Chapter 10 FileSystem Objectives n To discuss filesystem
Chapter 10: File-System Objectives n To discuss file-system design tradeoffs, including access methods, file sharing, file locking, and directory structures n To explore file-system protection n Skip 10. 2, 10. 4, 10. 5 Operating System Principles 10. 1 Silberschatz, Galvin and Gagne © 2005
10. 1 File Concept n The operating system abstracts from the physical properties of its storage to define a logical storage unit, the file. n Files are mapped by the OS onto physical, usually nonvolatile, devices. n The OS normally maintains two-level open-file tables, per-process and system-wide Operating System Principles 10. 2 Silberschatz, Galvin and Gagne © 2005
Open and Close Files n Several pieces of data are needed to manage open files: l File pointer: pointer to last read/write location, per process that has the file open l File-open count: counter of number of times a file is open – to allow removal of data from open-file table when last processes closes it l Disk location of the file: cache of data access information l Access rights: per-process access mode information Operating System Principles 10. 3 Silberschatz, Galvin and Gagne © 2005
Internal File Structure n All disks is performed in units of one block (physical record) n Logical records may vary in length n Packing a number of logical records into physical blocks is the common solution l Example: UNIX defines all files to be streams of bytes. Its logical record size is 1 byte. n Packing can be done either by user’s application or by the operating system l Internal fragmentation problem Operating System Principles 10. 4 Silberschatz, Galvin and Gagne © 2005
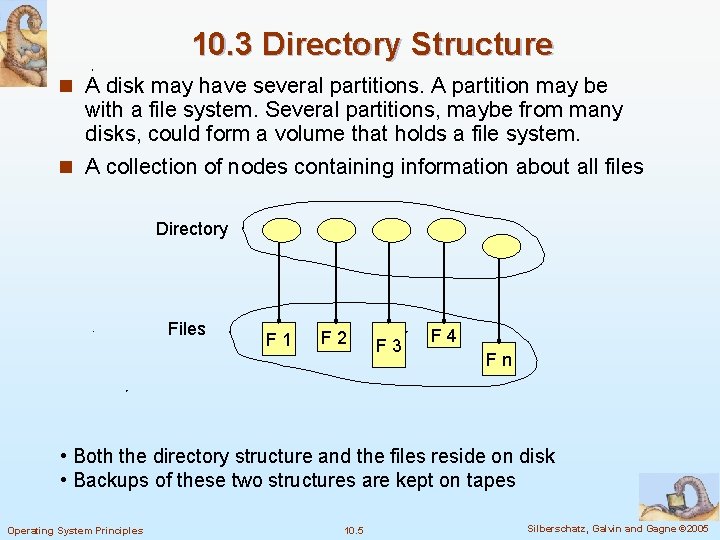
10. 3 Directory Structure n A disk may have several partitions. A partition may be with a file system. Several partitions, maybe from many disks, could form a volume that holds a file system. n A collection of nodes containing information about all files Directory Files F 1 F 2 F 3 F 4 Fn • Both the directory structure and the files reside on disk • Backups of these two structures are kept on tapes Operating System Principles 10. 5 Silberschatz, Galvin and Gagne © 2005
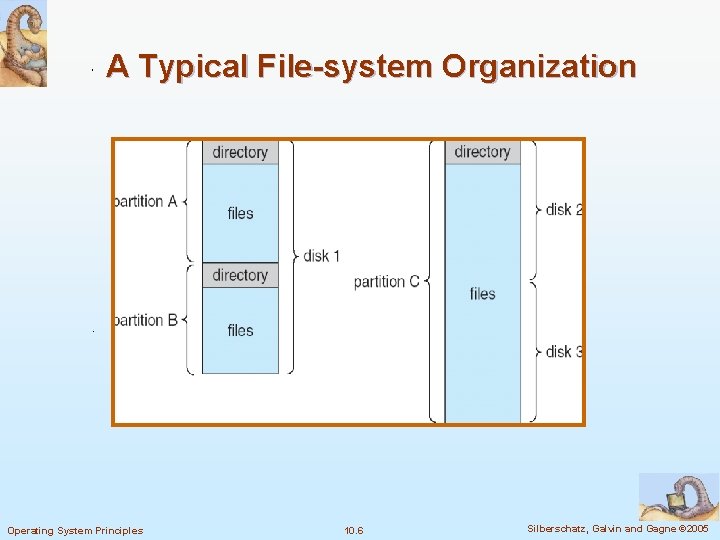
A Typical File-system Organization Operating System Principles 10. 6 Silberschatz, Galvin and Gagne © 2005
Operations Performed on Directory n Search for a file n Create a file n Delete a file n List a directory n Rename a file n Traverse the file system l for backup (to tape) Operating System Principles 10. 7 Silberschatz, Galvin and Gagne © 2005
Organize the Directory (Logically) to Obtain: n Efficiency – locating a file quickly n Naming – convenient to users l Two users can have same name for different files l The same file can have several different names n Grouping – logical grouping of files by properties l e. g. , all Java programs, all games, … Operating System Principles 10. 8 Silberschatz, Galvin and Gagne © 2005
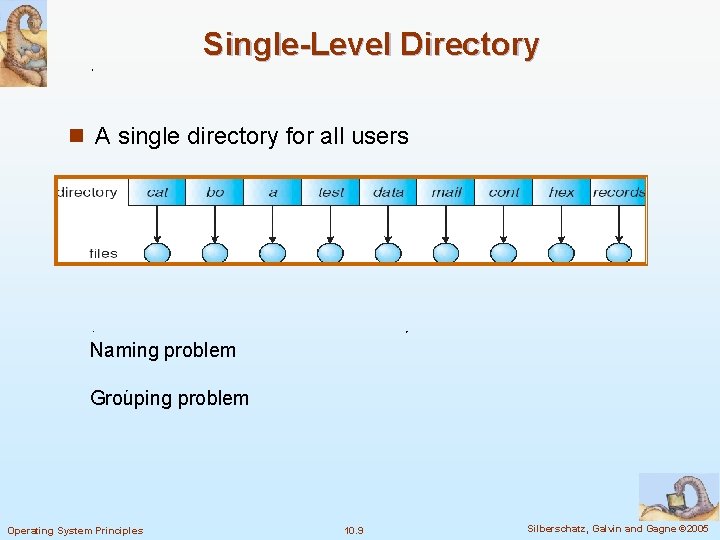
Single-Level Directory n A single directory for all users Naming problem Grouping problem Operating System Principles 10. 9 Silberschatz, Galvin and Gagne © 2005
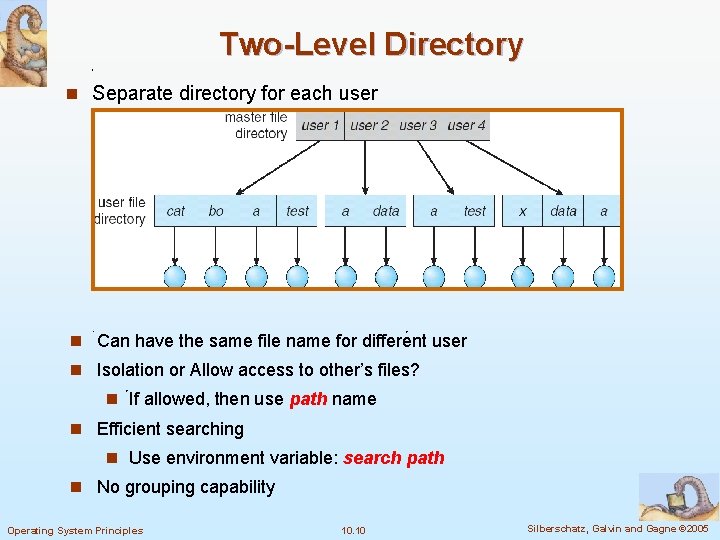
Two-Level Directory n Separate directory for each user n Can have the same file name for different user n Isolation or Allow access to other’s files? n If allowed, then use path name n Efficient searching n Use environment variable: search path n No grouping capability Operating System Principles 10. 10 Silberschatz, Galvin and Gagne © 2005
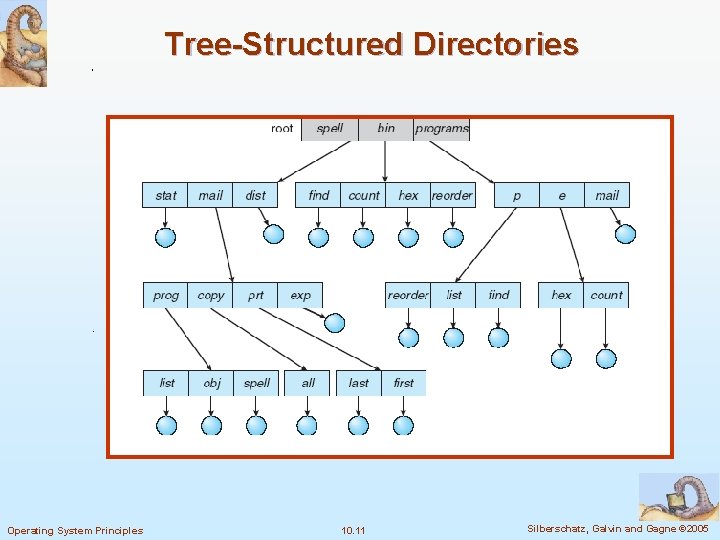
Tree-Structured Directories Operating System Principles 10. 11 Silberschatz, Galvin and Gagne © 2005
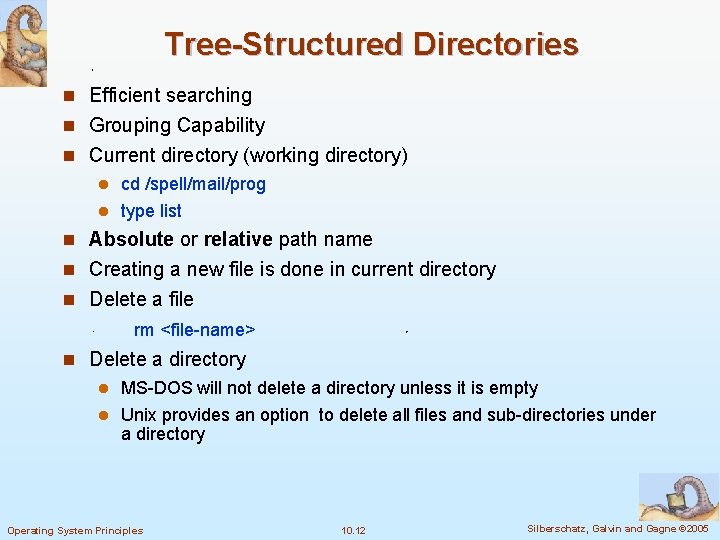
Tree-Structured Directories n Efficient searching n Grouping Capability n Current directory (working directory) l cd /spell/mail/prog l type list n Absolute or relative path name n Creating a new file is done in current directory n Delete a file rm <file-name> n Delete a directory l MS-DOS will not delete a directory unless it is empty l Unix provides an option to delete all files and sub-directories under a directory Operating System Principles 10. 12 Silberschatz, Galvin and Gagne © 2005
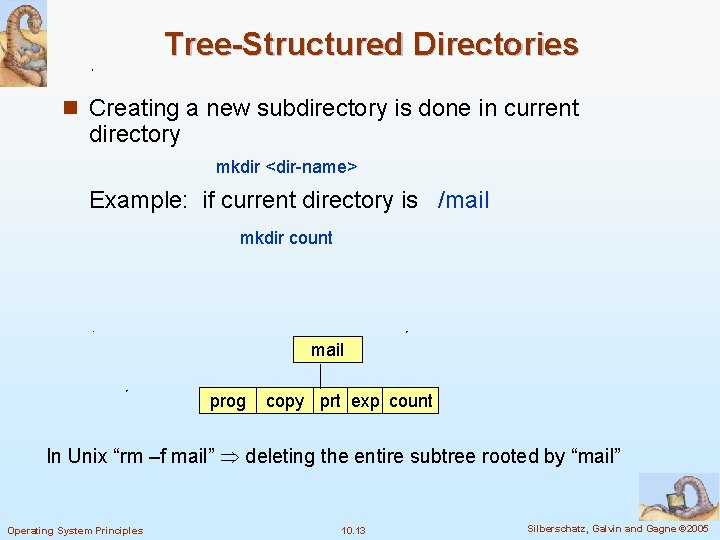
Tree-Structured Directories n Creating a new subdirectory is done in current directory mkdir <dir-name> Example: if current directory is /mail mkdir count mail prog copy prt exp count In Unix “rm –f mail” deleting the entire subtree rooted by “mail” Operating System Principles 10. 13 Silberschatz, Galvin and Gagne © 2005
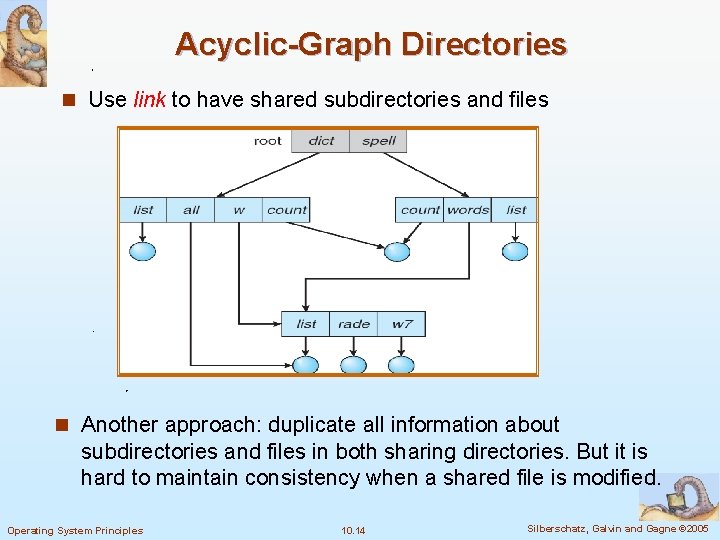
Acyclic-Graph Directories n Use link to have shared subdirectories and files n Another approach: duplicate all information about subdirectories and files in both sharing directories. But it is hard to maintain consistency when a shared file is modified. Operating System Principles 10. 14 Silberschatz, Galvin and Gagne © 2005
Acyclic-Graph Directories n New directory entry type l Link – another name (pointer) to an existing file l Resolve the link – follow pointer to locate the file n Two different names (aliasing) l A file could have multiple absolute path names. l Traverse problem. n If dict deletes all dangling pointer. Solutions: l Just wait for users to find out. It is used with symbolic links: l Preserve the file until all references to it are deleted. Unix uses this approach for hard links by keeping a reference count in the file information block. n Acyclic-graph could be maintained by prohibiting multiple references to directories SKIP: 10. 3. 7 Operating System Principles 10. 15 Silberschatz, Galvin and Gagne © 2005
10. 6 Protection n Reliability is to keep the computer system from physical damage. (Chapter 12) n Protection is to keep it from improper access. n File owner/creator should be able to control: l what can be done l by whom n Basic types of controlled access l Read l Write l Execute l Append l Delete l List Operating System Principles Other high-level functions, like copying and editing files may be implemented by making lower-level system calls 10. 16 Silberschatz, Galvin and Gagne © 2005
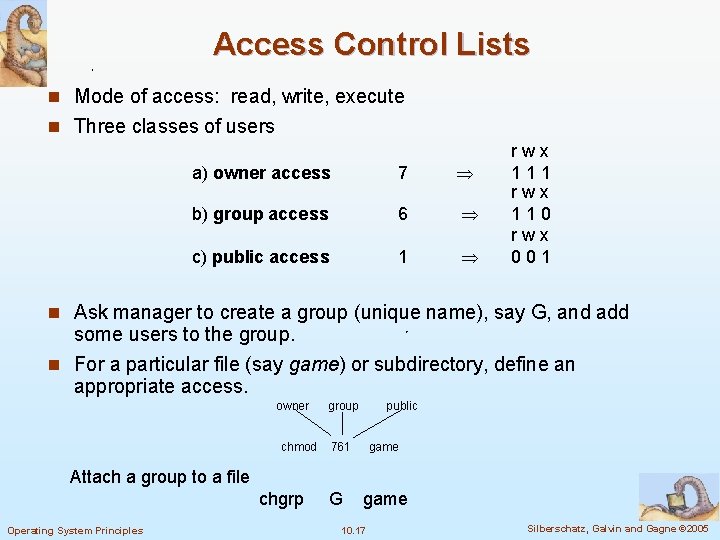
Access Control Lists n Mode of access: read, write, execute n Three classes of users a) owner access 7 b) group access 6 c) public access 1 rwx 110 rwx 001 n Ask manager to create a group (unique name), say G, and add some users to the group. n For a particular file (say game) or subdirectory, define an appropriate access. owner chmod group public 761 game Attach a group to a file chgrp Operating System Principles G game 10. 17 Silberschatz, Galvin and Gagne © 2005
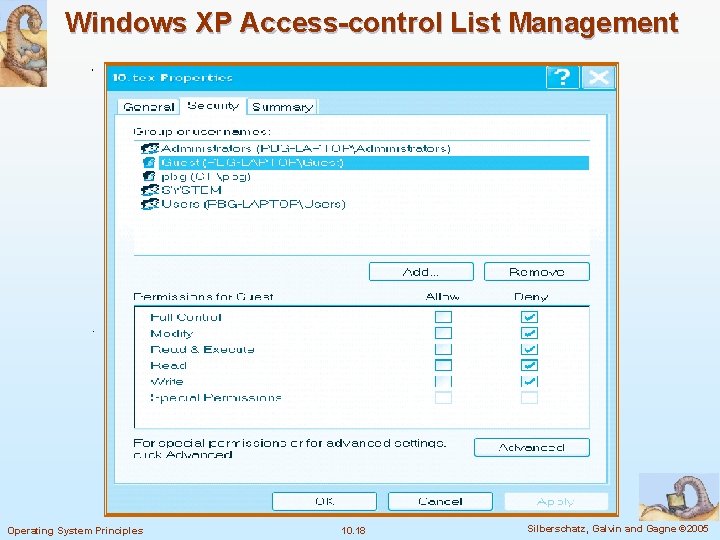
Windows XP Access-control List Management Operating System Principles 10. 18 Silberschatz, Galvin and Gagne © 2005
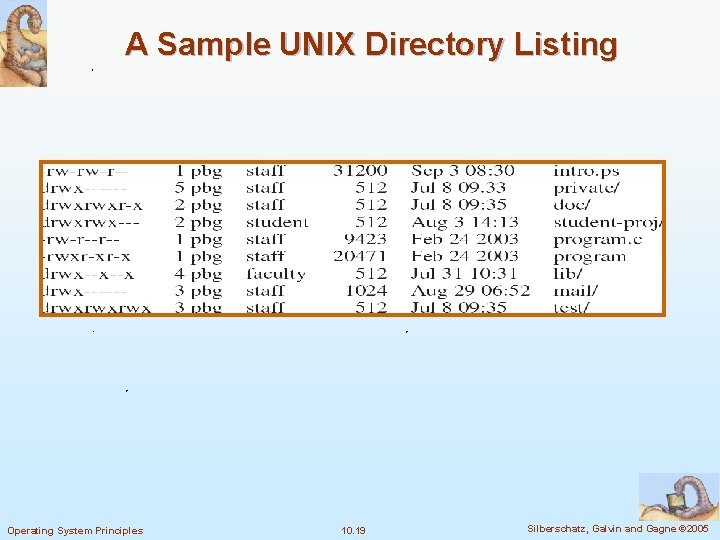
A Sample UNIX Directory Listing Operating System Principles 10. 19 Silberschatz, Galvin and Gagne © 2005
Other Protection Approaches n Associate a password with each file l Disadvantages 4 The number of passwords that a user needs to remember 4 If only one password is used for all the files, then protection is on an all-or-none basis – Some system allow the user to associate a password with a directory n Adding protection mechanisms to single-user OS is difficult n Directory protection Control the creation and deletion of files in a directory l Control whether a user could check the existence of a file in a directory. (Listing the contents of a directory) l Operating System Principles 10. 20 Silberschatz, Galvin and Gagne © 2005
- Slides: 20