libpcap and Analyze Speaker PoChou Chen Date 2007
libpcap and Analyze Speaker: Po-Chou Chen Date: 2007. 10. 11
Outline API (Application Program Interface) n Analyze RTP and SIP packet n Demo n Reference n
pcap_lookupdev() char *pcap_lookupdev(char *errbuf) n return a pointer to a network device suitable for use with pcap_open_live() and pcap_lookupnet() n return NULL indicates an error n
pcap_lookupnet() int pcap_lookupnet( const char *device, bpf_u_int 32 *netp, bpf_u_int 32 *maskp, char *errbuf) n determine the network number and mask associated with the network device n return -1 indicates an error n demo: lookupdev_net. c n
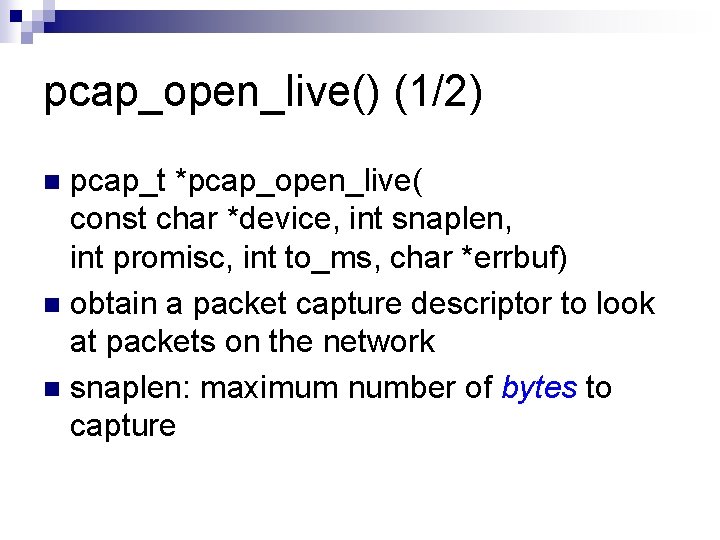
pcap_open_live() (1/2) pcap_t *pcap_open_live( const char *device, int snaplen, int promisc, int to_ms, char *errbuf) n obtain a packet capture descriptor to look at packets on the network n snaplen: maximum number of bytes to capture n
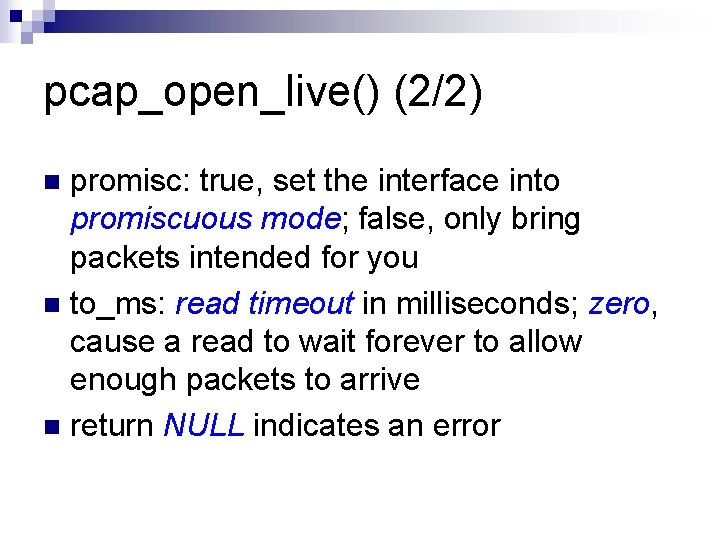
pcap_open_live() (2/2) promisc: true, set the interface into promiscuous mode; false, only bring packets intended for you n to_ms: read timeout in milliseconds; zero, cause a read to wait forever to allow enough packets to arrive n return NULL indicates an error n
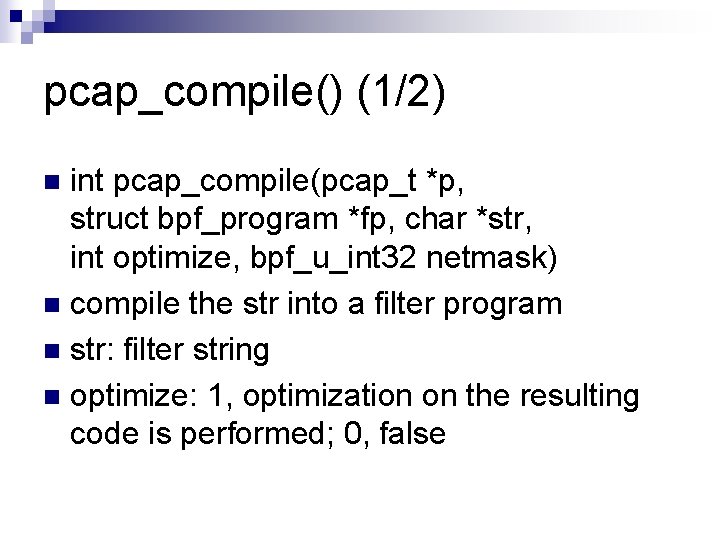
pcap_compile() (1/2) int pcap_compile(pcap_t *p, struct bpf_program *fp, char *str, int optimize, bpf_u_int 32 netmask) n compile the str into a filter program n str: filter string n optimize: 1, optimization on the resulting code is performed; 0, false n
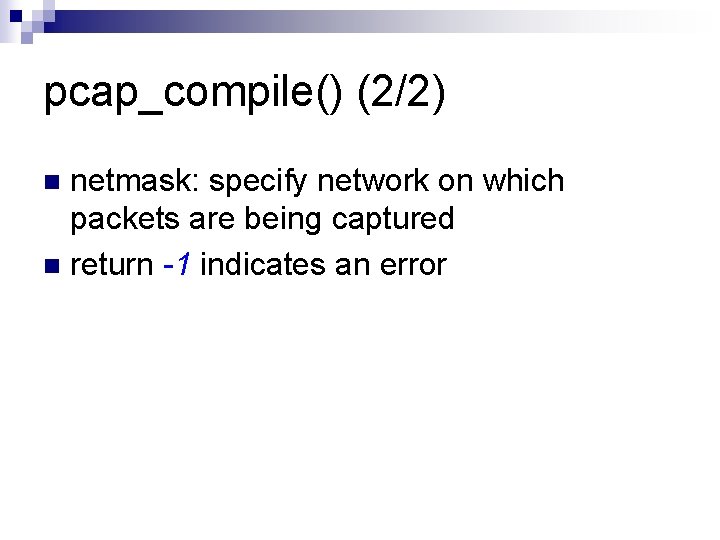
pcap_compile() (2/2) netmask: specify network on which packets are being captured n return -1 indicates an error n
pcap_setfilter() int pcap_setfilter(pcap_t *p, struct bpf_program *fp) n specify a filter program n return -1 indicates an error n
pcap_loop() int pcap_loop(pcap_t *p, int cnt, pcap_handler callback, u_char *user) n cnt: packet number; -1, loop until error n callback: callback function n ¨ void got_packet(u_char *args, const struct pcap_pkthdr *header, const u_char *packet)
got_packet() n n n void got_packet(u_char *args, const struct pcap_pkthdr *header, const u_char *packet); struct pcap_pkthdr { struct timeval ts; bpf_u_int 32 caplen; bpf_u_int 32 len; }; demo: pcap_filter. c
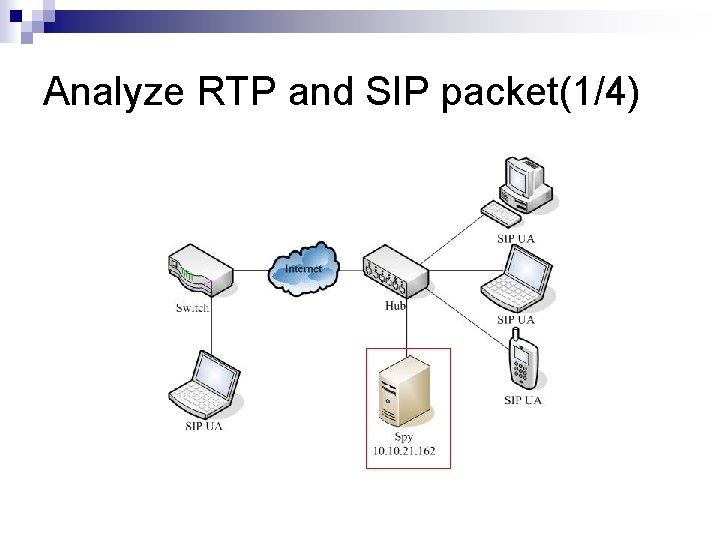
Analyze RTP and SIP packet(1/4)
![Analyze RTP and SIP packet(2/4) n n n n n static const char *sip_methods[] Analyze RTP and SIP packet(2/4) n n n n n static const char *sip_methods[]](http://slidetodoc.com/presentation_image_h/d06d16678a35e5ad4cec329044f9e285/image-13.jpg)
Analyze RTP and SIP packet(2/4) n n n n n static const char *sip_methods[] = { "<Invalid method>", /* Pad so that the real methods start at index 1 */ "ACK", "BYE", "CANCEL", "DO", "INFO", "INVITE", "MESSAGE", "NOTIFY", "OPTIONS", "PRACK", "QAUTH", "REFER", "REGISTER", "SPRACK", "SUBSCRIBE", "UPDATE", "PUBLISH", "SIP/2. 0" n n };
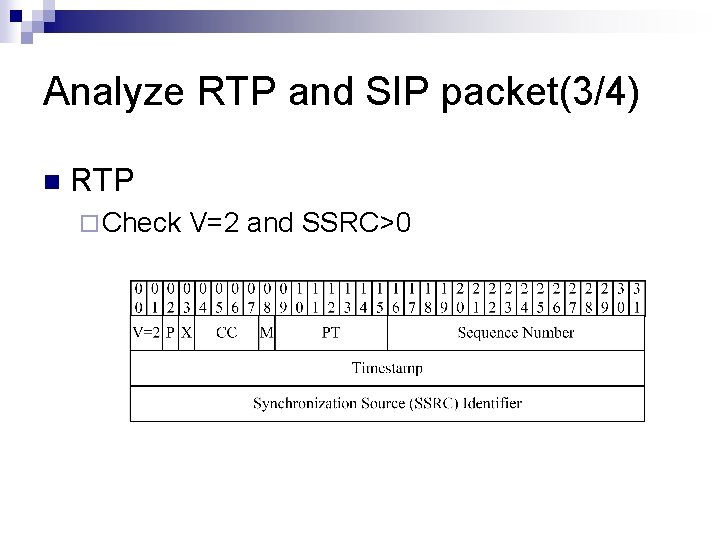
Analyze RTP and SIP packet(3/4) n RTP ¨ Check V=2 and SSRC>0
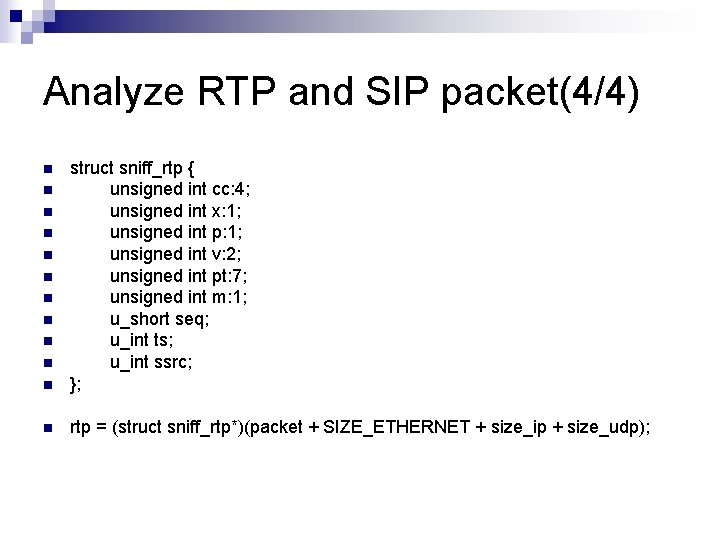
Analyze RTP and SIP packet(4/4) n struct sniff_rtp { unsigned int cc: 4; unsigned int x: 1; unsigned int p: 1; unsigned int v: 2; unsigned int pt: 7; unsigned int m: 1; u_short seq; u_int ts; u_int ssrc; }; n rtp = (struct sniff_rtp*)(packet + SIZE_ETHERNET + size_ip + size_udp); n n n n n
Demo n analyzer. c
Reference n Wireshark Wiki ¨ http: //wiki. wireshark. org/ n libpcap ¨ http: //www. tcpdump. org/
- Slides: 17