Central Management of 300 Firewalls and AccessLists Fabian

Central Management of 300 Firewalls and Access-Lists Fabian Mauchle fabian. mauchle@switch. ch TNC 2012 Reykjavík, 21 -May-2012
Outline WHY • Router Access Lists versus Stateful Firewalls • The Judgment of Solomon HOW • Basic Concept • Pitfalls of Local Firewalls • Building Blocks • Experiences © 2012 SWITCH 2
Access Lists vs. Stateful Firewalls How to protect SWITCH’s IT infrastructure from attacks from the Internet? • Are static IP access lists in the routers good enough? • Are stateful firewalls needed? © 2012 SWITCH 3

Access Lists • Up till recently SWITCH only used static router ACL – stateless – outgoing connections generally open – incoming. TCP connection forbidden, except what is explicitly needed – incoming UDP connections: a few well-known ports open where required – incoming UDP packets protocol ports ≥ 1024 allowed, • Features – simple, but limited in its capabilities – excellent performance and stability, – IPv 6 support © 2012 SWITCH 4
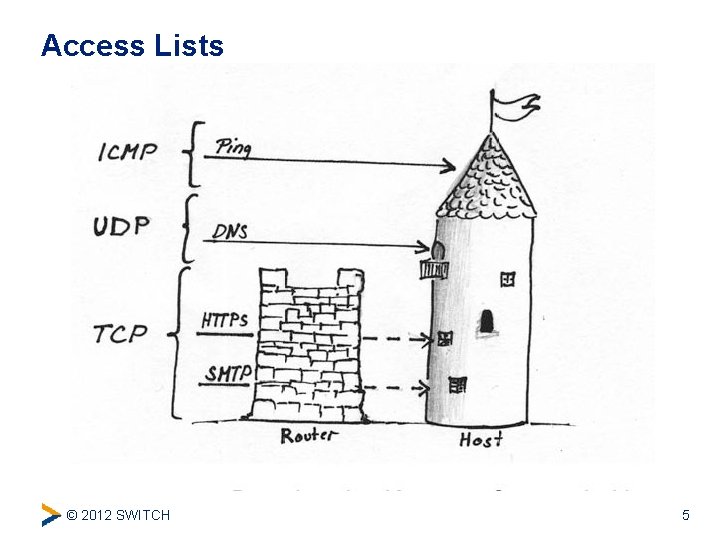
Access Lists © 2012 SWITCH 5
Firewalls can do better • Stateful firewalls dynamically open and close ports based on the state of each TCP connection or UDP conversation – not all UPD high port need to be permanently open • Features – better (stateful) handling of UDP traffic – better control in case of fragmented packets – sophisticated logging – deep packet inspection • But also: – potential bottleneck – single point of failure – … and redundancy is hard to configure and maintain © 2012 SWITCH 6
Network <-> Security ; -) • Network people and PERT staff hate firewalls: – can introduce hard to diagnose problems IP multicast, IP fragments, path MTU discovery q still buggy IPv 6 support q – difficult to deploy in a redundant configuration – performance issues • Security people love them: – state-of-the-art protection – central point to monitor and log traffic – ability to filter on payload – independence (separation of power) © 2012 SWITCH 7
Judgement of Solomon protection of the office: – wide range of equipment – every employee can have root access on his computer – guidelines for the employees (patched, disk encryption) protection of the servers: – well managed (patched, software only installed when needed) – only few people have root access – goal: maximum availability and performance © 2012 SWITCH 8
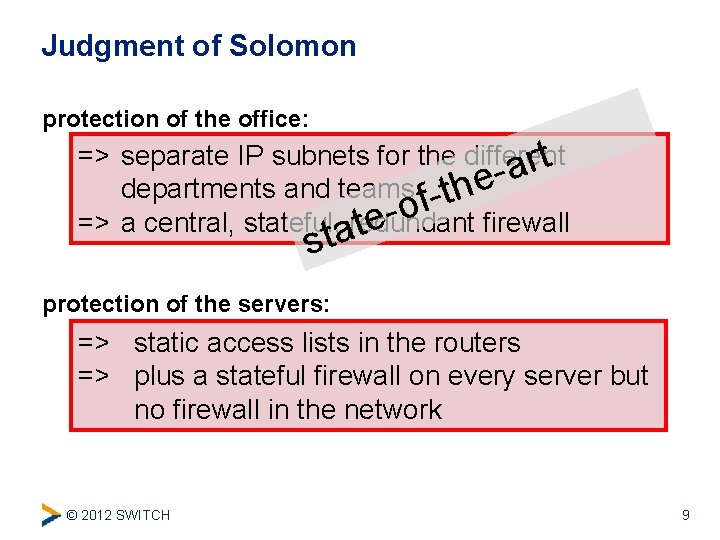
Judgment of Solomon protection of the office: => separate IP subnets for the different t r a departments and teams -thef o => a central, stateful, aredundant firewall te st protection of the servers: => static access lists in the routers => plus a stateful firewall on every server but no firewall in the network © 2012 SWITCH 9
Outline WHY • Router Access Lists versus Statefule Firewalls • The Judgment of Solomon HOW • Basic Concept • Pitfalls of Local Firewalls • Building Blocks • Experiences © 2012 SWITCH 10
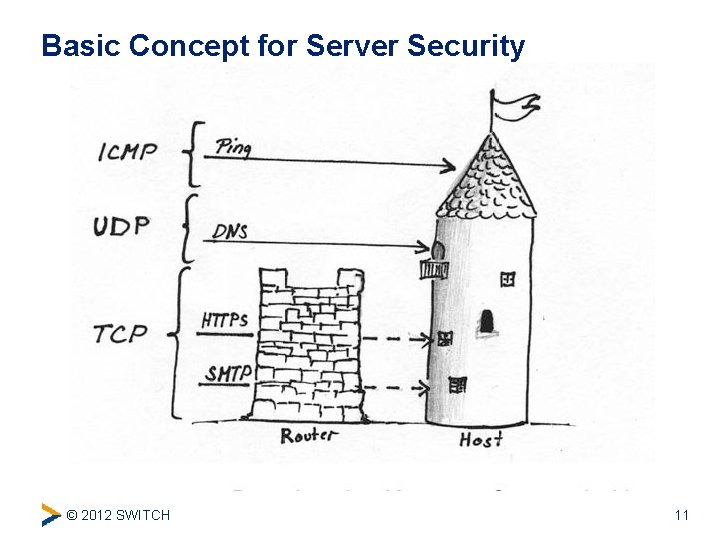
Basic Concept for Server Security © 2012 SWITCH 11
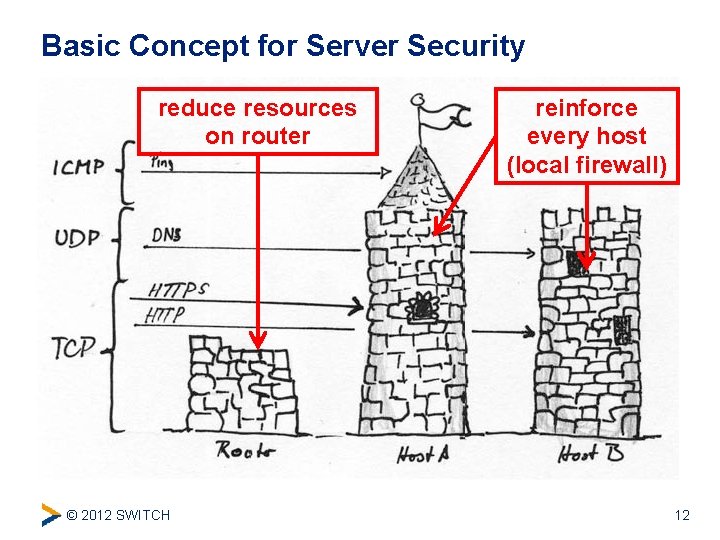
Basic Concept for Server Security reduce resources on router © 2012 SWITCH reinforce every host (local firewall) 12
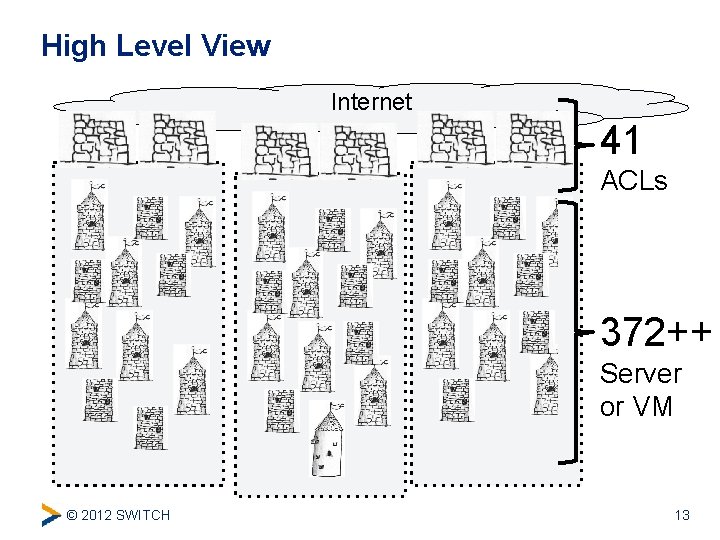
High Level View Internet 41 ACLs 372++ Server or VM © 2012 SWITCH 13
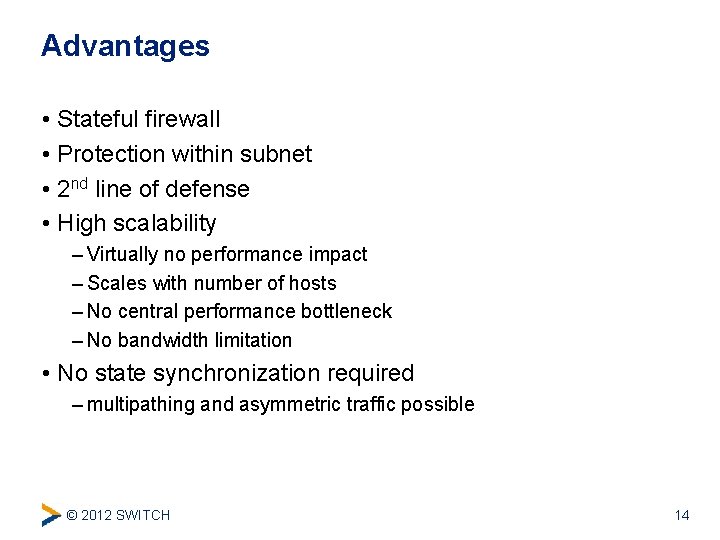
Advantages • Stateful firewall • Protection within subnet • 2 nd line of defense • High scalability – Virtually no performance impact – Scales with number of hosts – No central performance bottleneck – No bandwidth limitation • No state synchronization required – multipathing and asymmetric traffic possible © 2012 SWITCH 14
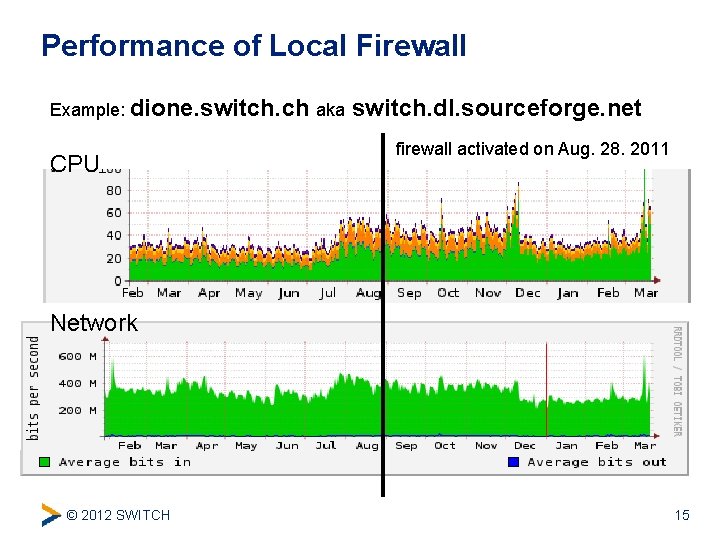
Performance of Local Firewall Example: dione. switch. ch aka CPU switch. dl. sourceforge. net firewall activated on Aug. 28. 2011 Network © 2012 SWITCH 15
Pitfalls of a Local Firewall • Requires rules on router and local firewall • Local connections (localhost) • Connections between hosts (on the same subnet) – Seldom used connections • Heterogeneous environments (different firewall impl. ) © 2012 SWITCH 16
Cavari • How to manage 300+ firewalls? • Web interfaced • Full IPv 6 capable • Use existing information (DNS, Server Management) • Request based policy management • Simple rollback • Platform support for – Cisco IOS ACL – Linux iptables – Solaris ipfilter © 2012 SWITCH 17
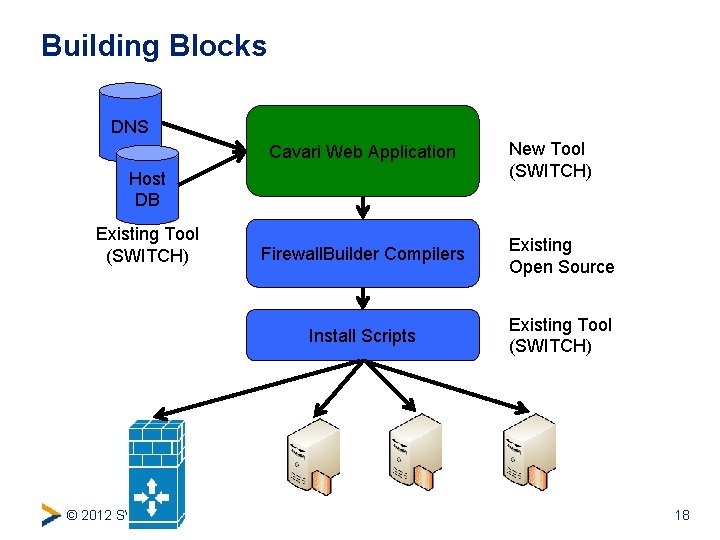
Building Blocks DNS Cavari Web Application Host DB Existing Tool (SWITCH) © 2012 SWITCH New Tool (SWITCH) Firewall. Builder Compilers Existing Open Source Install Scripts Existing Tool (SWITCH) 18
Mechanics • Define allowed connections – source, destination, service (protocol, port) • Use network topology to determine firewall rules • Optimize rules on each firewall – remove duplicate entries and redundant more specifics © 2012 SWITCH 19
Experiences • Stable operation since end of 2011 • Good user acceptance – Let users (admins) view actual rules! • Update IP addresses from DNS is very useful • Migration takes time – Start with logging to find unknown communication • Central logging facility is crucial • Hosts without firewall – Extended set of rule on the router (as before) © 2012 SWITCH 20
Future Work • Add Support for Mac OSX • maybe Windows … • Audit procedure © 2012 SWITCH 21

Questions © 2012 SWITCH 22
- Slides: 22