Grid Shib GridShibboleth Interoperability http gridshib globusorg November
Grid. Shib Grid/Shibboleth Interoperability http: //gridshib. globus/org November, 2006 Tom Barton 1, Tim Freeman 1, Kate Keahey 1, Raj Kettimuthu 1, Tom Scavo 2, Frank Siebenlist 1, Von Welch 2 1 University of Chicago 2 NCSA/University of Illinois at Urbana-Champaign National Center for Supercomputing Applications
Acknowledgments • Grid. Shib is a project funded by the NSF Middleware Initiative – NMI awards 0438424 and 0438385 – Opinions and recommendations are those of the authors and do not necessarily reflect the views of the National Science Foundation. • • Collaboration between NCSA and U. Chicago/ANL Also many thanks to Internet 2 National Center for Supercomputing Applications
Grid. Shib Goals • Allow the Grid to scale by leveraging existing campus identity management (Id. M) – Consider Shibboleth as the interface to campus Id. M systems – Get out of identity management game • Making joining the Grid as easy as possible for users – No separate long-term credential for Grid access to manage – No new passwords, certificates, etc • Allow campuses attributes and VO attributes to be aggregated and used by the Grid for authorization – Allow for scalability in user base through attribute-based authorization - I. e. know groups of users instead of individual users National Center for Supercomputing Applications
Some background University of Illinois at Urbana-Champaign National Center for Supercomputing Applications
Authentication vs Authorization • Identifier: A unique name for an entity – (username, DN, GUID, SSN, etc. ) • Authentication: Verifying Identity of users – associating them with a Identifier • Authorization: Deciding whether or not a request will be granted – Different authentication methods have different levels of certainty • Authorization Policy: The set of rules by which an authorization decision is made • Authentication does not imply Authorization – E. g. just because you trust a CA doesn’t mean all the user with certificates from it are authorized National Center for Supercomputing Applications
Attributes • Attribute: A property of an entity – Entities may have lots of properties – The same property may apply to many entities – E. g. community membership, affiliation, age, gender, height, occupation • Attribute-based authorization: Authorization based on who someone is (their identity) but what they are (their attributes) – E. g. you can buy me a beer if your age > 21 years National Center for Supercomputing Applications
Grid Authentication • • Globus Toolkit provides authentication services via X. 509 credentials When requesting a service, the user presents an X. 509 certificate – RFC 3820 proxy certificate or standard entity certificate • Grid. Shib leverages the existing authentication mechanisms in GT National Center for Supercomputing Applications
Grid Authorization • Today, Globus Toolkit provides identity-based authorization mechanisms: – Access control lists (called grid-mapfiles) map DNs to local identity (e. g. , Unix logins) – Community Authorization Service (CAS) • Some attribute-based authorization has appeared and is proving useful – E. g. VOMS, ca. BIG National Center for Supercomputing Applications
Shibboleth • • Allows for inter-organization access to web resources Exposes campus identity and attributes in standard format – Based on SAML as defined by OASIS – Policies for attribute release and transient handles to allow privacy National Center for Supercomputing Applications
Why Shibboleth? • • • What does Shibboleth bring to the table? A large (and growing) installed base on campuses around the world Professional development and support team A standards-based, open source implementation A standard attribute vocabulary (edu. Person) National Center for Supercomputing Applications
Challenges • • Application mismatch – Shibboleth works well with webapps and web browsers – Grid services are soap and otherwise Identity Federation – Have to convert between SAML and X. 509 – Have to map identifiers in Grid space to identifiers at campus National Center for Supercomputing Applications
Grid. Shib Software Components • • • Grid. Shib for Globus Toolkit – A plugin for GT 4. 0 Grid. Shib for Shibboleth – A plugin for Shibboleth 1. 3 Id. P Grid. Shib CA – A web-based CA for new grid users • Grid. Shib SAML Tools • – Tools for portals and users to embed attributes into X. 509 credentials All at: http: //gridshib. globus. org/ National Center for Supercomputing Applications
Grid. Shib for Globus Toolkit • • Grid. Shib for Globus Toolkit is a plugin for GT 4 Features: – – – SAML Authentication consumer SAML attribute consumption Attribute-based access control Attribute-based local account mapping SAML metadata consumption National Center for Supercomputing Applications
Grid. Shib SAML Tools • • Tools for creating SAML and binding to Grid Credentials Used to direct Grid. Shib for GT to appropriate Shibboleth AA – Addressing WAYF • Directs Grid. Shib for GT as what identifier to use in SAML attribute request – Can alleviate need for Shibboleth Idp changes • Upcoming version allows binding of attributes to the Credential National Center for Supercomputing Applications
Grid. Shib for Shibboleth • • Grid. Shib for Shibboleth is a plugin for a Shibboleth Id. P v 1. 3 (or later) Features: – Name Mapper – SAML name identifier implementations • X 509 Subject. Name, email. Address, etc. – Certificate Registry National Center for Supercomputing Applications
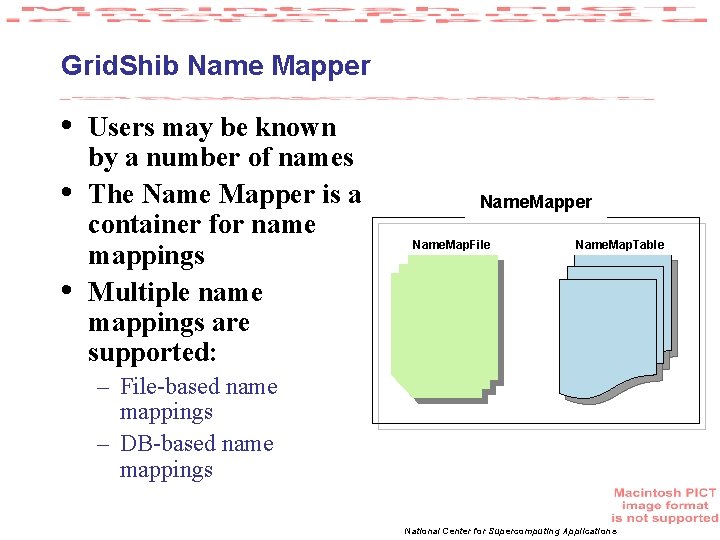
Grid. Shib Name Mapper • • • Users may be known by a number of names The Name Mapper is a container for name mappings Multiple name mappings are supported: Name. Mapper Name. Map. File Name. Map. Table – File-based name mappings – DB-based name mappings National Center for Supercomputing Applications
Grid. Shib Certificate Registry • • A Certificate Registry is integrated into Grid. Shib for Shibboleth An established grid user authenticates and registers an X. 509 end-entity cert The Registry binds the cert to the principal name and persists the binding in a database On the backend, Grid. Shib maps the DN in a query to a principal name in the DB National Center for Supercomputing Applications
Grid. Shib CA • • The Grid. Shib Certificate Authority is a web-based CA for new grid users The Grid. Shib CA is protected by a Shib SP and back-ended by the My. Proxy Online CA – Or a local Open. SSL-based CA • The CA issues short-term credentials suitable for authentication to a Grid SP – Short-lived EEC, similar to My. Proxy-CA or KCA • Credentials are downloaded to the desktop via Java Web Start National Center for Supercomputing Applications
Grid. Shib-my. Vocs Integration • my. Vocs developed @ UAB – Gemmill, Robinson • • my. Vocs allows for VOs based on Shibboleth identities Grid. Shib authorizes use of Grid Services based on Shibboleth identities Integration allows for the creation and management of Grid Vos based on Shibboleth http: //www. myvocs. org National Center for Supercomputing Applications
Deployment Scenarios University of Illinois at Urbana-Champaign National Center for Supercomputing Applications
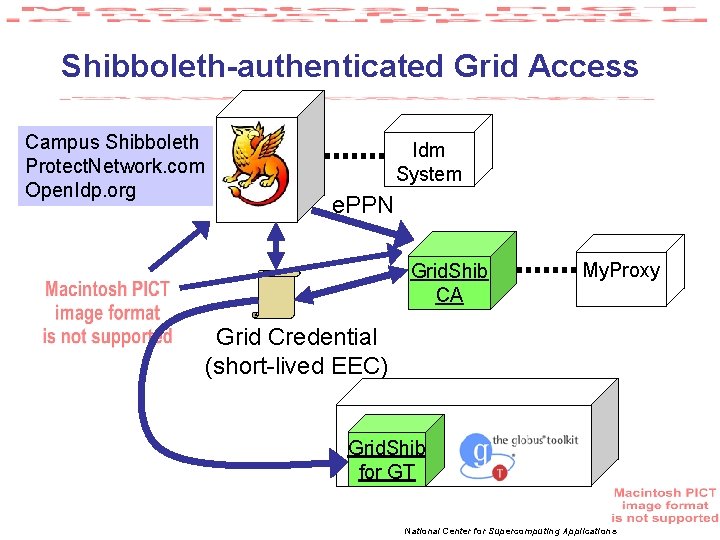
Shibboleth-authenticated Grid Access Campus Shibboleth Protect. Network. com Open. Idp. org Idm System e. PPN Grid. Shib CA My. Proxy Grid Credential (short-lived EEC) Grid. Shib for GT National Center for Supercomputing Applications
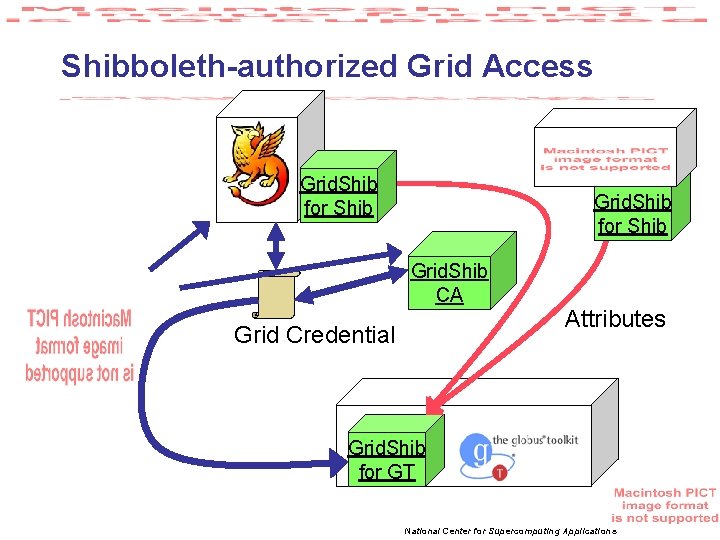
Shibboleth-authorized Grid Access Grid. Shib for Shib Grid. Shib CA Grid Credential Attributes Grid. Shib for GT National Center for Supercomputing Applications
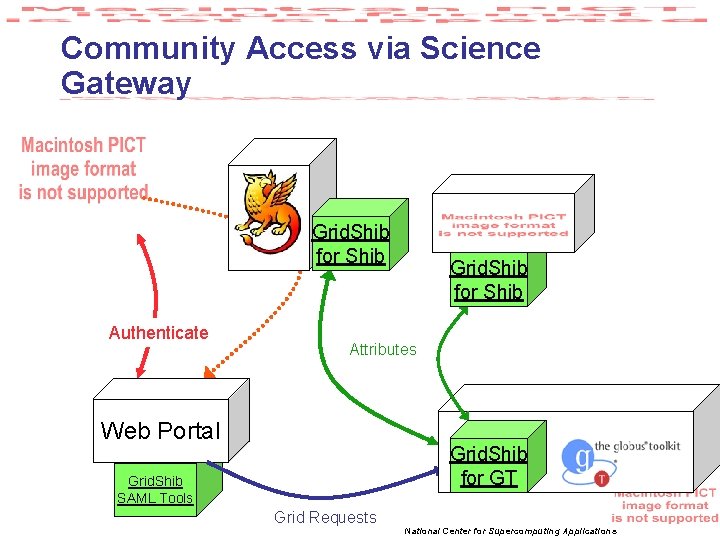
Community Access via Science Gateway Grid. Shib for Shib Authenticate Grid. Shib for Shib Attributes Web Portal Grid. Shib for GT Grid. Shib SAML Tools Grid Requests National Center for Supercomputing Applications
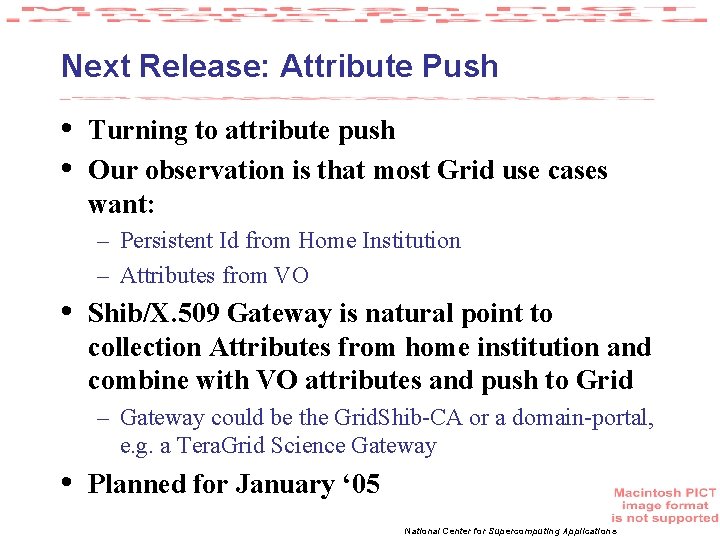
Next Release: Attribute Push • • Turning to attribute push Our observation is that most Grid use cases want: – Persistent Id from Home Institution – Attributes from VO • Shib/X. 509 Gateway is natural point to collection Attributes from home institution and combine with VO attributes and push to Grid – Gateway could be the Grid. Shib-CA or a domain-portal, e. g. a Tera. Grid Science Gateway • Planned for January ‘ 05 National Center for Supercomputing Applications
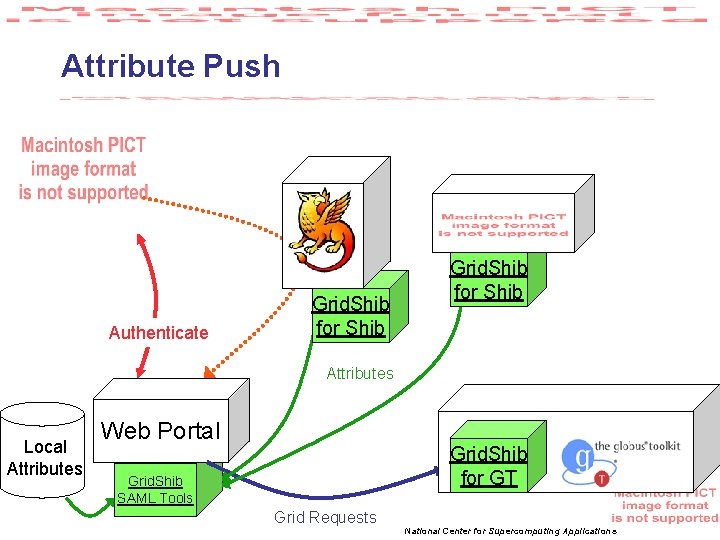
Attribute Push Authenticate Grid. Shib for Shib Attributes Local Attributes Web Portal Grid. Shib for GT Grid. Shib SAML Tools Grid Requests National Center for Supercomputing Applications
Tera. Grid testbed • Testbed for Federated Identity Management and Attribute-based Authorization – Building on Shibboleth, Grid. Shib • Goals: – Allow for scalable access by leveraging campus authentication - remove Idm burden from Tera. Grd – Allow for attribute-based authorization to define communities – Ease of use for users - no management of long-term Grid credentials – Interoperability with OSG, others. National Center for Supercomputing Applications
Grid. Shib Plans • December ‘ 06: 0. 5 release – Bug fixes and cleanup from Nanohub engagement • • December ‘ 06: Finish Tera. Grid Testbed planning January ‘ 06: 0. 6 release – Attribute push • January-May ‘ 07: Tera. Grid testbed – Bug fixes as arise – Evaluation of technology, gap analysis – Focus seems to be on Portal efforts at this point National Center for Supercomputing Applications
Summary • • Grid. Shib has a number of tools for leveraging Shibboleth for the Grid Both for user authentication and attributebased authorization Deploys easily on Shibboleth 1. 3 and Globus 4. 0 Available under Apache 2 license For more information and software: • http: //gridshib. globus. org • vwelch@ncsa. uiuc. edu • http: //dev. globus. org/wiki/Incubator/Grid. Shib National Center for Supercomputing Applications
Questions? University of Illinois at Urbana-Champaign National Center for Supercomputing Applications
- Slides: 29