Introduction v Images have been widely used in
Introduction v Images have been widely used in our daily life. v The image security has become an important issue in current computer world. v Image cryptology is a very useful tool to defend the information security. 2
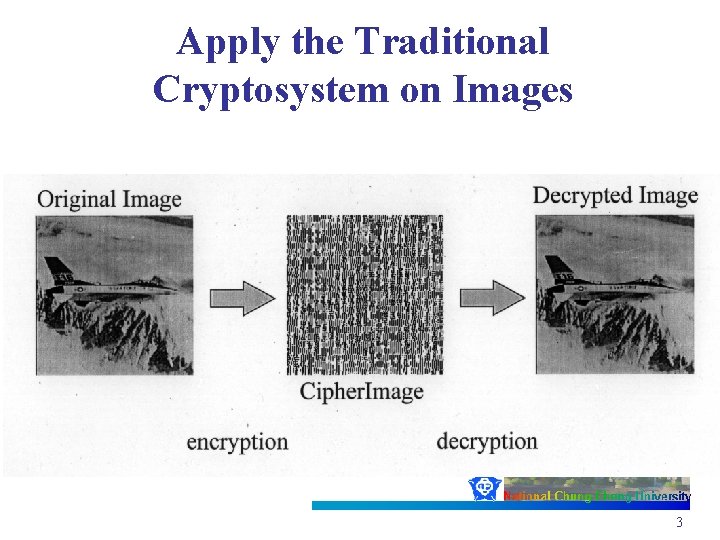
Apply the Traditional Cryptosystem on Images 3
Problems • The cipherimage is meaningless. Image Camouflage(影像偽裝) • Image size is huge Image Compression(影像壓縮) • The decrypted image containing a small distortion is usually acceptable. Vector Quantization (向量量畫編碼法) 4
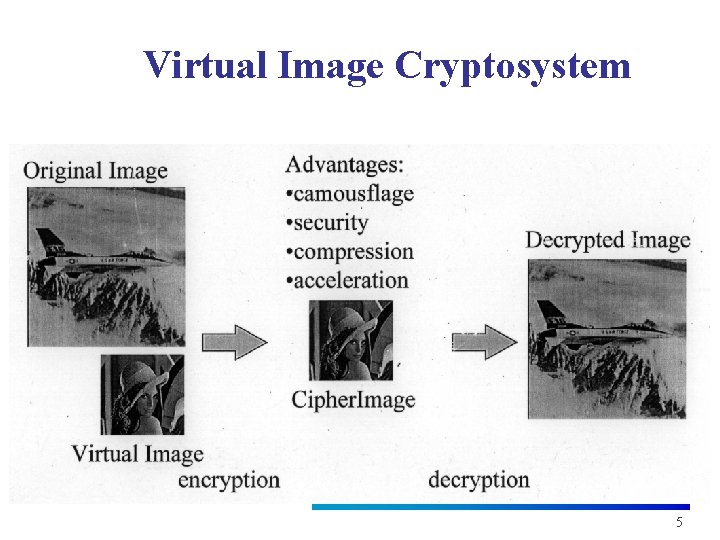
Virtual Image Cryptosystem 5
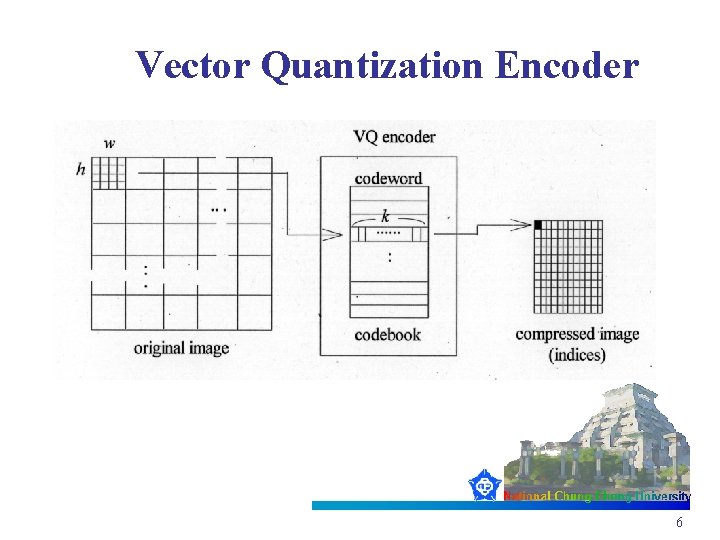
Vector Quantization Encoder 6
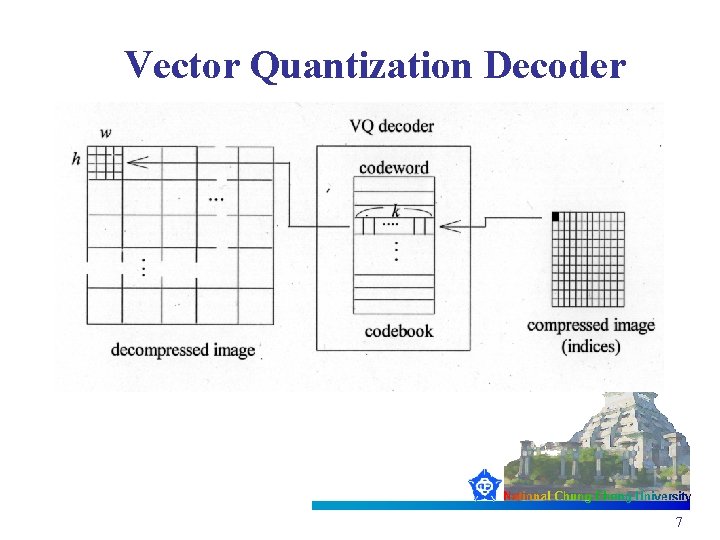
Vector Quantization Decoder 7
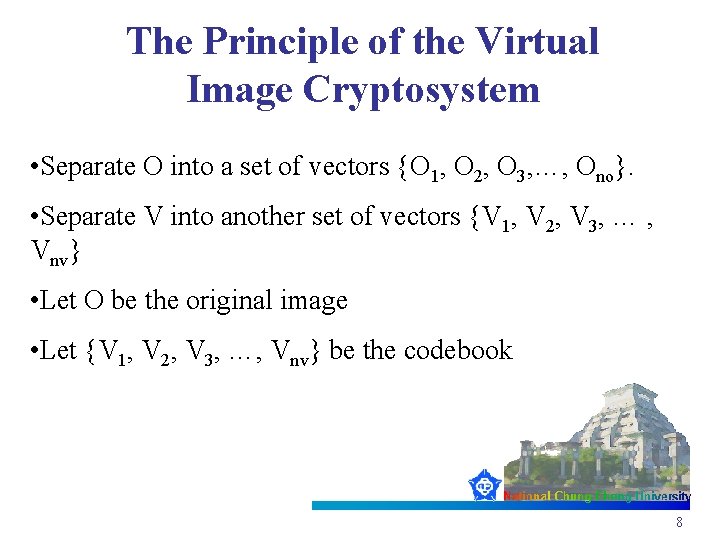
The Principle of the Virtual Image Cryptosystem • Separate O into a set of vectors {O 1, O 2, O 3, …, Ono}. • Separate V into another set of vectors {V 1, V 2, V 3, … , Vnv} • Let O be the original image • Let {V 1, V 2, V 3, …, Vnv} be the codebook 8
Encryption • Randomly generate the transformed-origin G and the project-direction D. • Project {V 1, V 2, V 3, …, Vnv} to D based on G • Sort the projected results, and obtain {{V’ 1, V’ 2, V’ 3, …, V’nv} 9
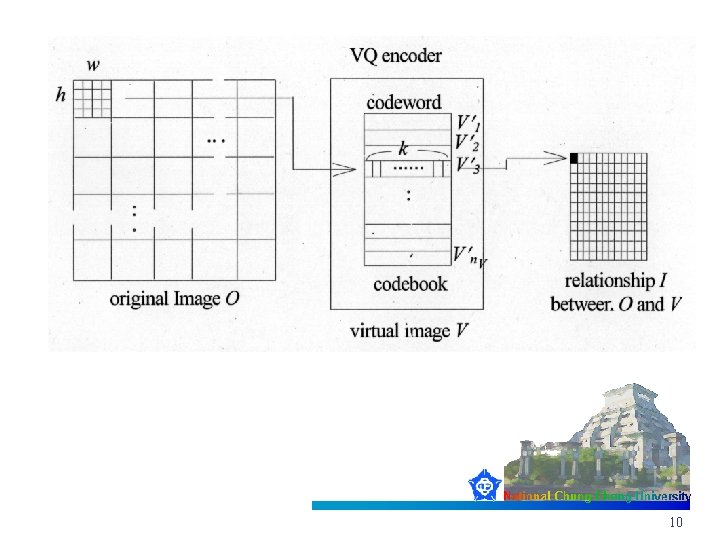
10
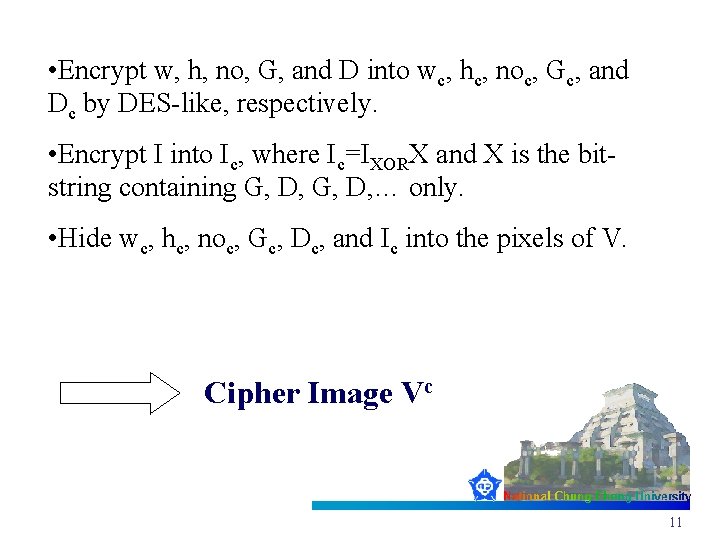
• Encrypt w, h, no, G, and D into wc, hc, noc, Gc, and Dc by DES-like, respectively. • Encrypt I into Ic, where Ic=IXORX and X is the bitstring containing G, D, … only. • Hide wc, hc, noc, Gc, Dc, and Ic into the pixels of V. Cipher Image Vc 11
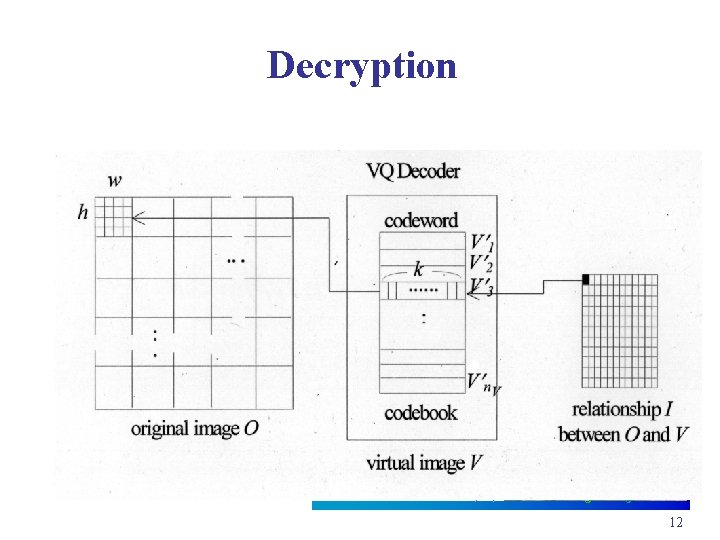
Decryption 12
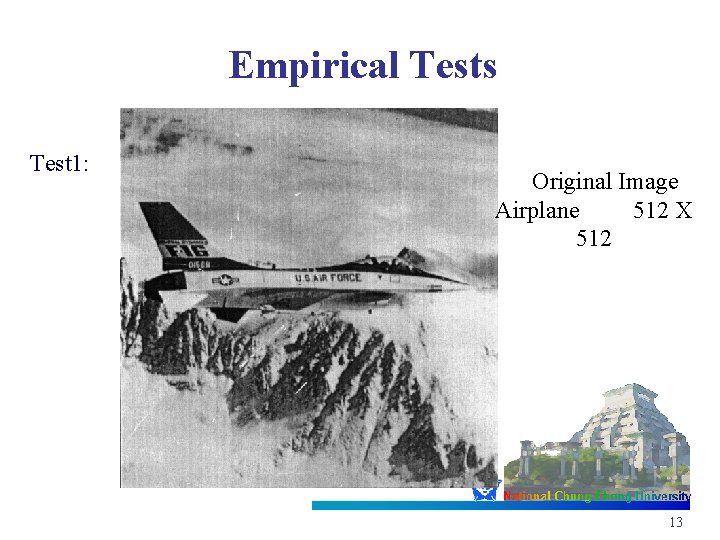
Empirical Tests Test 1: Original Image Airplane 512 X 512 13
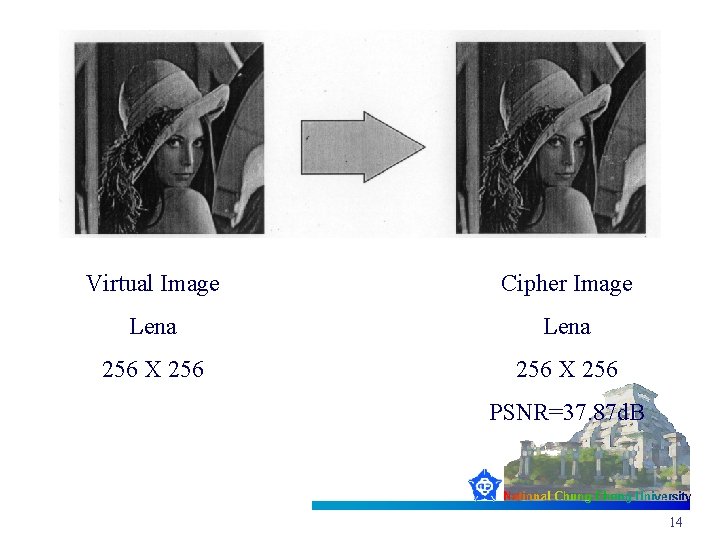
Virtual Image Cipher Image Lena 256 X 256 PSNR=37. 87 d. B 14
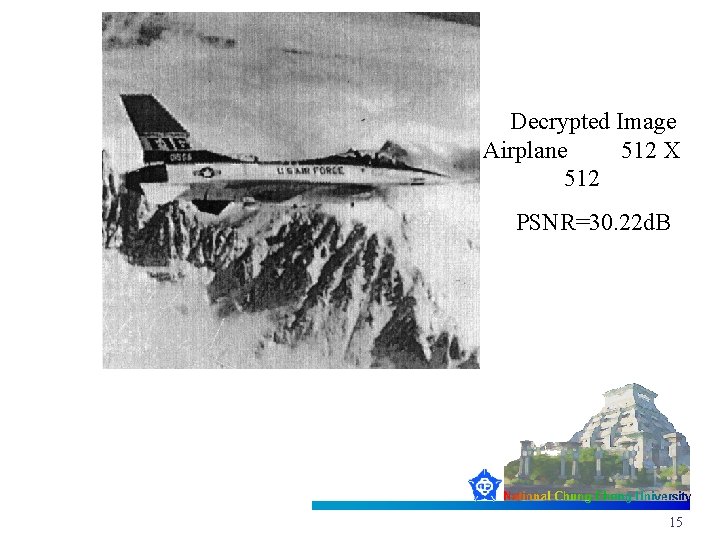
Decrypted Image Airplane 512 X 512 PSNR=30. 22 d. B 15
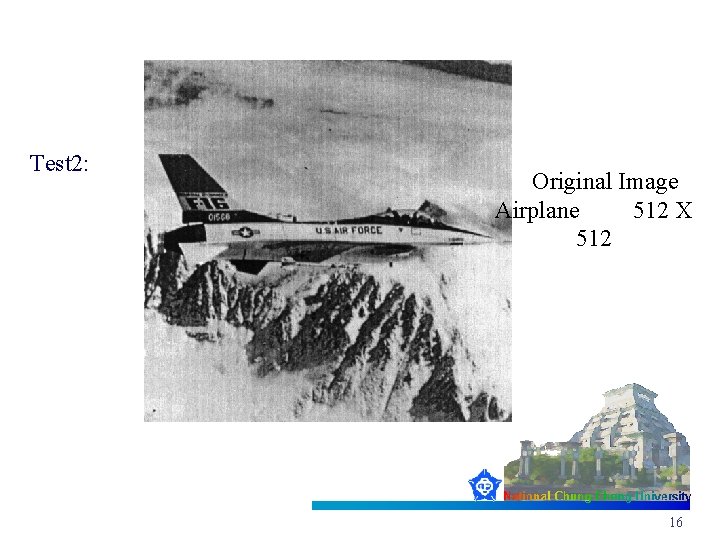
Test 2: Original Image Airplane 512 X 512 16
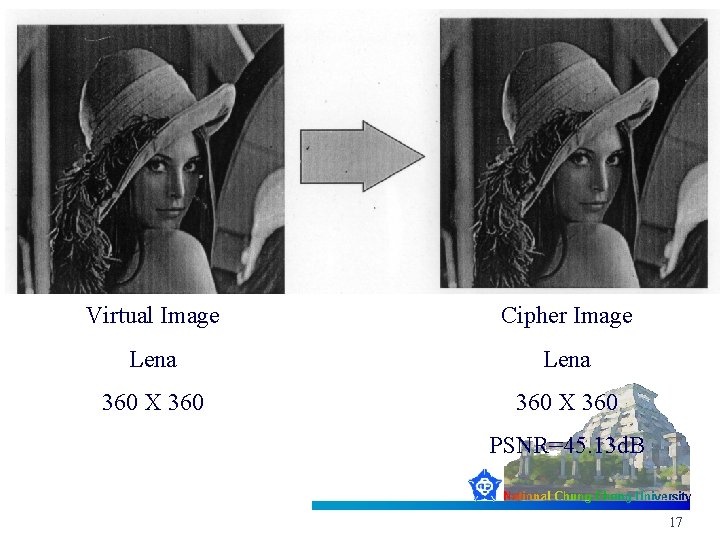
Virtual Image Cipher Image Lena 360 X 360 PSNR=45. 13 d. B 17
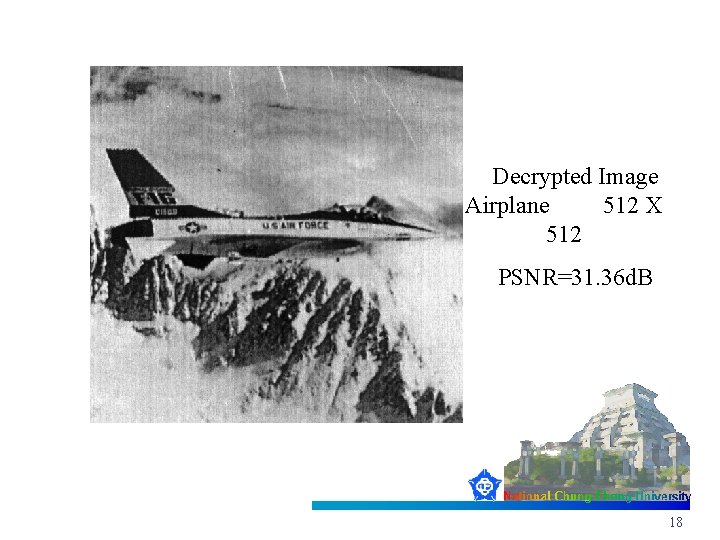
Decrypted Image Airplane 512 X 512 PSNR=31. 36 d. B 18
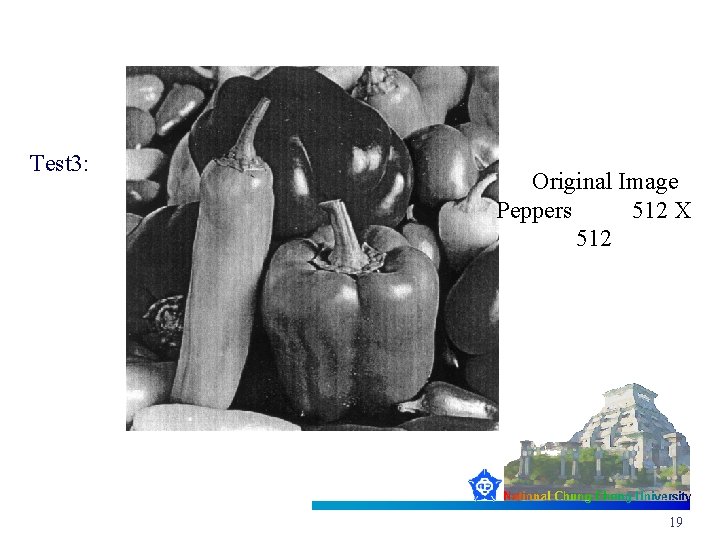
Test 3: Original Image Peppers 512 X 512 19
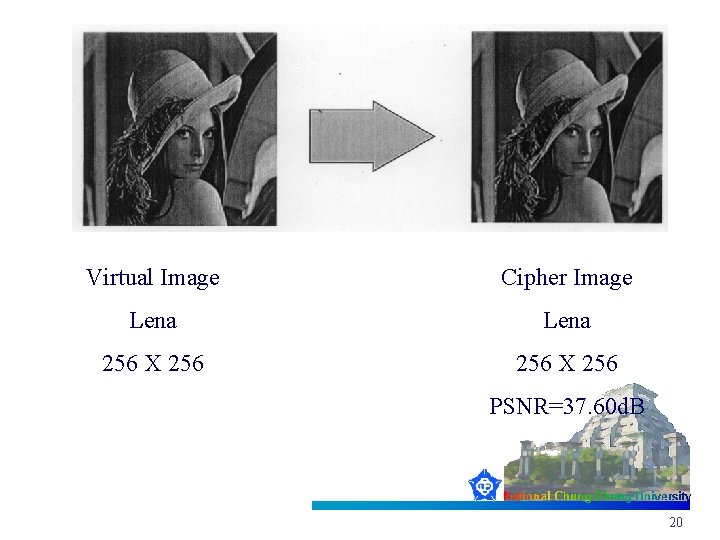
Virtual Image Cipher Image Lena 256 X 256 PSNR=37. 60 d. B 20
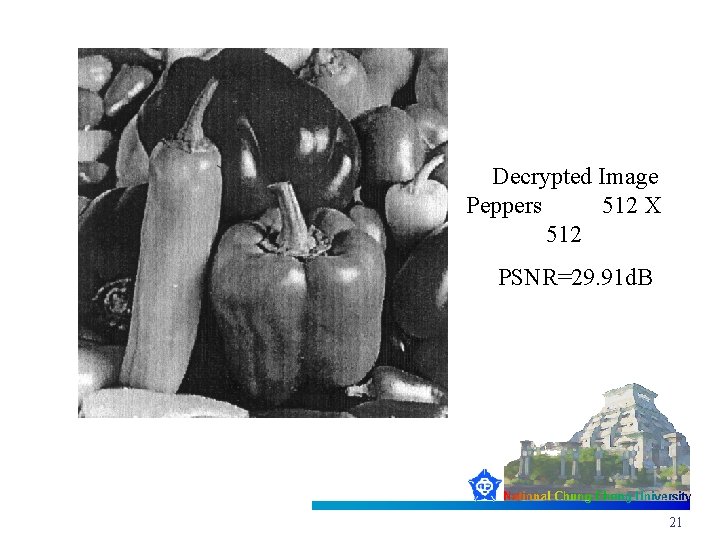
Decrypted Image Peppers 512 X 512 PSNR=29. 91 d. B 21
- Slides: 21