Efficient Reversible Data Hiding Based on Multiple Histograms
Efficient Reversible Data Hiding Based on Multiple Histograms Modification Source: IEEE TRANSACTIONS ON INFORMATION FORENSICS AND SECURITY, VOL. 10, NO. 9, SEPTEMBER 2015 Authors: Xiaolong Li, Weiming Zhang, Xinlu Gui, and Bin Yang Speaker: Zhao. Hua Zhu Date: 12/01/2017
Outline • • Related Work Proposed Scheme Experiment Result Conclusions
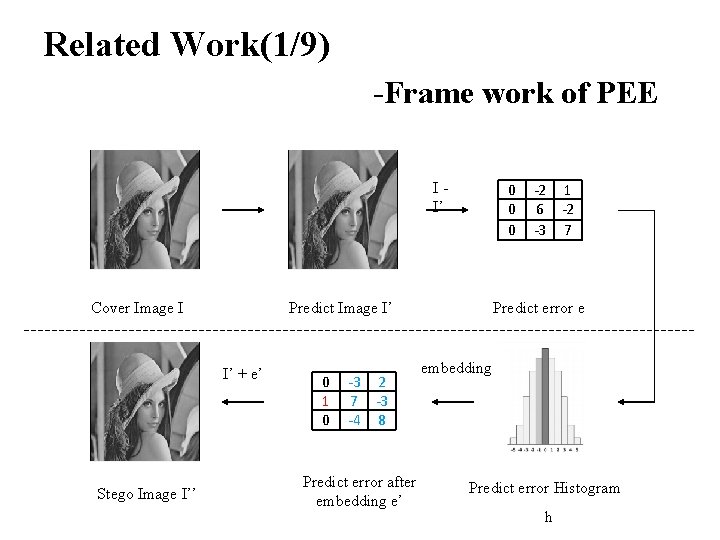
Related Work(1/9) -Frame work of PEE II’ Cover Image I Predict Image I’ I’ + e’ Stego Image I’’ 0 0 1 0 -3 2 7 -3 -4 8 Predict error after embedding e’ -2 1 6 -2 -3 7 Predict error e embedding Predict error Histogram h
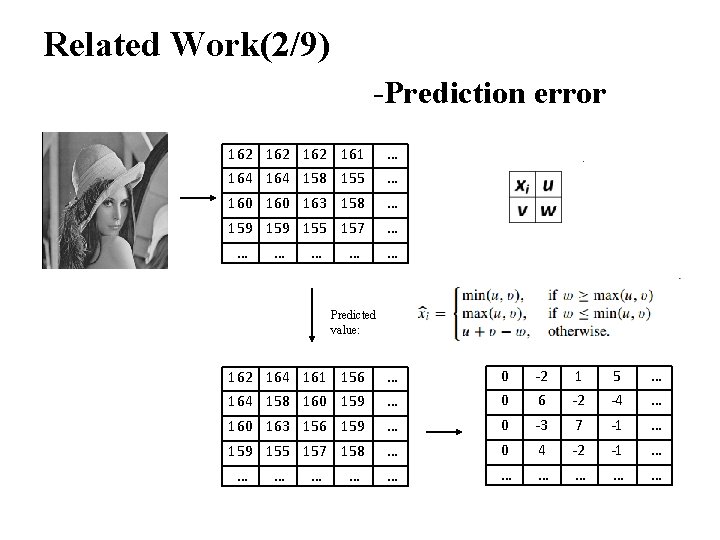
Related Work(2/9) -Prediction error 162 162 161 164 158 155 … … 160 163 158 … 159 155 157 … … … Predicted value: 162 164 161 156 164 158 160 159 … … 0 0 -2 6 1 -2 5 -4 … … 160 163 156 159 … 0 -3 7 -1 … 159 155 157 158 … 0 4 -2 -1 … … …
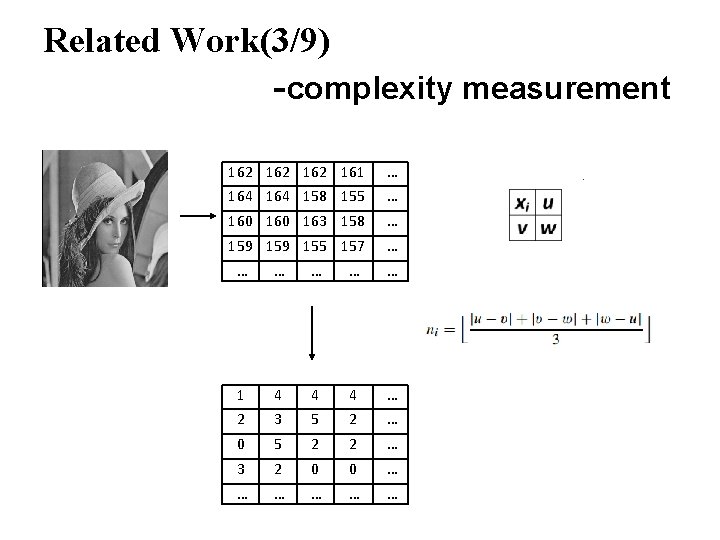
Related Work(3/9) -complexity measurement 162 162 161 164 158 155 … … 160 163 158 … 159 155 157 … … … 1 2 4 3 4 5 4 2 … … 0 5 2 2 … 3 2 0 0 … … …
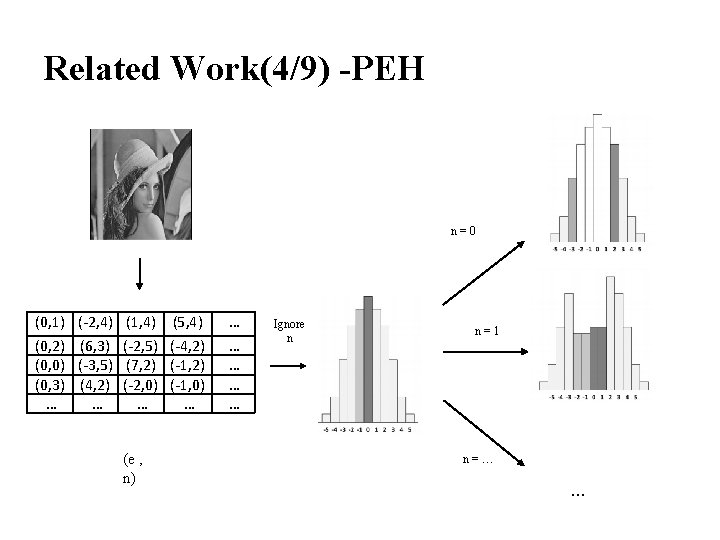
Related Work(4/9) -PEH n=0 (0, 1) (-2, 4) (1, 4) (5, 4) … (0, 2) (6, 3) (-2, 5) (-4, 2) (0, 0) (-3, 5) (7, 2) (-1, 2) (0, 3) (4, 2) (-2, 0) (-1, 0) … … … … (e , n) Ignore n n=1 n=… …
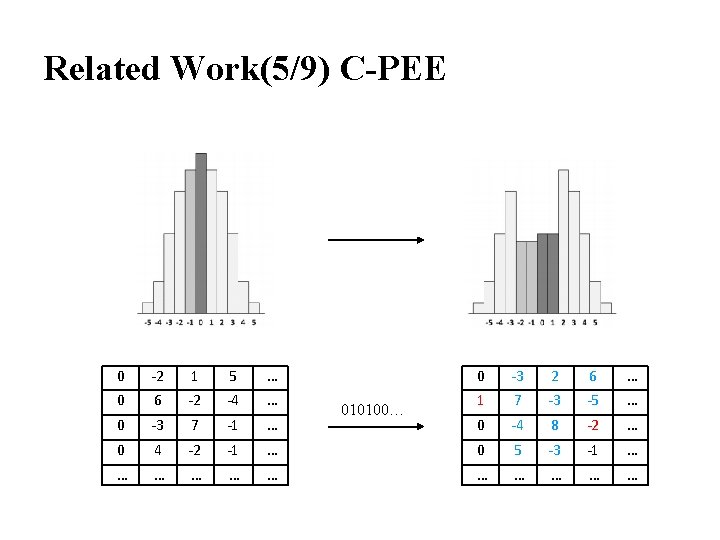
Related Work(5/9) C-PEE 0 0 -2 6 1 -2 5 -4 … … 0 1 -3 7 2 -3 6 -5 … … 0 -3 7 -1 … 0 -4 8 -2 … 0 4 -2 -1 … 0 5 -3 -1 … … … 010100…
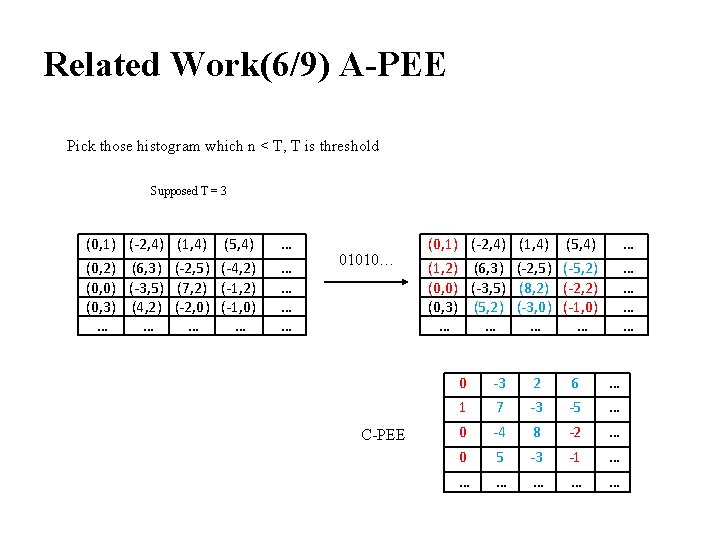
Related Work(6/9) A-PEE Pick those histogram which n < T, T is threshold Supposed T = 3 (0, 1) (-2, 4) (1, 4) (5, 4) … (0, 2) (6, 3) (-2, 5) (-4, 2) (0, 0) (-3, 5) (7, 2) (-1, 2) (0, 3) (4, 2) (-2, 0) (-1, 0) … … … … 01010… C-PEE (0, 1) (-2, 4) (1, 4) (5, 4) … (1, 2) (6, 3) (-2, 5) (-5, 2) (0, 0) (-3, 5) (8, 2) (-2, 2) (0, 3) (5, 2) (-3, 0) (-1, 0) … … … … 0 1 -3 7 2 -3 6 -5 … … 0 -4 8 -2 … 0 5 -3 -1 … … …
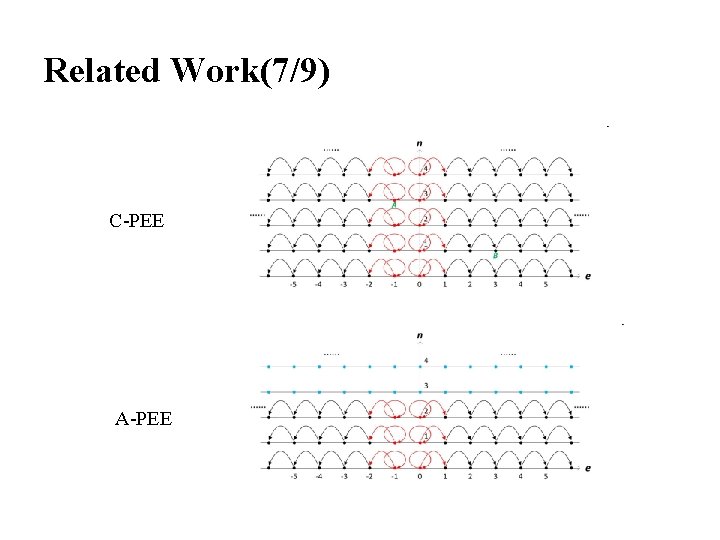
Related Work(7/9) C-PEE A-PEE
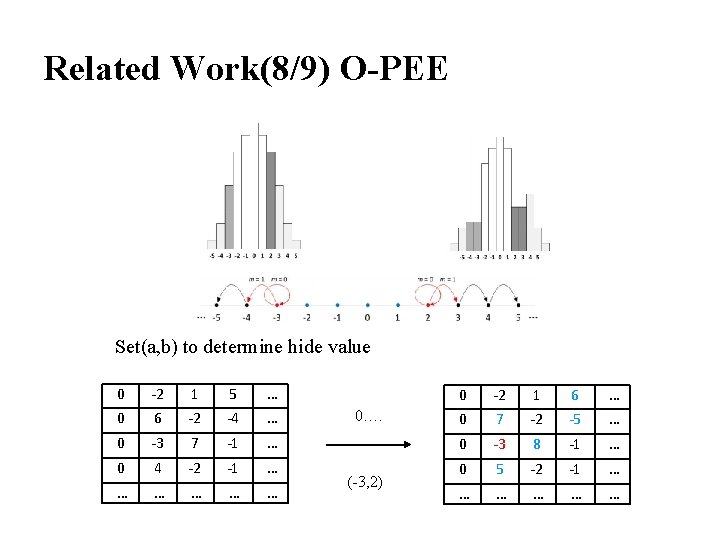
Related Work(8/9) O-PEE Set(a, b) to determine hide value 0 0 -2 6 1 -2 5 -4 … … 0 -3 7 -1 … 0 4 -2 -1 … … … 0…. (-3, 2) 0 0 -2 7 1 -2 6 -5 … … 0 -3 8 -1 … 0 5 -2 -1 … … …

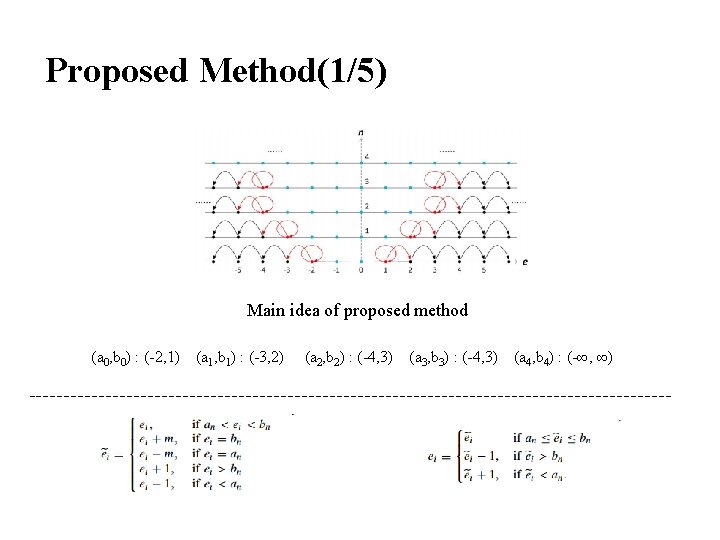
Proposed Method(1/5) Main idea of proposed method (a 0, b 0) : (-2, 1) (a 1, b 1) : (-3, 2) (a 2, b 2) : (-4, 3) (a 3, b 3) : (-4, 3) (a 4, b 4) : (-∞, ∞)
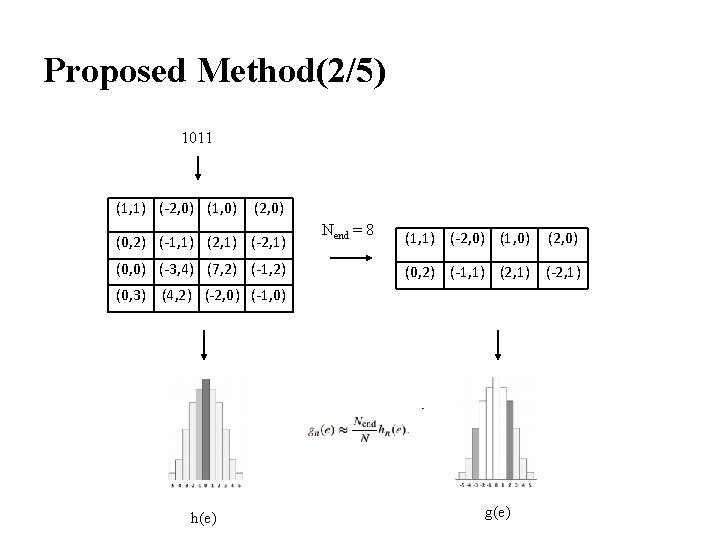
Proposed Method(2/5) 1011 (1, 1) (-2, 0) (1, 0) (2, 0) (0, 2) (-1, 1) (2, 1) (-2, 1) (0, 0) (-3, 4) (7, 2) (-1, 2) Nend = 8 (1, 1) (-2, 0) (1, 0) (2, 0) (0, 2) (-1, 1) (2, 1) (-2, 1) (0, 3) (4, 2) (-2, 0) (-1, 0) h(e) g(e)
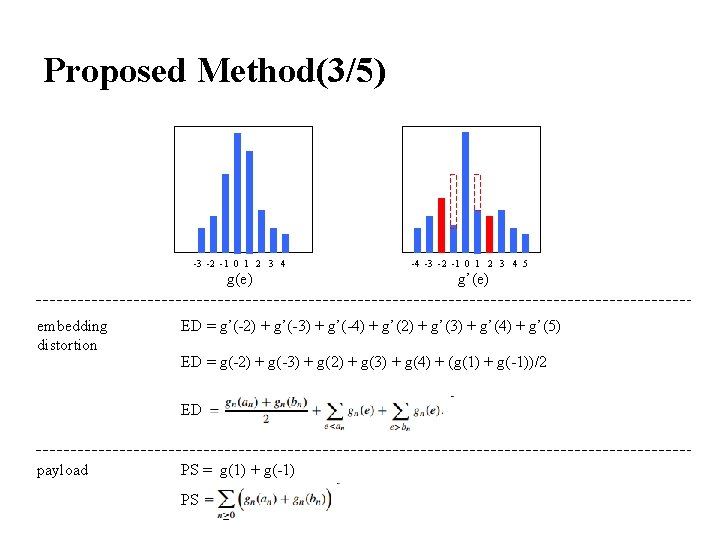
Proposed Method(3/5) -3 -2 -1 0 1 2 3 4 g(e) embedding distortion g’(e) ED = g’(-2) + g’(-3) + g’(-4) + g’(2) + g’(3) + g’(4) + g’(5) ED = g(-2) + g(-3) + g(2) + g(3) + g(4) + (g(1) + g(-1))/2 ED payload -4 -3 -2 -1 0 1 2 3 4 5 PS = g(1) + g(-1) PS
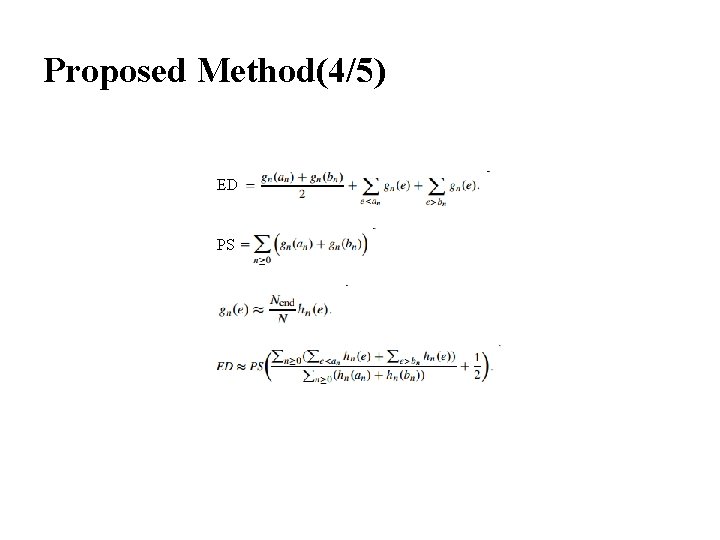
Proposed Method(4/5) ED PS
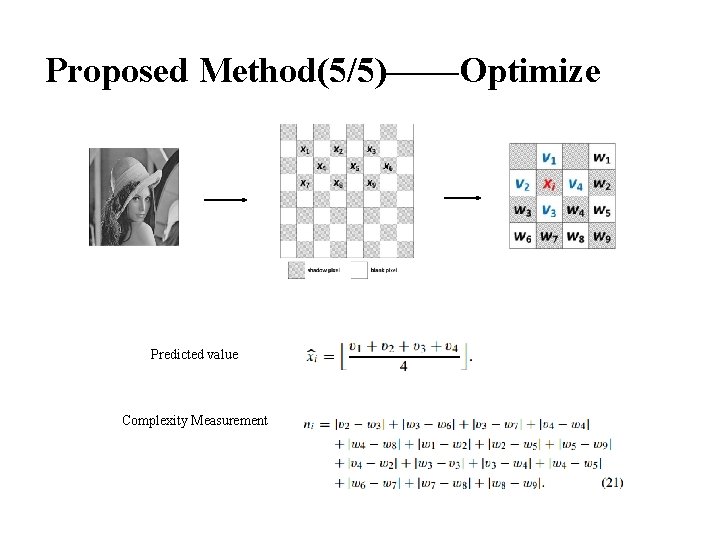
Proposed Method(5/5)——Optimize Predicted value Complexity Measurement
![Experiment Result(1/2) [29] W. Hong, T. -S. Chen, and C. -W. Shiu, “Reversible data Experiment Result(1/2) [29] W. Hong, T. -S. Chen, and C. -W. Shiu, “Reversible data](http://slidetodoc.com/presentation_image_h/2c96b291e23fe426bac245e2ab826571/image-17.jpg)
Experiment Result(1/2) [29] W. Hong, T. -S. Chen, and C. -W. Shiu, “Reversible data hiding for high quality images using modification of prediction errors, ” J. Syst. Softw. , vol. 82, no. 11, pp. 1833– 1842, Nov. 2009. [35] G. Coatrieux, W. Pan, N. Cuppens-Boulahia, F. Cuppens, and C. Roux, “Reversible watermarking based on invariant image classification and dynamic histogram shifting, ” IEEE Trans. Inf. Forensics Security, vol. 8, no. 1, pp. 111– 120, Jan. 2013. [40] V. Sachnev, H. J. Kim, J. Nam, S. Suresh, and Y. Q. Shi, “Reversible watermarking algorithm using sorting and prediction, ” IEEE Trans. Circuits Syst. Video Technol. , vol. 19, no. 7, pp. 989– 999, Jul. 2009. [44] C. Wang, X. Li, and B. Yang, “Efficient reversible image watermarking by using dynamical prediction-error expansion, ” in Proc. IEEE ICIP, Sep. 2010, pp. 3673– 3676. [48] X. Li, W. Zhang, X. Gui, and B. Yang, “A novel reversible data hiding scheme based on two-dimensional difference-histogram modification, ” IEEE Trans. Inf. Forensics Security, vol. 8, no. 7, pp. 1091– 1100, Jul. 2013. [49] B. Ou, X. Li, Y. Zhao, R. Ni, and Y. -Q. Shi, “Pairwise predictionerror expansion for efficient reversible data hiding, ” IEEE Trans. Image Process. , vol. 22, no. 12, pp. 5010– 5021, Dec. 2013. [55] H. J. Hwang, H. J. Kim, V. Sachnev, and S. H. Joo, “Reversible watermarking method using optimal histogram pair shifting based on prediction and sorting, ” KSII Trans. Internet Inf. Syst. , vol. 4, no. 4, pp. 655– 670, Aug. 2010.
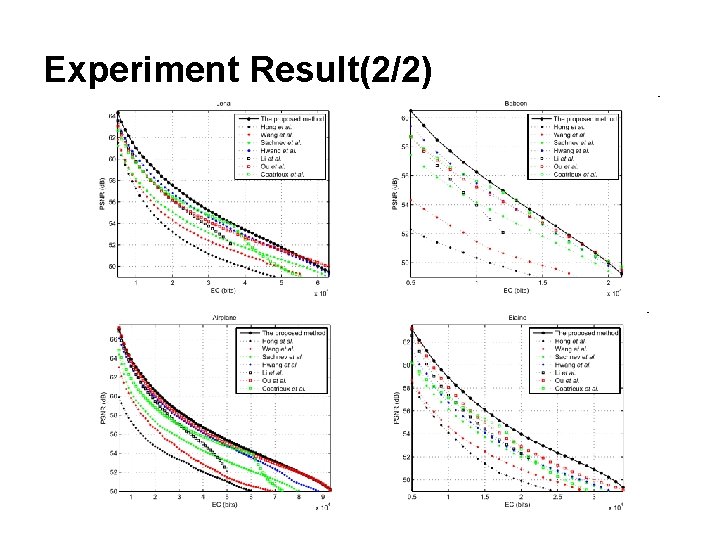
Experiment Result(2/2)
Conclusion • This method can achieve higher PSNR value than other method, but have limits in hiding capacity. I think this method can provide higher security of Image.
Thank You
- Slides: 20