Exploitbased BandwidthNetwork Analysis Framework Matt Weaver UCCS Spring
Exploit-based Bandwidth/Network Analysis Framework Matt Weaver UCCS Spring 2007
Abstract • Basic bandwidth tools are limited by network security. • An exploit could be used to infect machines on a network and provide metrics while overcoming the problems inherent in the traditional approach. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 2
Background • The Morris Worm – Robert Morris @ Cornell through MIT, 1988 – Government attention – Unix back doors, bad passwords. . . hacked any way possible • Hindsight: security wasn't a big enough factor. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 3
Related Work • Chen, G. and Gray, R. S. 2006. Simulating non-scanning worms on peer-to-peer networks. – How worms spread. – Effectiveness of different styles. • Kienzle, D. M. and Elder, M. C. 2003. Recent worms: a survey and trends. – Exploits are not innovative. • Zou, C. C. , Gong, W. , and Towsley, D. 2002. Code red worm propagation modeling and analysis. – Code Red infected Microsoft IIS (Internet Information Server) via buffer overflow. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 4

Buffer Overflow • In C, “strcpy” is not smart. – No bounds checking. – Write past the end of the buffer. • void bad_function(char *string) { char buffer[5]; strcpy(buffer, string); } int main(int argc, char* argv[]) { char a_large_string[] = "This string is far too big. Far, far too big. "; bad_function(a_large_string); exit(0); } 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 5
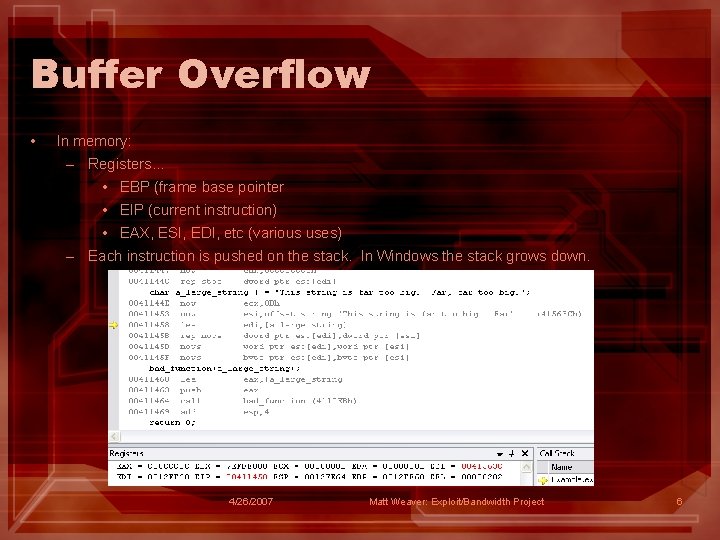
Buffer Overflow • In memory: – Registers. . . • EBP (frame base pointer • EIP (current instruction) • EAX, ESI, EDI, etc (various uses) – Each instruction is pushed on the stack. In Windows the stack grows down. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 6
Buffer Overflow • Options: – We can modify the return address: EBP and EIP will revert to the “calling” frame. If we “muck” with these values, we can modify the return address. – Overwrite EIP to make some other call (similar to the above). . . this is how real exploits work. You must somehow change the flow of execution. • Shellcode – Put machine instructions into the “extra” characters. They will look like regular instructions, we just have to jump into them. • Instruction have addresses where the machine code to execute them exists, these can be found with “dumpbin”. – In Windows/x 86, we can use a NOP sledge (no operation -> “x 90” in Shellcode). – Hard to get working right in Windows: • Variable instruction addresses: – A product of DLL-Hell inherited from VMS – Changes with patches, updates, and other products installed. • Security settings introduced in newer MS compilers. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 7
Using Overflow • In essence, create a new function with shellcode. • Modify EIP and EBP to point to our new “function”, that is the chunk of memory where our shellcode is loaded. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 8
Exploit Architecture • Follow the model of Russian exploits (SASSER, SLAMMER): – Surround payload with NOP (no operation) instructions – Modify EIP to execute our “function” • We won’t know exactly where it goes, but NOP instructions don’t do anything. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 9
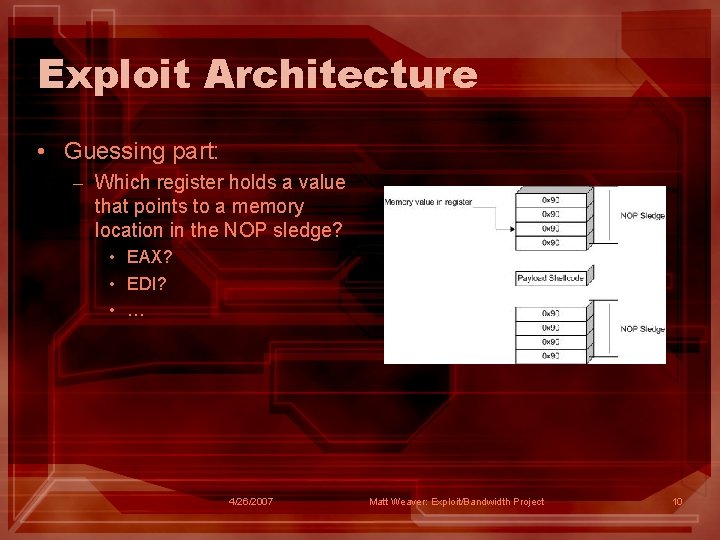
Exploit Architecture • Guessing part: – Which register holds a value that points to a memory location in the NOP sledge? • EAX? • EDI? • … 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 10
Exploit Architecture • The JMP instruction will overwrite EIP. – Hard-coding the JMP instruction is typical of Russian exploits. – Other, more complicated methods of finding instructions at runtime exist… but they are difficult to code and test. • No way to know “where” we will jump, but we try until we can get to our NOP sledge. • kernel 32. dll JMP instructions will “JMP EAX”, “JMP EDI”, etc. Since we don’t know what our target is doing… – We try a few, depending on the system we target (sometimes it just won’t work): • “ 0 x 77 EA 855 E” • “ 0 x 77 E 448 E 2” • Researchers have done the tricky disassembly debug and made lists for SP 0 (ex: https: //www. securinfos. info/international-opcodes/). 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 11
Exploit Architecture • Our JMP instruction will be the first thing executed after the overflow, rewriting the old EIP value on the stack: – We don’t want to call it twice… so the payload has to be “smart”. – Stick the JMP instruction AFTER the payload, in our “buffer”. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 12
Payload • The easy part (kind of)! – Tools can generate stable payloads, we can use Metasploit to generate new payloads for: • Starting a listener (call back with netcat). • Download and execute. • All kinds of things. – Not all payloads work with all exploits: • OS security features might disable certain calls. • Large payloads are easily detected by IDS… because legitimate transactions aren’t usually long strings of hex. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 13
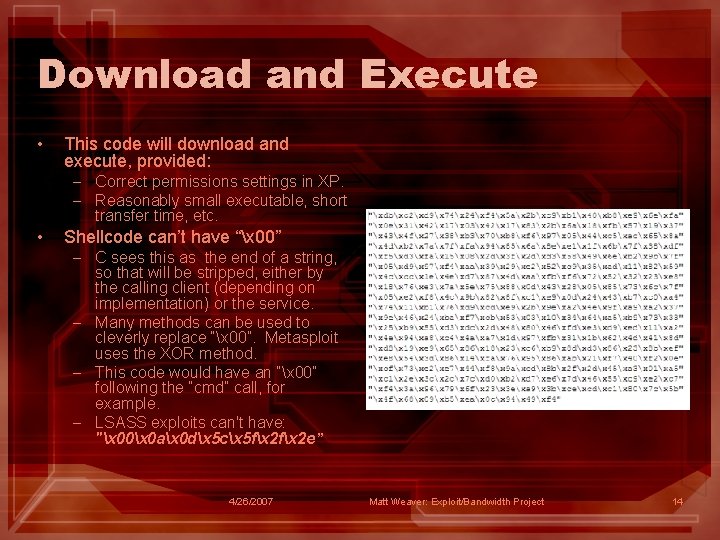
Download and Execute • This code will download and execute, provided: – Correct permissions settings in XP. – Reasonably small executable, short transfer time, etc. • Shellcode can’t have “x 00” – C sees this as the end of a string, so that will be stripped, either by the calling client (depending on implementation) or the service. – Many methods can be used to cleverly replace “x 00”. Metasploit uses the XOR method. – This code would have an “x 00” following the “cmd” call, for example. – LSASS exploits can't have: "x 00x 0 ax 0 dx 5 cx 5 fx 2 e” 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 14
One last thing on shellcode • Makes or breaks your overflow exploit. – Unfortunately, this isn’t always up to you. – Many variables are beyond your control. • The payload is easy, it’s the “getting to the payload” that is a “trying” process (pun intended). – If it doesn’t work, find a new exploit… SOL. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 15
sni. FF Architecture • sni. FF app starts user buildable exploits (via XML config file and the command line). – Captures data messages from clients. – With certain clients, acts as a sort of “parent lookup service” – Clients are downloaded and executed on remote machines. • Some clients will be blocked. • Not all exploits can complete download and execute. • Other options exist. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 16
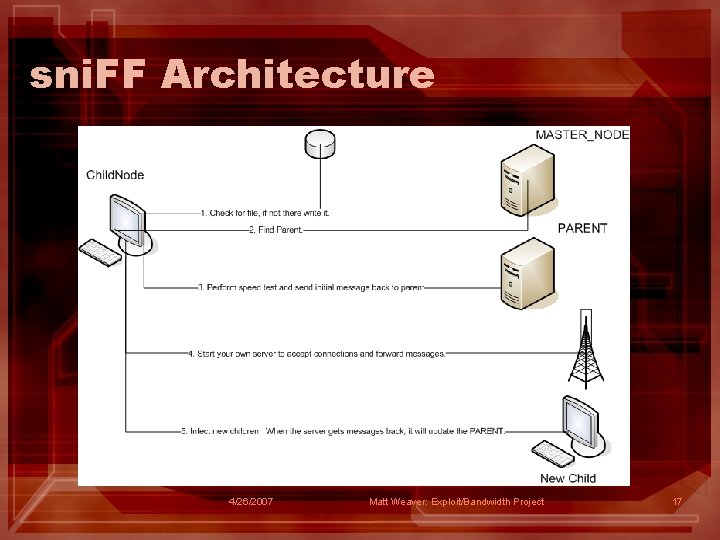
sni. FF Architecture 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 17

Tools/Technology • • • Visual Studio. NET 2002, 2003, 2005. – C, C++, C# – Utilities integrated into SDK: • Dumpbin – find addresses • MIDL – compiler for COM GCC/GDB (Cygwin and Bloodshed). – C, C++ Metasploit – Pre-existing exploit and payload generator. • • Write new modules in C or Perl. – Invaluable in exploit research, writing, and investigation. – Point to point attack only… not concerned with the payload part. SPIKE DCE-RPC browser – Inspect COM objects on a given machine Ethereal: packet sniffer Olly. Dbg: for debugging dlls. . . fuzzing. VMWare Workstation/Server Various incarnations of XP. Xcode: gcc/gdb on OS X (bash) for testing, education as Unix provides an easier place to learn. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 18
Lessons Learned • Exploits are nasty to write: – Win addressing problem – Not all payloads will work with a given exploit. • Windows poorly handles security – Never re-baselined, so lots of buggy code still exists. MS patches usually just move addresses around. – Exploits that don't work can still crash systems. – OS level services have mostly been blocked off (or hacked around by MS), newer overflow exploits focus on SQLServer, IIS, etc. • IT Experts shouldn't know about potential overflows and do nothing to fix them. – But with new Metasploit modules and new discoveries on milw 0 rm. com, we can keep trying. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 19

Basically. . . • Not like most CS problems: – Little “good” research has been done and documented. – You are mostly poking around in the dark, when it comes to development. – Constraints on imagination, versus technology. • Science versus gambling/hacking/hoping/guessing. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 20
Future Work • Convert sni. FF source to Mono and tinker with: Fedora Core, Ubuntu, Solaris, etc. • Write working instruction prowler shellcode for Windows: – All available text neglects to do this. – Examples that exist. . . don't actually work. • Get SASSER working with downloads. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 21
Aleph One. Smashing the Stack For Fun and Profit. Phrack (Volume seven, issue forty-nine; November 8, 1996). http: //www. phrack. org/phrack/49/P 49 -01 Anderson, Ross. Security Engineering: A Guide to Building Dependable Distributed Systems. New York, NY: John Wiley & Sons, Inc 2001. Blum, Richard. C# Network Programming. Alameda, CA: Sybex, 2003. Chen, G. and Gray, R. S. 2006. Simulating non-scanning worms on peerto-peer networks. In Proceedings of the 1 st international Conference on Scalable information Systems (Hong Kong, May 30 - June 01, 2006). Info. Scale '06, vol. 152. ACM Press, New York, NY, 29. DOI= http: //doi. acm. org/10. 1145/1146847. 1146876 Erickson, Jon. Hacking: The Art of Exploitation. San Francisco: No Startch Press, 2003.
Davis, Ralph. Win 32 Network Programming. New York: Addison-Wesley, 1996. Irvine, Kip R. Assembly Language For Intel-Based Computers. Saddle Hill, New Jersey: Prentice Hall, 2006. Kienzle, D. M. and Elder, M. C. 2003. Recent worms: a survey and trends. In Proceedings of the 2003 ACM Workshop on Rapid Malcode (Washington, DC, USA, October 27 - 27, 2003). WORM '03. ACM Press, New York, NY, 1 -10. DOI= http: //doi. acm. org/10. 1145/948187. 948189 Koziol, Jack et al. The Shellcoders Handbook. Indianapolis: Wiley Publishing, 2004. Petkov, K. 2005. Overcoming programming flaws: indexing of common software vulnerabilities. In Proceedings of the 2 nd Annual Conference on information Security Curriculum Development (Kennesaw, Georgia, September 23 - 24, 2005). Info. Sec. CD '05. ACM Press, New York, NY, 127 -134. DOI= http: //doi. acm. org/10. 1145/1107622. 1107652 Pfleeger, Charles P and Shari Lawrence Pfleeger. Security in Computing. Saddle Hill, New Jersey: Prentice Hall, 2003. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 23

Skape. Understanding Windows Shell code. December 6, 2003. nologin. org. 16 July 2006 Spangler, Ryan. Analysis of the Microsoft Windows LSASS Exploit. Packet Watch. http: //www. packetwatch. net/documents/papers/windows-lsass. pdf Sk. Advances in Windows Shell code. Phrack (Volume seven, issue sixty-two; June 22, 2004). Zou, C. C. , Gong, W. , and Towsley, D. 2002. Code red worm propagation modeling and analysis. In Proceedings of the 9 th ACM Conference on Computer and Communications Security (Washington, DC, USA, November 18 - 22, 2002). V. Atluri, Ed. CCS '02. ACM Press, New York, NY, 138 -147. DOI= http: //doi. acm. org/10. 1145/586110. 586130 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 24

Coda • Demo: – Pieces of sni. FF • Clients – Large client (recursive infection) – Lightweight client. • Configuration: – Write new exploits, plug them in! » Lots left to do. • In action: – Clients run conventionally. – Clients infecting XP no SP running bad service. » A view of the network. » Ethereal packet data. » Use Metasploit and LSASS (fixed it!) to infect a machine. » Use “bad service” to infect machine. – Nearest neighbour randomized infection (failure, but examine IPs generated). • A glance at the framework. 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 25
Voila! • Questions? 4/26/2007 Matt Weaver: Exploit/Bandwidth Project 26
- Slides: 26