Lecture 6 Deadlocks Outline Resource Shareable and Nonshareable
Lecture 6 Deadlocks Outline: • • • Resource Shareable and Non-shareable Resources Introduction to deadlocks The Deadlock Problem Examples of Deadlock Conditions Under which a Deadlock Occurs Deadlock Modeling Methods For Handling Deadlock Problem - Deadlock detection and recovery - Deadlock avoidance - Deadlock prevention - Just ignore the problem Other issues - Bankers’ Algorithm 1
Resources (1) • Examples of computer resources – Printers – Disk drives – Tables • Processes need access to resources in reasonable order Example: • Suppose a process holds resource A and requests resource B – at same time another process holds B and requests A – both are blocked and remain so. 2
Example: Deadlock Scenario • Suppose two processes each want to record a scanned document on a CD. • Process A requests permission to use the scanner and is granted it. • Process B is programmed differently and requests the CD recorder first and is also granted it. • Now A asks for the CD recorder, but the request is denied until B releases it. • Unfortunately, instead of releasing the CD recorder B asks for the scanner. • At this point both processes (A and B) are blocked and will remain so forever. 3
Shareable and Non-shareable Resources • System resource may be classified as shareable and non-shareable. • A resource is said to be shareable if it can be used by several processes concurrently. • A resource is said to be non-shareable if its use is restricted to one process at a time. 4
Shareable and Non-shareable Resources • Examples of shareable resources are: 1. Memory 2. Drum 3. Disk. • Examples of non-shareable resources are: 1. the line printer 5. slot in the system internal table 2. a memory location 3. magnetic tape or tape drive 4. a card reader 5
Resources (2) • Deadlocks occur when … – processes are granted exclusive access to devices – we refer to these devices generally as resources • Preemptable resources – can be taken away from a process with no ill effects • Non-preemptable resources – will cause the process to fail if taken away 6
Resources (3) • Sequence of events required to use a resource: 1. request the resource 2. use the resource 3. release the resource Must wait if request is denied: • – – requesting process may be blocked may fail with error code 7
Introduction to Deadlocks Deadlock can be defined formally as follows: • This comes about when several processes compete for resources and a situation arises in which no process can continue because the resources each one requires are held up by another. OR • A set of processes is deadlocked if each process in the set is waiting for an event that only another process in the set can cause. OR • A set of blocked processes each holding a resource and waiting to acquire a resource held by another process in the set. 8
Deadlock Problem • Usually the event is release of a currently held resource. • None of the processes can … – run – release resources – be awakened – Example: – System has 2 tape drives. P 1 and P 2 each hold one tape drive and each needs the other one. 9
Examples of Deadlock • A Traffic Deadlock – This occurs when a number of vehicles are attempting to drive through a very busy intersection. • River Crossing Using Stepping Stones – with a restriction that at most a foot can be on each stepping stone at a time. • A Single Resource Deadlock – This occurs because of the normal contention for dedicated resources. This is often referred to as the circular wait state. 10
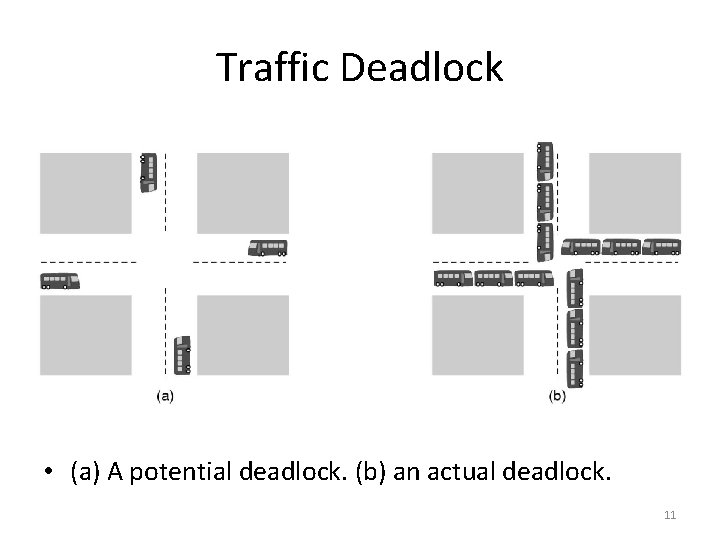
Traffic Deadlock • (a) A potential deadlock. (b) an actual deadlock. 11
Conditions Under which a Deadlock Occurs Mutual Exclusion Condition 1. • each resource is either currently assigned to exactly one process or is available Hold and Wait Condition 2. • Processes currently holding resources granted earlier can request new resources No Preemption Condition 3. • 4. • previously granted resources cannot forcibly be taken away from a process. - they must be explicitly released by the process holding them. Circular Wait Condition must be a circular chain of two or more processes - each is waiting for resource held by next member of the chain. 12
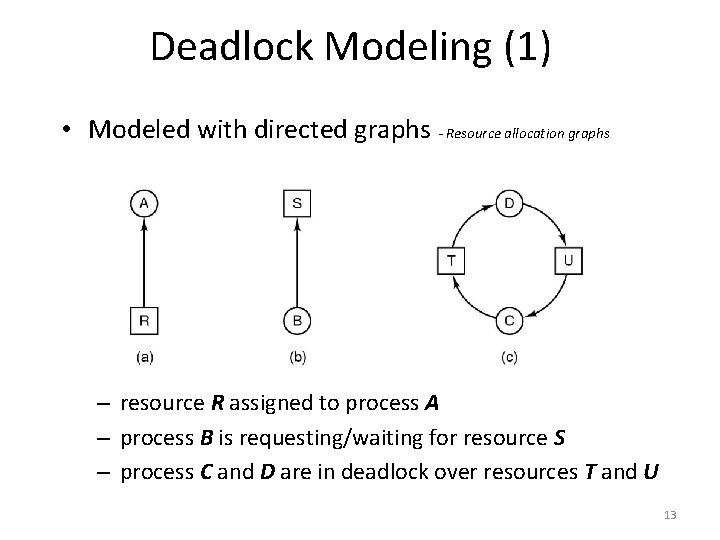
Deadlock Modeling (1) • Modeled with directed graphs - Resource allocation graphs – resource R assigned to process A – process B is requesting/waiting for resource S – process C and D are in deadlock over resources T and U 13
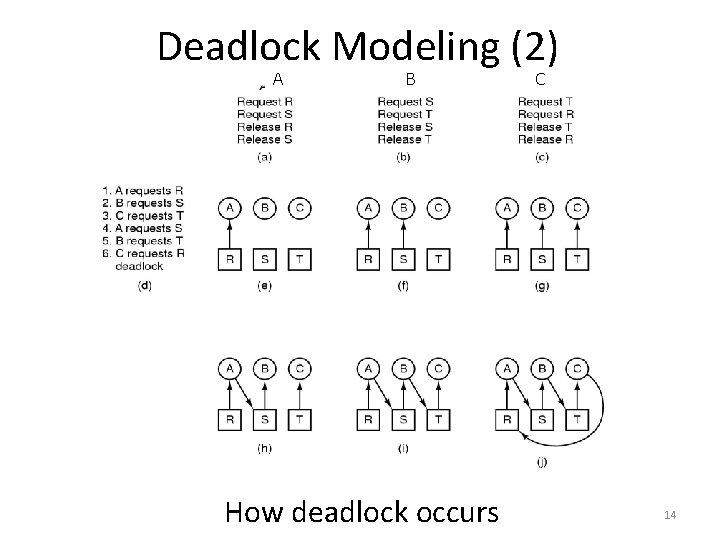
Deadlock Modeling (2) A B How deadlock occurs C 14
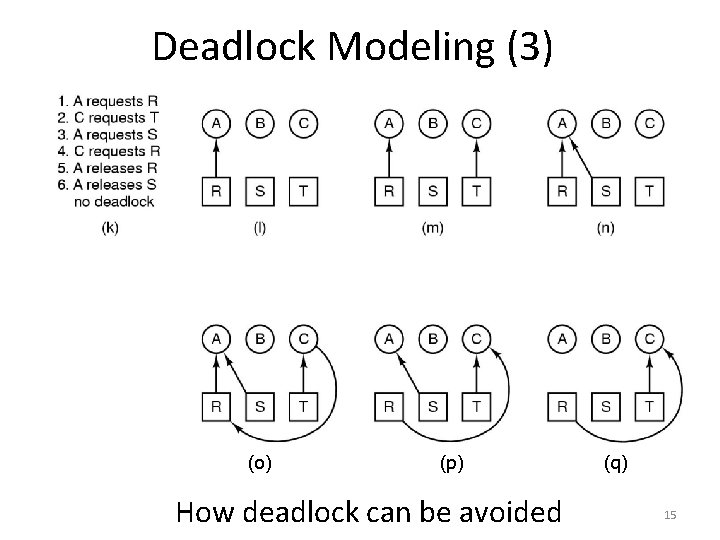
Deadlock Modeling (3) (o) (p) How deadlock can be avoided (q) 15
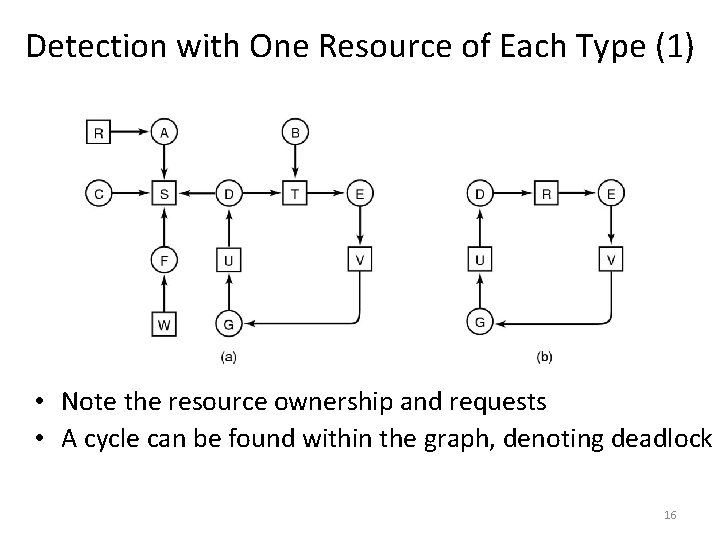
Detection with One Resource of Each Type (1) • Note the resource ownership and requests • A cycle can be found within the graph, denoting deadlock 16
- Slides: 16