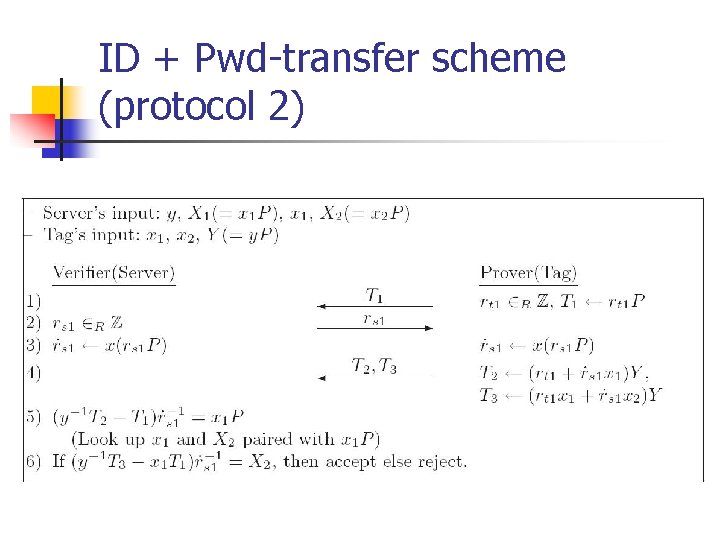
ID + Pwd-transfer scheme (protocol 2)
- Slides: 27