Image Steganography and Reversible Data Embedding Techniques Advisor
Image Steganography and Reversible Data Embedding Techniques 影像偽裝與可逆式資訊隱藏技術 Advisor: Prof. Chin-Chen Chang (張真誠 教授) Student: Wei-Liang Tai (戴維良) Department of Computer Science and Information Engineering, National Chung Cheng University 1
Outline • Part I: Image Steganography – covert (undetectable) communication – slight modification • Part II: Reversible Data Embedding – lossless (reversibility) – original image 2
Image Steganography Escape Bob Alice Warden 3
Steganography for VQ Compressed Images Using Hamming Codes and Declustering 4
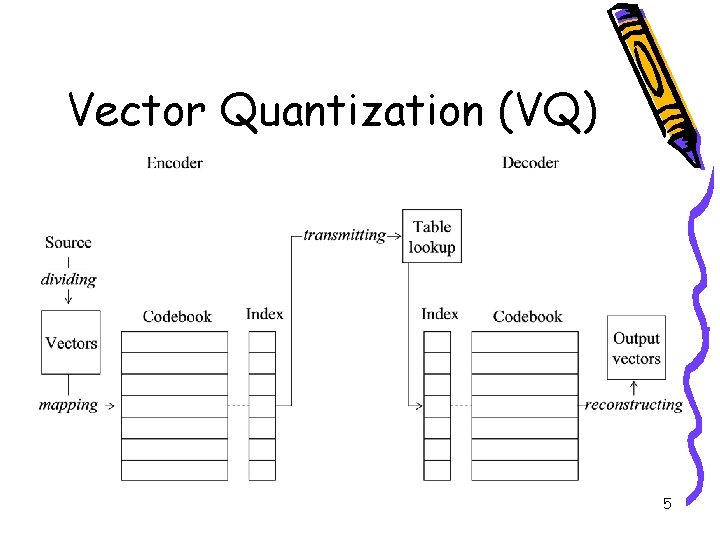
Vector Quantization (VQ) 5
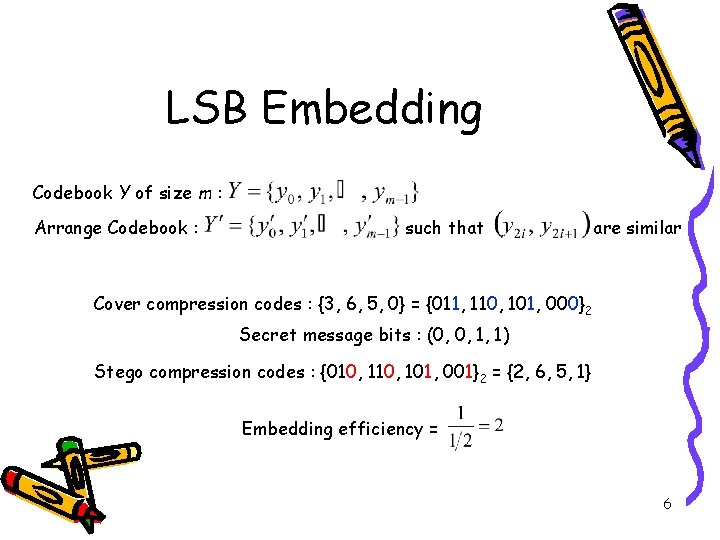
LSB Embedding Codebook Y of size m : Arrange Codebook : such that are similar Cover compression codes : {3, 6, 5, 0} = {011, 110, 101, 000}2 Secret message bits : (0, 0, 1, 1) Stego compression codes : {010, 101, 001}2 = {2, 6, 5, 1} Embedding efficiency = 6
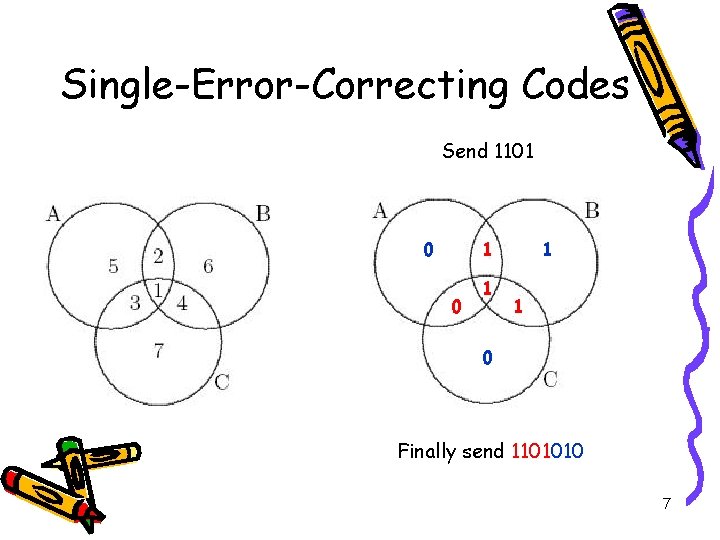
Single-Error-Correcting Codes Send 1101 0 1 1 1 0 Finally send 1101010 7
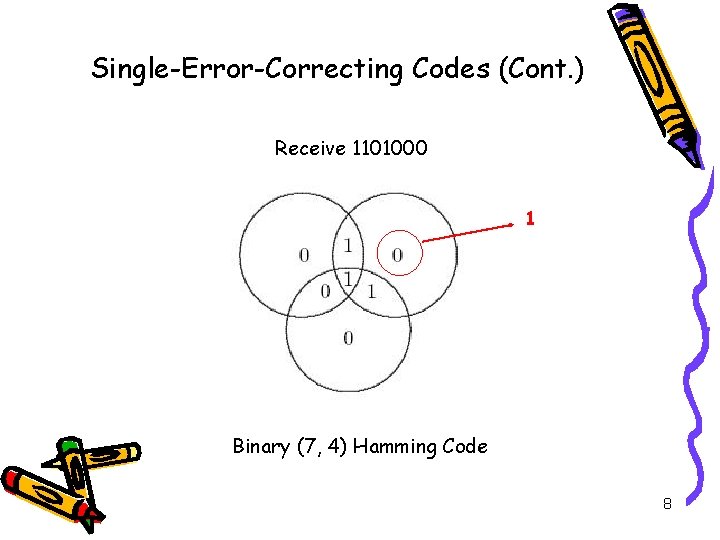
Single-Error-Correcting Codes (Cont. ) Receive 1101000 1 Binary (7, 4) Hamming Code 8
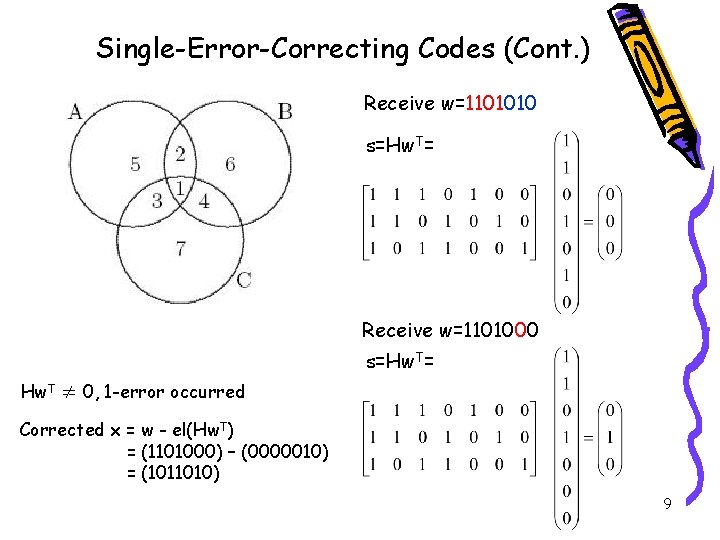
Single-Error-Correcting Codes (Cont. ) Receive w=1101010 s=Hw. T= Receive w=1101000 s=Hw. T= Hw. T ≠ 0, 1 -error occurred Corrected x = w - el(Hw. T) = (1101000) – (0000010) = (1011010) 9
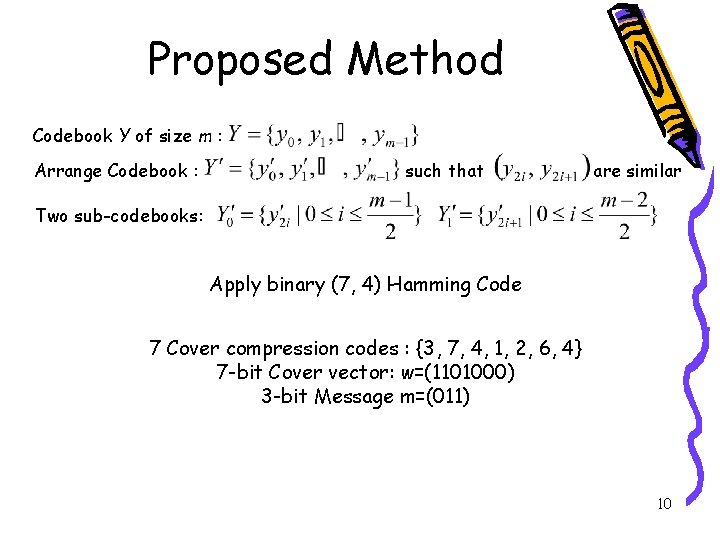
Proposed Method Codebook Y of size m : Arrange Codebook : such that are similar Two sub-codebooks: Apply binary (7, 4) Hamming Code 7 Cover compression codes : {3, 7, 4, 1, 2, 6, 4} 7 -bit Cover vector: w=(1101000) 3 -bit Message m=(011) 10
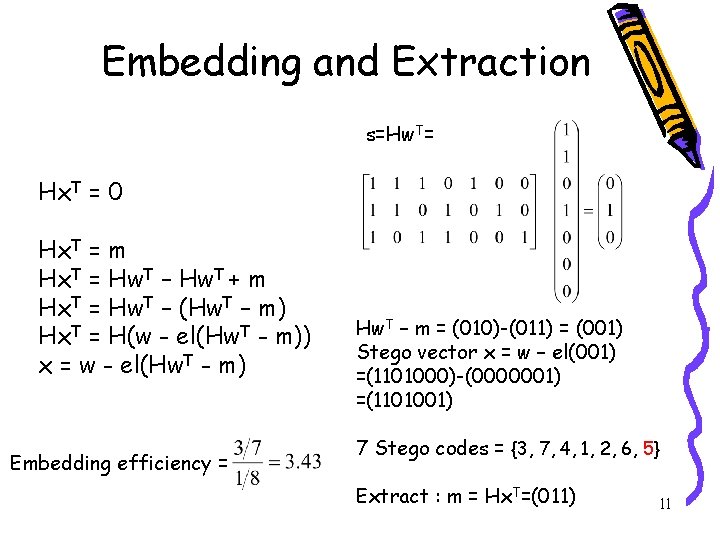
Embedding and Extraction s=Hw. T= Hx. T = 0 Hx. T = m Hx. T = Hw. T – Hw. T + m Hx. T = Hw. T – (Hw. T – m) Hx. T = H(w - el(Hw. T - m)) x = w - el(Hw. T - m) Embedding efficiency = Hw. T – m = (010)-(011) = (001) Stego vector x = w – el(001) =(1101000)-(0000001) =(1101001) 7 Stego codes = {3, 7, 4, 1, 2, 6, 5} Extract : m = Hx. T=(011) 11
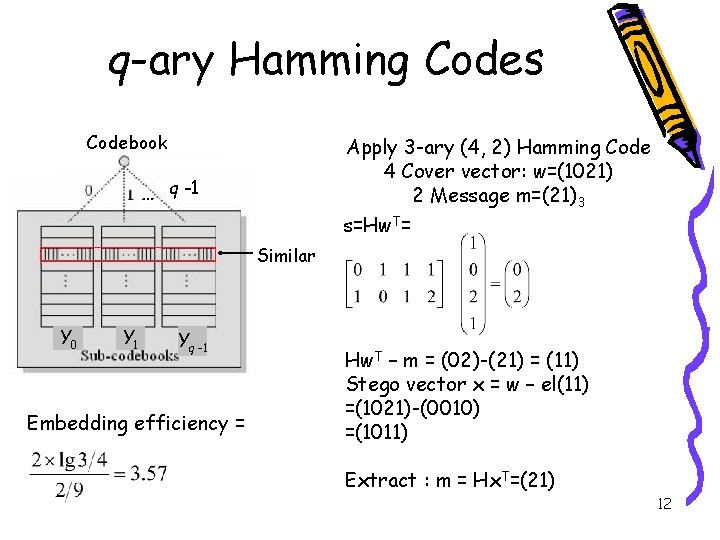
q-ary Hamming Codes Codebook Apply 3 -ary (4, 2) Hamming Code 4 Cover vector: w=(1021) 2 Message m=(21)3 s=Hw. T= … q -1 Similar Y 0 Y 1 Yq -1 Embedding efficiency = Hw. T – m = (02)-(21) = (11) Stego vector x = w – el(11) =(1021)-(0010) =(1011) Extract : m = Hx. T=(21) 12
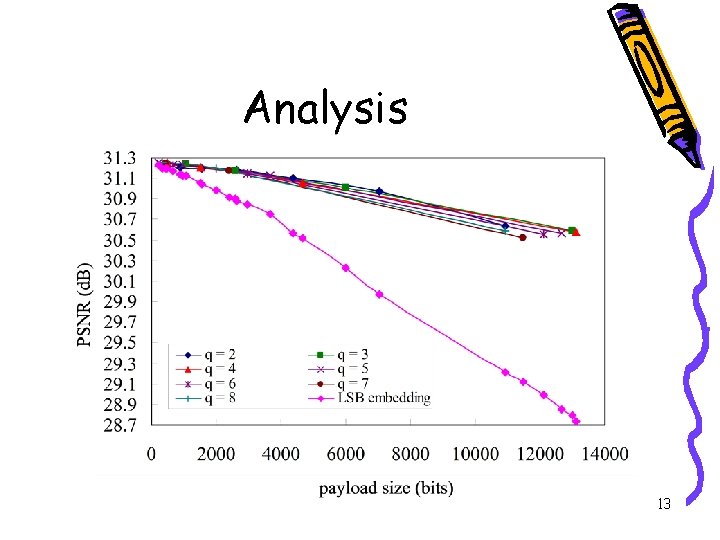
Analysis Use the q-ary Hamming to convey r q-ary symbols in codes indices by performing at most one embedding change. Embedding efficiency = > 2 = LSB embedding 13
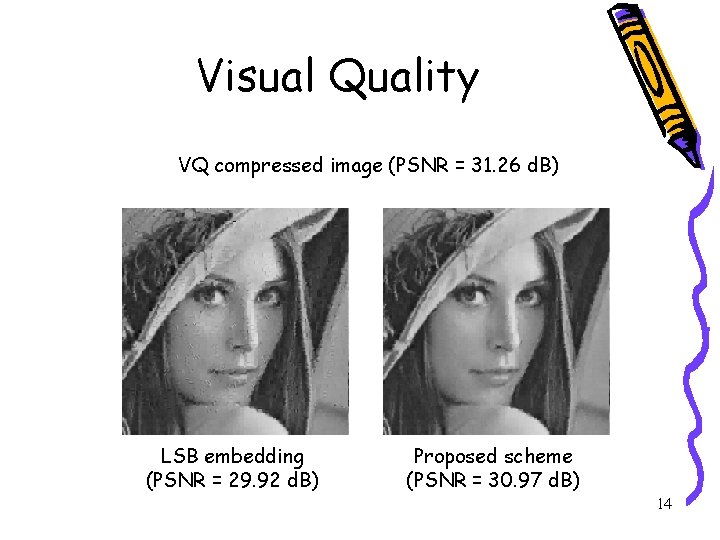
Visual Quality VQ compressed image (PSNR = 31. 26 d. B) LSB embedding (PSNR = 29. 92 d. B) Proposed scheme (PSNR = 30. 97 d. B) 14
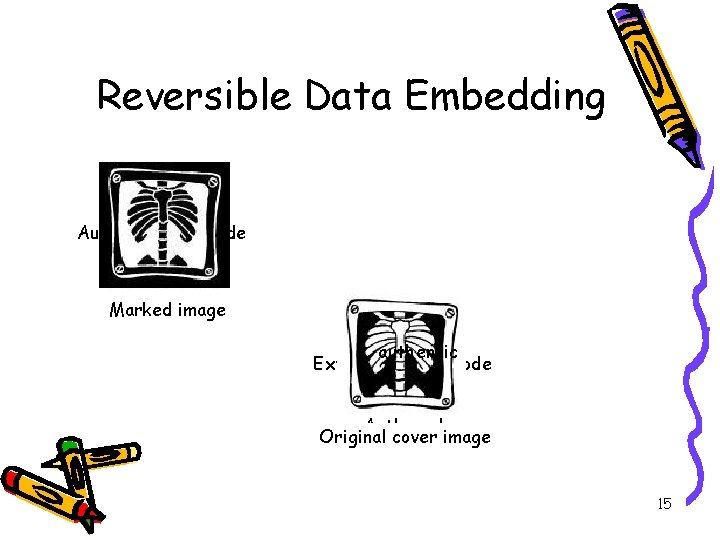
Reversible Data Embedding Authentication code Marked Cover image = authentic Extracted auth. code Auth. code Original cover image 15

Reversible Data Hiding Based on Histogram Modification of Pixel Differences 16
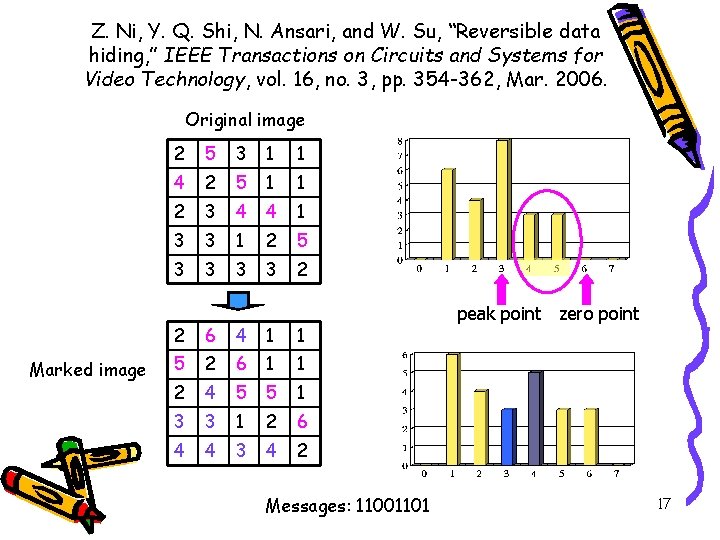
Z. Ni, Y. Q. Shi, N. Ansari, and W. Su, “Reversible data hiding, ” IEEE Transactions on Circuits and Systems for Video Technology, vol. 16, no. 3, pp. 354 -362, Mar. 2006. Original image Marked image 2 5 3 1 1 4 2 5 1 1 2 3 4 4 1 3 3 1 2 5 3 3 2 2 6 3 4 1 1 5 2 6 1 1 2 3 4 5 5 1 3 3 1 2 6 3 4 3 3 4 2 Messages: 11001101 peak point zero point 17
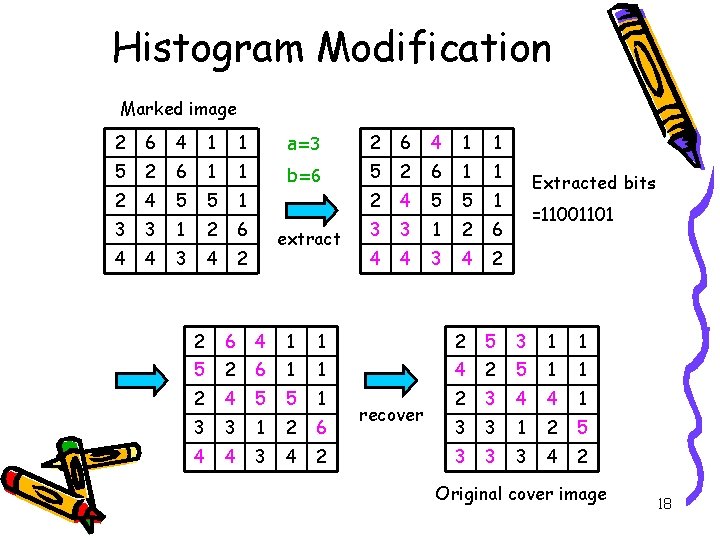
Histogram Modification Marked image 2 6 4 1 1 a=3 2 6 4 1 1 5 2 6 1 1 b=6 5 2 6 1 1 2 4 5 5 1 3 3 1 2 6 4 4 3 4 2 extract Extracted bits =11001101 2 6 4 1 1 2 5 3 1 1 5 2 6 1 1 4 2 5 1 1 2 4 5 5 1 2 3 4 4 1 3 3 1 2 6 3 3 1 2 5 4 4 3 4 2 3 3 3 4 2 recover Original cover image 18
Proposed Method 19
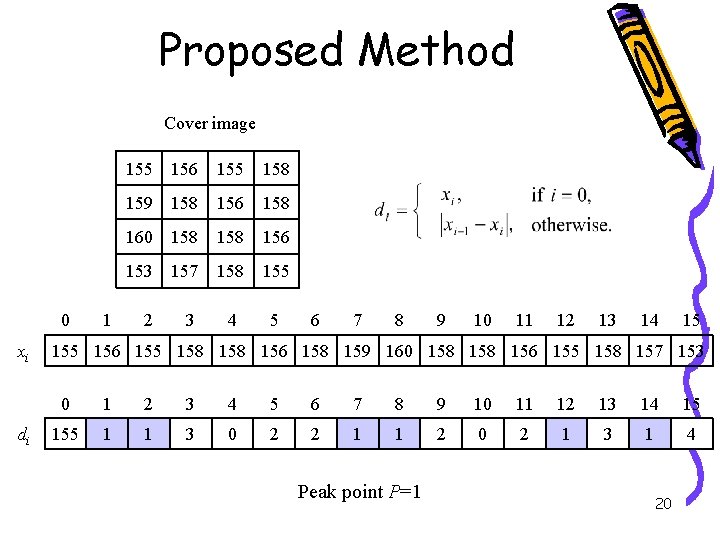
Proposed Method Cover image 0 xi di 1 155 156 155 158 159 158 156 158 160 158 156 153 157 158 155 2 3 4 5 6 7 8 9 10 11 12 13 14 15 156 155 158 156 158 159 160 158 156 155 158 157 153 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 155 1 1 3 0 2 2 1 1 2 0 2 1 3 1 4 Peak point P=1 20
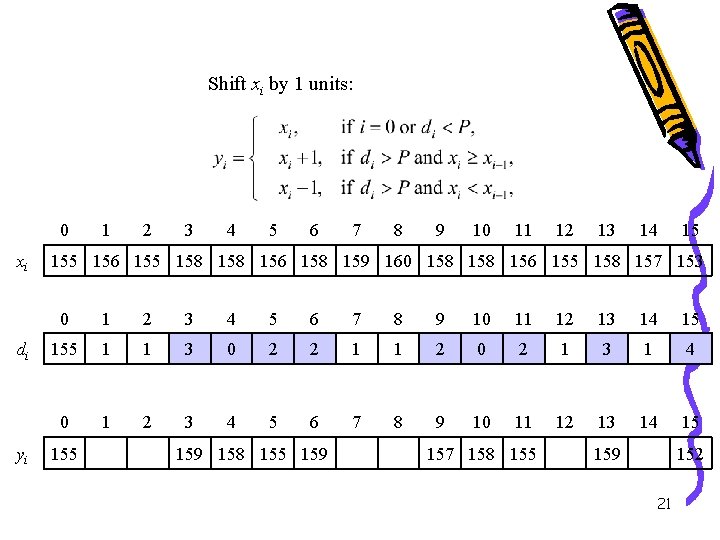
Shift xi by 1 units: 0 xi di yi 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 156 155 158 156 158 159 160 158 156 155 158 157 153 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 155 1 1 3 0 2 2 1 1 2 0 2 1 3 1 4 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 159 158 155 159 157 158 155 159 152 21
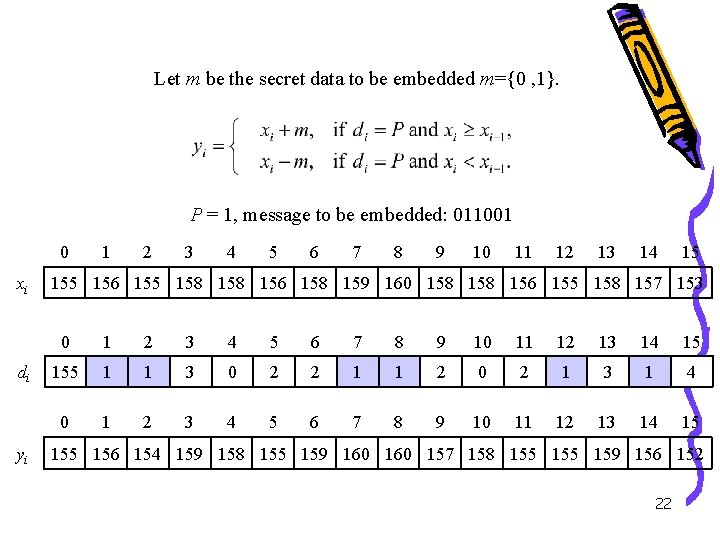
Let m be the secret data to be embedded m={0 , 1}. P = 1, message to be embedded: 011001 0 xi di yi 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 156 155 158 156 158 159 160 158 156 155 158 157 153 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 155 1 1 3 0 2 2 1 1 2 0 2 1 3 1 4 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 156 154 159 158 155 159 160 157 158 155 159 156 152 22
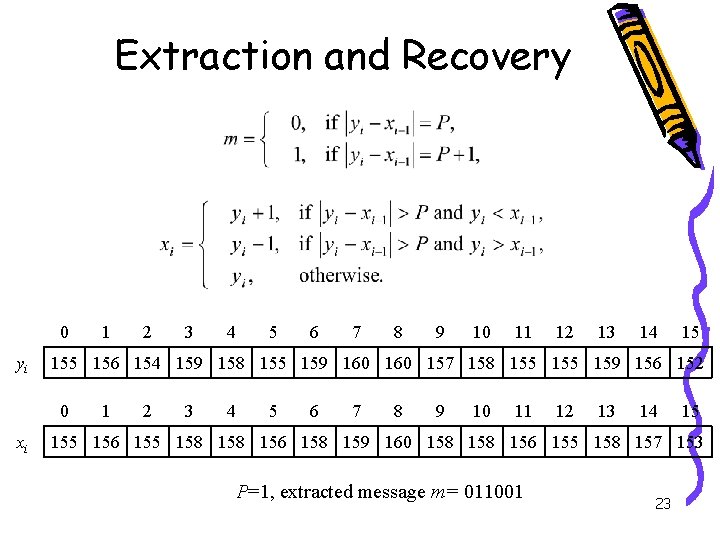
Extraction and Recovery 0 yi 2 3 4 5 6 7 8 9 10 11 12 13 14 15 156 154 159 158 155 159 160 157 158 155 159 156 152 0 xi 1 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 156 155 158 156 158 159 160 158 156 155 158 157 153 P=1, extracted message m= 011001 23
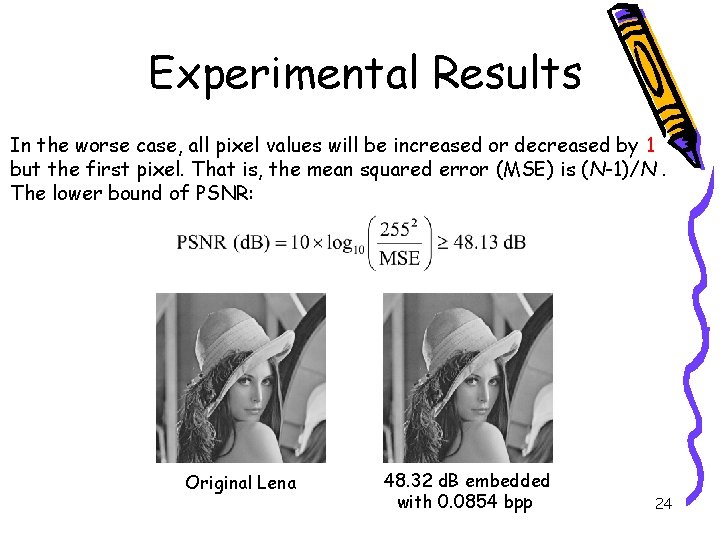
Experimental Results In the worse case, all pixel values will be increased or decreased by 1 but the first pixel. That is, the mean squared error (MSE) is (N-1)/N. The lower bound of PSNR: Original Lena 48. 32 d. B embedded with 0. 0854 bpp 24
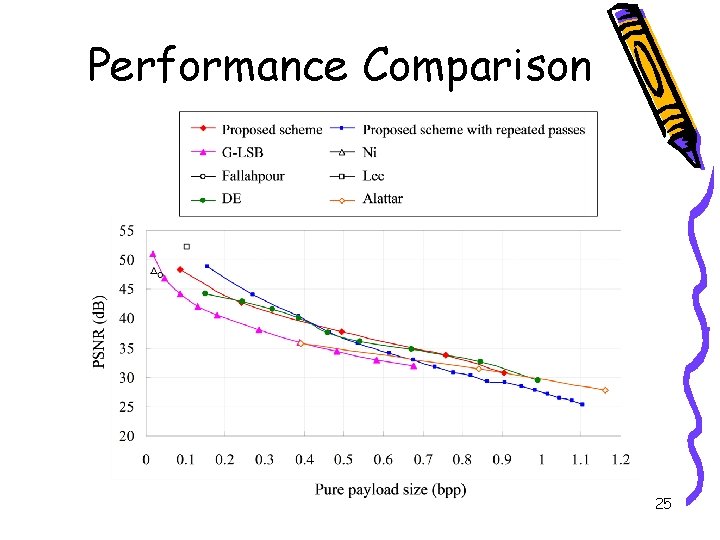
Performance Comparison 25
Future Works • Image Steganography – spatial domain, JPEG 2000, etc. – combine other codes • Reversible Data Embedding – higher hiding capacity with lower distortion. – transform domains such as wavelet 26
- Slides: 26