Grid Shib Project Update Tom Barton 1 Tim
Grid. Shib Project Update Tom Barton 1, Tim Freeman 1, Kate Keahey 1, Raj Kettimuthu 1, Tom Scavo 2, Frank Siebenlist 1, Von Welch 2 1 University of Chicago 2 NCSA/University of Illinois
Outline l Grid. Shib Overview l Grid. Shib Components l Grid. Shib Profiles l Grid. Shib Roadmap
What is Grid. Shib? l Grid. Shib enables secure attribute sharing among Grid virtual organizations and higher-educational institutions l The goal of Grid. Shib is to allow interoperability between the Globus Toolkit® with Shibboleth® l Grid. Shib adds attribute-based authorization to Globus Toolkit
Some Background l Large scientific projects have spawned Virtual Organizations (VOs) l The cyberinfrastructure and software systems to support VOs are called grids l Globus Toolkit is the de facto standard software solution for grids l Grid Security Infrastructure (GSI) provides basic security services for grids
Grid Authentication l Globus Toolkit provides authentication services via X. 509 credentials l When requesting a service, the user presents an X. 509 certificate, usually a proxy certificate l Grid. Shib leverages the existing authentication mechanisms in GT
Grid Authorization l Today, Globus Toolkit provides identitybased authorization mechanisms: u u Access control lists (called grid-mapfiles) map DNs to local identity (e. g. , Unix logins) Community Authorization Service (CAS) l PERMIS and VOMS l Grid. Shib provides attribute-based authorization based on Shibboleth
Grid. Shib Project Motivation l VOs are difficult to manage u l Identity-based access control methods are inflexible and do not scale u l Goal: Leverage existing identity management infrastructure Goal: Use attribute-based access control Solution: Leverage Shibboleth with Globus Toolkit!
Grid. Shib Use Cases l Three use cases under consideration: 1. Established grid user (non-browser) 2. New grid user (non-browser) 3. Portal grid user (browser) l Initial efforts concentrated on the nonbrowser use cases l Current efforts are focused on the portal grid user
Established Grid User l User possesses an X. 509 end entity certificate l User may or may not use My. Proxy Server to manage X. 509 credentials l User authenticates to Grid SP with a proxy certificate l The current Grid. Shib implementation addresses this use case
New Grid User l User does not possess an X. 509 end entity certificate l User relies on Grid. Shib CA to obtain shortlived X. 509 certificates l User authenticates to Grid SP using shortlived X. 509 credential l The my. Vocs-Grid. Shib integration addresses this use case
Portal Grid User l User does not possess an X. 509 cert l A browser user authenticates to a Grid Portal (which may or may not be Shibenabled) l The user delegates the Grid Portal to request a service at the Grid SP l The Grid Portal authenticates to the Grid SP using its “community credential”
Outline l Grid. Shib Overview l Grid. Shib Components l Grid. Shib Profiles l Grid. Shib Roadmap
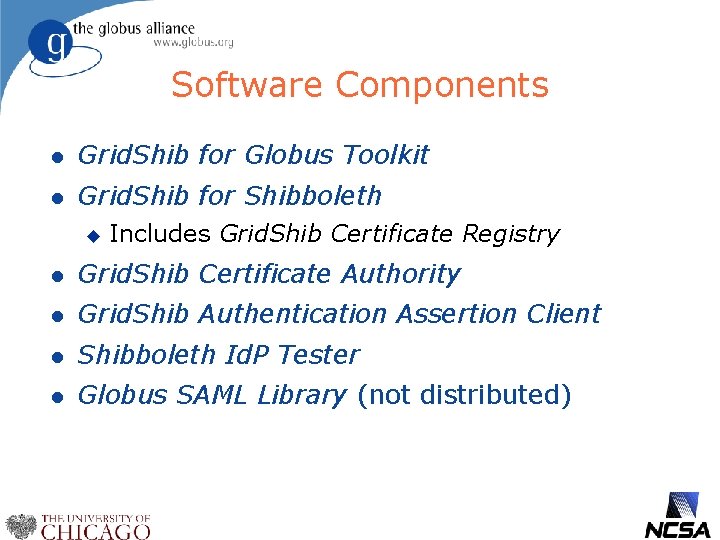
Software Components l Grid. Shib for Globus Toolkit l Grid. Shib for Shibboleth u Includes Grid. Shib Certificate Registry l Grid. Shib Certificate Authority l Grid. Shib Authentication Assertion Client l Shibboleth Id. P Tester l Globus SAML Library (not distributed)
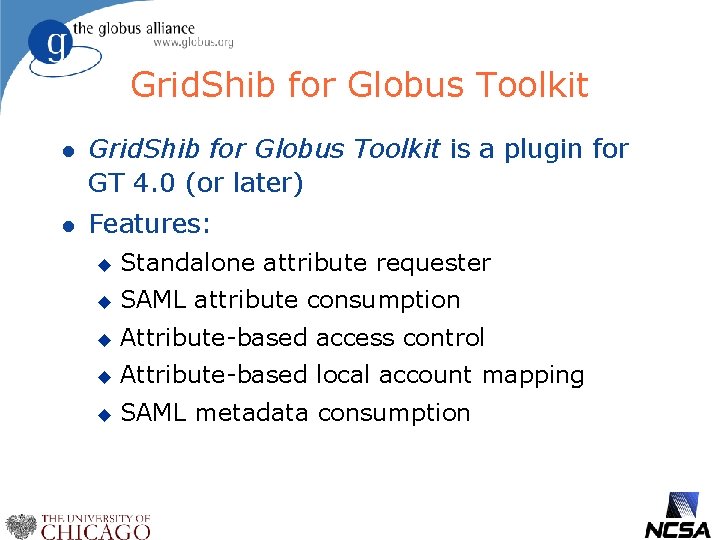
Grid. Shib for Globus Toolkit l Grid. Shib for Globus Toolkit is a plugin for GT 4. 0 (or later) l Features: u Standalone attribute requester u SAML attribute consumption u Attribute-based access control u Attribute-based local account mapping u SAML metadata consumption
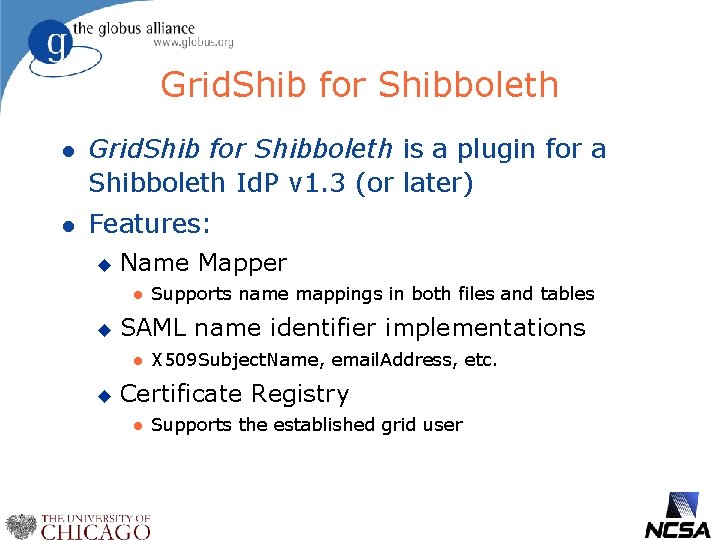
Grid. Shib for Shibboleth l Grid. Shib for Shibboleth is a plugin for a Shibboleth Id. P v 1. 3 (or later) l Features: u Name Mapper l u SAML name identifier implementations l u Supports name mappings in both files and tables X 509 Subject. Name, email. Address, etc. Certificate Registry l Supports the established grid user
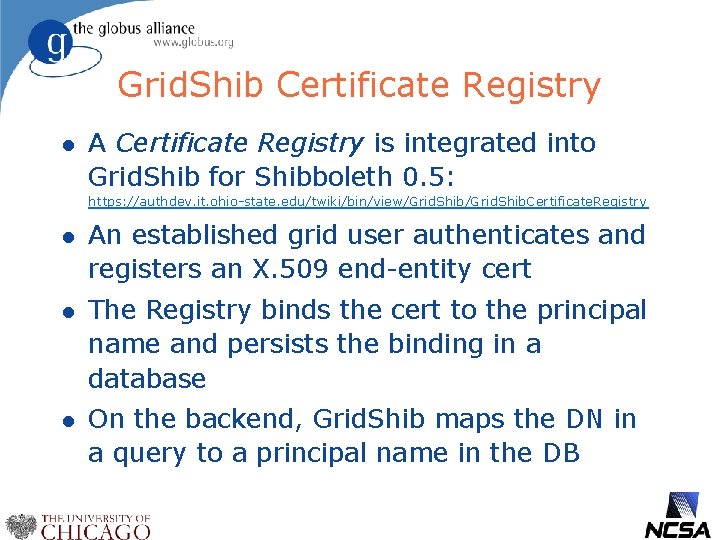
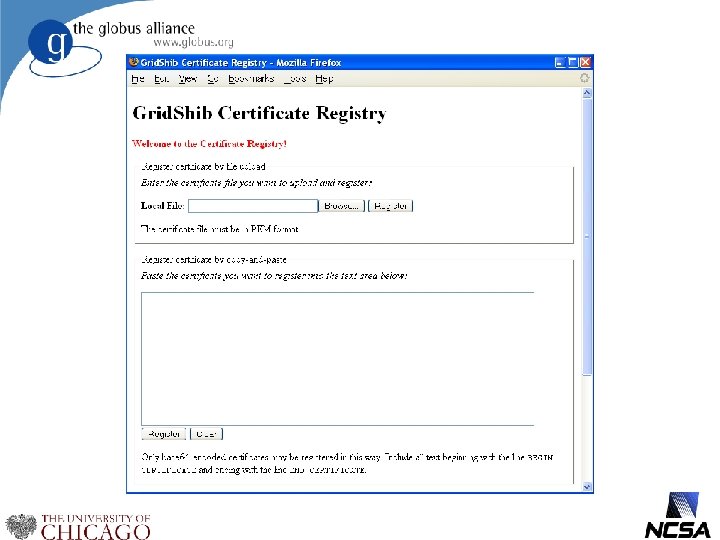
Grid. Shib Certificate Registry l A Certificate Registry is integrated into Grid. Shib for Shibboleth 0. 5: https: //authdev. it. ohio-state. edu/twiki/bin/view/Grid. Shib. Certificate. Registry l An established grid user authenticates and registers an X. 509 end-entity cert l The Registry binds the cert to the principal name and persists the binding in a database l On the backend, Grid. Shib maps the DN in a query to a principal name in the DB
Grid. Shib Authn Assertion Client l The Grid. Shib Authn Assertion Client is a standalone tool that creates an X. 509 proxy certificate with bound SAML authn assertion l The client uses the proxy to authenticate to a Grid SP l The Grid SP queries a Shibboleth AA based on the information in the bound SAML assertion
Shibboleth Id. P Tester l The Shibboleth Id. P Tester is a tool that queries a Shibboleth AA for attributes l The Id. P Tester can be used to: l u Test an ordinary Shibboleth AA u Test a Grid. Shib-enabled AA The Id. P Tester installs as a Shib Id. P extension (i. e. , it does not disturb an existing Shib deployment)
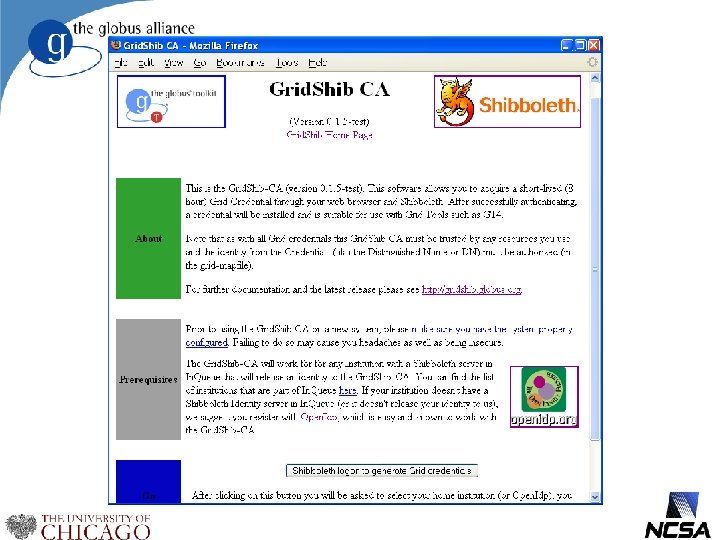
Grid. Shib CA l The Grid. Shib Certificate Authority is a webbased CA for new grid users: https: //authdev. it. ohio-state. edu/twiki/bin/view/Grid. Shib. Certificate. Authority l The Grid. Shib CA is protected by a Shib SP and backended by either Open. SSL or the My. Proxy Online CA l The CA issues short-term credentials suitable for authentication to a Grid SP l Credentials are downloaded to the desktop via Java Web Start
Globus SAML Library l Grid. Shib forked the Open. SAML 1. 1 source library in Jan 2006 l Globus SAML Library is in synch with Open. SAML 1. 1 CVS HEAD l Globus SAML Library is bundled with Grid. Shib for GT l Globus SAML Library adds new features to Open. SAML 1. 1
Outline l Grid. Shib Overview l Grid. Shib Components l Grid. Shib Profiles l Grid. Shib Roadmap
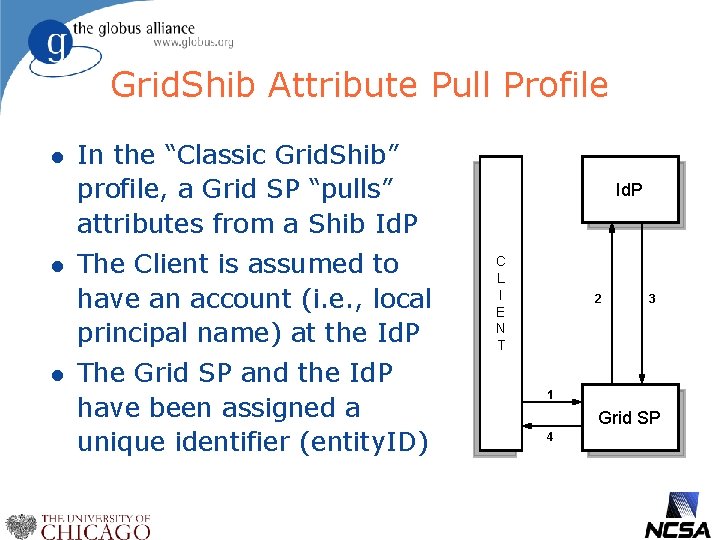
Grid. Shib Attribute Pull Profile l l l In the “Classic Grid. Shib” profile, a Grid SP “pulls” attributes from a Shib Id. P The Client is assumed to have an account (i. e. , local principal name) at the Id. P The Grid SP and the Id. P have been assigned a unique identifier (entity. ID) Id. P C L I E N T 2 3 1 Grid SP 4
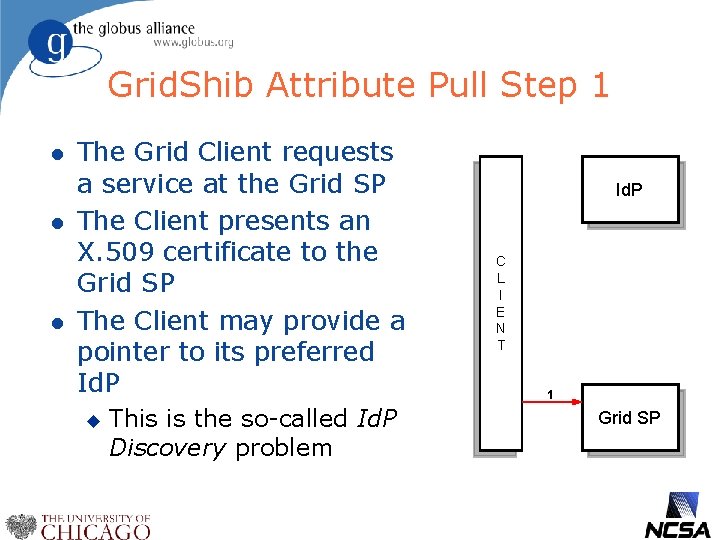
Grid. Shib Attribute Pull Step 1 l l l The Grid Client requests a service at the Grid SP The Client presents an X. 509 certificate to the Grid SP The Client may provide a pointer to its preferred Id. P u This is the so-called Id. P Discovery problem Id. P C L I E N T 1 Grid SP
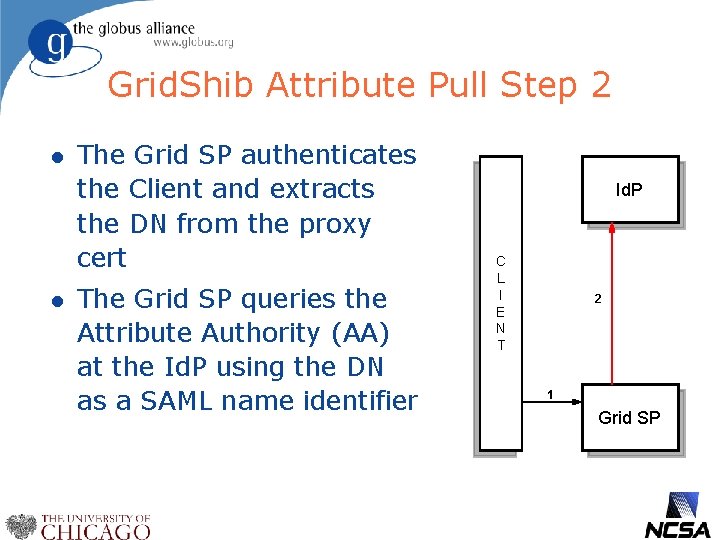
Grid. Shib Attribute Pull Step 2 l l The Grid SP authenticates the Client and extracts the DN from the proxy cert The Grid SP queries the Attribute Authority (AA) at the Id. P using the DN as a SAML name identifier Id. P C L I E N T 2 1 Grid SP
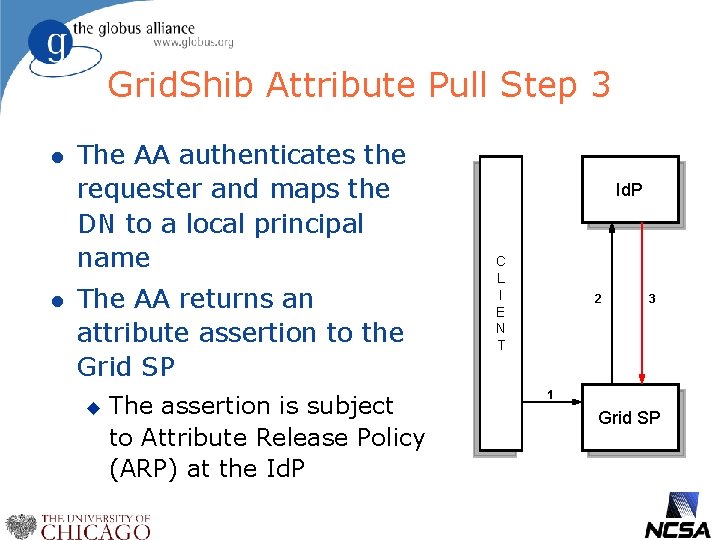
Grid. Shib Attribute Pull Step 3 l l The AA authenticates the requester and maps the DN to a local principal name The AA returns an attribute assertion to the Grid SP u The assertion is subject to Attribute Release Policy (ARP) at the Id. P C L I E N T 2 3 1 Grid SP
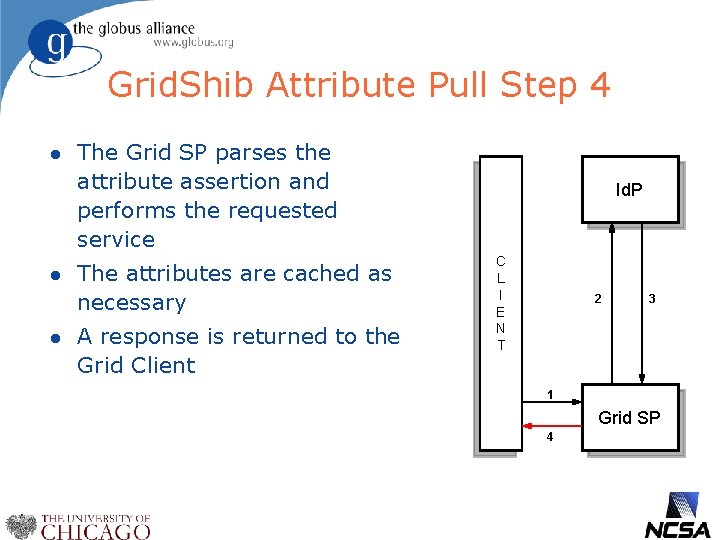
Grid. Shib Attribute Pull Step 4 l l l The Grid SP parses the attribute assertion and performs the requested service The attributes are cached as necessary A response is returned to the Grid Client Id. P C L I E N T 2 3 1 Grid SP 4
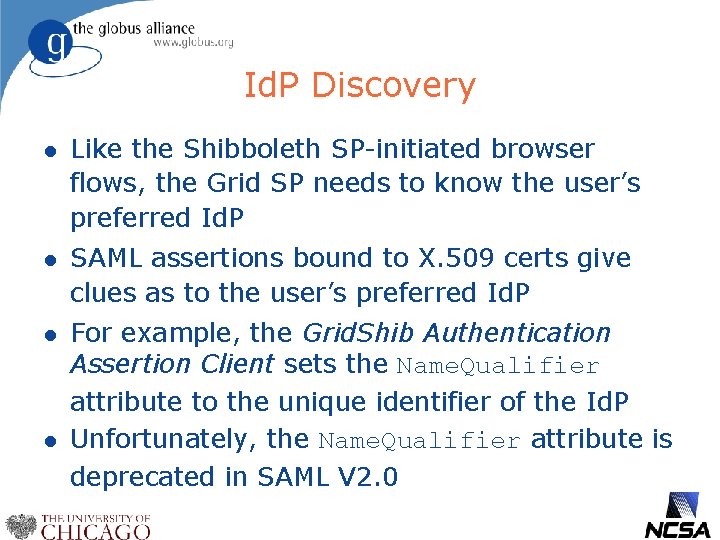
Id. P Discovery l Like the Shibboleth SP-initiated browser flows, the Grid SP needs to know the user’s preferred Id. P l SAML assertions bound to X. 509 certs give clues as to the user’s preferred Id. P l For example, the Grid. Shib Authentication Assertion Client sets the Name. Qualifier attribute to the unique identifier of the Id. P Unfortunately, the Name. Qualifier attribute is deprecated in SAML V 2. 0 l
Id. P Discovery (cont’d) l The Issuer attribute is a better indicator of the user’s preferred Id. P l However, for self-issued assertions (assertion issuer == certificate issuer) the Issuer is a DN, which doesn’t help Id. P discovery l Solution: Set the X. 509 Subject Information Access extension to the Id. P entity. ID
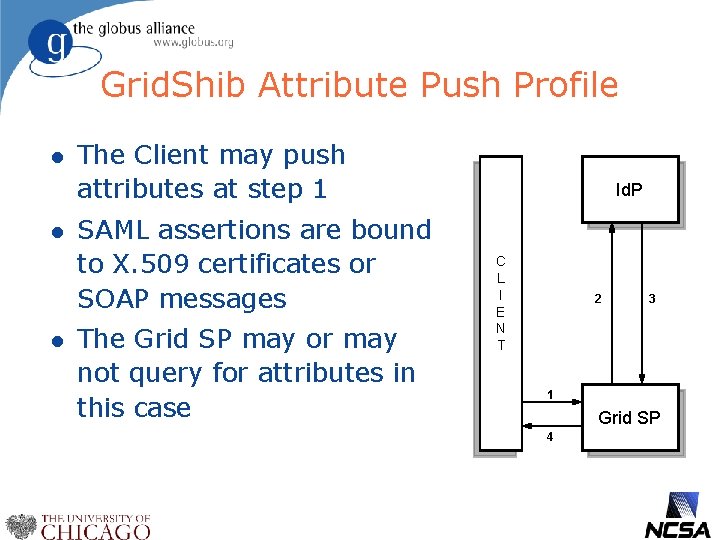
Grid. Shib Attribute Push Profile l l l The Client may push attributes at step 1 SAML assertions are bound to X. 509 certificates or SOAP messages The Grid SP may or may not query for attributes in this case Id. P C L I E N T 2 3 1 Grid SP 4
Outline l Grid. Shib Overview l Grid. Shib Components l Grid. Shib Profiles l Grid. Shib Roadmap
Online Roadmap l We present current plans and timelines l Roadmap online at Grid. Shib dev. globus incubator site http: //dev. globus. org/wiki/Grid. Shib_Development_Roadmap l Roadmap will be maintained as work progresses, check web page for updates
Attribute Push l For the past six months, Grid. Shib has concentrated on attribute push l Advantages of attribute push: u l Id. P Discovery is less of an issue Disadvantages of attribute push: u What to push? (we call this “SP Discovery”)
Grid. Shib X. 509 Certificate l The anatomy of an X. 509 certificate suitable for Grid. Shib attribute push: short lifetime u Id. P entity. ID in Subject Information Access extension u SAML Subject in the Subject Alt Name extension u SAML assertion(s) bound to X. 509 v 3 certificate extension u SSO assertion(s) nested in the Advice element of a bound SAML assertion u
X. 509 Binding for SAML l We bind an ASN. 1 SEQUENCE of SAML elements at a well-known, non-critical X. 509 v 3 certificate extension l Grid. Shib and Globus CAS already have limited ability to bind <Assertion> elements to X. 509 proxy certificates l Future versions of the Grid. Shib CA will bind SAML to end-entity certificates
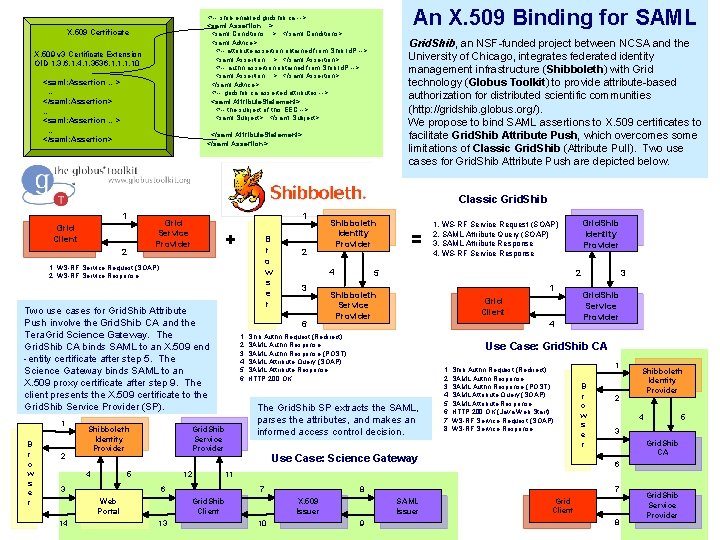
An X. 509 Binding for SAML <!-- shib-enabled gridshib ca --> <saml: Assertion. . . > <saml: Conditions. . . >. . . </saml: Conditions> <saml: Advice> <!-- attribute assertion obtained from Shib Id. P --> <saml: Assertion. . . >. . . </saml: Assertion> <!-- authn assertion obtained from Shib Id. P --> <saml: Assertion. . . >. . . </saml: Assertion> </saml: Advice> <!-- gridshib ca-asserted attributes --> <saml: Attribute. Statement> <!-- the subject of this EEC --> <saml: Subject>. . . </saml: Attribute. Statement> </saml: Assertion> X. 509 Certificate X. 509 v 3 Certificate Extension OID 1. 3. 6. 1. 4. 1. 3536. 1. 10 <saml: Assertion …> … </saml: Assertion> … <saml: Assertion …> … </saml: Assertion> Grid. Shib, an NSF-funded project between NCSA and the University of Chicago, integrates federated identity management infrastructure (Shibboleth) with Grid technology (Globus Toolkit) to provide attribute-based authorization for distributed scientific communities (http: //gridshib. globus. org/). We propose to bind SAML assertions to X. 509 certificates to facilitate Grid. Shib Attribute Push, which overcomes some limitations of Classic Grid. Shib (Attribute Pull). Two use cases for Grid. Shib Attribute Push are depicted below. Classic Grid. Shib 1 1 Grid Service Provider Grid Client 2 + 1. WS-RF Service Request (SOAP) 2. WS-RF Service Response Two use cases for Grid. Shib Attribute Push involve the Grid. Shib CA and the Tera. Grid Science Gateway. The Grid. Shib CA binds SAML to an X. 509 end -entity certificate after step 5. The Science Gateway binds SAML to an X. 509 proxy certificate after step 9. The client presents the X. 509 certificate to the Grid. Shib Service Provider (SP). 1 B r o w s e r 2 Shibboleth Identity Provider 4 12 3 14 3 = Grid. Shib Identity Provider 1. WS-RF Service Request (SOAP) 2. SAML Attribute Query (SOAP) 3. SAML Attribute Response 4. WS-RF Service Response 5 2 1 Shibboleth Service Provider Grid Client 4 3 Grid. Shib Service Provider Use Case: Grid. Shib CA The Grid. Shib SP extracts the SAML, parses the attributes, and makes an informed access control decision. 1. Shib Authn Request (Redirect) 2. SAML Authn Response 3. SAML Authn Response (POST) 4. SAML Attribute Query (SOAP) 5. SAML Attribute Response 6. HTTP 200 OK (Java Web Start) 7. WS-RF Service Request (SOAP) 8. WS-RF Service Response Use Case: Science Gateway 1 B r o w s e r 2 Shibboleth Identity Provider 4 5 3 Grid. Shib CA 6 11 7 Grid. Shib Client 13 4 6 6 Web Portal 2 1. Shib Authn Request (Redirect) 2. SAML Authn Response 3. SAML Authn Response (POST) 4. SAML Attribute Query (SOAP) 5. SAML Attribute Response 6. HTTP 200 OK Grid. Shib Service Provider 5 B r o w s e r Shibboleth Identity Provider 10 7 8 X. 509 Issuer SAML Issuer 9 Grid Client 8 Grid. Shib Service Provider
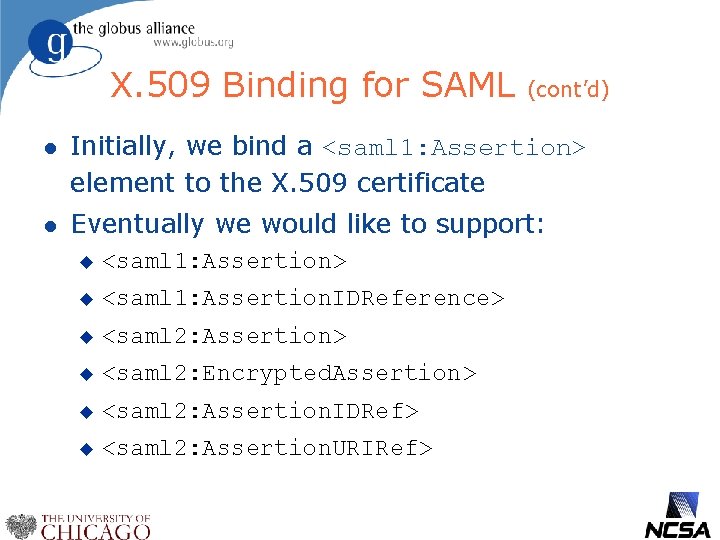
X. 509 Binding for SAML (cont’d) l Initially, we bind a <saml 1: Assertion> element to the X. 509 certificate l Eventually we would like to support: u <saml 1: Assertion> u <saml 1: Assertion. IDReference> u <saml 2: Assertion> u <saml 2: Encrypted. Assertion> u <saml 2: Assertion. IDRef> u <saml 2: Assertion. URIRef>
X. 509 Binding: Use Cases l Presenter is the Subject Principal Self-assertion u Principal Self-query u Shib-enabled Grid. Shib CA u My. Proxy Online CA u Community Authorization Service u l Presenter Acting on Behalf of the Subject: nano. HUB Pull u National Virtual Observatory (NVO) Push u Shib-enabled Science Gateway u
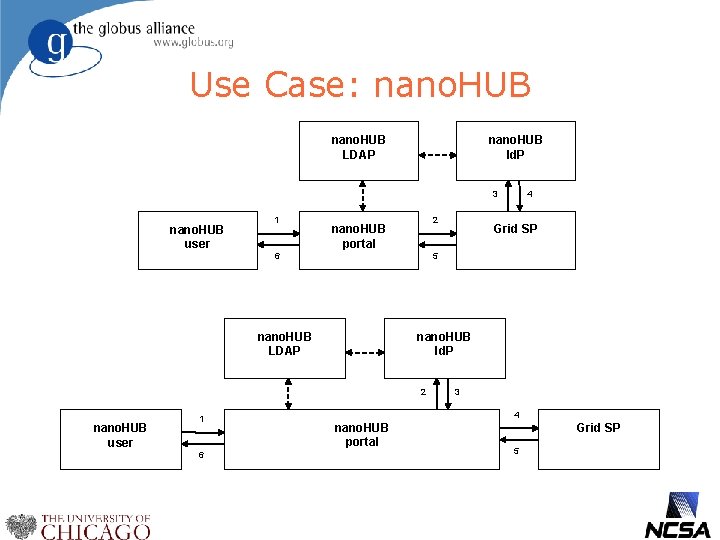
Use Case: nano. HUB LDAP nano. HUB Id. P 3 nano. HUB user 1 2 nano. HUB portal 6 nano. HUB Id. P 2 nano. HUB user 6 Grid SP 5 nano. HUB LDAP 1 4 3 4 nano. HUB portal Grid SP 5
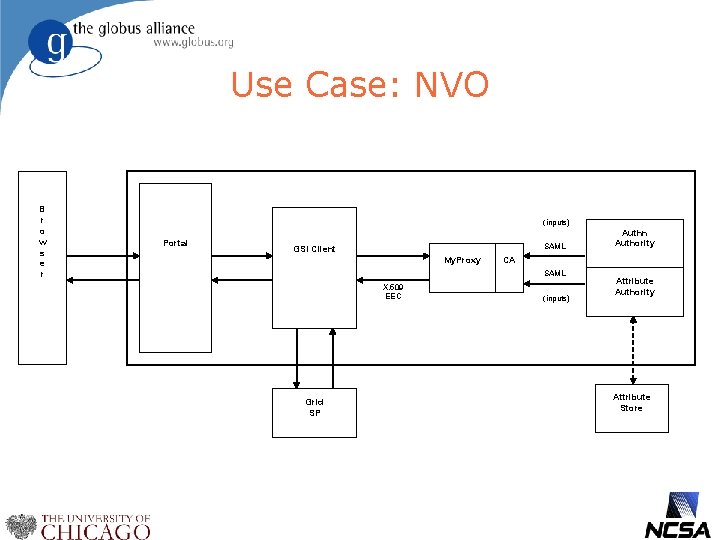
Use Case: NVO B r o w s e r (inputs) Portal SAML GSI Client My. Proxy CA SAML X. 509 EEC Grid SP Authn Authority (inputs) Attribute Authority Attribute Store
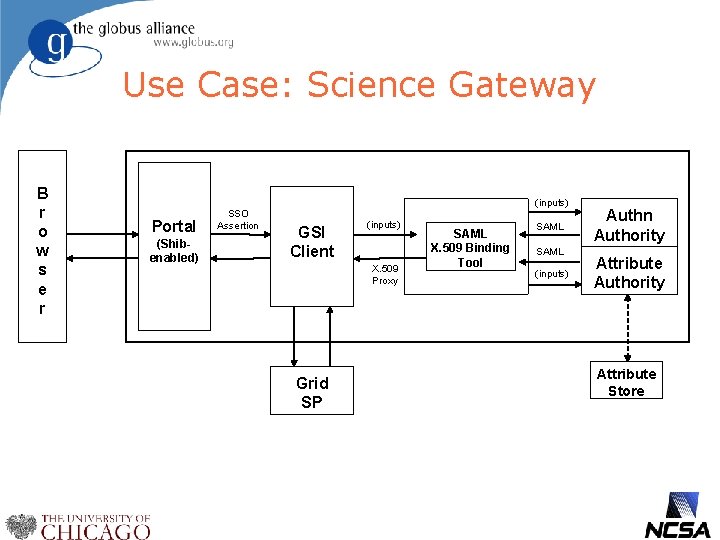
Use Case: Science Gateway B r o w s e r (inputs) Portal (Shibenabled) SSO Assertion GSI Client (inputs) X. 509 Proxy Grid SP SAML X. 509 Binding Tool SAML (inputs) Authn Authority Attribute Store
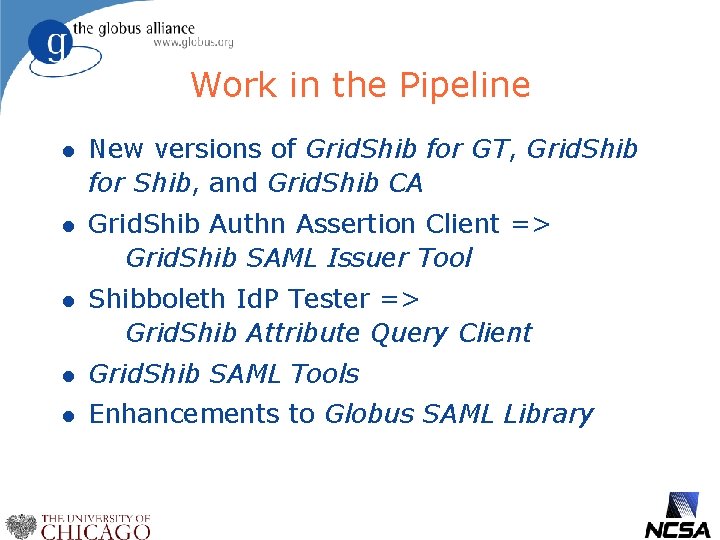
Work in the Pipeline l New versions of Grid. Shib for GT, Grid. Shib for Shib, and Grid. Shib CA l Grid. Shib Authn Assertion Client => Grid. Shib SAML Issuer Tool l Shibboleth Id. P Tester => Grid. Shib Attribute Query Client l Grid. Shib SAML Tools l Enhancements to Globus SAML Library
Grid. Shib for GT Versions l Grid. Shib for GT 0. 5 u l Grid. Shib for GT 0. 5. 1 u l Announced Nov 30, 2006 Expected ? Grid. Shib for GT 0. 6 u Expected ?
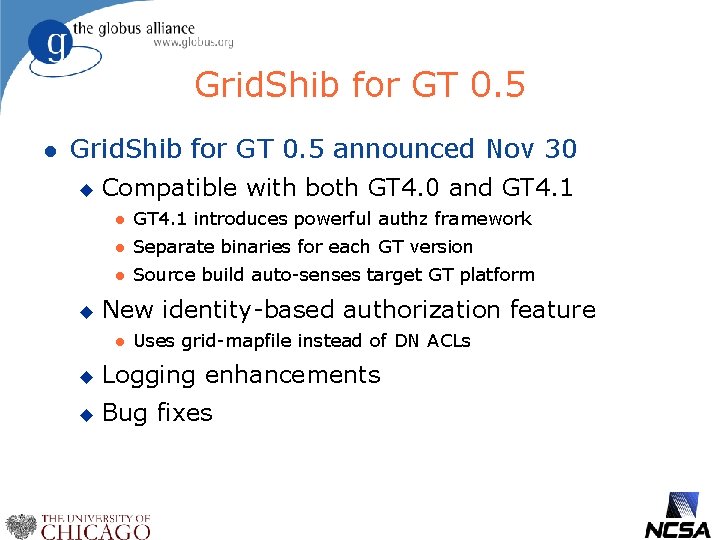
Grid. Shib for GT 0. 5 l Grid. Shib for GT 0. 5 announced Nov 30 u u Compatible with both GT 4. 0 and GT 4. 1 l GT 4. 1 introduces powerful authz framework l Separate binaries for each GT version l Source build auto-senses target GT platform New identity-based authorization feature l Uses grid-mapfile instead of DN ACLs u Logging enhancements u Bug fixes
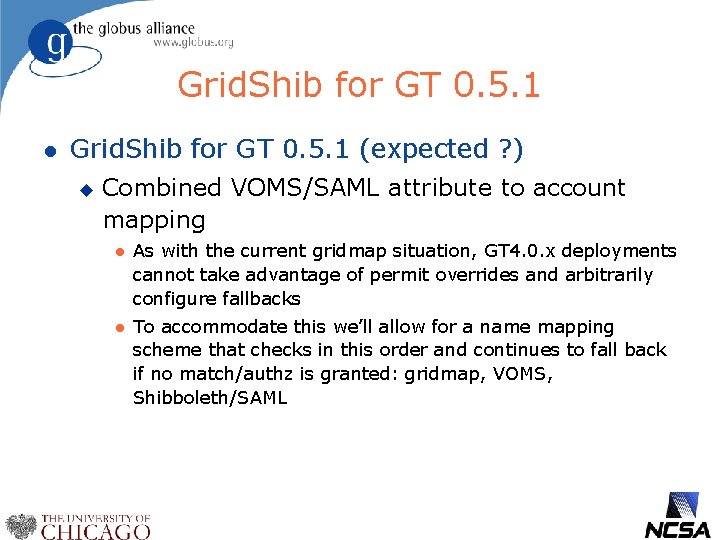
Grid. Shib for GT 0. 5. 1 l Grid. Shib for GT 0. 5. 1 (expected ? ) u Combined VOMS/SAML attribute to account mapping l As with the current gridmap situation, GT 4. 0. x deployments cannot take advantage of permit overrides and arbitrarily configure fallbacks l To accommodate this we’ll allow for a name mapping scheme that checks in this order and continues to fall back if no match/authz is granted: gridmap, VOMS, Shibboleth/SAML
Grid. Shib for GT 0. 6 l Grid. Shib for GT 0. 6 (expected ? ) u Full-featured attribute push PIP l u TBA More powerful attribute-based authz policies l Allow unique issuer in authz policy rules
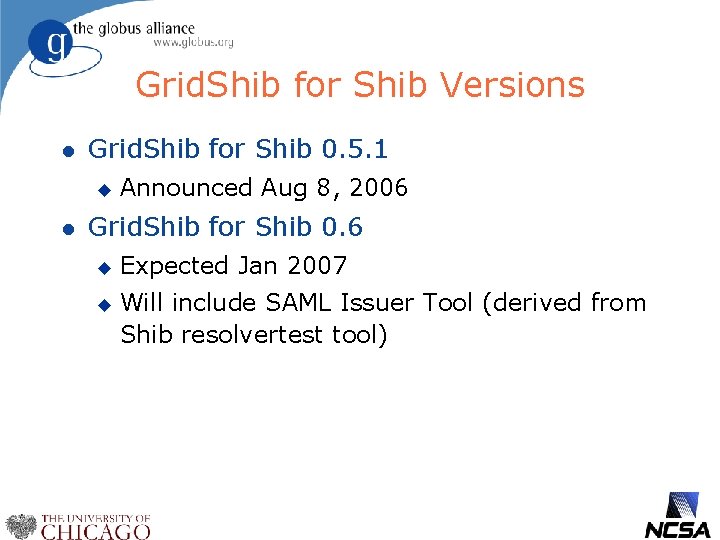
Grid. Shib for Shib Versions l Grid. Shib for Shib 0. 5. 1 u l Announced Aug 8, 2006 Grid. Shib for Shib 0. 6 u u Expected Jan 2007 Will include SAML Issuer Tool (derived from Shib resolvertest tool)
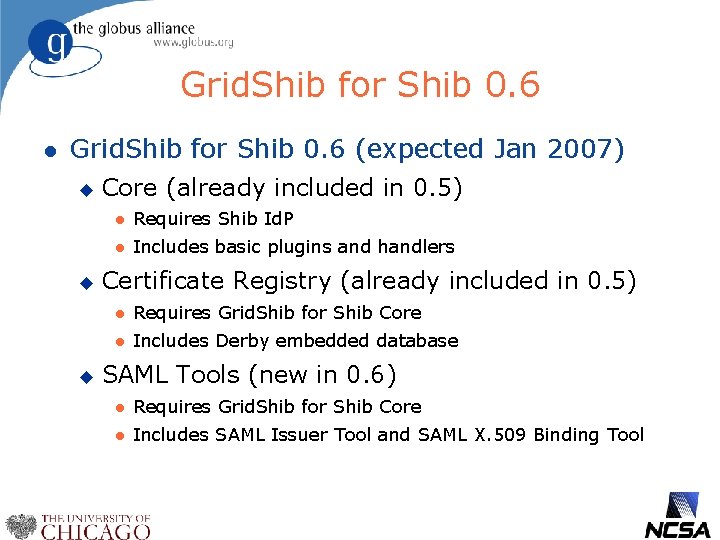
Grid. Shib for Shib 0. 6 l Grid. Shib for Shib 0. 6 (expected Jan 2007) u u u Core (already included in 0. 5) l Requires Shib Id. P l Includes basic plugins and handlers Certificate Registry (already included in 0. 5) l Requires Grid. Shib for Shib Core l Includes Derby embedded database SAML Tools (new in 0. 6) l Requires Grid. Shib for Shib Core l Includes SAML Issuer Tool and SAML X. 509 Binding Tool
Grid. Shib CA Versions l Grid. Shib CA 0. 3 u l Announced Nov 27, 2006 Grid. Shib CA 0. 4 u Expected March, 2007
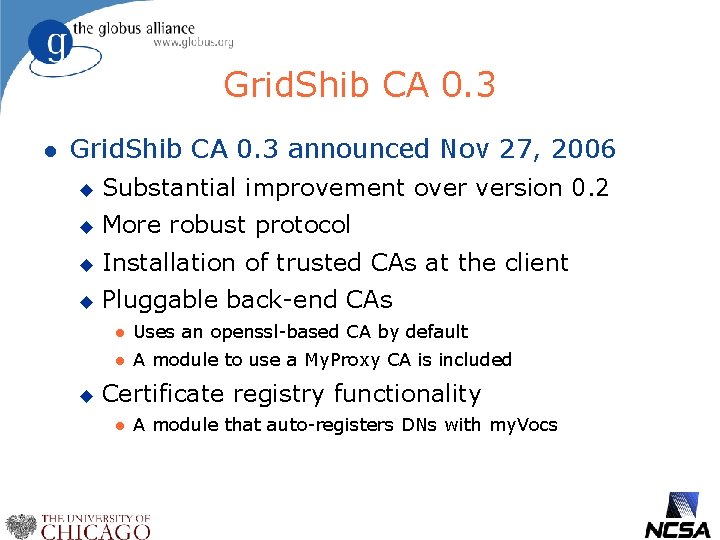
Grid. Shib CA 0. 3 l Grid. Shib CA 0. 3 announced Nov 27, 2006 u Substantial improvement over version 0. 2 u More robust protocol u Installation of trusted CAs at the client u Pluggable back-end CAs u l Uses an openssl-based CA by default l A module to use a My. Proxy CA is included Certificate registry functionality l A module that auto-registers DNs with my. Vocs
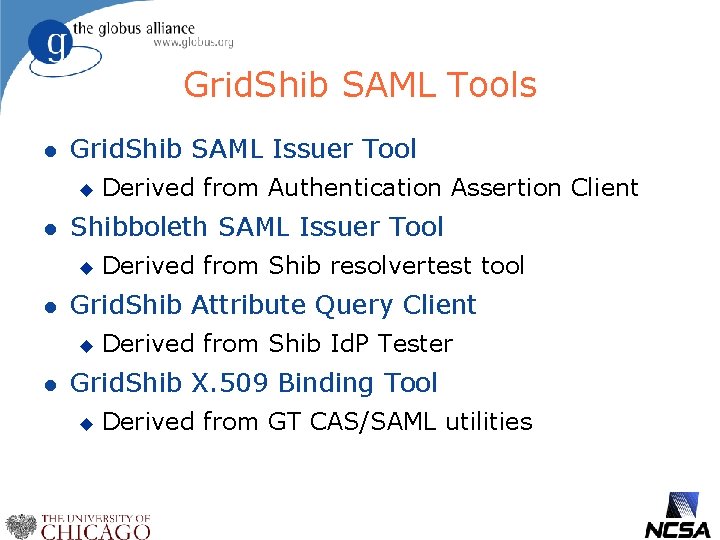
Grid. Shib SAML Tools l Grid. Shib SAML Issuer Tool u l Shibboleth SAML Issuer Tool u l Derived from Shib resolvertest tool Grid. Shib Attribute Query Client u l Derived from Authentication Assertion Client Derived from Shib Id. P Tester Grid. Shib X. 509 Binding Tool u Derived from GT CAS/SAML utilities
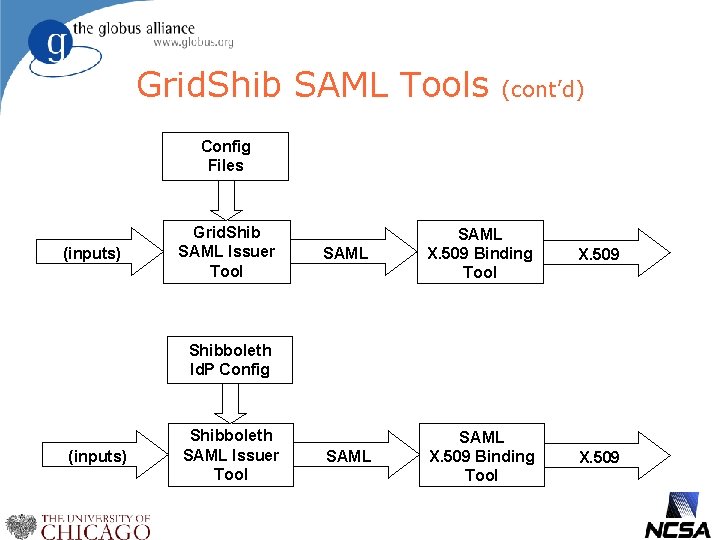
Grid. Shib SAML Tools (cont’d) Config Files (inputs) Grid. Shib SAML Issuer Tool SAML X. 509 Binding Tool X. 509 Shibboleth Id. P Config (inputs) Shibboleth SAML Issuer Tool
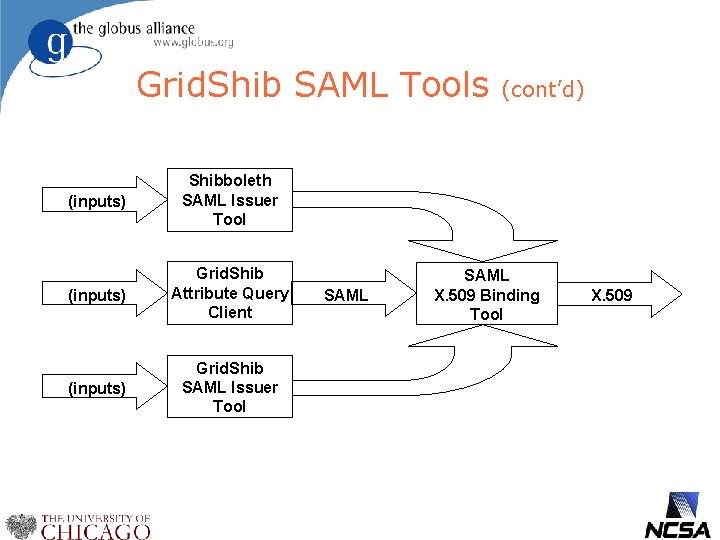
Grid. Shib SAML Tools (cont’d) (inputs) Shibboleth SAML Issuer Tool (inputs) Grid. Shib Attribute Query Client (inputs) Grid. Shib SAML Issuer Tool SAML X. 509 Binding Tool X. 509
SAML Tool Distributions l The Shib SAML Issuer Tool and the SAML X. 509 Binding Tool will be distributed with Grid. Shib for Shib 0. 6 l The Grid. Shib SAML Issuer Tool, Grid. Shib Attribute Query Client, and SAML X. 509 Binding Tool will be distributed as a single, standalone package l Note: The latter does not require Grid. Shib for Shib or Grid. Shib for GT
Globus SAML Library l Features and enhancements: u Support for SAML V 2. 0 metadata u SAML object equivalence implementation u Enhanced SAMLName. Identifier class u SAML Name. Identifier format handlers u New SAMLSubject. Assertion class u New Subject. Statement class u Additional unit tests and examples u Requires JDK 1. 4 or above
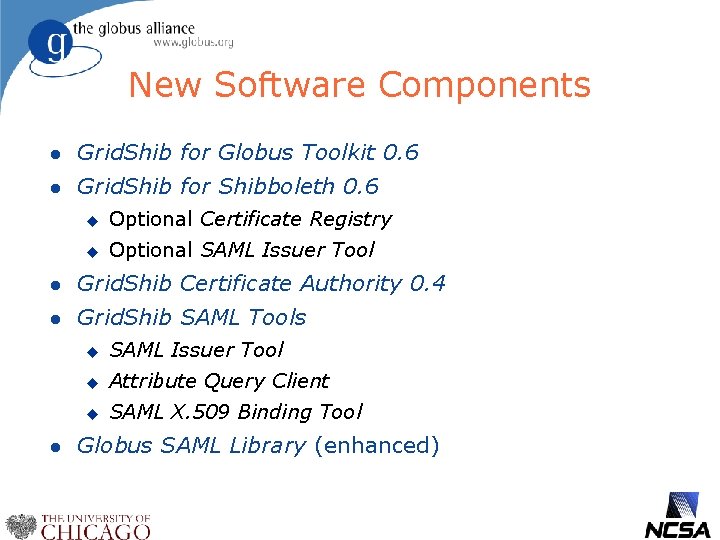
New Software Components l Grid. Shib for Globus Toolkit 0. 6 l Grid. Shib for Shibboleth 0. 6 u Optional Certificate Registry u Optional SAML Issuer Tool l Grid. Shib Certificate Authority 0. 4 l Grid. Shib SAML Tools l u SAML Issuer Tool u Attribute Query Client u SAML X. 509 Binding Tool Globus SAML Library (enhanced)
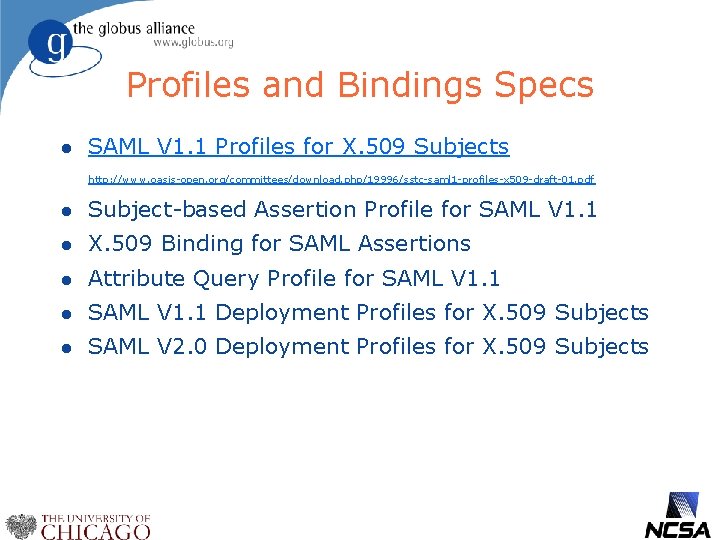
Profiles and Bindings Specs l SAML V 1. 1 Profiles for X. 509 Subjects http: //www. oasis-open. org/committees/download. php/19996/sstc-saml 1 -profiles-x 509 -draft-01. pdf l Subject-based Assertion Profile for SAML V 1. 1 l X. 509 Binding for SAML Assertions l Attribute Query Profile for SAML V 1. 1 l SAML V 1. 1 Deployment Profiles for X. 509 Subjects l SAML V 2. 0 Deployment Profiles for X. 509 Subjects
Acknowledgments l Grid. Shib is a project funded by the NSF Middleware Initiative u u l NMI awards 0438424 and 0438385 Opinions and recommendations are those of the authors and do not necessarily reflect the views of the National Science Foundation. Also many thanks to Internet 2 Shibboleth Project
Summary l l Grid. Shib has a number of tools for leveraging Shibboleth for the Grid Both for user authentication and attribute-based authorization Deploys easily on Shibboleth 1. 3 and Globus 4. 0 Available under Apache 2 license For more information and software: l http: //gridshib. globus. org l vwelch@ncsa. uiuc. edu l http: //dev. globus. org/wiki/Incubator/Grid. Shib
Questions?
- Slides: 61