Firewalls K Salah 1 Firewalls l Idea separate
- Slides: 29
Firewalls K. Salah 1
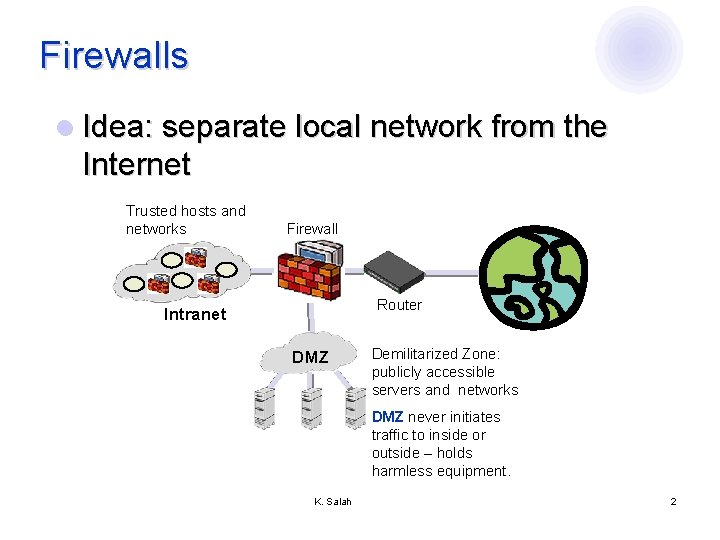
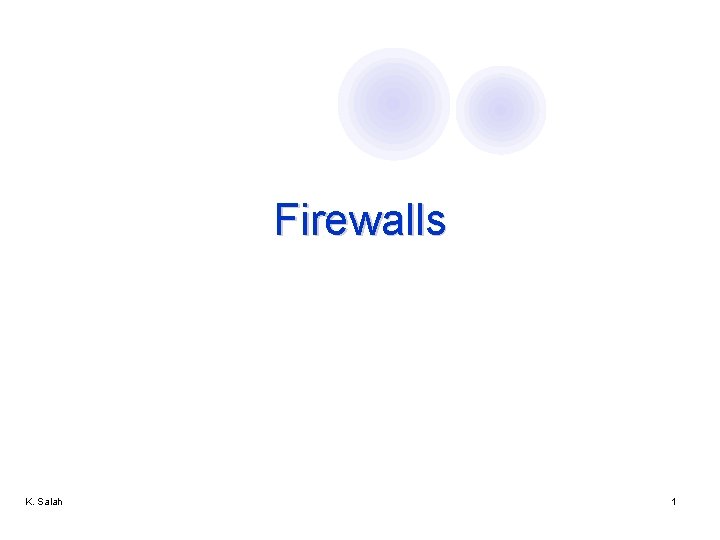
Firewalls l Idea: separate local network from the Internet Trusted hosts and networks Firewall Router Intranet DMZ Demilitarized Zone: publicly accessible servers and networks DMZ never initiates traffic to inside or outside – holds harmless equipment. K. Salah 2
Castle and Moat Analogy l More like the moat around a castle than a firewall ¡ ¡ Restricts access from the outside Restricts outbound connections, too (!!) l Important: filter out undesirable activity from internal hosts! K. Salah 3
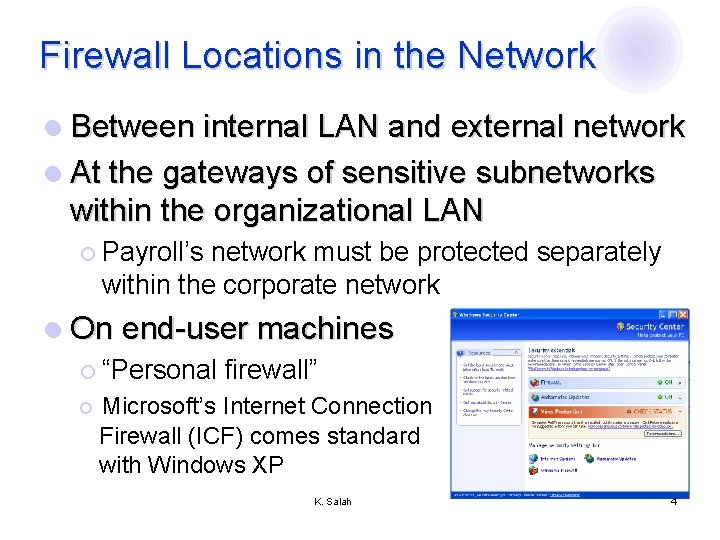
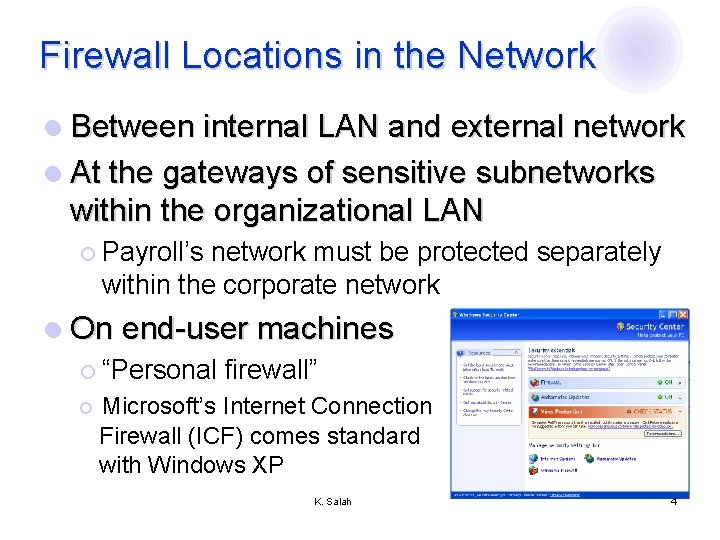
Firewall Locations in the Network l Between internal LAN and external network l At the gateways of sensitive subnetworks within the organizational LAN ¡ Payroll’s network must be protected separately within the corporate network l On end-user machines ¡ “Personal firewall” ¡ Microsoft’s Internet Connection Firewall (ICF) comes standard with Windows XP K. Salah 4
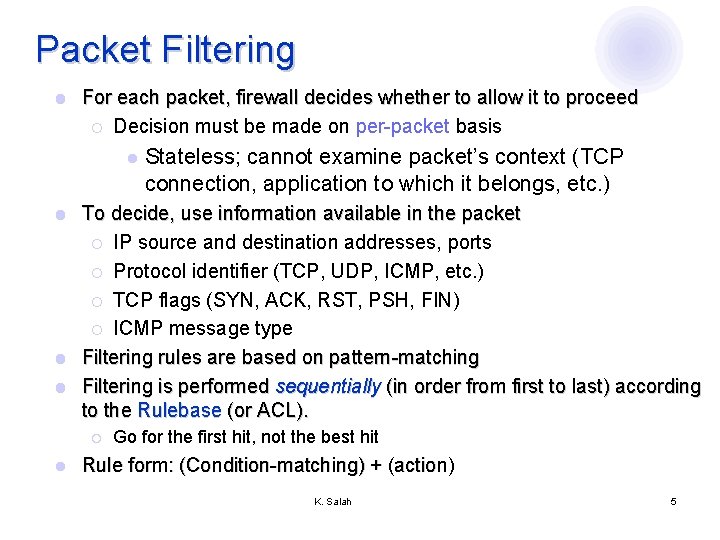
Packet Filtering l For each packet, firewall decides whether to allow it to proceed ¡ Decision must be made on per-packet basis l Stateless; cannot examine packet’s context (TCP connection, application to which it belongs, etc. ) To decide, use information available in the packet ¡ IP source and destination addresses, ports ¡ Protocol identifier (TCP, UDP, ICMP, etc. ) ¡ TCP flags (SYN, ACK, RST, PSH, FIN) ¡ ICMP message type l Filtering rules are based on pattern-matching l Filtering is performed sequentially (in order from first to last) according to the Rulebase (or ACL). l ¡ l Go for the first hit, not the best hit Rule form: (Condition-matching) + (action) K. Salah 5
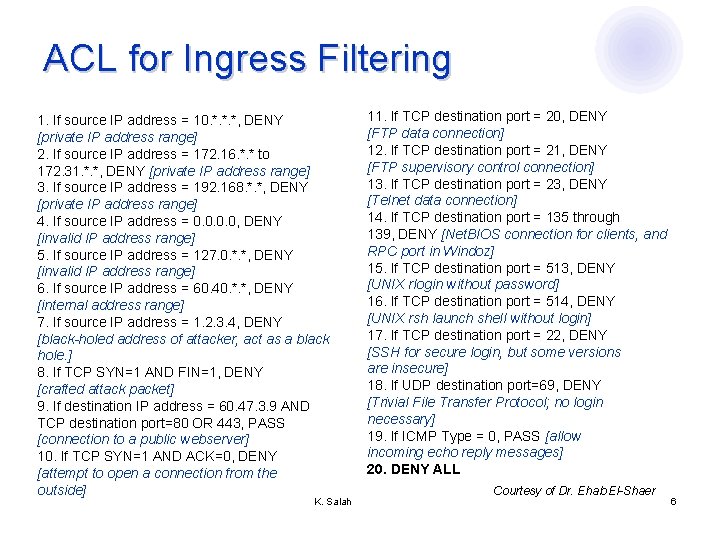
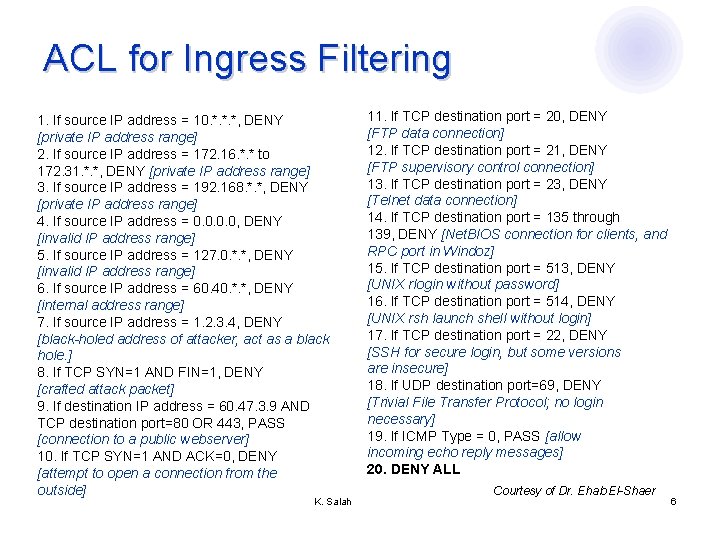
ACL for Ingress Filtering 1. If source IP address = 10. *. *. *, DENY [private IP address range] 2. If source IP address = 172. 16. *. * to 172. 31. *. *, DENY [private IP address range] 3. If source IP address = 192. 168. *. *, DENY [private IP address range] 4. If source IP address = 0. 0, DENY [invalid IP address range] 5. If source IP address = 127. 0. *. *, DENY [invalid IP address range] 6. If source IP address = 60. 40. *. *, DENY [internal address range] 7. If source IP address = 1. 2. 3. 4, DENY [black-holed address of attacker, act as a black hole. ] 8. If TCP SYN=1 AND FIN=1, DENY [crafted attack packet] 9. If destination IP address = 60. 47. 3. 9 AND TCP destination port=80 OR 443, PASS [connection to a public webserver] 10. If TCP SYN=1 AND ACK=0, DENY [attempt to open a connection from the outside] K. Salah 11. If TCP destination port = 20, DENY [FTP data connection] 12. If TCP destination port = 21, DENY [FTP supervisory control connection] 13. If TCP destination port = 23, DENY [Telnet data connection] 14. If TCP destination port = 135 through 139, DENY [Net. BIOS connection for clients, and RPC port in Windoz] 15. If TCP destination port = 513, DENY [UNIX rlogin without password] 16. If TCP destination port = 514, DENY [UNIX rsh launch shell without login] 17. If TCP destination port = 22, DENY [SSH for secure login, but some versions are insecure] 18. If UDP destination port=69, DENY [Trivial File Transfer Protocol; no login necessary] 19. If ICMP Type = 0, PASS [allow incoming echo reply messages] 20. DENY ALL Courtesy of Dr. Ehab El-Shaer 6
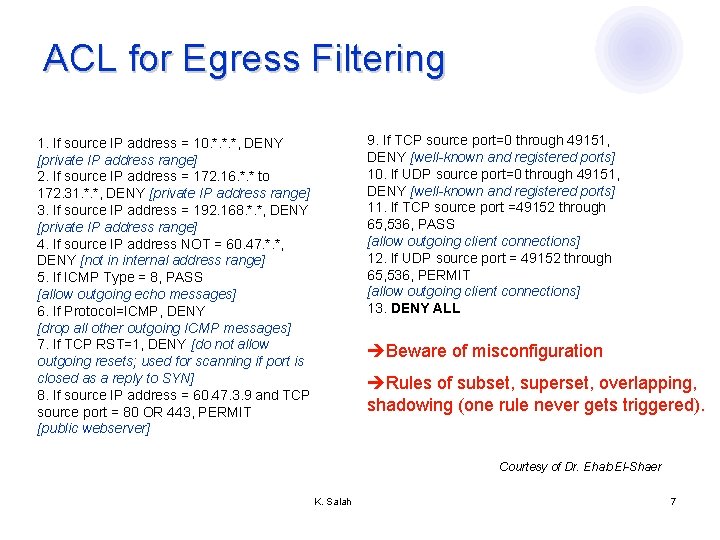
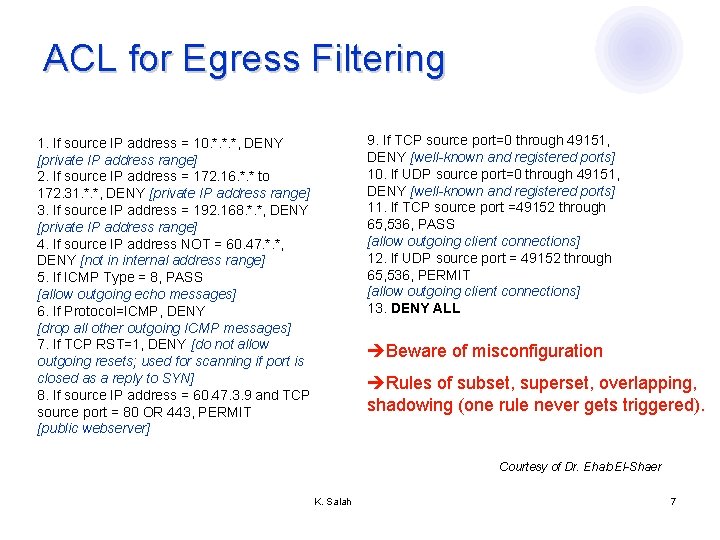
ACL for Egress Filtering 9. If TCP source port=0 through 49151, DENY [well-known and registered ports] 10. If UDP source port=0 through 49151, DENY [well-known and registered ports] 11. If TCP source port =49152 through 65, 536, PASS [allow outgoing client connections] 12. If UDP source port = 49152 through 65, 536, PERMIT [allow outgoing client connections] 13. DENY ALL 1. If source IP address = 10. *. *. *, DENY [private IP address range] 2. If source IP address = 172. 16. *. * to 172. 31. *. *, DENY [private IP address range] 3. If source IP address = 192. 168. *. *, DENY [private IP address range] 4. If source IP address NOT = 60. 47. *. *, DENY [not in internal address range] 5. If ICMP Type = 8, PASS [allow outgoing echo messages] 6. If Protocol=ICMP, DENY [drop all other outgoing ICMP messages] 7. If TCP RST=1, DENY [do not allow outgoing resets; used for scanning if port is closed as a reply to SYN] 8. If source IP address = 60. 47. 3. 9 and TCP source port = 80 OR 443, PERMIT [public webserver] Beware of misconfiguration Rules of subset, superset, overlapping, shadowing (one rule never gets triggered). Courtesy of Dr. Ehab El-Shaer K. Salah 7
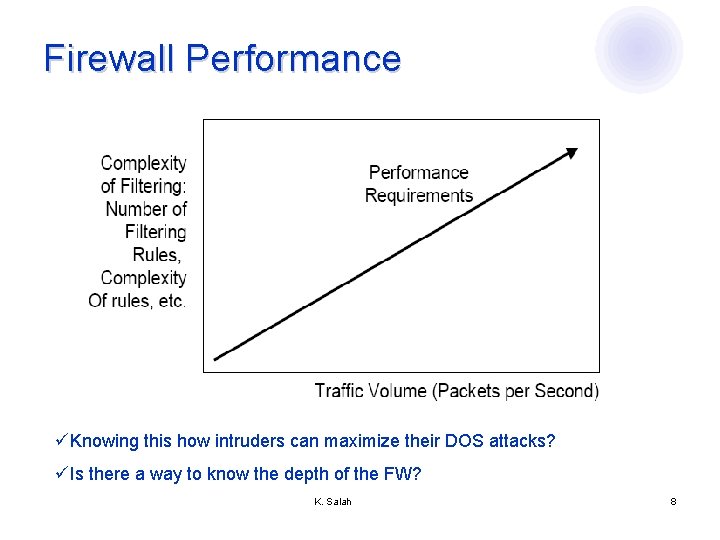
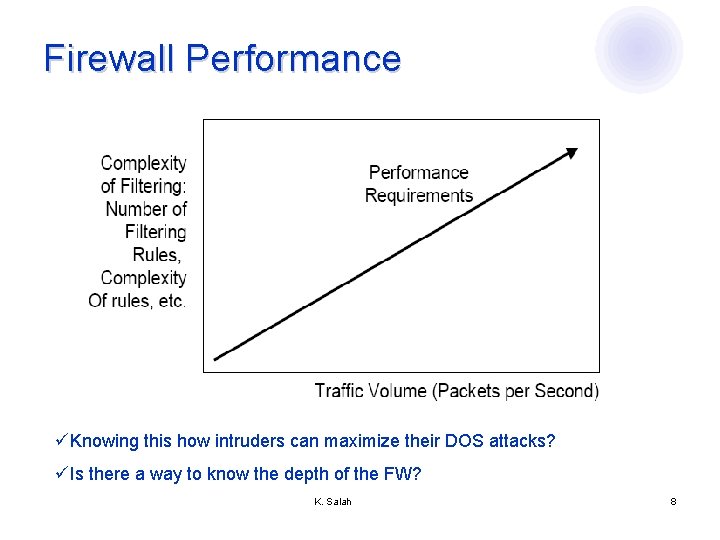
Firewall Performance üKnowing this how intruders can maximize their DOS attacks? üIs there a way to know the depth of the FW? K. Salah 8
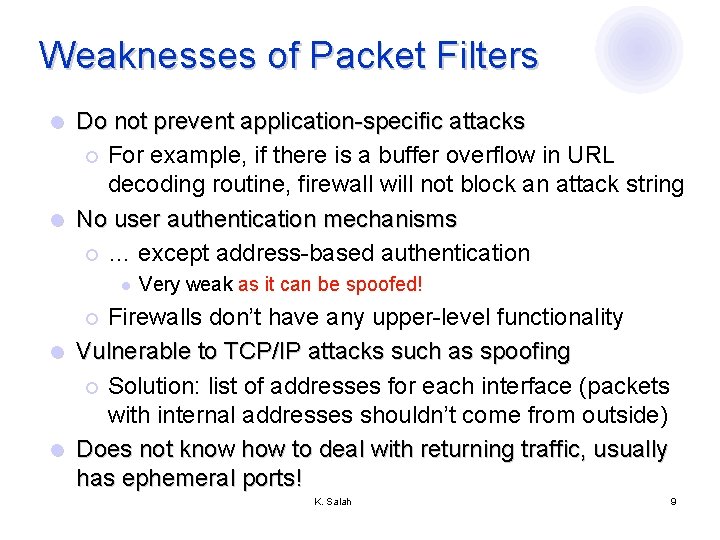
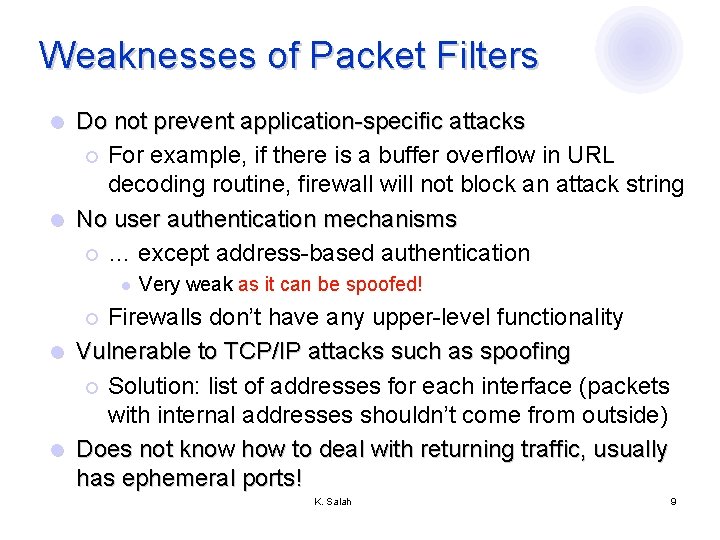
Weaknesses of Packet Filters Do not prevent application-specific attacks ¡ For example, if there is a buffer overflow in URL decoding routine, firewall will not block an attack string l No user authentication mechanisms ¡ … except address-based authentication l l Very weak as it can be spoofed! Firewalls don’t have any upper-level functionality l Vulnerable to TCP/IP attacks such as spoofing ¡ Solution: list of addresses for each interface (packets with internal addresses shouldn’t come from outside) l Does not know how to deal with returning traffic, usually has ephemeral ports! ¡ K. Salah 9
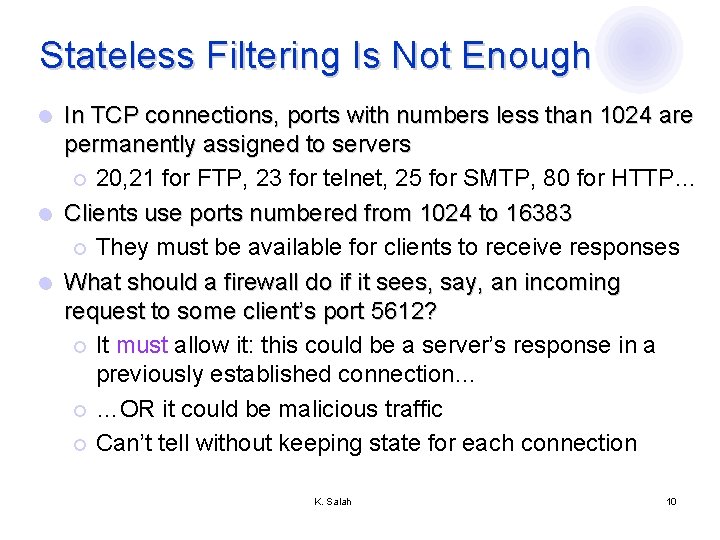
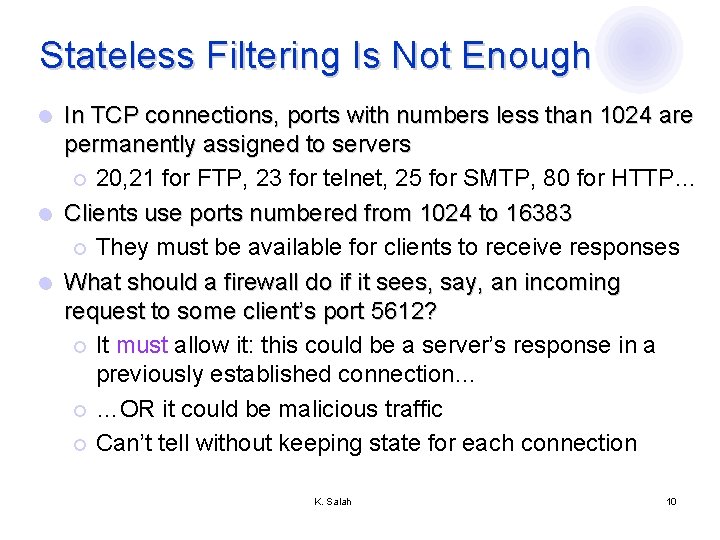
Stateless Filtering Is Not Enough In TCP connections, ports with numbers less than 1024 are permanently assigned to servers ¡ 20, 21 for FTP, 23 for telnet, 25 for SMTP, 80 for HTTP… l Clients use ports numbered from 1024 to 16383 ¡ They must be available for clients to receive responses l What should a firewall do if it sees, say, an incoming request to some client’s port 5612? ¡ It must allow it: this could be a server’s response in a previously established connection… ¡ …OR it could be malicious traffic ¡ Can’t tell without keeping state for each connection l K. Salah 10
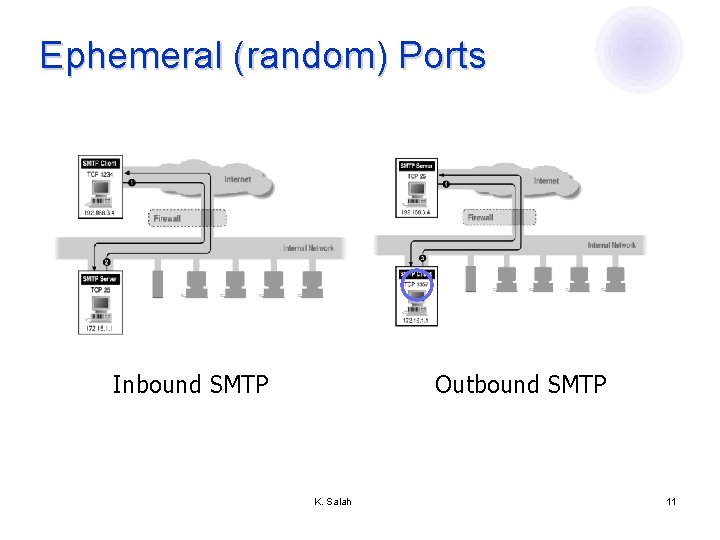
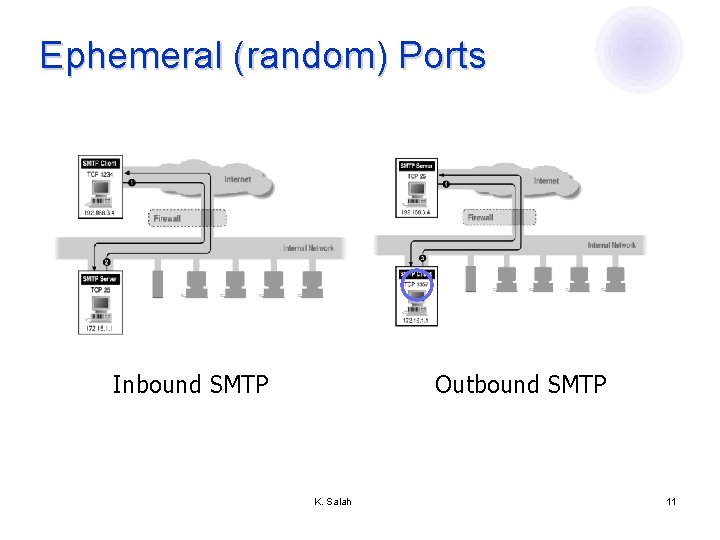
Ephemeral (random) Ports Inbound SMTP Outbound SMTP K. Salah 11
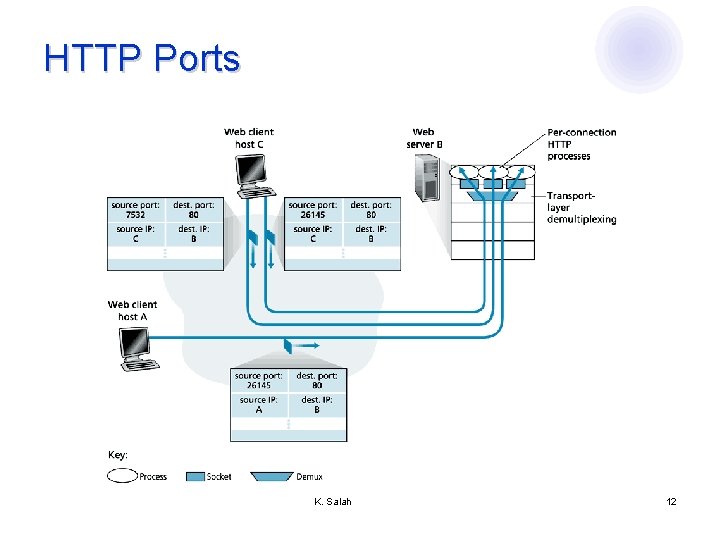
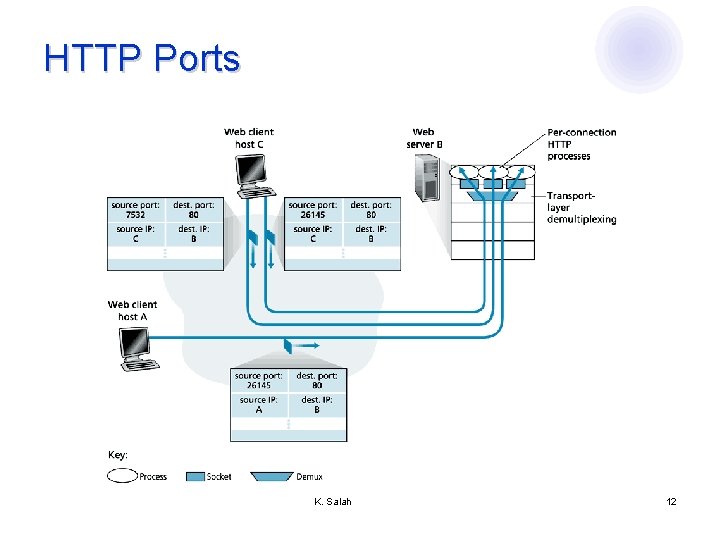
HTTP Ports K. Salah 12
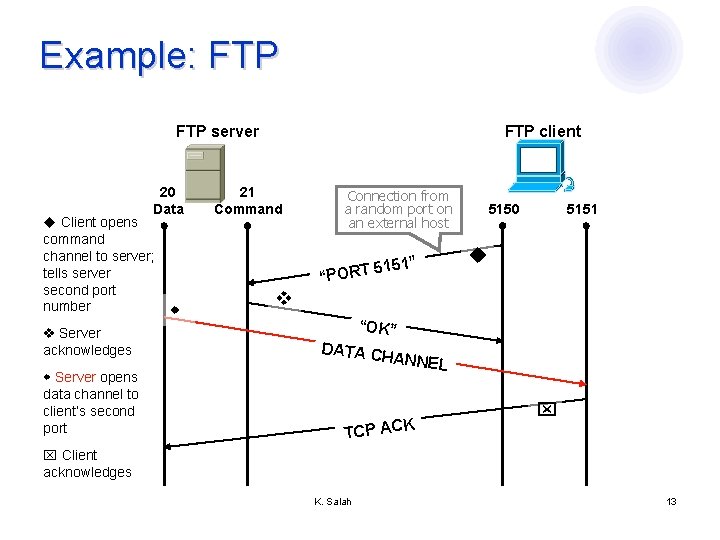
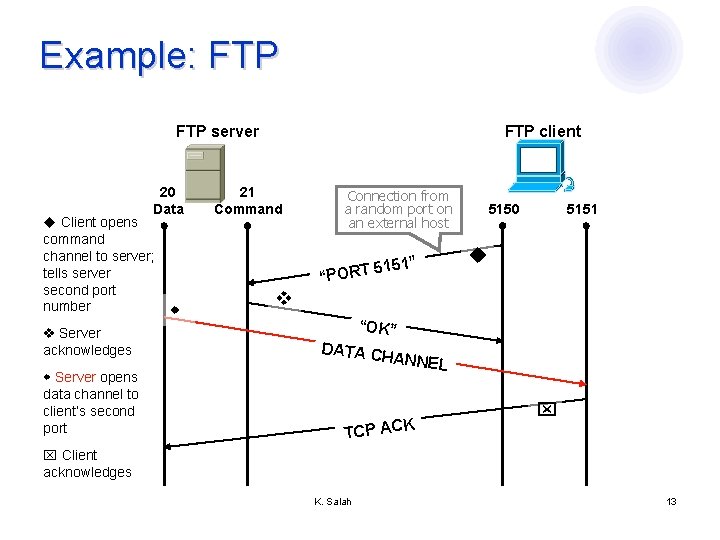
Example: FTP server 20 Data Client opens command channel to server; tells server second port number Server acknowledges Server opens data channel to client’s second port FTP client 21 Command Connection from a random port on an external host 5151” “PORT 5150 5151 “OK” DATA C HANNEL CP ACK T Client acknowledges K. Salah 13
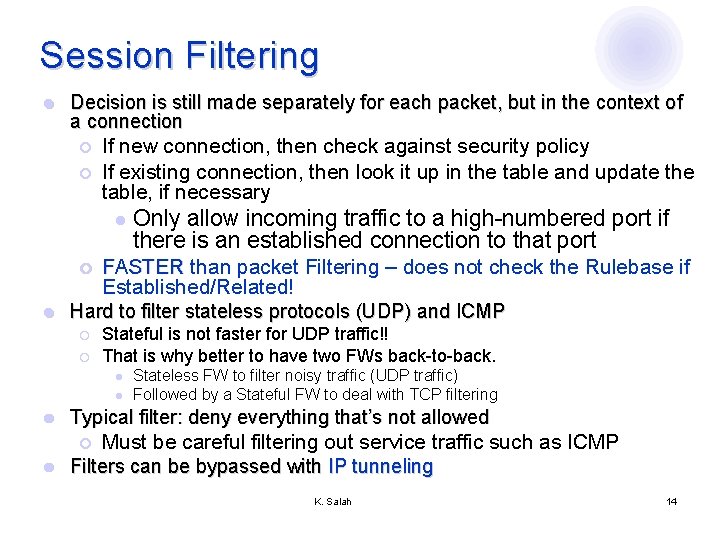
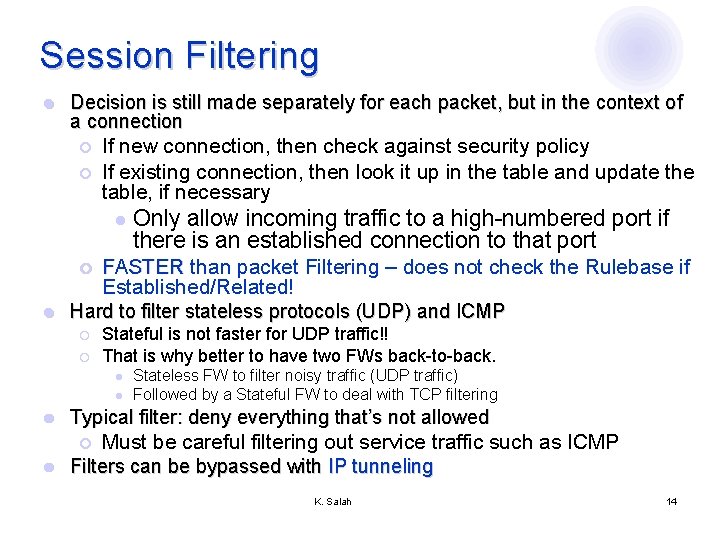
Session Filtering l Decision is still made separately for each packet, but in the context of a connection ¡ ¡ If new connection, then check against security policy If existing connection, then look it up in the table and update the table, if necessary l Only allow incoming traffic to a high-numbered port if there is an established connection to that port FASTER than packet Filtering – does not check the Rulebase if Established/Related! Hard to filter stateless protocols (UDP) and ICMP ¡ l ¡ ¡ Stateful is not faster for UDP traffic!! That is why better to have two FWs back-to-back. l l Stateless FW to filter noisy traffic (UDP traffic) Followed by a Stateful FW to deal with TCP filtering l Typical filter: deny everything that’s not allowed l Must be careful filtering out service traffic such as ICMP Filters can be bypassed with IP tunneling ¡ K. Salah 14
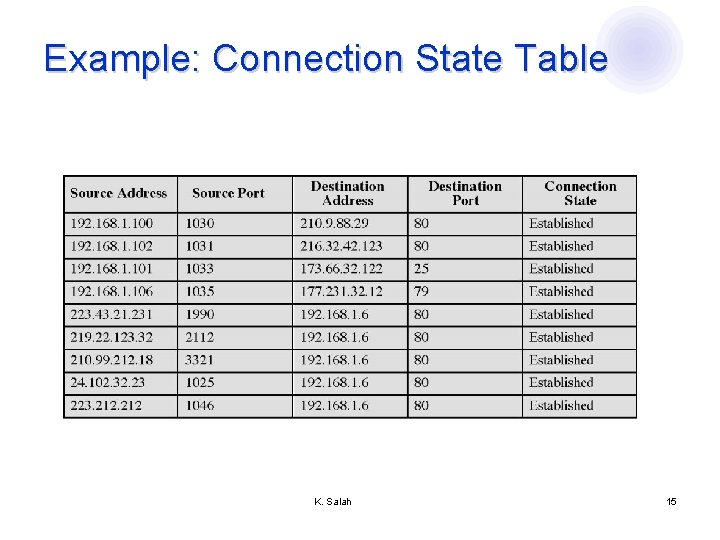
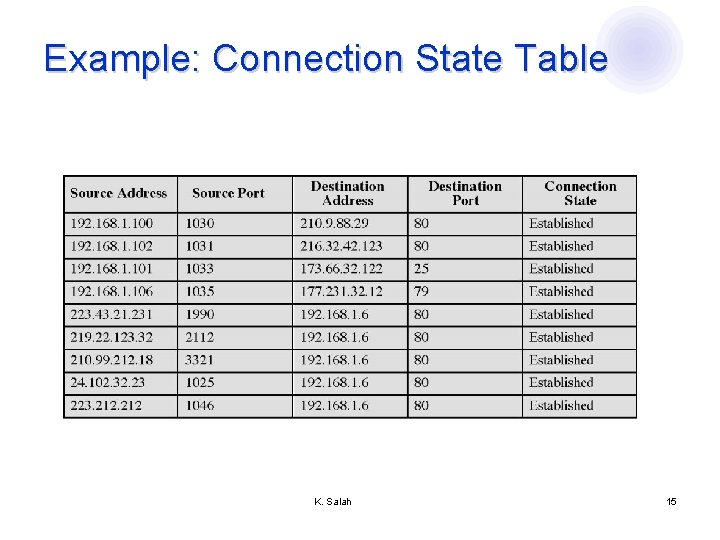
Example: Connection State Table K. Salah 15
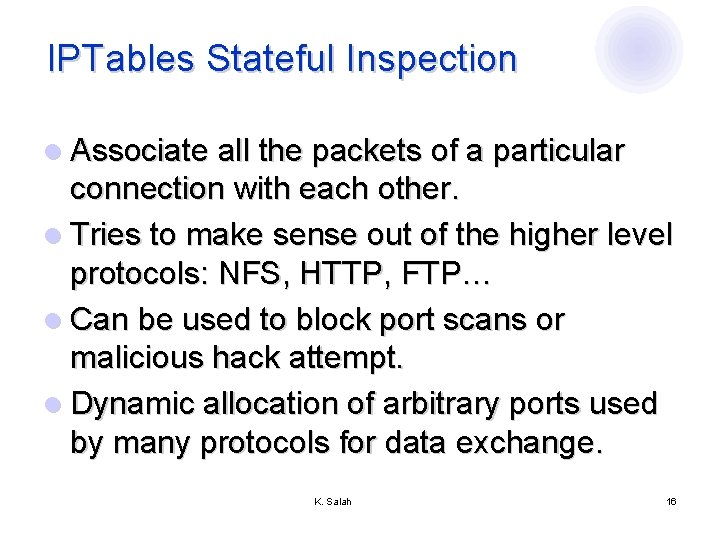
IPTables Stateful Inspection l Associate all the packets of a particular connection with each other. l Tries to make sense out of the higher level protocols: NFS, HTTP, FTP… l Can be used to block port scans or malicious hack attempt. l Dynamic allocation of arbitrary ports used by many protocols for data exchange. K. Salah 16
IPTables Stateful Inspection l States ¡ NEW ¡ RELATED ¡ INVALID ¡ ESTABLISHED ¡ RELATED+REPLY K. Salah 17
Available Firewalls l Buy a solution ¡ Hardware -- PIX, Sonicwall, Watch. Guard… ¡ Software -- Check. Point, ISA, Boarder Manager l Build a solution ¡ Linux – IPTables, Netfilter ¡ BSD -- IPFW, IPFilter, pf K. Salah 18
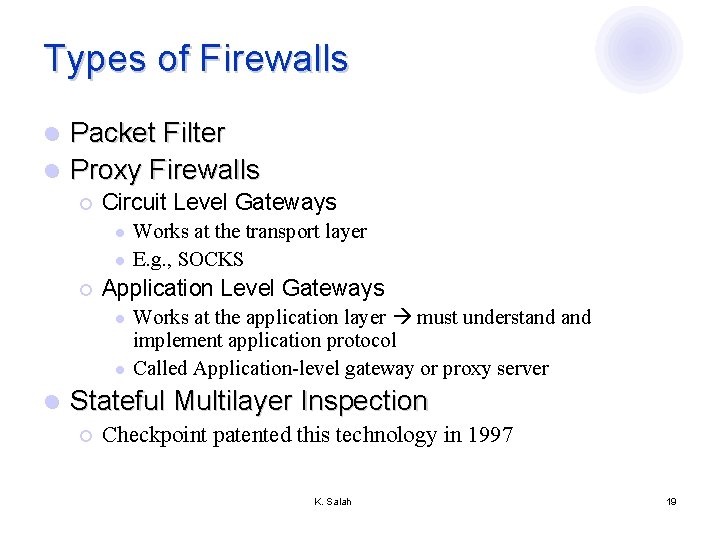
Types of Firewalls Packet Filter l Proxy Firewalls l ¡ Circuit Level Gateways l l ¡ Application Level Gateways l l l Works at the transport layer E. g. , SOCKS Works at the application layer must understand implement application protocol Called Application-level gateway or proxy server Stateful Multilayer Inspection ¡ Checkpoint patented this technology in 1997 K. Salah 19
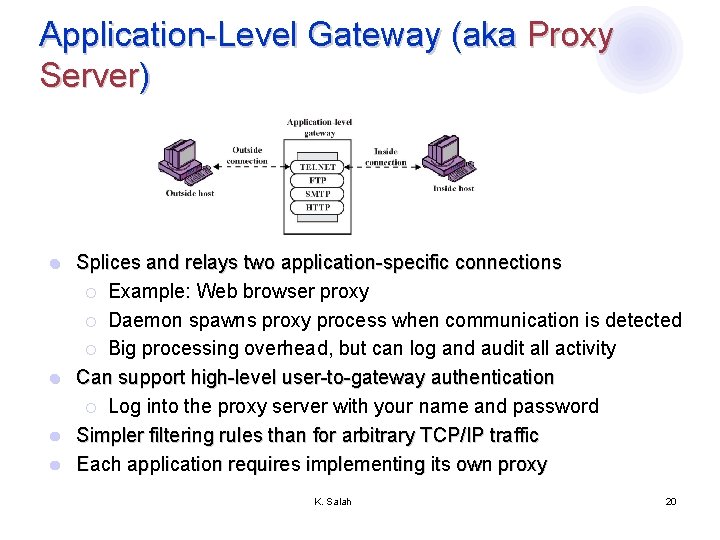
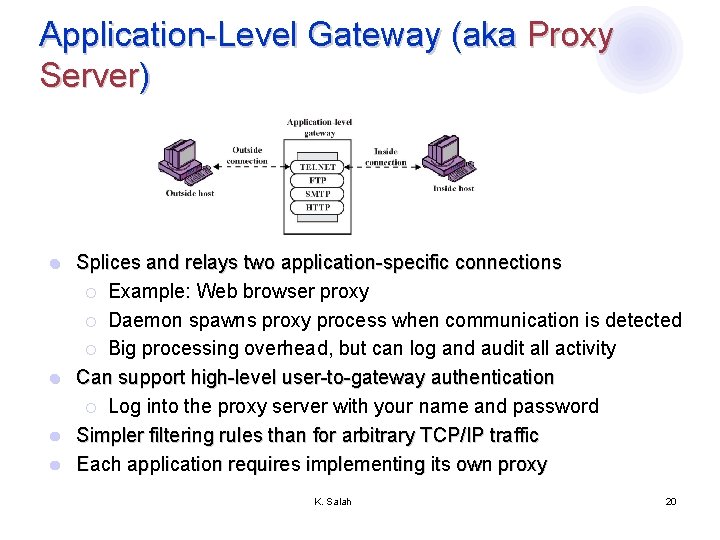
Application-Level Gateway (aka Proxy Server) Splices and relays two application-specific connections ¡ Example: Web browser proxy ¡ Daemon spawns proxy process when communication is detected ¡ Big processing overhead, but can log and audit all activity l Can support high-level user-to-gateway authentication ¡ Log into the proxy server with your name and password l Simpler filtering rules than for arbitrary TCP/IP traffic l Each application requires implementing its own proxy l K. Salah 20
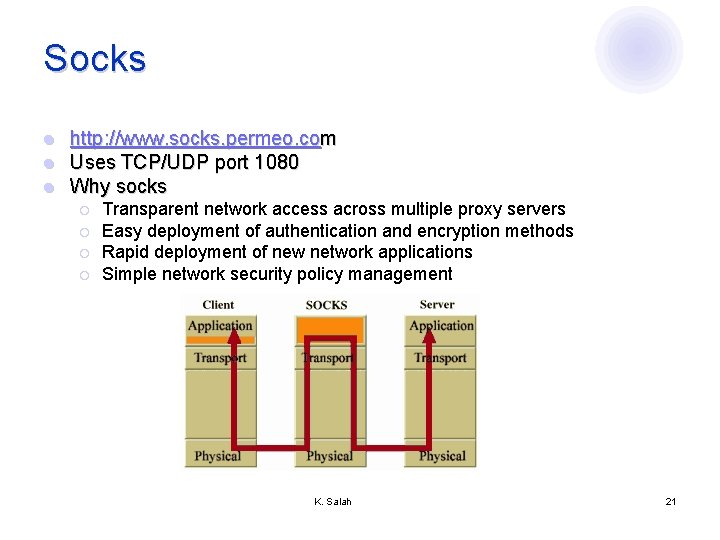
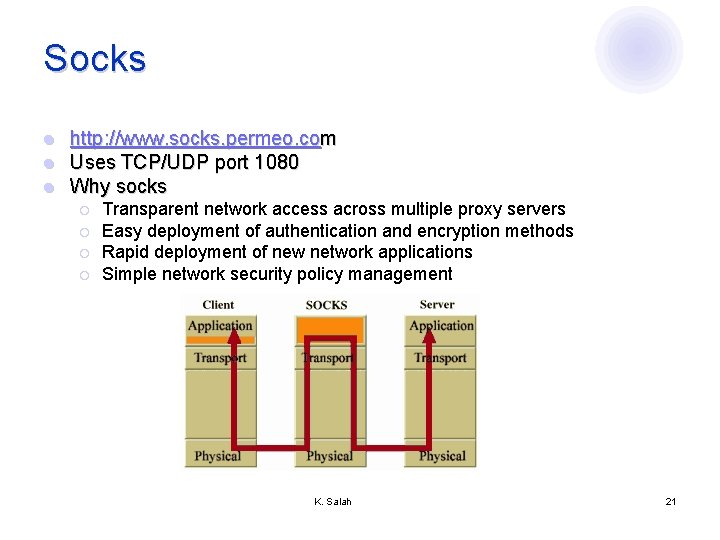
Socks l l l http: //www. socks. permeo. com Uses TCP/UDP port 1080 Why socks ¡ ¡ Transparent network access across multiple proxy servers Easy deployment of authentication and encryption methods Rapid deployment of new network applications Simple network security policy management K. Salah 21
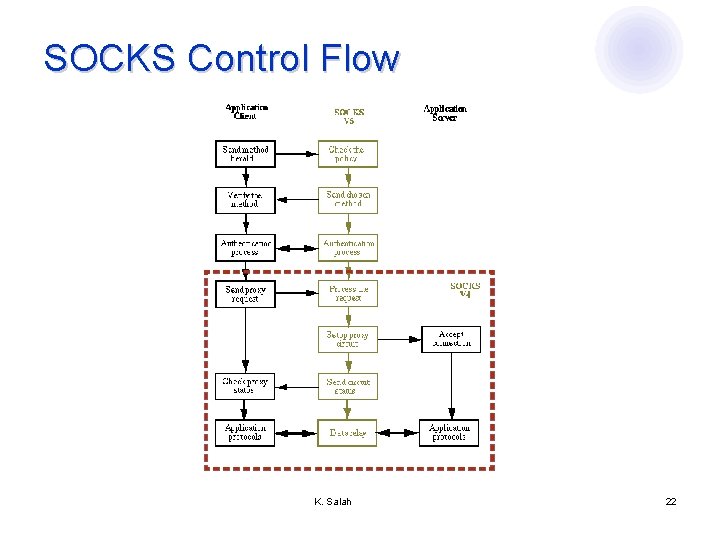
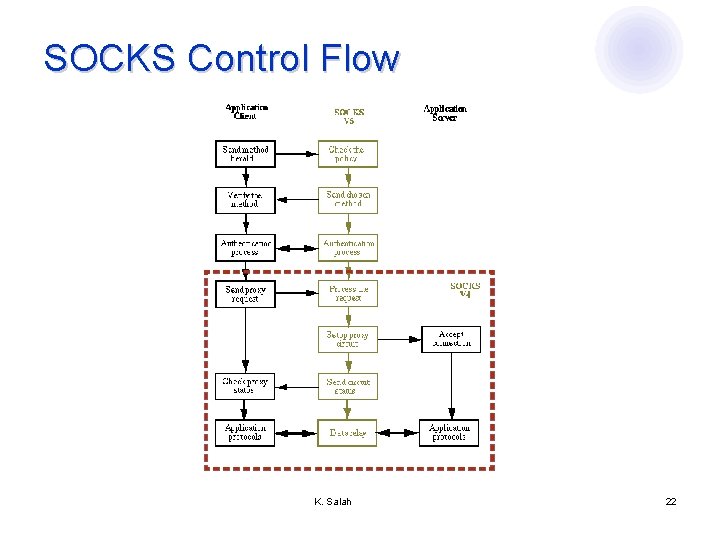
SOCKS Control Flow K. Salah 22
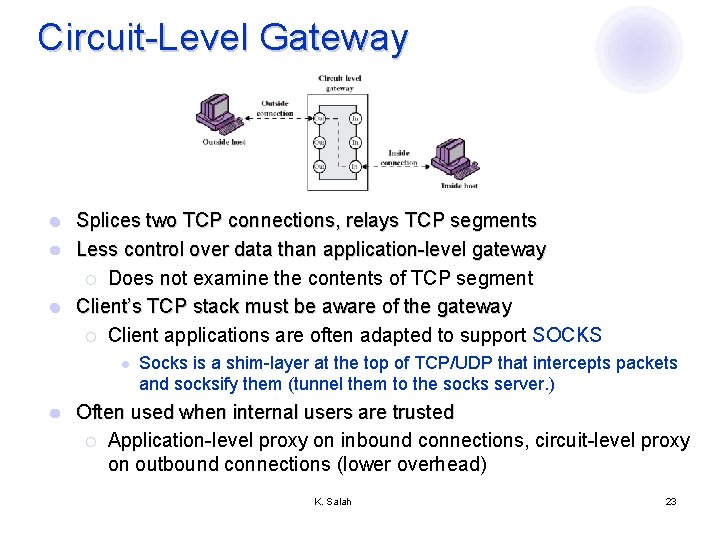
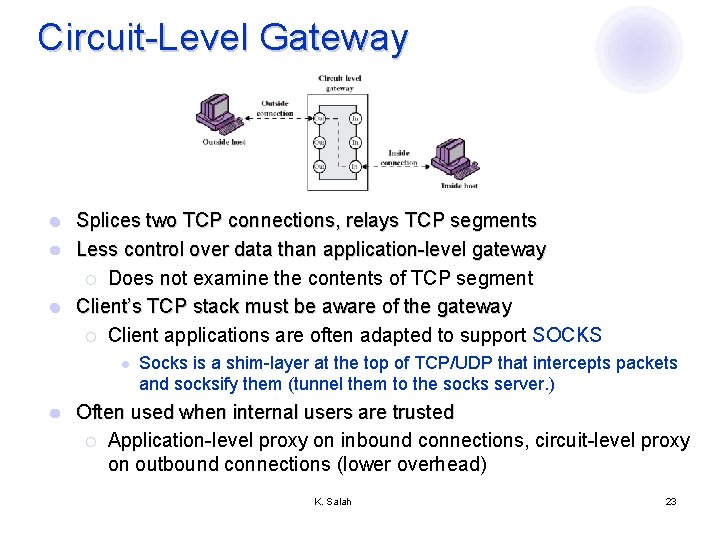
Circuit-Level Gateway Splices two TCP connections, relays TCP segments l Less control over data than application-level gateway ¡ Does not examine the contents of TCP segment l Client’s TCP stack must be aware of the gateway ¡ Client applications are often adapted to support SOCKS l l l Socks is a shim-layer at the top of TCP/UDP that intercepts packets and socksify them (tunnel them to the socks server. ) Often used when internal users are trusted ¡ Application-level proxy on inbound connections, circuit-level proxy on outbound connections (lower overhead) K. Salah 23
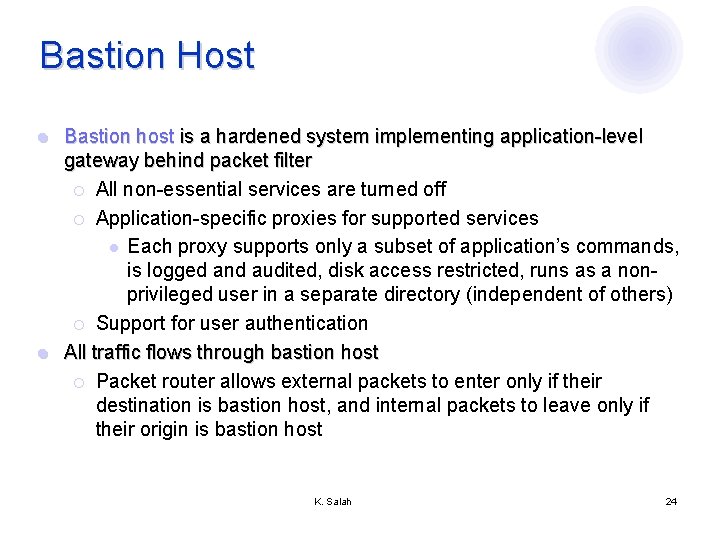
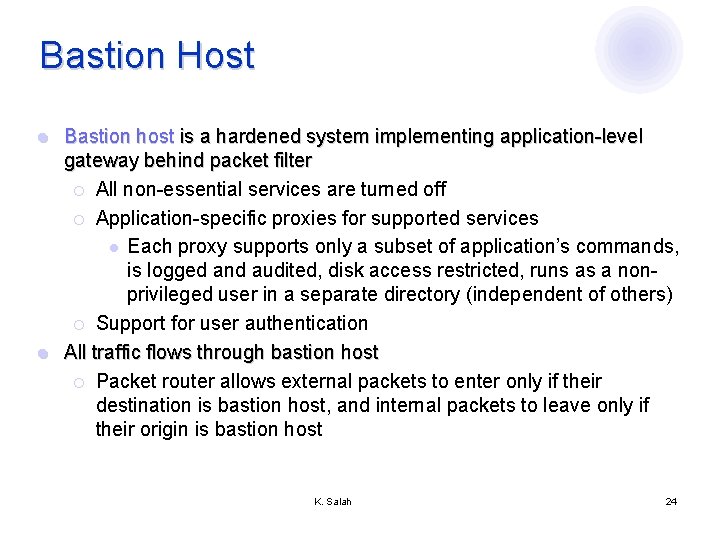
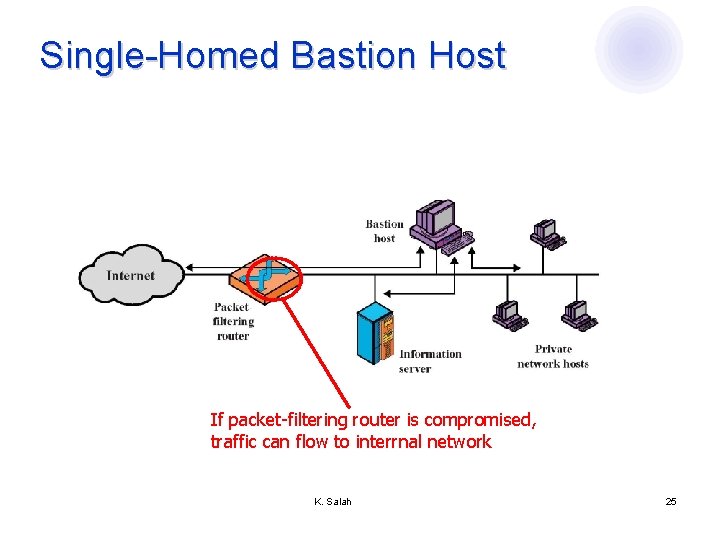
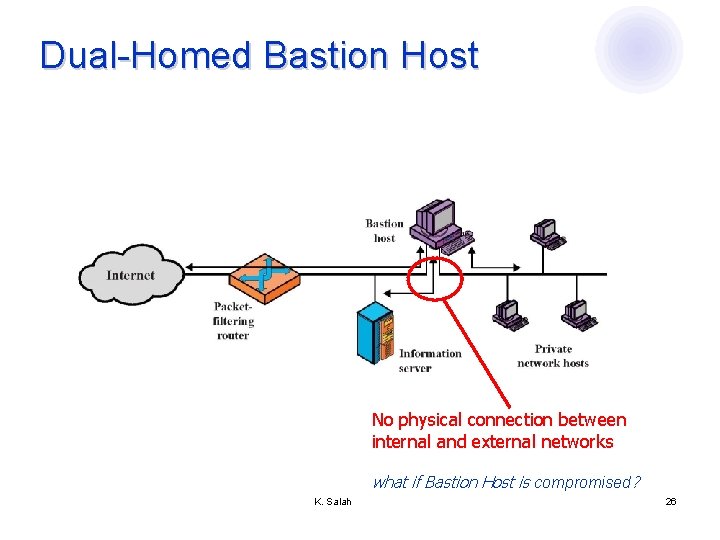
Bastion Host Bastion host is a hardened system implementing application-level gateway behind packet filter ¡ All non-essential services are turned off ¡ Application-specific proxies for supported services l Each proxy supports only a subset of application’s commands, is logged and audited, disk access restricted, runs as a nonprivileged user in a separate directory (independent of others) ¡ Support for user authentication l All traffic flows through bastion host ¡ Packet router allows external packets to enter only if their destination is bastion host, and internal packets to leave only if their origin is bastion host l K. Salah 24
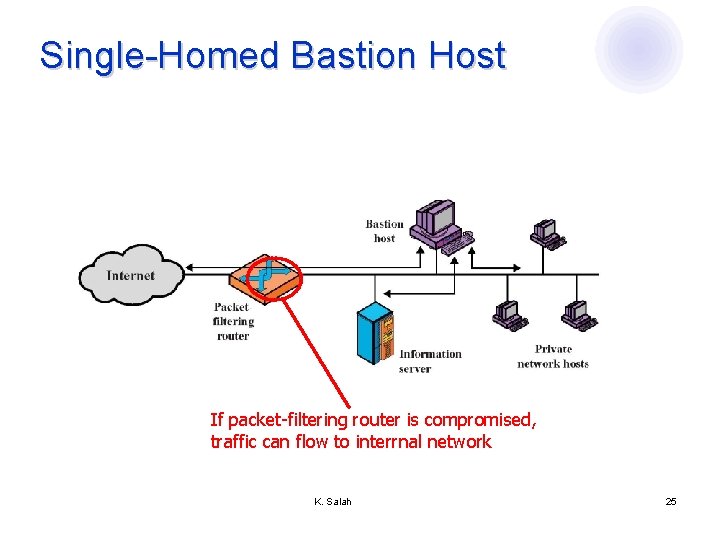
Single-Homed Bastion Host If packet-filtering router is compromised, traffic can flow to interrnal network K. Salah 25
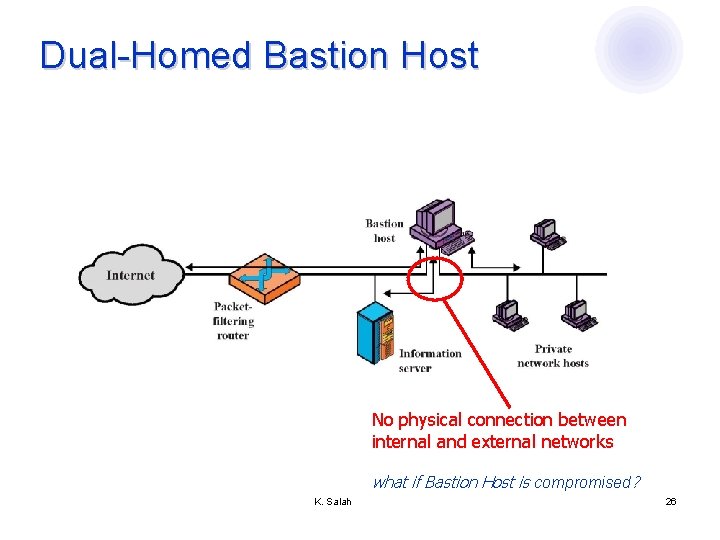
Dual-Homed Bastion Host No physical connection between internal and external networks what if Bastion Host is compromised? K. Salah 26
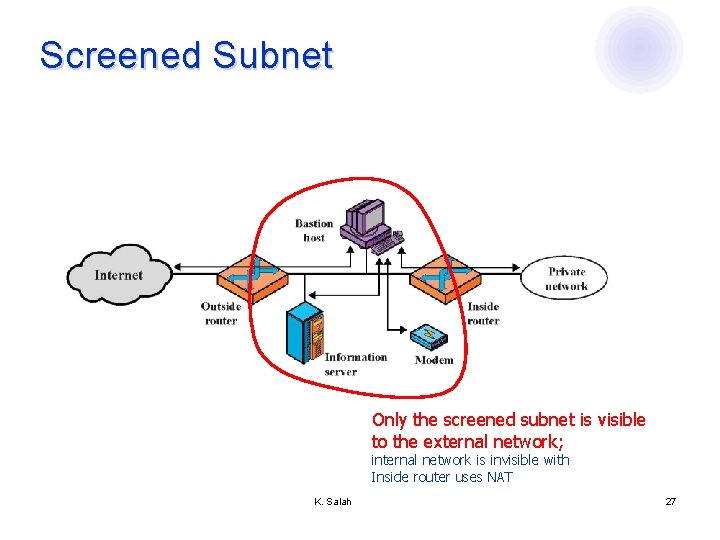
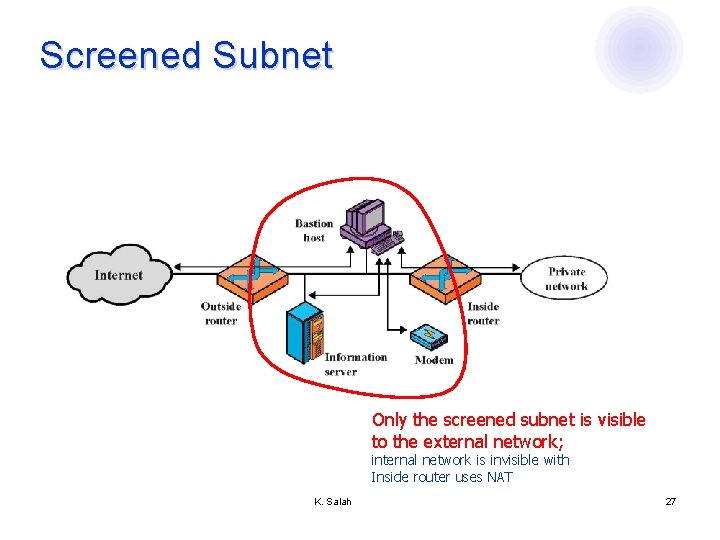
Screened Subnet Only the screened subnet is visible to the external network; internal network is invisible with Inside router uses NAT K. Salah 27
Protecting Addresses and Routes Hide IP addresses of hosts on internal network ¡ Only services that are intended to be accessed from outside need to reveal their IP addresses ¡ Keep other addresses secret to make spoofing harder l Use NAT (network address translation) to map addresses in packet headers to internal addresses ¡ 1 -to-1 or N-to-1 mapping l Filter route announcements ¡ No need to advertise routes to internal hosts ¡ Prevent attacker from advertising that the shortest route to an internal host lies through him l K. Salah 28
General Problems with Firewalls l Interfere with networked applications l Don’t solve the real problems ¡ Buggy software (think buffer overflow exploits) ¡ Bad protocol design (think WEP in 802. 11 b) l Generally don’t prevent denial of service l Don’t prevent insider attacks l Increasing complexity and potential for misconfiguration K. Salah 29