ECE 111 Final Project Secure Hash Algorithm SHA1
![Module Interface • Very similar to Project 2 on RLE Co-Processor Done Hash[159: 0] Module Interface • Very similar to Project 2 on RLE Co-Processor Done Hash[159: 0]](https://slidetodoc.com/presentation_image_h/c719c0210ade0c735b1c2c65ce4379d9/image-17.jpg)
![Big-Endian vs. Little-Endian • Use this function [31: 0] change. Endian; //transform to big-endian Big-Endian vs. Little-Endian • Use this function [31: 0] change. Endian; //transform to big-endian](https://slidetodoc.com/presentation_image_h/c719c0210ade0c735b1c2c65ce4379d9/image-19.jpg)
- Slides: 22
ECE 111 Final Project Secure Hash Algorithm SHA-1
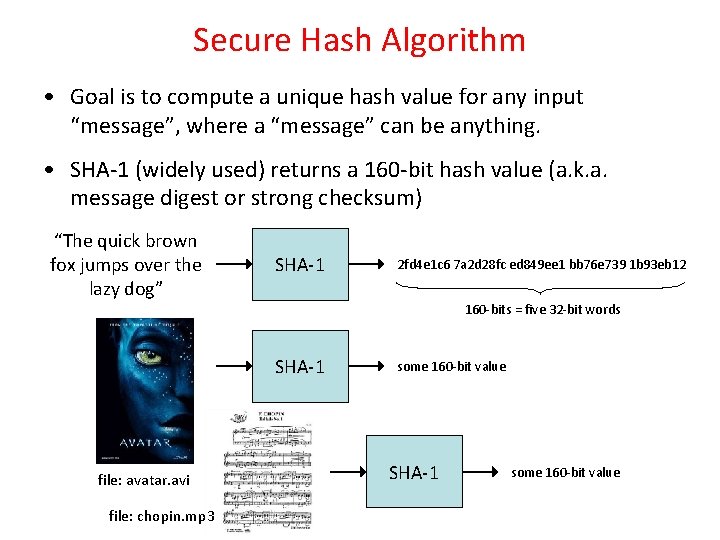
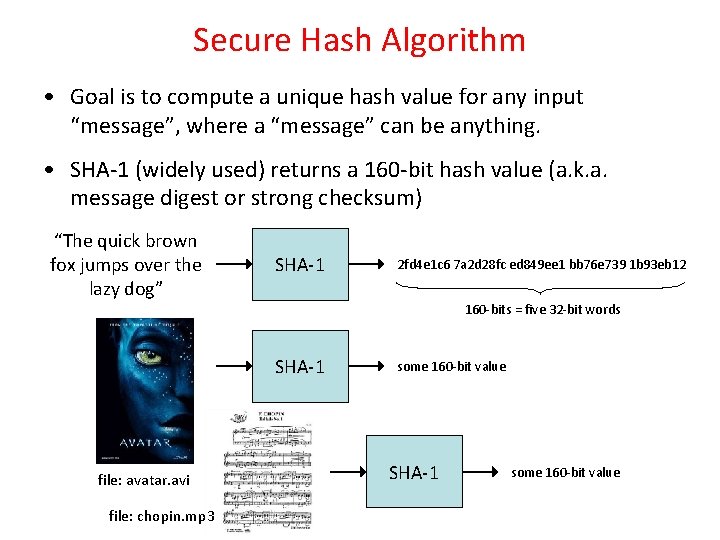
Secure Hash Algorithm • Goal is to compute a unique hash value for any input “message”, where a “message” can be anything. • SHA-1 (widely used) returns a 160 -bit hash value (a. k. a. message digest or strong checksum) “The quick brown fox jumps over the lazy dog” SHA-1 2 fd 4 e 1 c 6 7 a 2 d 28 fc ed 849 ee 1 bb 76 e 739 1 b 93 eb 12 160 -bits = five 32 -bit words SHA-1 file: avatar. avi file: chopin. mp 3 some 160 -bit value SHA-1 some 160 -bit value
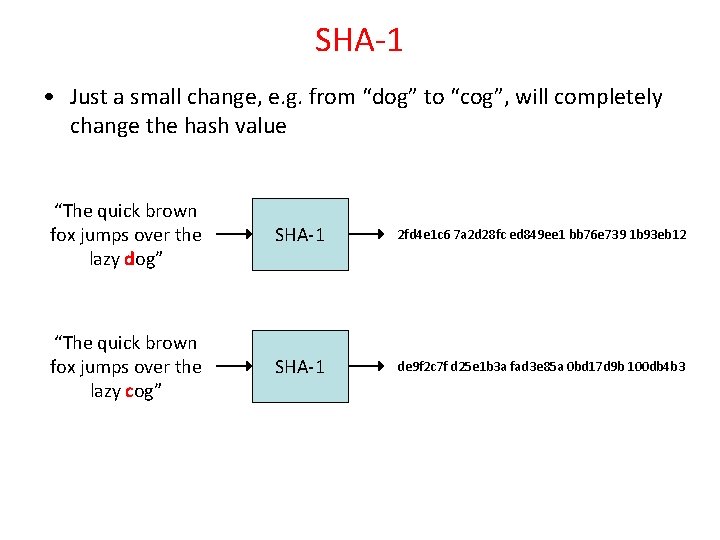
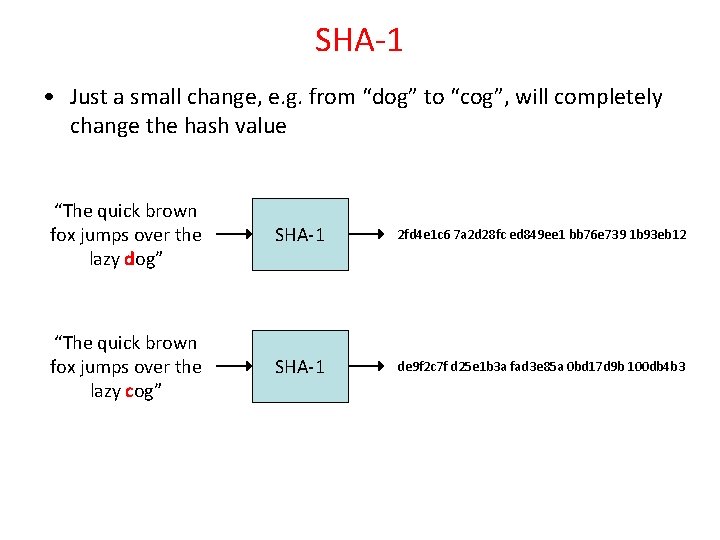
SHA-1 • Just a small change, e. g. from “dog” to “cog”, will completely change the hash value “The quick brown fox jumps over the lazy dog” SHA-1 2 fd 4 e 1 c 6 7 a 2 d 28 fc ed 849 ee 1 bb 76 e 739 1 b 93 eb 12 “The quick brown fox jumps over the lazy cog” SHA-1 de 9 f 2 c 7 f d 25 e 1 b 3 a fad 3 e 85 a 0 bd 17 d 9 b 100 db 4 b 3
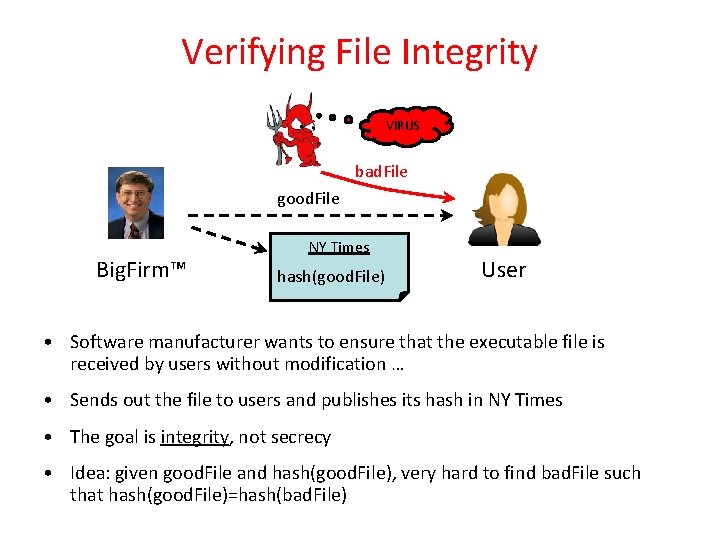
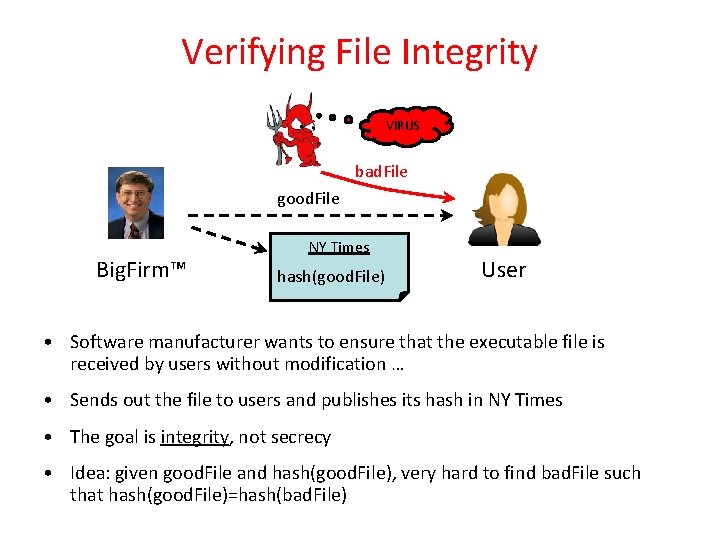
Verifying File Integrity VIRUS bad. File good. File Big. Firm™ NY Times hash(good. File) User • Software manufacturer wants to ensure that the executable file is received by users without modification … • Sends out the file to users and publishes its hash in NY Times • The goal is integrity, not secrecy • Idea: given good. File and hash(good. File), very hard to find bad. File such that hash(good. File)=hash(bad. File)
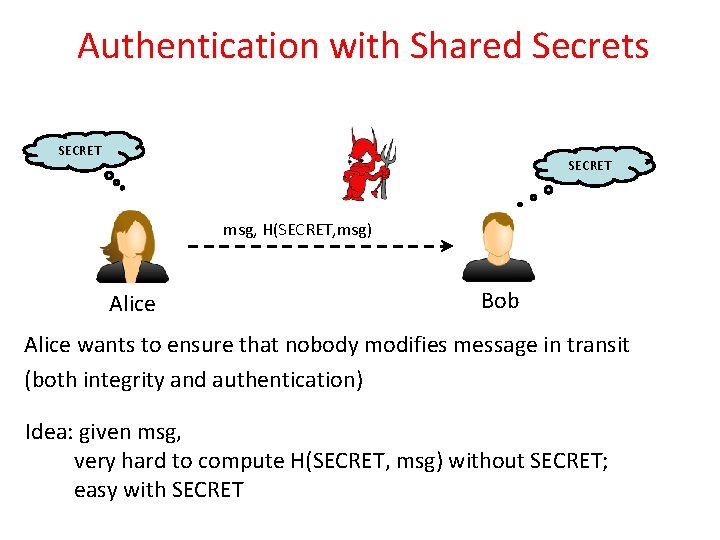
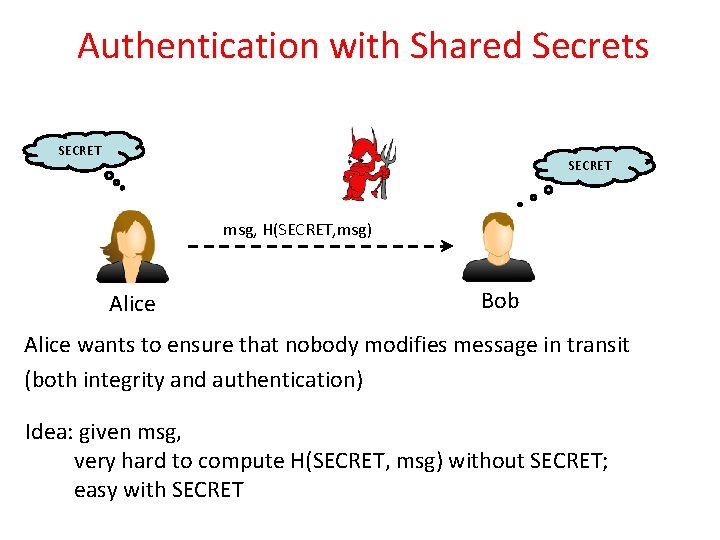
Authentication with Shared Secrets SECRET msg, H(SECRET, msg) Alice Bob Alice wants to ensure that nobody modifies message in transit (both integrity and authentication) Idea: given msg, very hard to compute H(SECRET, msg) without SECRET; easy with SECRET
SHA-1 • Developed by NIST, specified in the Secure Hash Standard (SHS, FIPS Pub 180), 1993 • SHA-1 is specified as the hash algorithm in the Digital Signature Standard (DSS), NIST
General Logic • Input message must be < 264 bits – not really a problem • Message is processed in 512 -bit blocks sequentially • Message digest is 160 bits
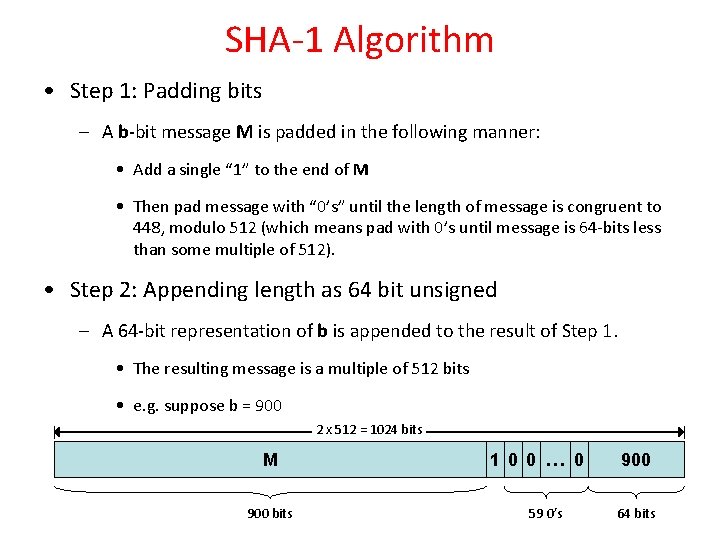
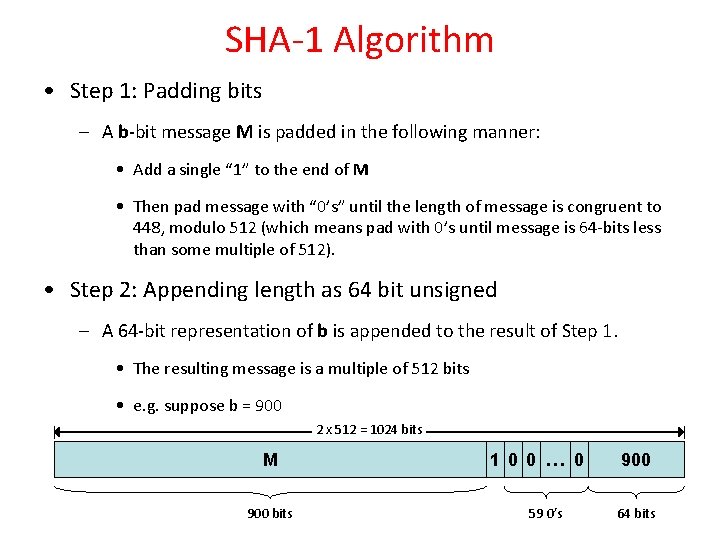
SHA-1 Algorithm • Step 1: Padding bits – A b-bit message M is padded in the following manner: • Add a single “ 1” to the end of M • Then pad message with “ 0’s” until the length of message is congruent to 448, modulo 512 (which means pad with 0’s until message is 64 -bits less than some multiple of 512). • Step 2: Appending length as 64 bit unsigned – A 64 -bit representation of b is appended to the result of Step 1. • The resulting message is a multiple of 512 bits • e. g. suppose b = 900 2 x 512 = 1024 bits M 900 bits 1 0 0 … 0 59 0’s 900 64 bits
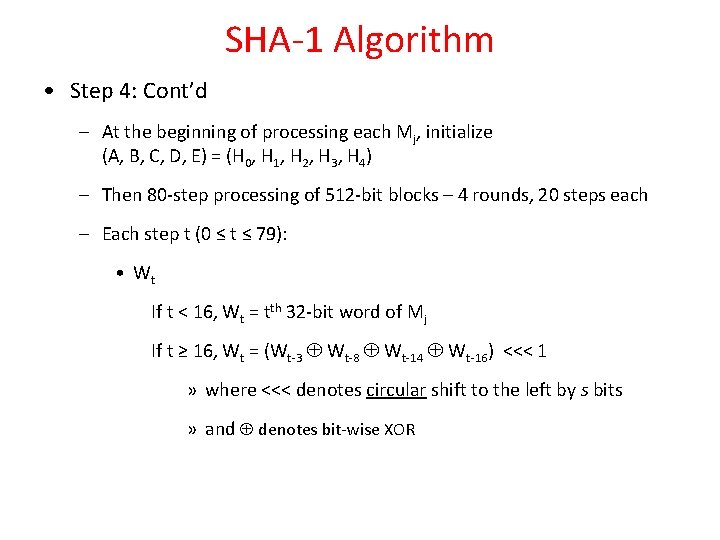
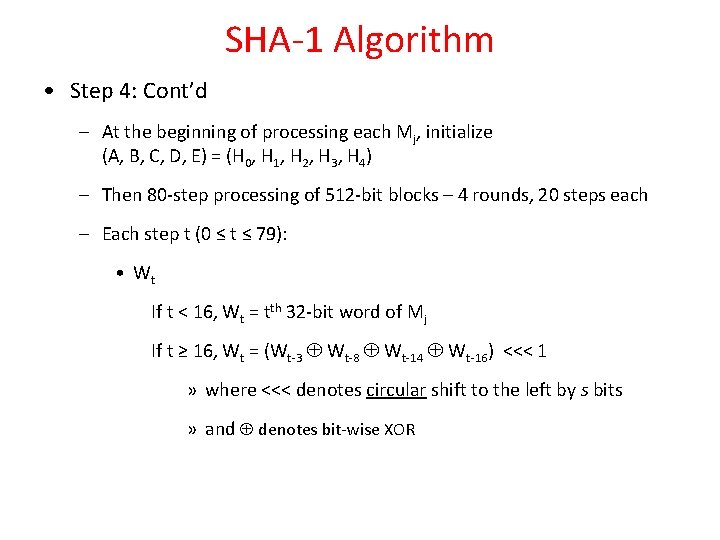
SHA-1 Algorithm • Step 3: Buffer initiation – initialize message digest (MD) to these five 32 -bit words H 0 = 67452301 H 1 = efcdab 89 H 2 = 98 badcfe H 3 = 10325476 H 4 = c 3 d 2 e 1 f 0
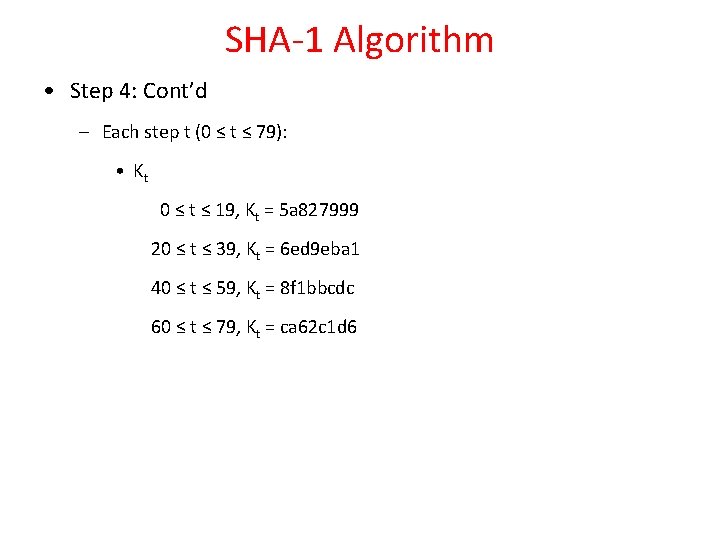
SHA-1 Algorithm • Step 4: Processing of the message (the algorithm) – Divide message M into 512 -bit blocks, M 0, M 1, … Mj, … – Process each Mj sequentially, one after the other – Input: • Wt : a 32 -bit word from the message • Kt : a constant • H 0, H 1, H 2, H 3, H 4 : current MD – Output: • H 0, H 1, H 2, H 3, H 4 : new MD
SHA-1 Algorithm • Step 4: Cont’d – At the beginning of processing each Mj, initialize (A, B, C, D, E) = (H 0, H 1, H 2, H 3, H 4) – Then 80 -step processing of 512 -bit blocks – 4 rounds, 20 steps each – Each step t (0 ≤ t ≤ 79): • Wt If t < 16, Wt = tth 32 -bit word of Mj If t ≥ 16, Wt = (Wt-3 Wt-8 Wt-14 Wt-16) <<< 1 » where <<< denotes circular shift to the left by s bits » and denotes bit-wise XOR
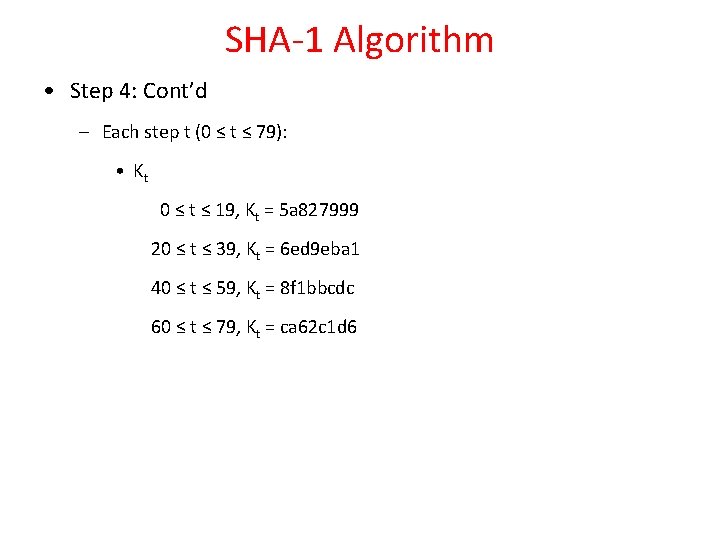
SHA-1 Algorithm • Step 4: Cont’d – Each step t (0 ≤ t ≤ 79): • Kt 0 ≤ t ≤ 19, Kt = 5 a 827999 20 ≤ t ≤ 39, Kt = 6 ed 9 eba 1 40 ≤ t ≤ 59, Kt = 8 f 1 bbcdc 60 ≤ t ≤ 79, Kt = ca 62 c 1 d 6
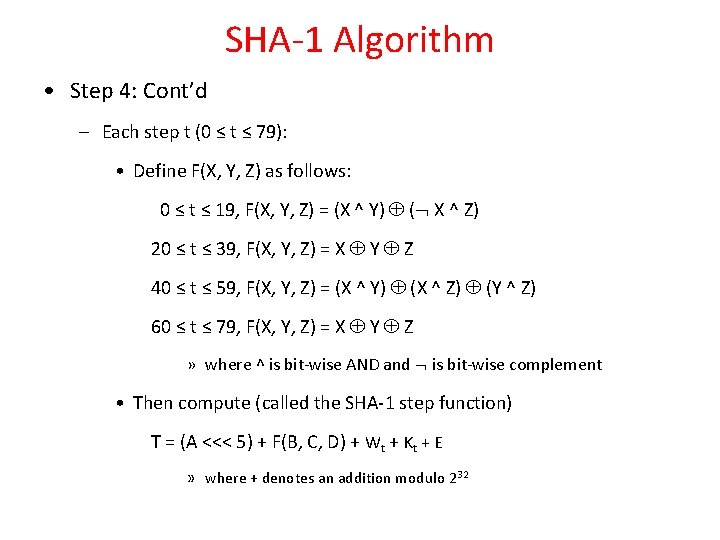
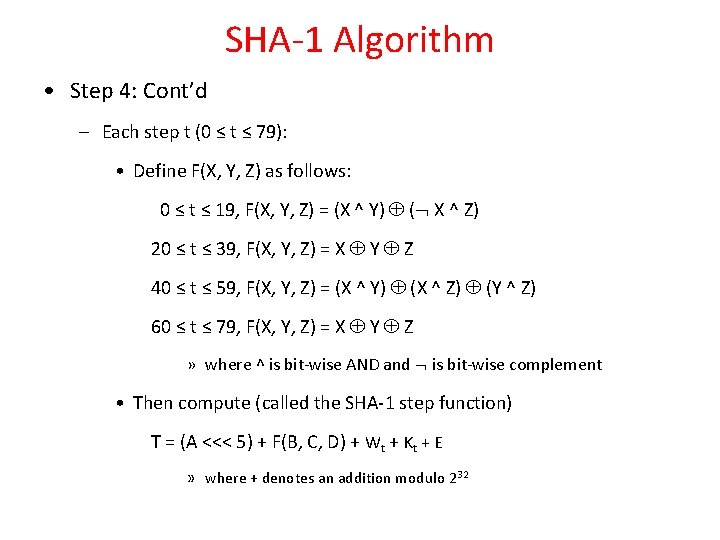
SHA-1 Algorithm • Step 4: Cont’d – Each step t (0 ≤ t ≤ 79): • Define F(X, Y, Z) as follows: 0 ≤ t ≤ 19, F(X, Y, Z) = (X ^ Y) ( X ^ Z) 20 ≤ t ≤ 39, F(X, Y, Z) = X Y Z 40 ≤ t ≤ 59, F(X, Y, Z) = (X ^ Y) (X ^ Z) (Y ^ Z) 60 ≤ t ≤ 79, F(X, Y, Z) = X Y Z » where ^ is bit-wise AND and is bit-wise complement • Then compute (called the SHA-1 step function) T = (A <<< 5) + F(B, C, D) + Wt + Kt + E » where + denotes an addition modulo 232
SHA-1 Algorithm • Step 4: Cont’d – Each step t (0 ≤ t ≤ 79): • The values of (A, B, C, D, E) are updated as follows: (A, B, C, D, E) = (T, A, B <<< 30, C, D)
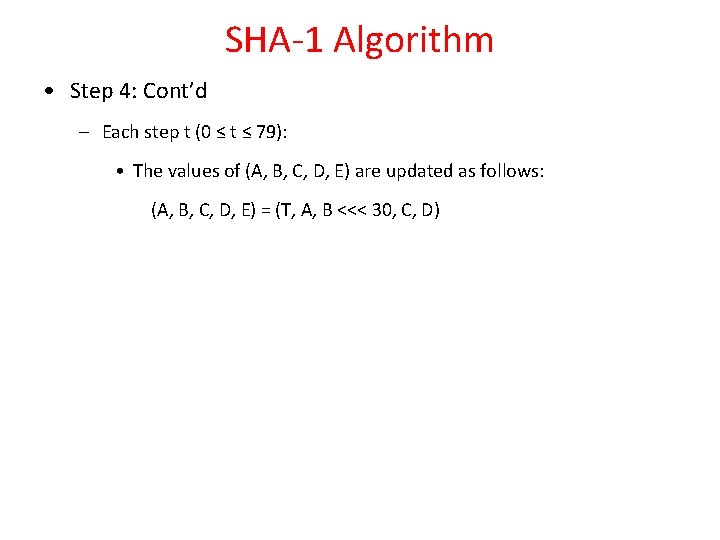
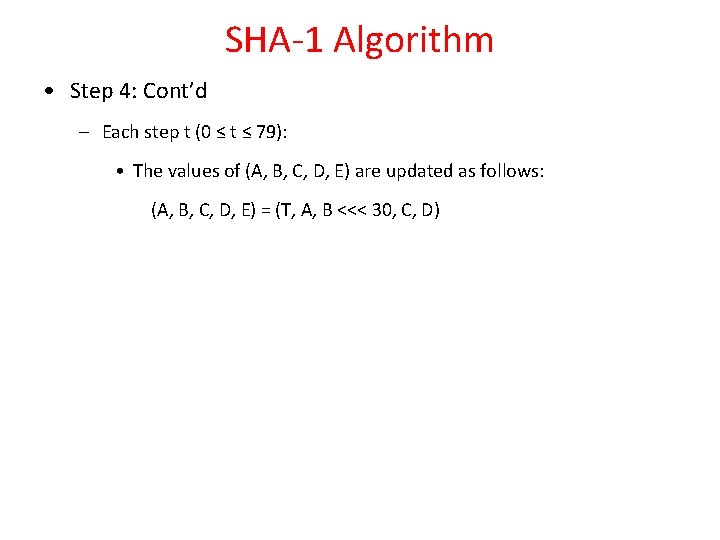
SHA-1 Algorithm • Step 4: Cont’d – Finally, when all 80 steps have been processed, set H 0 = H 0 + A H 1 = H 1 + B H 2 = H 2 + C H 3 = H 3 + D H 4 = H 4 + E
SHA-1 Algorithm • Step 5: Output – When all Mj have been processed, the 160 -bit hash of M is available in H 0, H 1, H 2, H 3, and H 4
![Module Interface Very similar to Project 2 on RLE CoProcessor Done Hash159 0 Module Interface • Very similar to Project 2 on RLE Co-Processor Done Hash[159: 0]](https://slidetodoc.com/presentation_image_h/c719c0210ade0c735b1c2c65ce4379d9/image-17.jpg)
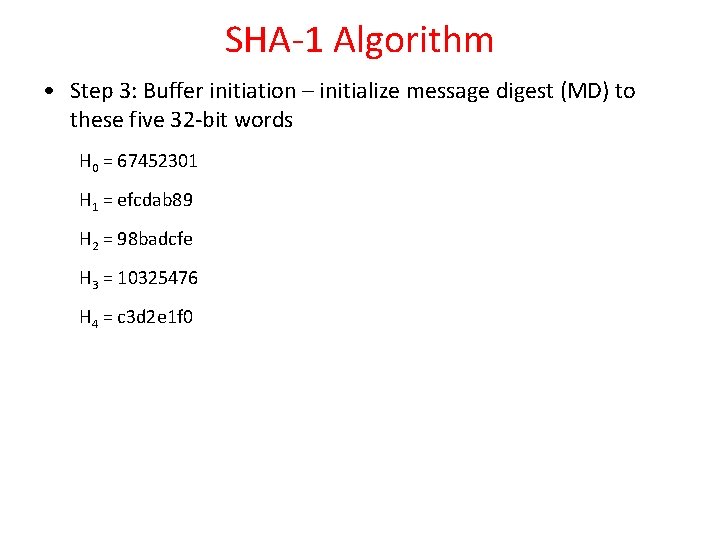
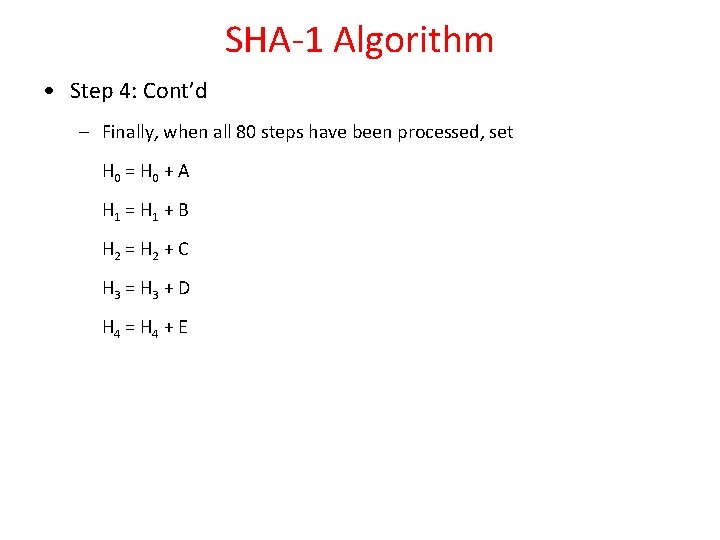
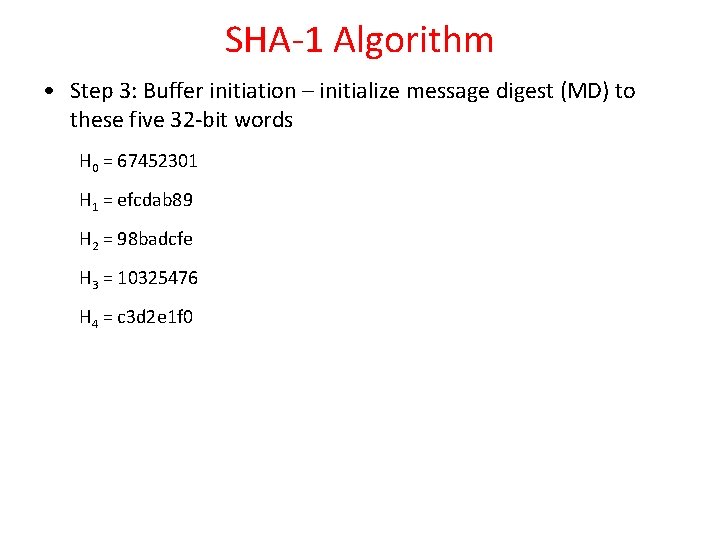
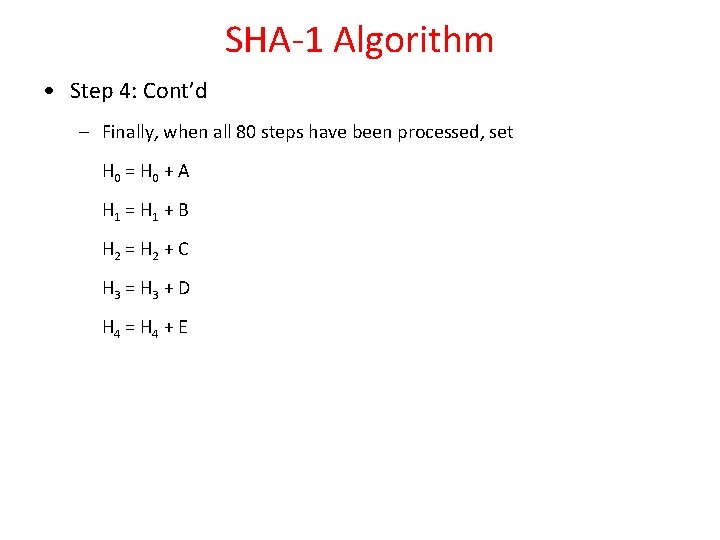
Module Interface • Very similar to Project 2 on RLE Co-Processor Done Hash[159: 0] Start_hash Message_size[31: 0] Message_addr[31: 0] • Notes: Message_size given in number of bytes and no need to use Port_A_data_in[31: 0] as memory used for read only Port_A_addr[15: 0] DPSRAM (stores message) Port_A_we Port_A_data_in[31: 0] Port_A_data_out[31: 0] DPSRAM interface Port_A_clk Clk SHA-1 Processor nreset
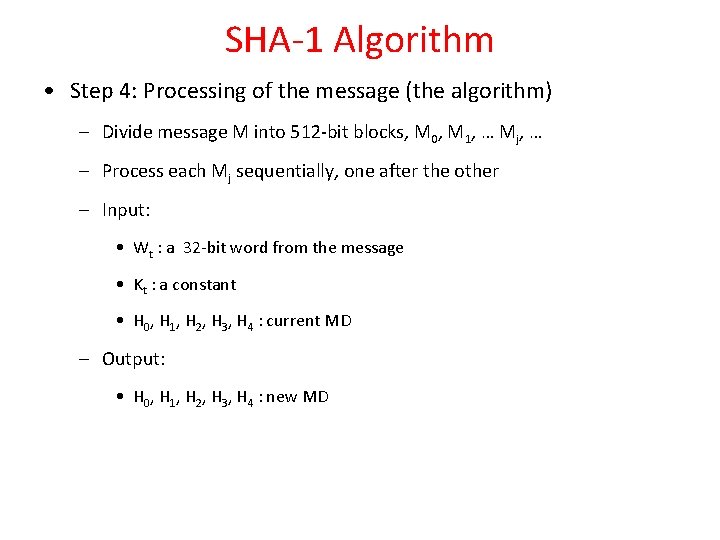
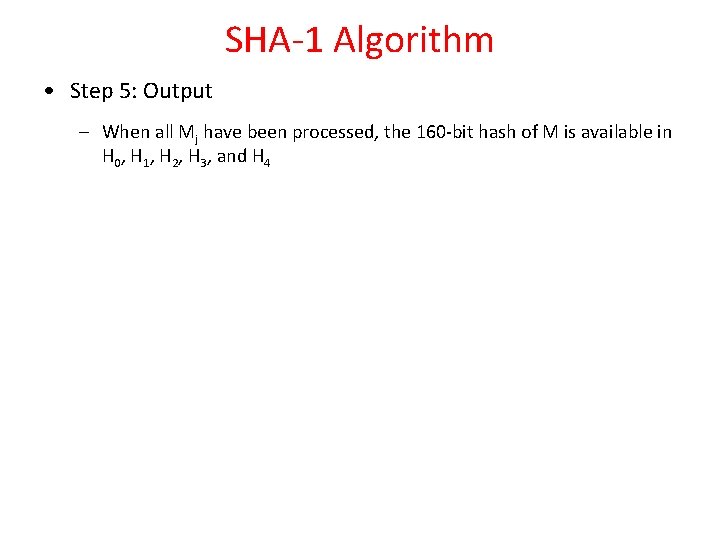
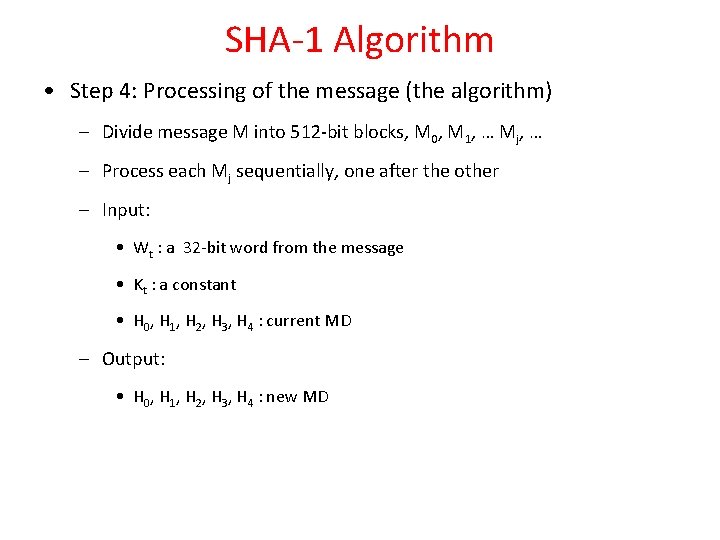
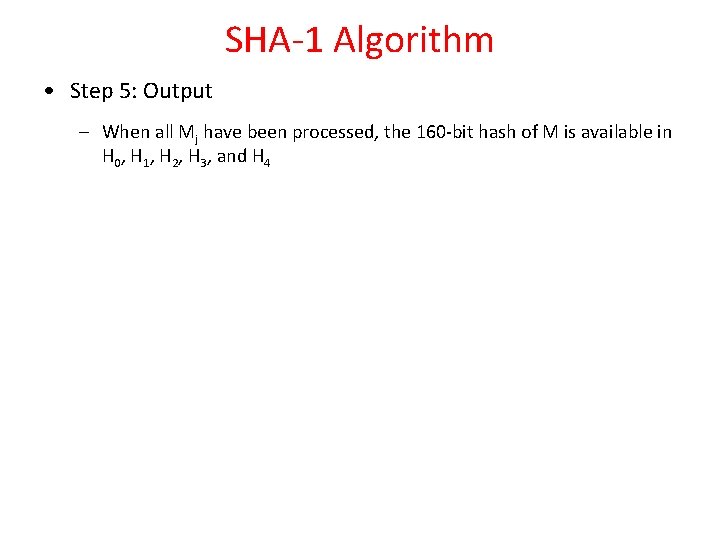
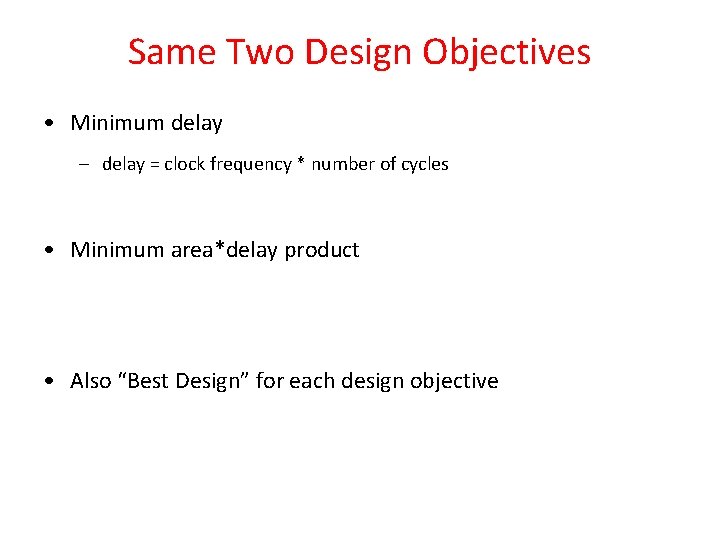
Big-Endian vs. Little-Endian • The memory representation (as with the RLE project) uses a little-endian representation whereas the SHA 1 algorithm uses a big-endian representation. • For message “The boat”, little-endian would be: M[0] = “ eh. T”; M[1] = “taob”; big-endian would be: W[0] = “The “; W[1] = “boat”;
![BigEndian vs LittleEndian Use this function 31 0 change Endian transform to bigendian Big-Endian vs. Little-Endian • Use this function [31: 0] change. Endian; //transform to big-endian](https://slidetodoc.com/presentation_image_h/c719c0210ade0c735b1c2c65ce4379d9/image-19.jpg)
Big-Endian vs. Little-Endian • Use this function [31: 0] change. Endian; //transform to big-endian input [31: 0] value; change. Endian = {value[7: 0], value[15: 8], value[23: 16], value[31: 24]}; endfunction • Then in your Verilog code, you can do something like this: w[i] <= change. Endian(port_A_data_out);
Same Two Design Objectives • Minimum delay – delay = clock frequency * number of cycles • Minimum area*delay product • Also “Best Design” for each design objective
Disable the use of Block Memories • Altera Quartus will automatically replace some registers with block memories, which are not counted in the total number of registers. If you look at the Analysis & Synthesis Summary, you will see a Total block memory bits entry. If it is non-zero, it means block memories were allocated. • To provide a common basis for comparison, you should disable the use of block memories. This can be done as follows: – In the analysis and synthesis settings, there is an option for auto shift register replacement. – Turning that off will disable the use of block memories. • If Total block memory bits is non-zero, then you have to add the number of memory bits to your area. – i. e. area = #ALUT + #registers + #block memory bits
More Information • Here is the official IETF specification. – http: //www. ietf. org/rfc 3174. txt • Here is the Wikipedia page. – http: //en. wikipedia. org/wiki/SHA-1