Introduction to the new mainframe LargeScale Commercial Computing

- Slides: 26
Introduction to the new mainframe: Large-Scale Commercial Computing Chapter 4: Integrity and security © Copyright IBM Corp. , 2006. All rights reserved. Click to add text
Introduction to the new mainframe Objectives The ability to: • Describe the security and integrity needs of a large-scale operating environment • Describe the methods for serialization in a multi -user environment • Describe the built-in features that enable integrity and security • Describe the two-phase commit process and why it is needed • Describe the features needed from an add-on security package © Copyright IBM Corp. , 2006. All rights reserved. 2
Introduction to the new mainframe Integrity Data Integrity – Primarily concerned with the accidental damage and recovery of data. System Integrity – Ensures there is no way for any unauthorized program to: Bypass store or fetch protection Bypass security checking Obtain control in an authorized (privileged) state © Copyright IBM Corp. , 2006. All rights reserved. 3
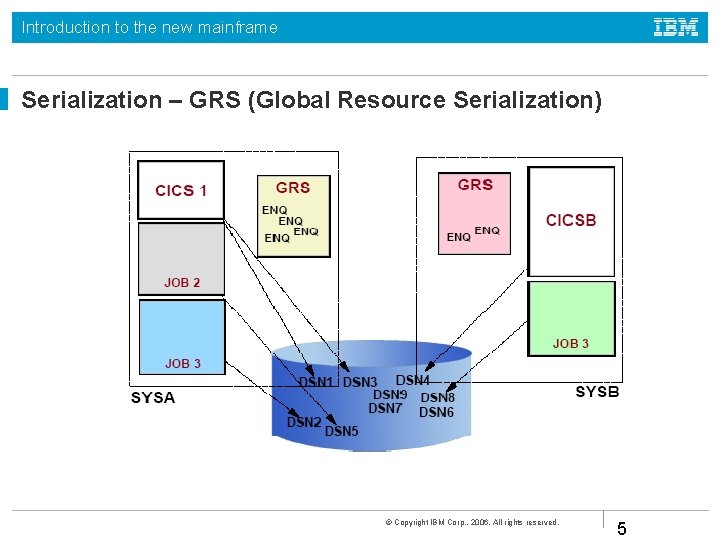
Introduction to the new mainframe Serialization means make a resource to be used on a one-at-atime basis Methods to prevent concurrent updates: Enqueing- wait in queue during execution Reserves- e. g. reserve at startup (before execution) Locks- exclusive or read shared Global Resource Serialization (GRS) – across all systems © Copyright IBM Corp. , 2006. All rights reserved. 4
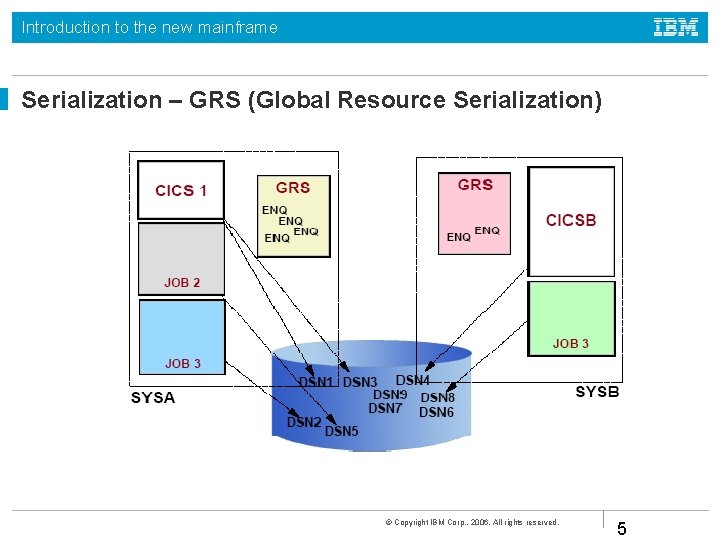
Introduction to the new mainframe Serialization – GRS (Global Resource Serialization) © Copyright IBM Corp. , 2006. All rights reserved. 5
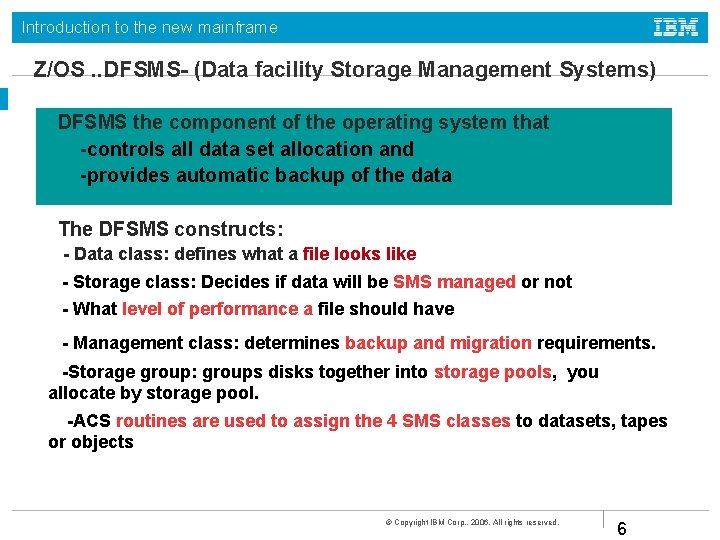
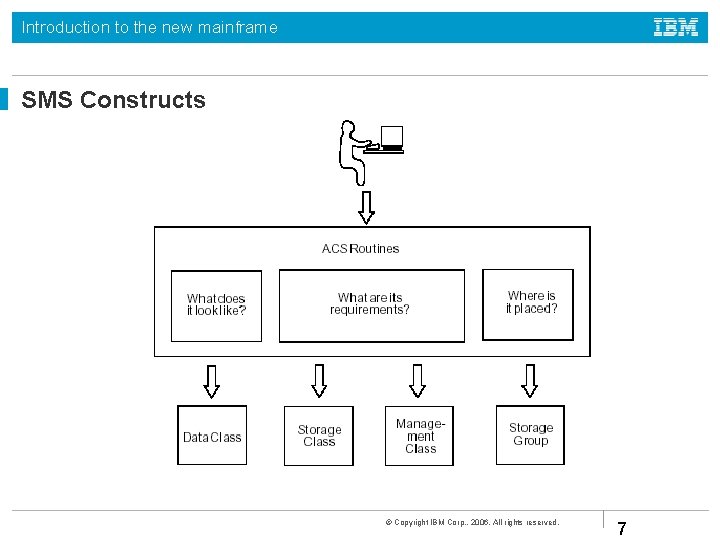
Introduction to the new mainframe Z/OS. . DFSMS- (Data facility Storage Management Systems) DFSMS the component of the operating system that -controls all data set allocation and -provides automatic backup of the data The DFSMS constructs: - Data class: defines what a file looks like - Storage class: Decides if data will be SMS managed or not - What level of performance a file should have - Management class: determines backup and migration requirements. -Storage group: groups disks together into storage pools, you allocate by storage pool. -ACS routines are used to assign the 4 SMS classes to datasets, tapes or objects © Copyright IBM Corp. , 2006. All rights reserved. 6
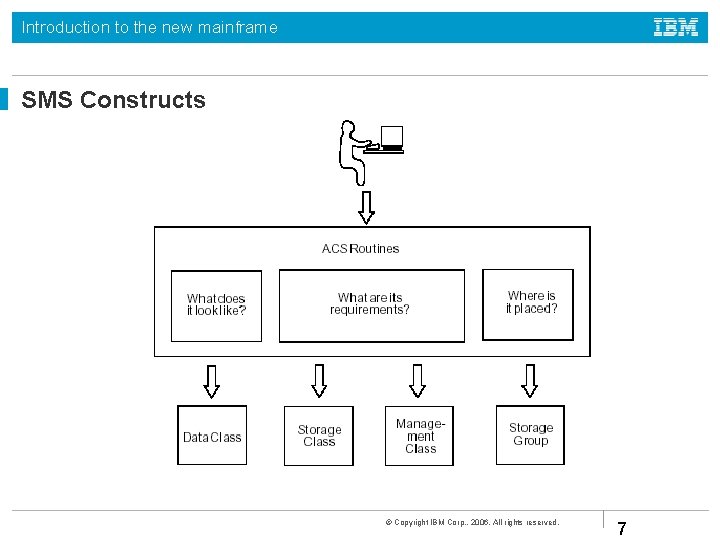
Introduction to the new mainframe SMS Constructs © Copyright IBM Corp. , 2006. All rights reserved. 7
Introduction to the new mainframe Auditing is ensuring that the information processing system complies with the installation policy. Auditing may be: A one time project (e. g; a snap inspection) or An ongoing process System Management Facilities: writes audit records on DASD System Logger: log changes to data © Copyright IBM Corp. , 2006. All rights reserved. 8
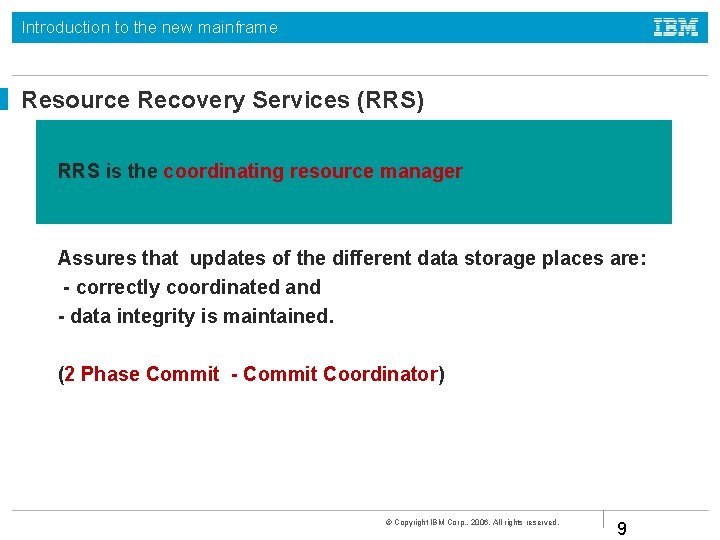
Introduction to the new mainframe Resource Recovery Services (RRS) RRS is the coordinating resource manager Assures that updates of the different data storage places are: - correctly coordinated and - data integrity is maintained. (2 Phase Commit - Commit Coordinator) © Copyright IBM Corp. , 2006. All rights reserved. 9
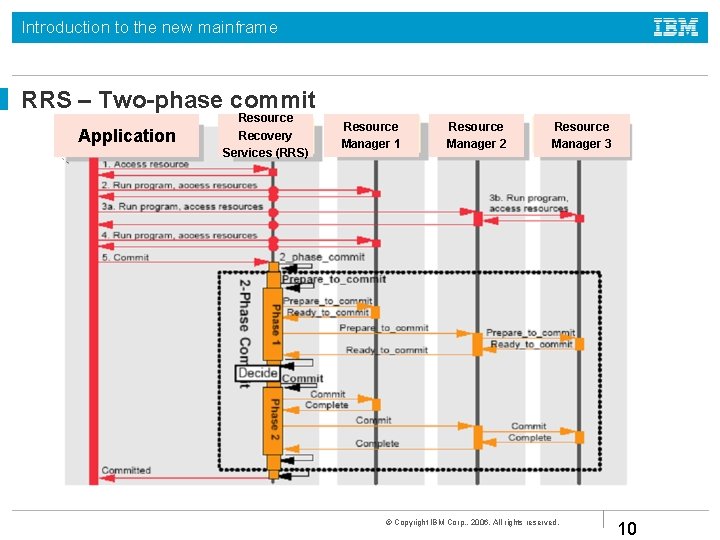
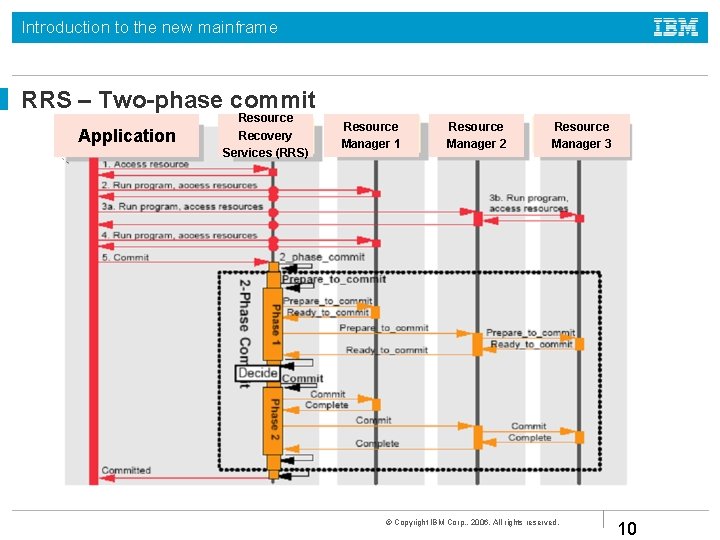
Introduction to the new mainframe RRS – Two-phase commit Application Resource Recovery Services (RRS) Resource Manager 1 Resource Manager 2 Resource Manager 3 © Copyright IBM Corp. , 2006. All rights reserved. 10
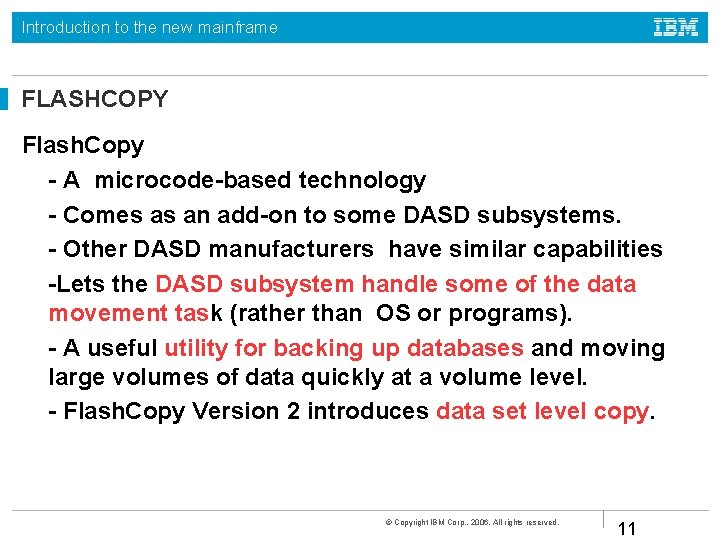
Introduction to the new mainframe FLASHCOPY Flash. Copy - A microcode-based technology - Comes as an add-on to some DASD subsystems. - Other DASD manufacturers have similar capabilities -Lets the DASD subsystem handle some of the data movement task (rather than OS or programs). - A useful utility for backing up databases and moving large volumes of data quickly at a volume level. - Flash. Copy Version 2 introduces data set level copy. © Copyright IBM Corp. , 2006. All rights reserved. 11
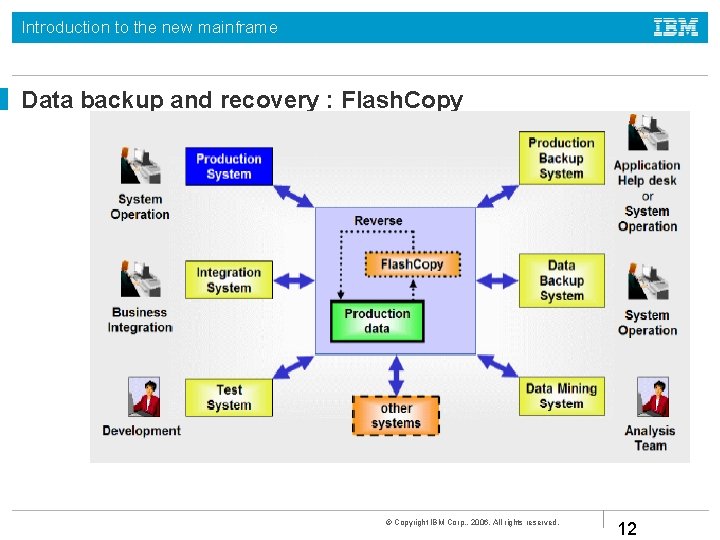
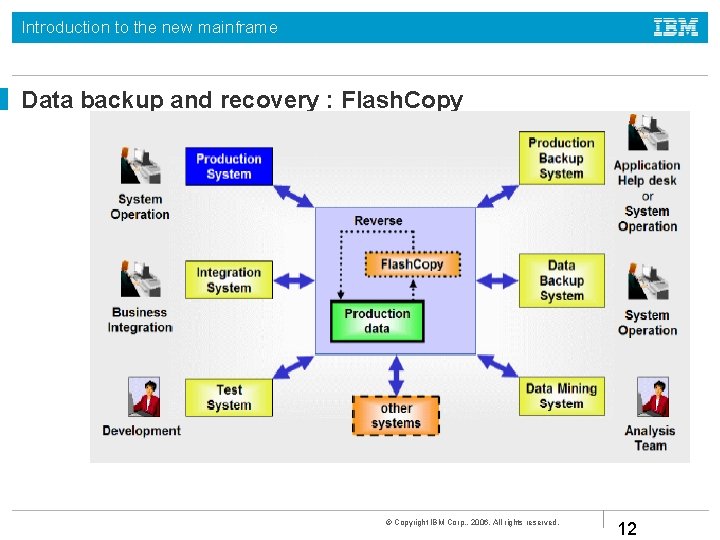
Introduction to the new mainframe Data backup and recovery : Flash. Copy © Copyright IBM Corp. , 2006. All rights reserved. 12
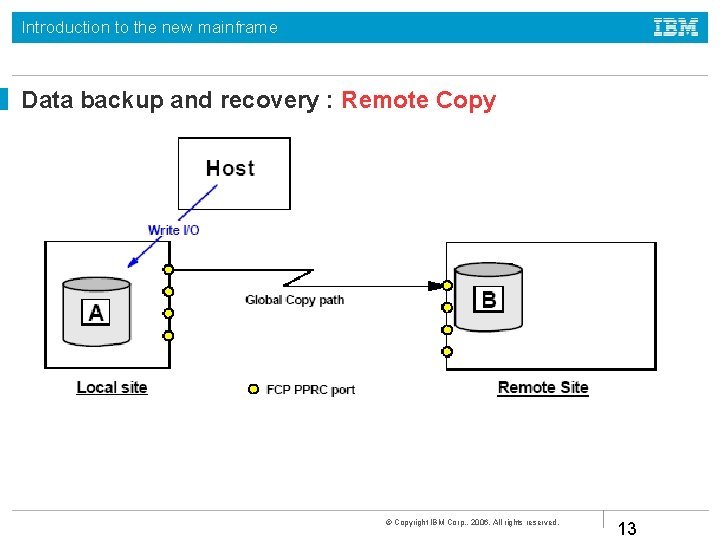
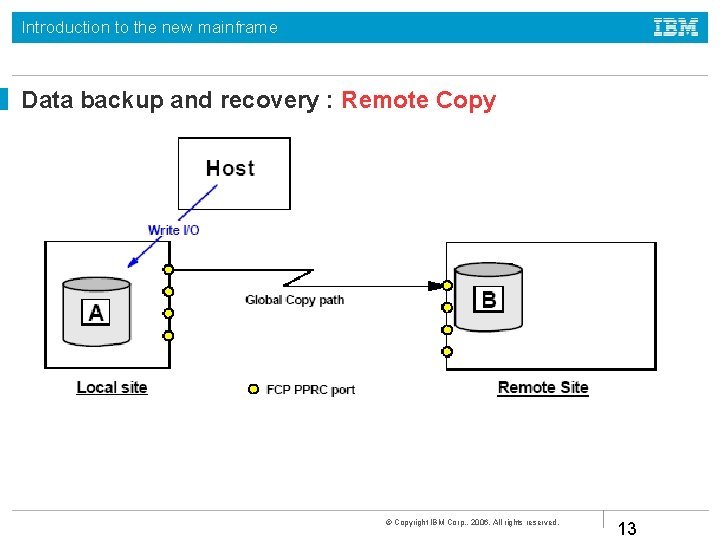
Introduction to the new mainframe Data backup and recovery : Remote Copy © Copyright IBM Corp. , 2006. All rights reserved. 13
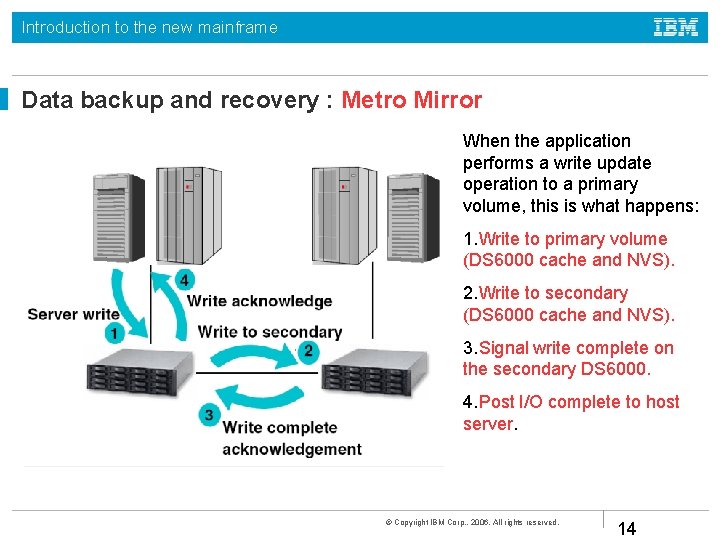
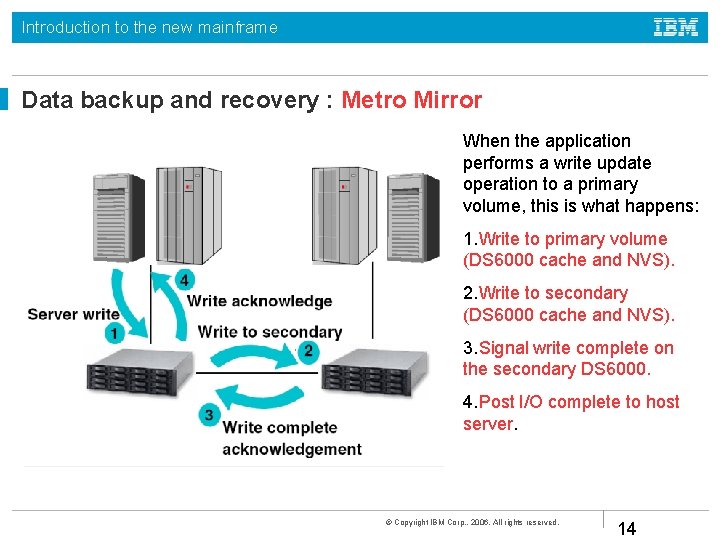
Introduction to the new mainframe Data backup and recovery : Metro Mirror When the application performs a write update operation to a primary volume, this is what happens: 1. Write to primary volume (DS 6000 cache and NVS). 2. Write to secondary (DS 6000 cache and NVS). 3. Signal write complete on the secondary DS 6000. 4. Post I/O complete to host server. © Copyright IBM Corp. , 2006. All rights reserved. 14
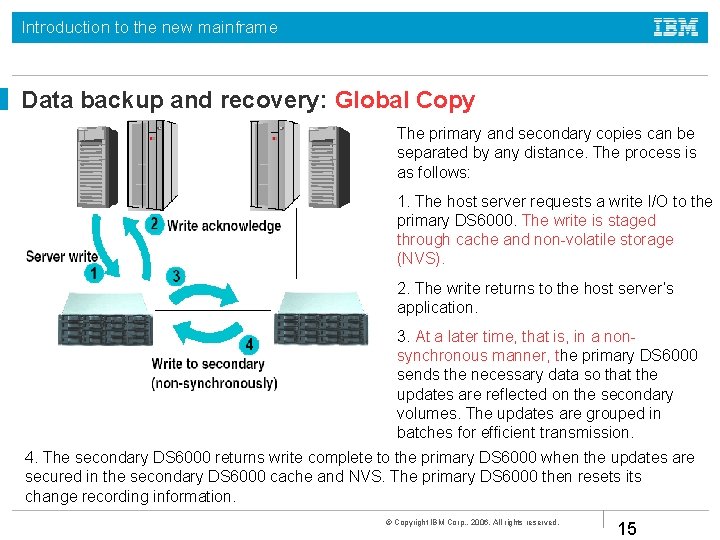
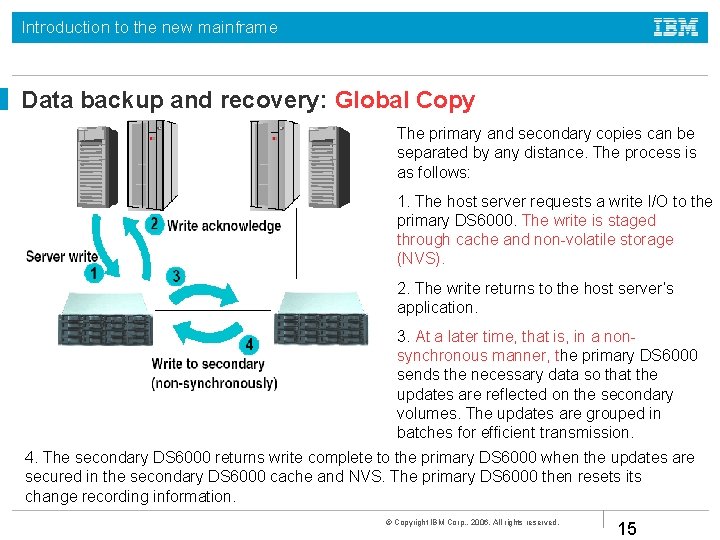
Introduction to the new mainframe Data backup and recovery: Global Copy The primary and secondary copies can be separated by any distance. The process is as follows: 1. The host server requests a write I/O to the primary DS 6000. The write is staged through cache and non-volatile storage (NVS). 2. The write returns to the host server’s application. 3. At a later time, that is, in a nonsynchronous manner, the primary DS 6000 sends the necessary data so that the updates are reflected on the secondary volumes. The updates are grouped in batches for efficient transmission. 4. The secondary DS 6000 returns write complete to the primary DS 6000 when the updates are secured in the secondary DS 6000 cache and NVS. The primary DS 6000 then resets its change recording information. © Copyright IBM Corp. , 2006. All rights reserved. 15
Introduction to the new mainframe Data backup and recovery: Global Mirror Other backup and recovery solutions: Data set level Volume level Application level © Copyright IBM Corp. , 2006. All rights reserved. 16

Introduction to the new mainframe © Copyright IBM Corp. , 2006. All rights reserved. 17
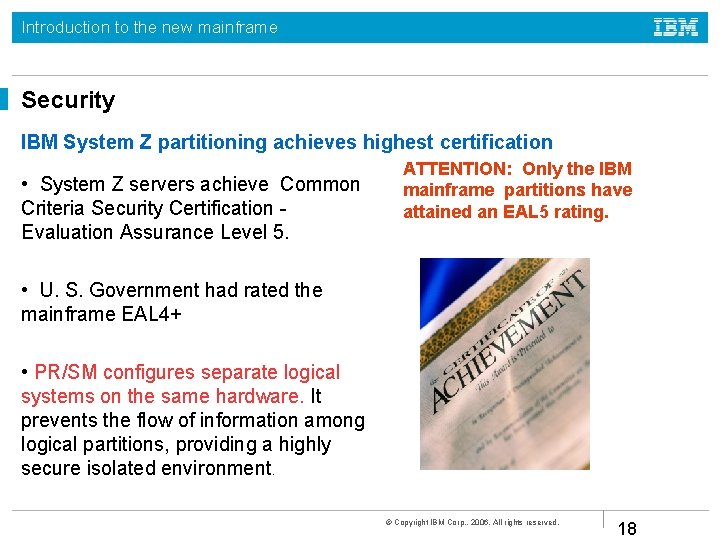
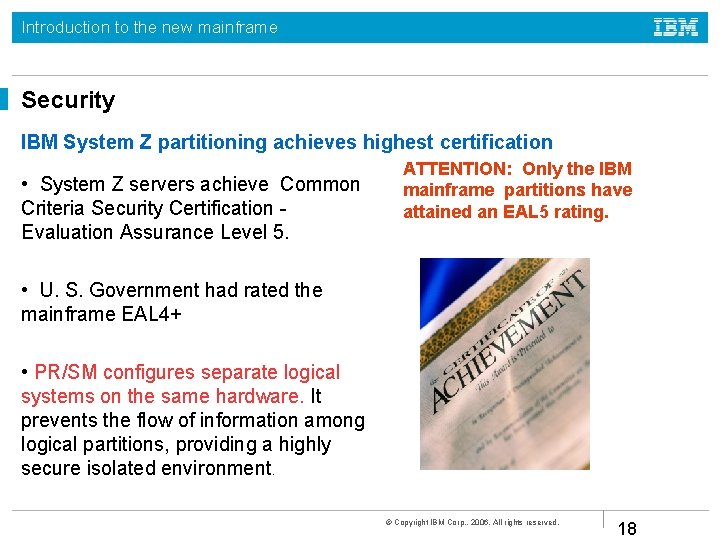
Introduction to the new mainframe Security IBM System Z partitioning achieves highest certification • System Z servers achieve Common Criteria Security Certification Evaluation Assurance Level 5. ATTENTION: Only the IBM mainframe partitions have attained an EAL 5 rating. • U. S. Government had rated the mainframe EAL 4+ • PR/SM configures separate logical systems on the same hardware. It prevents the flow of information among logical partitions, providing a highly secure isolated environment. © Copyright IBM Corp. , 2006. All rights reserved. 18
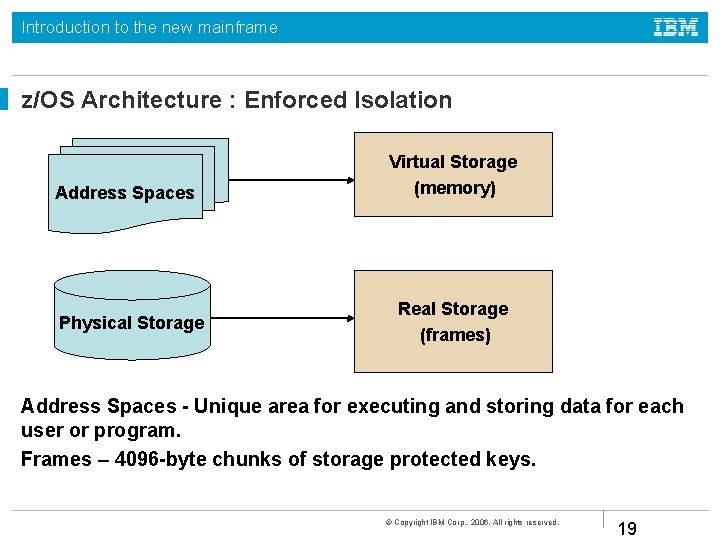
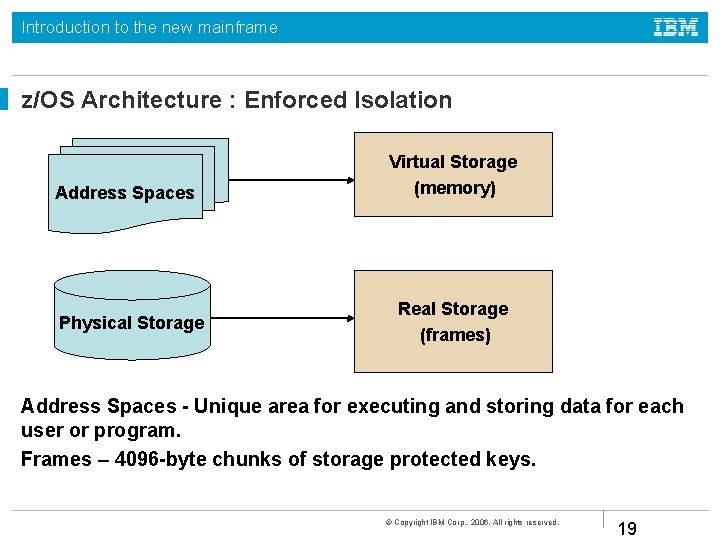
Introduction to the new mainframe z/OS Architecture : Enforced Isolation Address Spaces Physical Storage Virtual Storage (memory) Real Storage (frames) Address Spaces - Unique area for executing and storing data for each user or program. Frames – 4096 -byte chunks of storage protected keys. © Copyright IBM Corp. , 2006. All rights reserved. 19
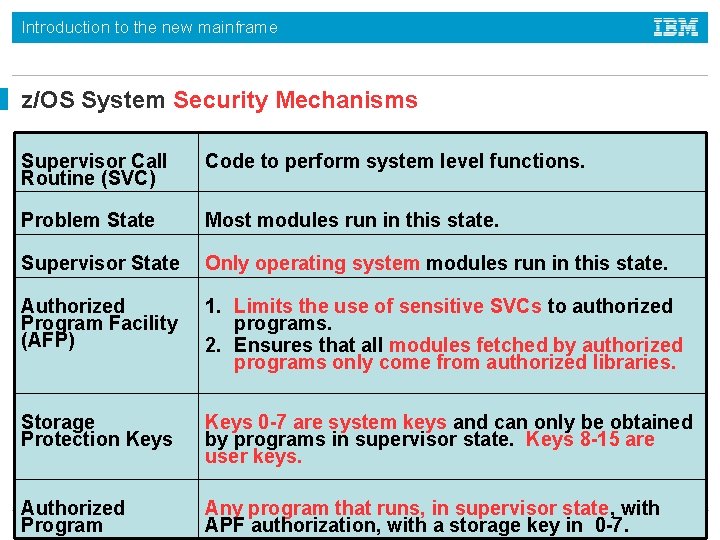
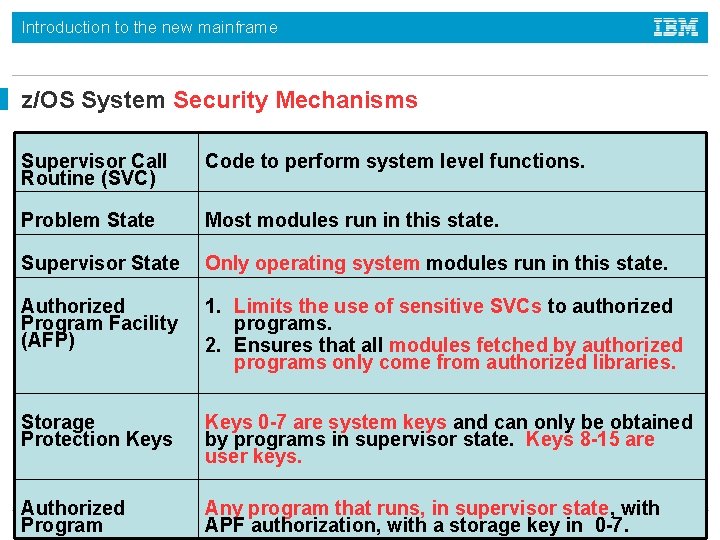
Introduction to the new mainframe z/OS System Security Mechanisms Supervisor Call Routine (SVC) Code to perform system level functions. Problem State Most modules run in this state. Supervisor State Only operating system modules run in this state. Authorized Program Facility (AFP) 1. Limits the use of sensitive SVCs to authorized programs. 2. Ensures that all modules fetched by authorized programs only come from authorized libraries. Storage Protection Keys 0 -7 are system keys and can only be obtained by programs in supervisor state. Keys 8 -15 are user keys. Authorized Program Any program that runs, in supervisor state, with APF authorization, with a storage key in 0 -7. 20 © Copyright IBM Corp. , 2006. All rights reserved.
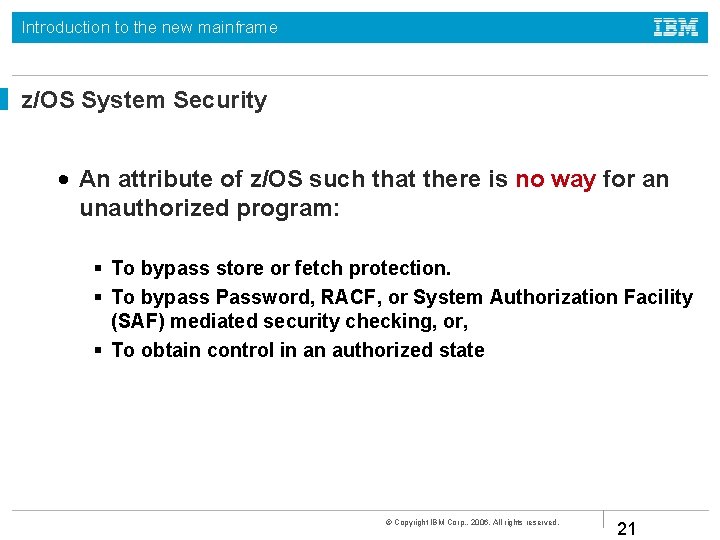
Introduction to the new mainframe z/OS System Security • An attribute of z/OS such that there is no way for an unauthorized program: To bypass store or fetch protection. To bypass Password, RACF, or System Authorization Facility (SAF) mediated security checking, or, To obtain control in an authorized state © Copyright IBM Corp. , 2006. All rights reserved. 21
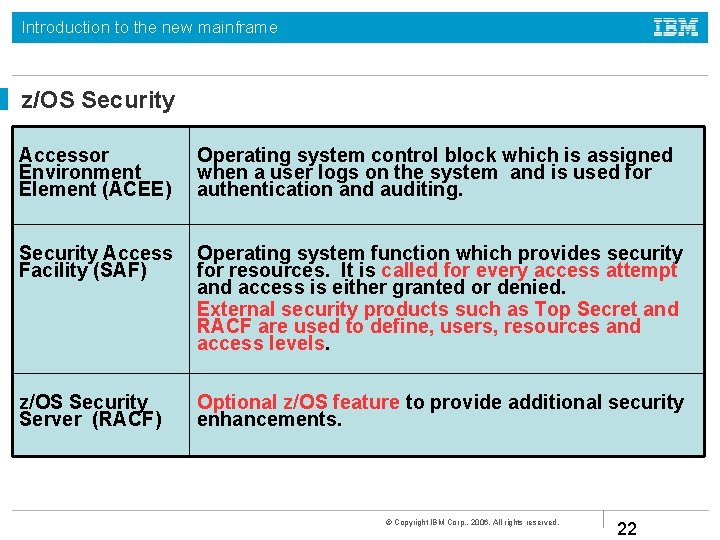
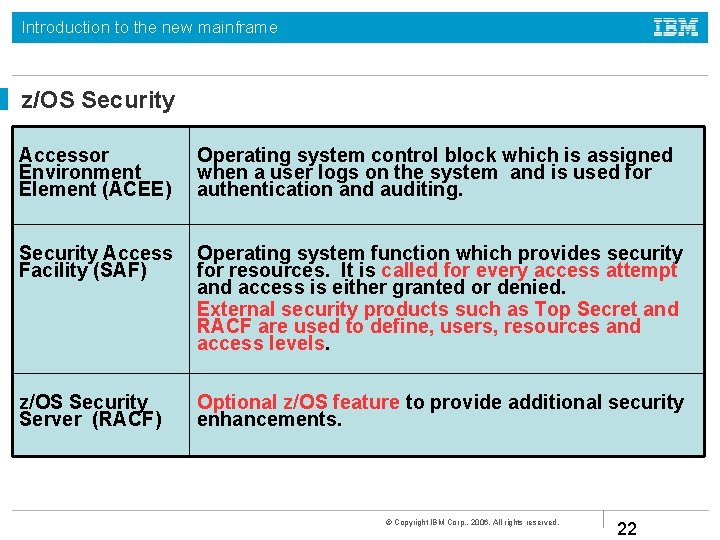
Introduction to the new mainframe z/OS Security Accessor Environment Element (ACEE) Operating system control block which is assigned when a user logs on the system and is used for authentication and auditing. Security Access Facility (SAF) Operating system function which provides security for resources. It is called for every access attempt and access is either granted or denied. External security products such as Top Secret and RACF are used to define, users, resources and access levels. z/OS Security Server (RACF) Optional z/OS feature to provide additional security enhancements. © Copyright IBM Corp. , 2006. All rights reserved. 22
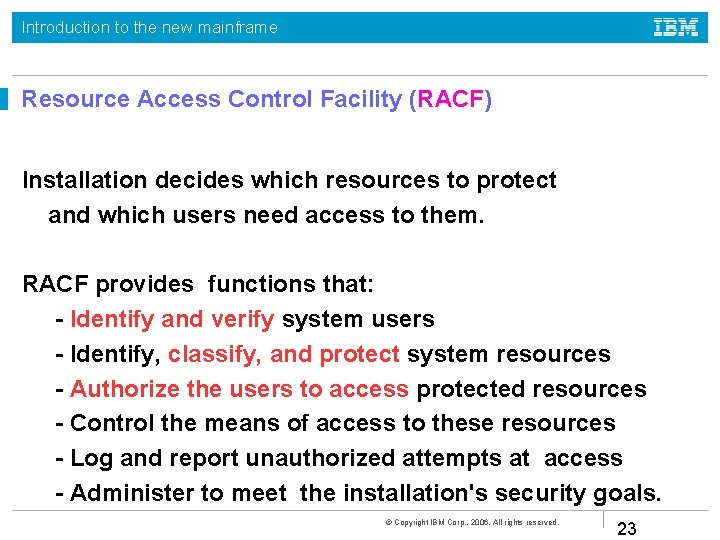
Introduction to the new mainframe Resource Access Control Facility (RACF) Installation decides which resources to protect and which users need access to them. RACF provides functions that: - Identify and verify system users - Identify, classify, and protect system resources - Authorize the users to access protected resources - Control the means of access to these resources - Log and report unauthorized attempts at access - Administer to meet the installation's security goals. © Copyright IBM Corp. , 2006. All rights reserved. 23
Introduction to the new mainframe z/OS Certification On March 11, 2005, BSI awarded IBM EAL 3+ certification for its flagship operating system z/OS 1. 6 with the RACF optional feature. The certification encompasses Controlled Access Protection Profile (CAPP) EAL 3+ and Labeled Security Protection Profile (LSPP) EAL 3+. z/OS 1. 5 and later with the RACF optional feature and DB 2 Version 8, provides a multilevel security (MLS) solution. © Copyright IBM Corp. , 2006. All rights reserved. 24
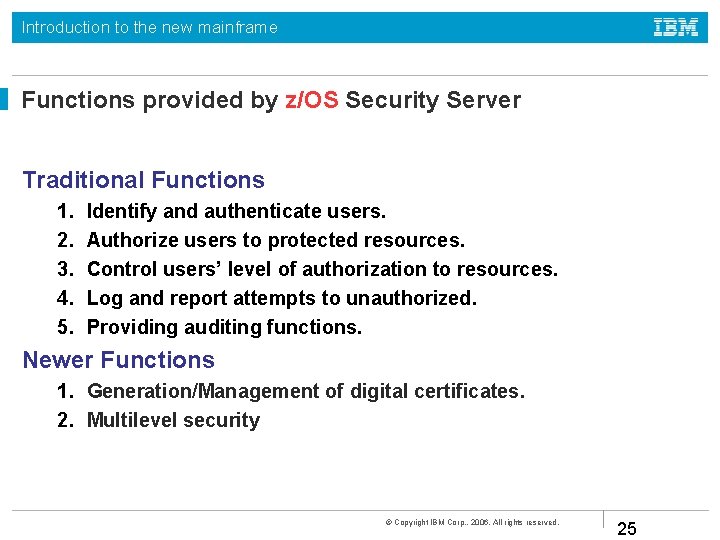
Introduction to the new mainframe Functions provided by z/OS Security Server Traditional Functions 1. 2. 3. 4. 5. Identify and authenticate users. Authorize users to protected resources. Control users’ level of authorization to resources. Log and report attempts to unauthorized. Providing auditing functions. Newer Functions 1. Generation/Management of digital certificates. 2. Multilevel security © Copyright IBM Corp. , 2006. All rights reserved. 25
Introduction to the new mainframe Summary The Mainframe: • Has several possibilities for to guaranty the integrity of the data • Data can be recovered when needed • Has several possibilities to make sure that the data is saved and secure © Copyright IBM Corp. , 2006. All rights reserved. 26