CS 526 Advanced Internet And Web Systems Semester
CS 526 – Advanced Internet And Web Systems Semester Project Public Key Infrastructure (PKI) By Samatha Sudarshanam
Introduction • PKI’s? • Functionality of a Public Key Infrastructure – Creation of the key–pair and the certificate request – Signing of the certificate request by the Certification Authority – Certification Authority chains – Typical uses of public key cryptography
PKIX • Important concepts with regard to the PKIX standards – Certificate–using Systems and PKIs – Certificate–using Systems and PMIs
PKIX (cntd …) • • PKIX standardization areas. Public–key infrastructure functionality Public–Key Infrastructure (PKI) Privilege Management Infrastructure (PMI)
PKIX standardization areas • PKIX standardization areas – Profiles of X. 509 v 3 Public Key Certificates and X. 509 v 2 Certificate Revocation Lists (CRLs). – Management protocols – Operational protocols. – Certificate policies and Certificate Practice Statements. – Time–stamping and data–certification/validation services
Public–key infrastructure functionality • • • Registration Initialisation Certification Key–pair recovery Key generation Key update Key expiry Key compromise Cross certification Revocation Certificate and Revocation Notice Distribution and Publication
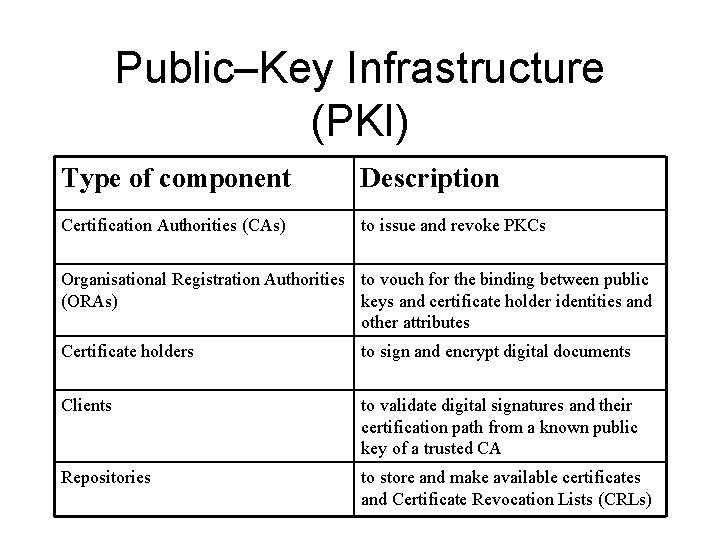
Public–Key Infrastructure (PKI) Type of component Description Certification Authorities (CAs) to issue and revoke PKCs Organisational Registration Authorities to vouch for the binding between public (ORAs) keys and certificate holder identities and other attributes Certificate holders to sign and encrypt digital documents Clients to validate digital signatures and their certification path from a known public key of a trusted CA Repositories to store and make available certificates and Certificate Revocation Lists (CRLs)
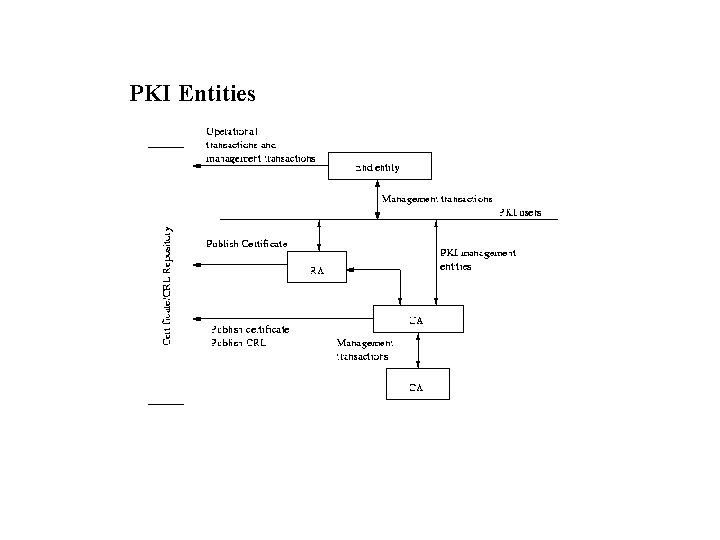
PKI Entities
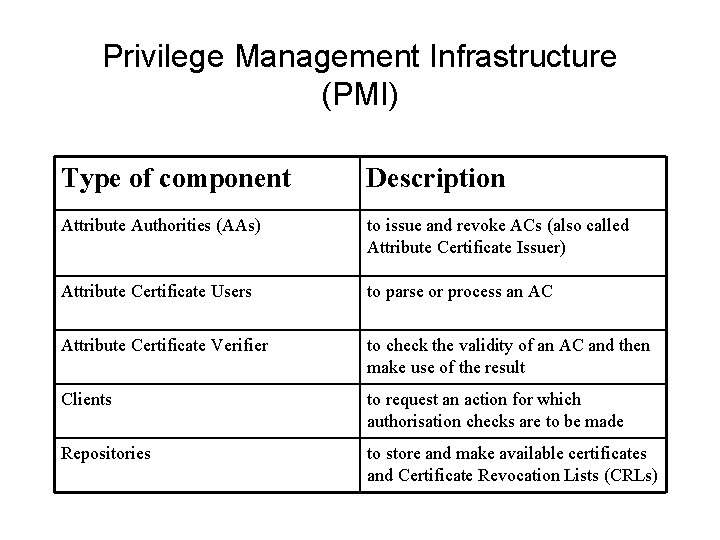
Privilege Management Infrastructure (PMI) Type of component Description Attribute Authorities (AAs) to issue and revoke ACs (also called Attribute Certificate Issuer) Attribute Certificate Users to parse or process an AC Attribute Certificate Verifier to check the validity of an AC and then make use of the result Clients to request an action for which authorisation checks are to be made Repositories to store and make available certificates and Certificate Revocation Lists (CRLs)
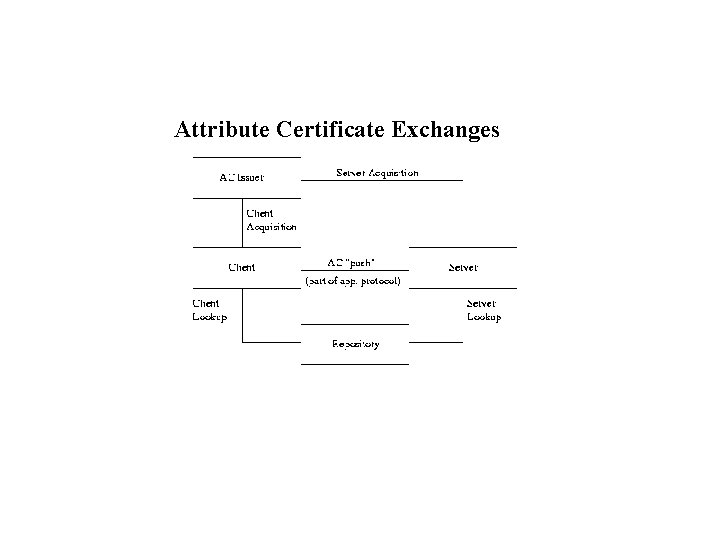
Attribute Certificate Exchanges
Conclusion • This document describes Public Key Infrastructures, the PKIX standards, practical PKI functionality. Its aim is foster the creation of viable open– source PKI implementations.
- Slides: 11