ARSPA 05 Design and Analysis of Diffie HellmanBased
ARSPA’ 05 Design and Analysis of Diffie. Hellman-Based Key Exchange Using One-time ID by SVO Logic Kenji Imamoto, Kouichi Sakurai Kyushu University, Japan 1
Outline n Introduction ¨ Background ¨ Idea of One-time ID ¨ Key exchange in three-party model n n Preliminaries of SVO Logic Proposed Protocol ¨ Propose a three-party key exchange using One-time ID ¨ Analyze the proposed protocol by SVO Logic ¨ Propose One-time ID generation method n Conclusion 2
n Main focus of our study is … Authenticated key exchange protocol based on pre-shared key In most previous works, ØLeakage of user’s Identity, Do. S attack Denial of Service attack Pre-shared key model Shared secret 3
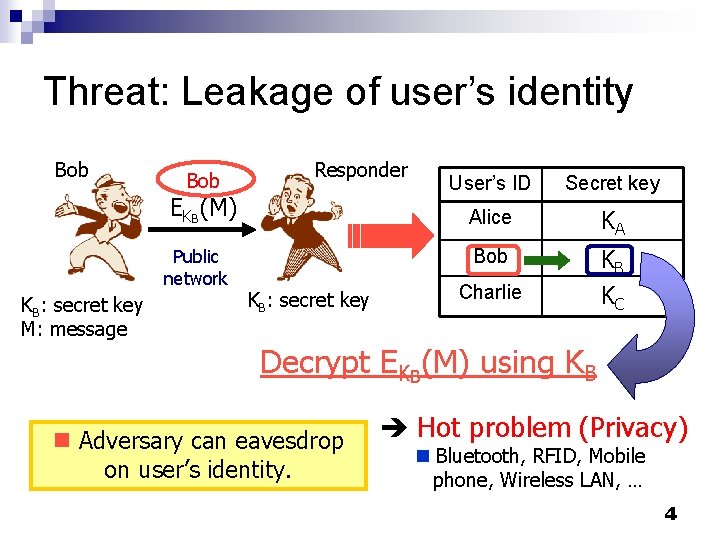
Threat: Leakage of user’s identity Bob Responder EKB(M) Public network KB: secret key M: message KB: secret key User’s ID Secret key Alice KA Bob KB KC Charlie Decrypt EKB(M) using KB n Adversary can eavesdrop on user’s identity. Hot problem (Privacy) n Bluetooth, RFID, Mobile phone, Wireless LAN, … 4
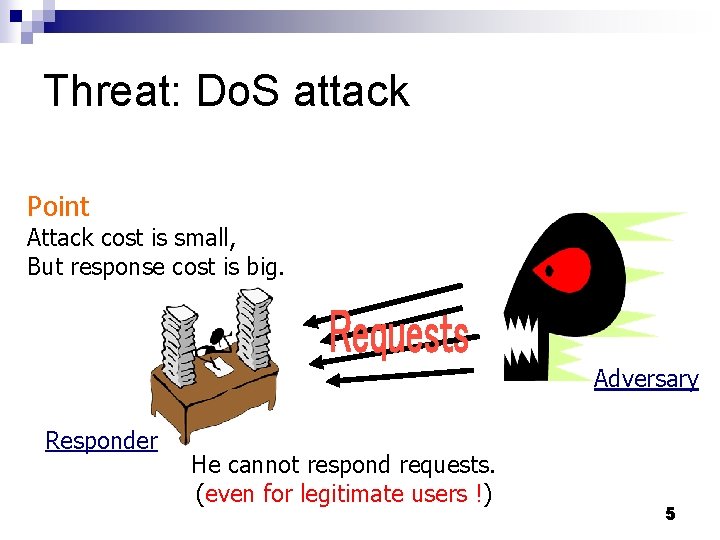
Threat: Do. S attack Point Attack cost is small, But response cost is big. Adversary Responder He cannot respond requests. (even for legitimate users !) 5
n To prevent leakage of user’s identity, we need an identity that cannot be specified by eavesdropper. ¨ By substituting shared secret for user’s identity u Legitimate user can specify his partner. u Adversary cannot specify who is communicating. n To prevent Do. S attack, we need an identity that is one-time and adversary cannot guess the next valid identity. u Responder checks validity of identity before he responds. (the cost of checking is small. ) n Encrypted communication, Key establishment protocol, Authentication … 6
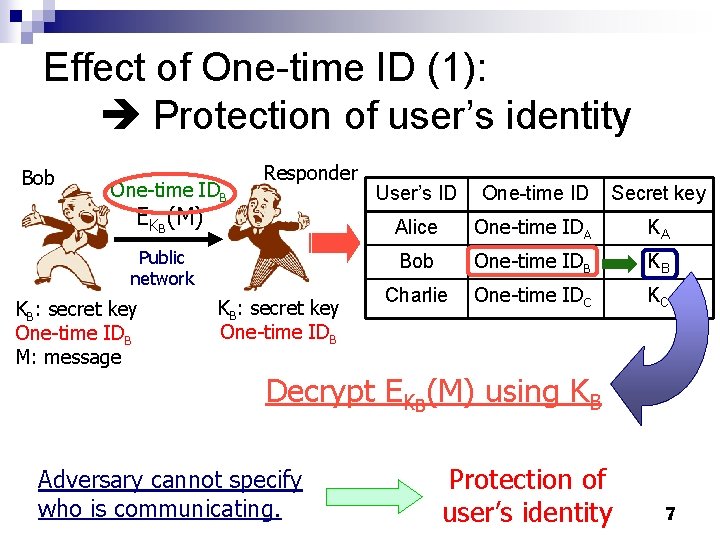
Effect of One-time ID (1): Protection of user’s identity Bob One-time IDB Responder EKB(M) Public network KB: secret key One-time IDB M: message KB: secret key One-time IDB User’s ID One-time ID Secret key Alice One-time IDA KA Bob One-time IDB KB Charlie One-time IDC KC Decrypt EKB(M) using KB Adversary cannot specify who is communicating. Protection of user’s identity 7
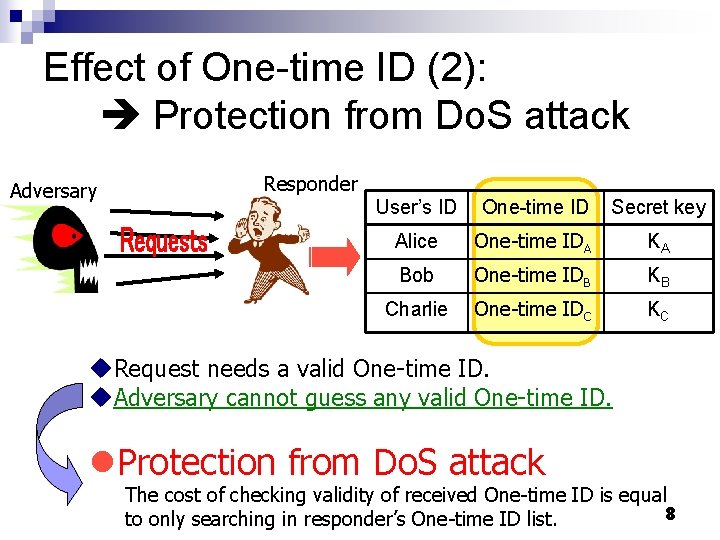
Effect of One-time ID (2): Protection from Do. S attack Adversary Responder User’s ID One-time ID Secret key Alice One-time IDA KA Bob One-time IDB KB Charlie One-time IDC KC u. Request needs a valid One-time ID. u. Adversary cannot guess any valid One-time ID. l. Protection from Do. S attack The cost of checking validity of received One-time ID is equal 8 to only searching in responder’s One-time ID list.
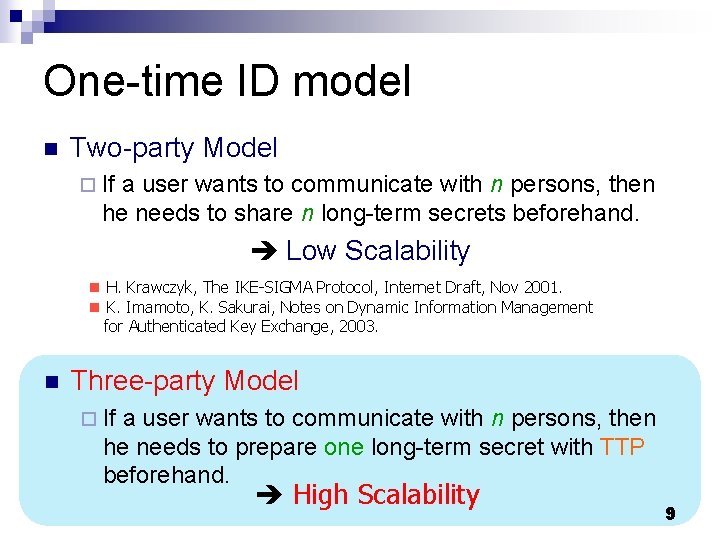
One-time ID model n Two-party Model ¨ If a user wants to communicate with n persons, then he needs to share n long-term secrets beforehand. Low Scalability n H. Krawczyk, The IKE-SIGMA Protocol, Internet Draft, Nov 2001. n K. Imamoto, K. Sakurai, Notes on Dynamic Information Management for Authenticated Key Exchange, 2003. n Three-party Model ¨ If a user wants to communicate with n persons, then he needs to prepare one long-term secret with TTP beforehand. High Scalability 9
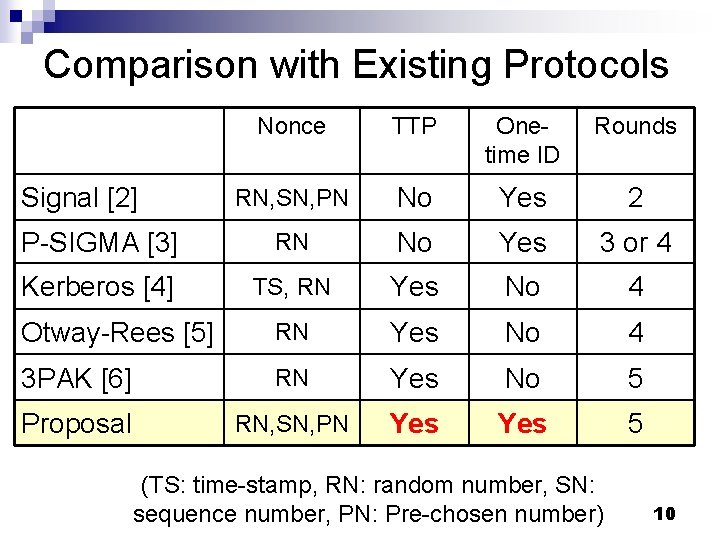
Comparison with Existing Protocols Nonce TTP Onetime ID Rounds RN, SN, PN No Yes 2 P-SIGMA [3] RN No Yes 3 or 4 Kerberos [4] TS, RN Yes No 4 Otway-Rees [5] RN Yes No 4 3 PAK [6] RN Yes No 5 Proposal RN, SN, PN Yes 5 Signal [2] (TS: time-stamp, RN: random number, SN: sequence number, PN: Pre-chosen number) 10
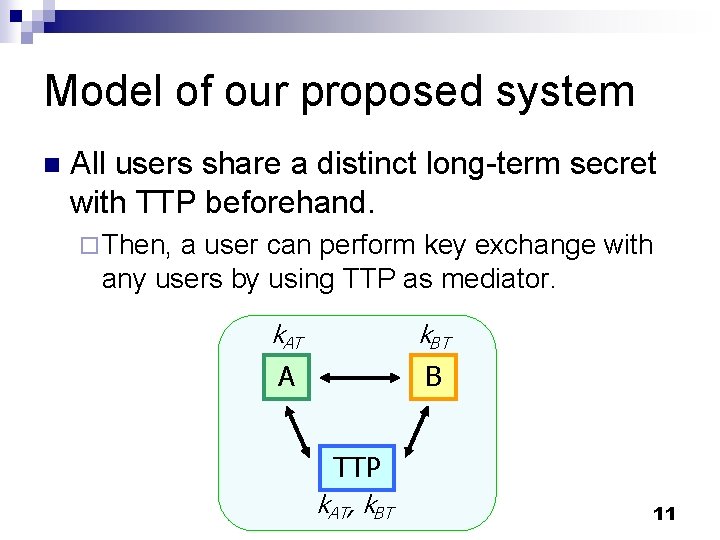
Model of our proposed system n All users share a distinct long-term secret with TTP beforehand. ¨ Then, a user can perform key exchange with any users by using TTP as mediator. k. AT k. BT A B TTP k. AT, k. BT 11
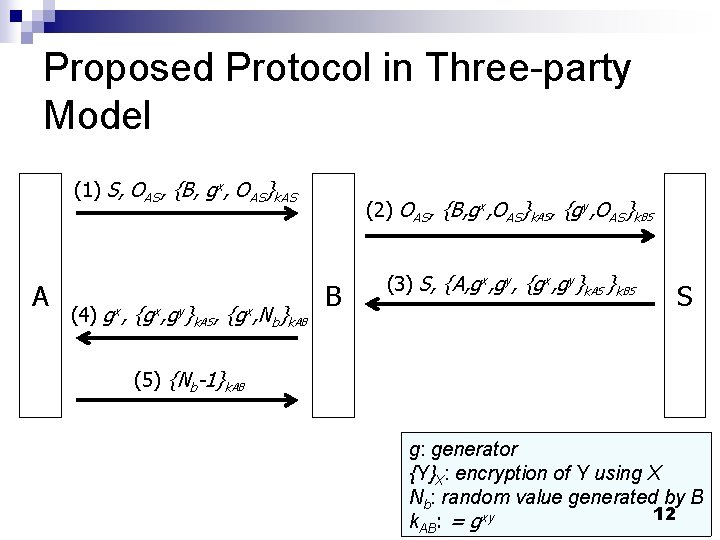
Proposed Protocol in Three-party Model (1) S, OAS, {B, gx, OAS}k. AS A (4) gx, {gx, gy} k. AS, {gx, N b}k. AB (2) OAS, {B, gx, OAS}k. AS, {gy, OAS}k. BS B (3) S, {A, gx, gy, {gx, gy}k. AS }k. BS S (5) {Nb-1}k. AB g: generator {Y}X: encryption of Y using X Nb: random value generated by B 12 k. AB: = gxy
![Preliminaries of SVO Logic n SVO Logic [7, 8] ¨A formal method for authentication Preliminaries of SVO Logic n SVO Logic [7, 8] ¨A formal method for authentication](http://slidetodoc.com/presentation_image/215b2002478aef8478b955b30377d362/image-13.jpg)
Preliminaries of SVO Logic n SVO Logic [7, 8] ¨A formal method for authentication protocols Based on modal logic n Especially, applicable to authenticated key exchange protocol including Diffie-Hellman-based protocol n SVO logic can clarify üwhich assumptions are necessary üwhich authentication goals are achievable 13
Preliminaries of SVO Logic SVO notations n SVO rules n SVO axioms n Authentication goals n 14
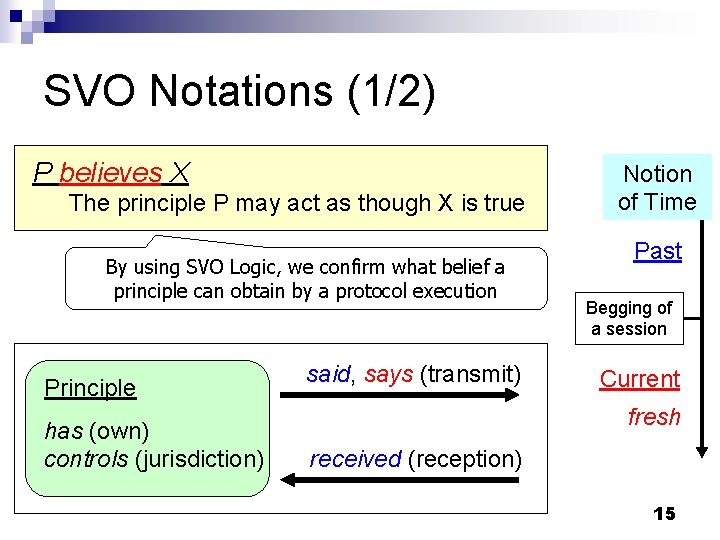
SVO Notations (1/2) P believes X The principle P may act as though X is true By using SVO Logic, we confirm what belief a principle can obtain by a protocol execution Principle has (own) controls (jurisdiction) said, says (transmit) Notion of Time Past Begging of a session Current fresh received (reception) 15
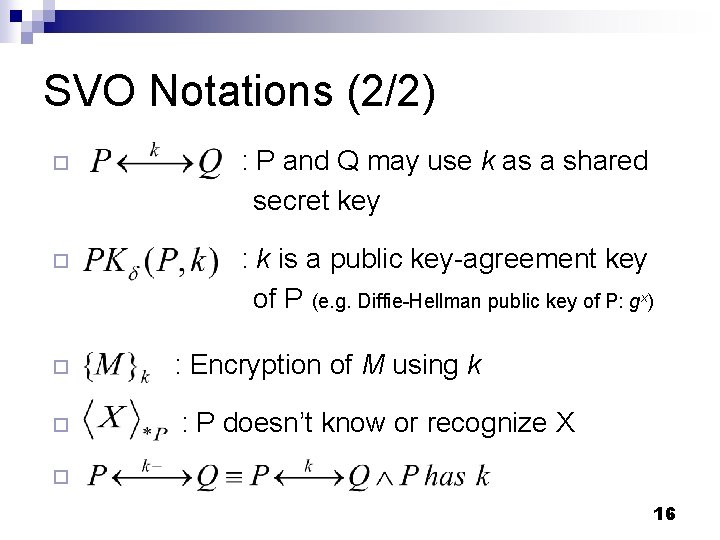
SVO Notations (2/2) ¨ : P and Q may use k as a shared secret key ¨ : k is a public key-agreement key of P (e. g. Diffie-Hellman public key of P: gx) ¨ ¨ : Encryption of M using k : P doesn’t know or recognize X ¨ 16
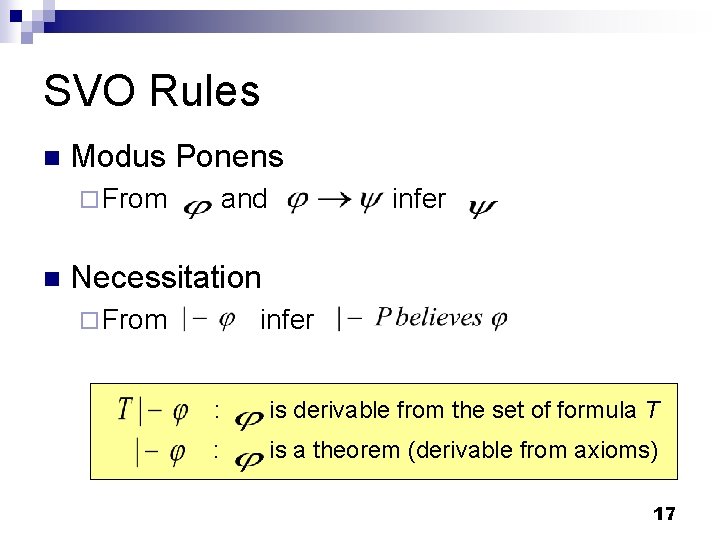
SVO Rules n Modus Ponens ¨ From n and infer Necessitation ¨ From infer : is derivable from the set of formula T : is a theorem (derivable from axioms) 17
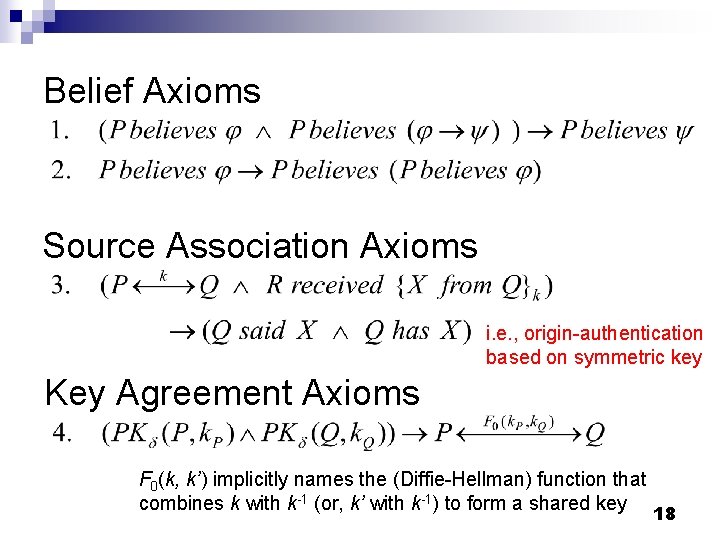
Belief Axioms Source Association Axioms i. e. , origin-authentication based on symmetric key Key Agreement Axioms F 0(k, k’) implicitly names the (Diffie-Hellman) function that combines k with k-1 (or, k’ with k-1) to form a shared key 18
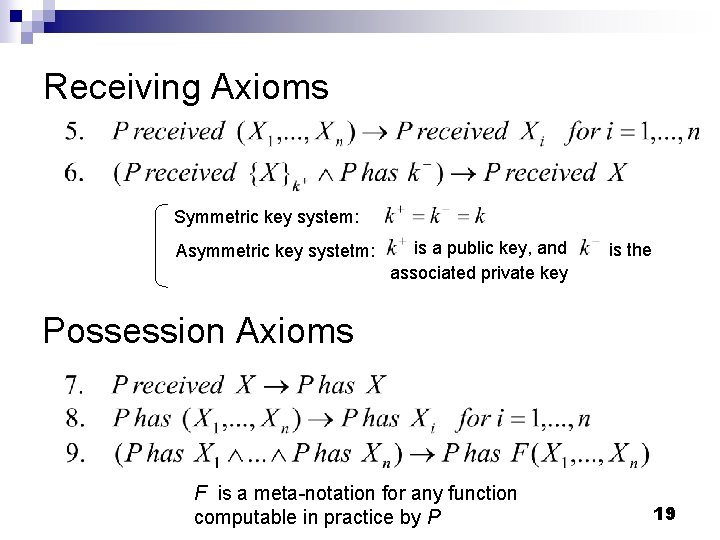
Receiving Axioms Symmetric key system: Asymmetric key systetm: is a public key, and associated private key is the Possession Axioms F is a meta-notation for any function computable in practice by P 19
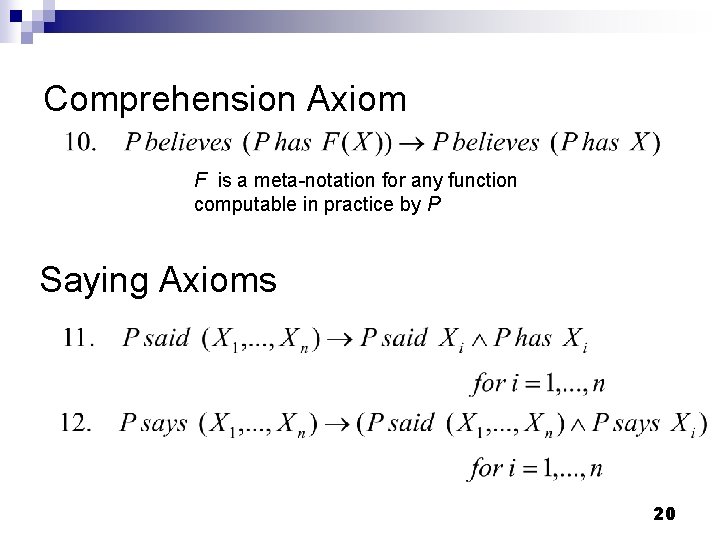
Comprehension Axiom F is a meta-notation for any function computable in practice by P Saying Axioms 20
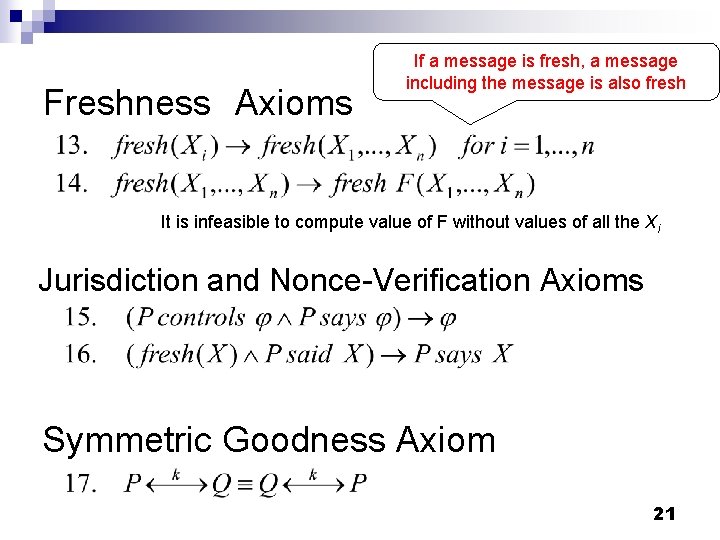
Freshness Axioms If a message is fresh, a message including the message is also fresh It is infeasible to compute value of F without values of all the Xi Jurisdiction and Nonce-Verification Axioms Symmetric Goodness Axiom 21
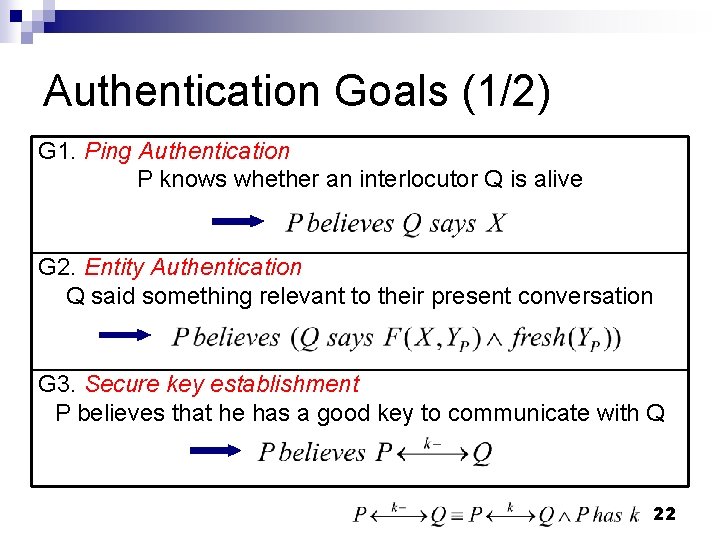
Authentication Goals (1/2) G 1. Ping Authentication P knows whether an interlocutor Q is alive G 2. Entity Authentication Q said something relevant to their present conversation G 3. Secure key establishment P believes that he has a good key to communicate with Q 22
Authentication Goals (2/2) G 4. Key freshness P believes a key to be fresh G 5. Mutual understanding of shared keys P can establish that Q has sent a key as an unconfirmed secret between the two of them G 6. Key confirmation P believes that Q proved to receive a previously unconfirmed secret key between the two of them 23

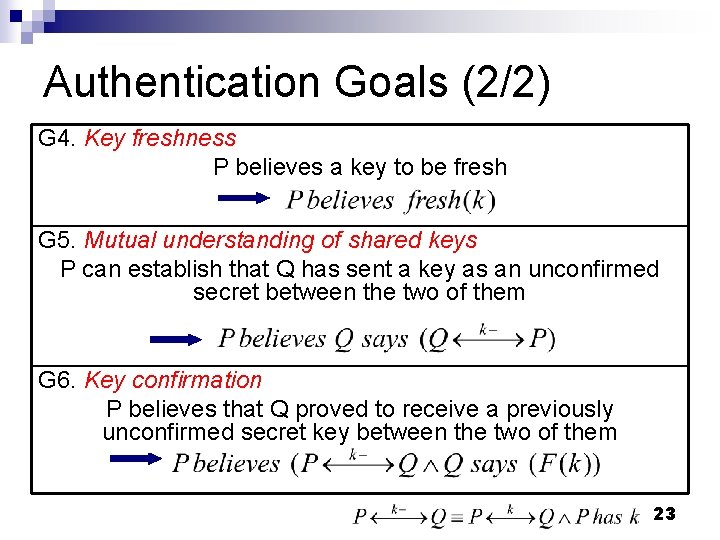
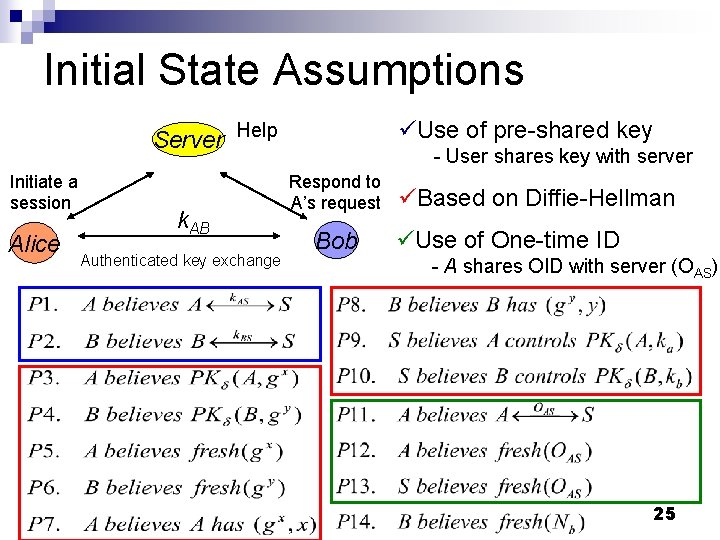
Procedure of Analysis by SVO Logic 1. Initial state assumptions n 2. Received message assumptions n 3. Write assumptions about each party’s comprehension of received messages Interpretation assumptions n 5. Write assumptions about messages each party receives in case that a protocol completes faithfully Comprehension assumptions n 4. Write assumptions about initial status (eg. Pre-shared key, PKI) Write assumptions about how each party interprets received messages Derivation n Derive the beliefs each party obtains by above assumptions, and check which authentication goals are derived 24
Initial State Assumptions üUse of pre-shared key Server Help Initiate a session Alice k. AB Authenticated key exchange - User shares key with server Respond to A’s request Bob üBased on Diffie-Hellman üUse of One-time ID - A shares OID with server (OAS) 25
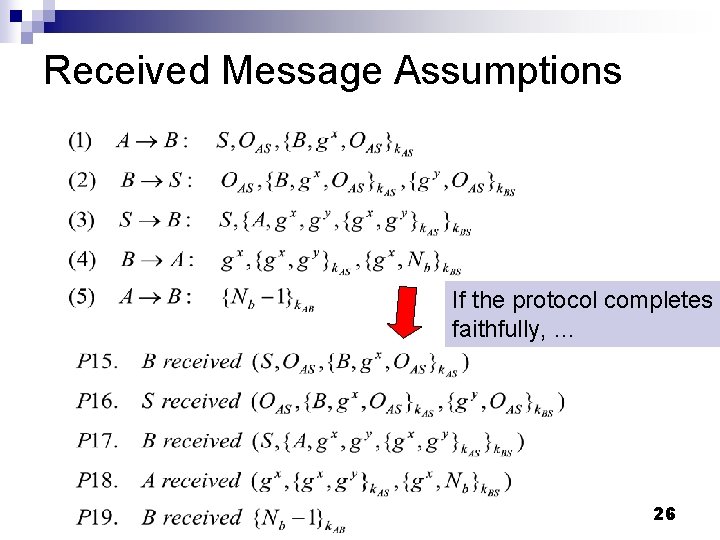
Received Message Assumptions If the protocol completes faithfully, … 26
Comprehension Assumptions Transform P 15 - P 19 Append “believes” and check unrecognized messages 27
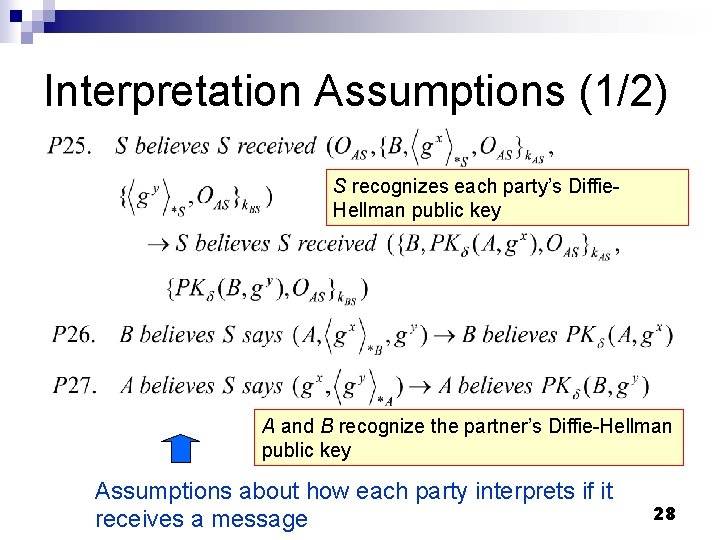
Interpretation Assumptions (1/2) S recognizes each party’s Diffie. Hellman public key A and B recognize the partner’s Diffie-Hellman public key Assumptions about how each party interprets if it receives a message 28
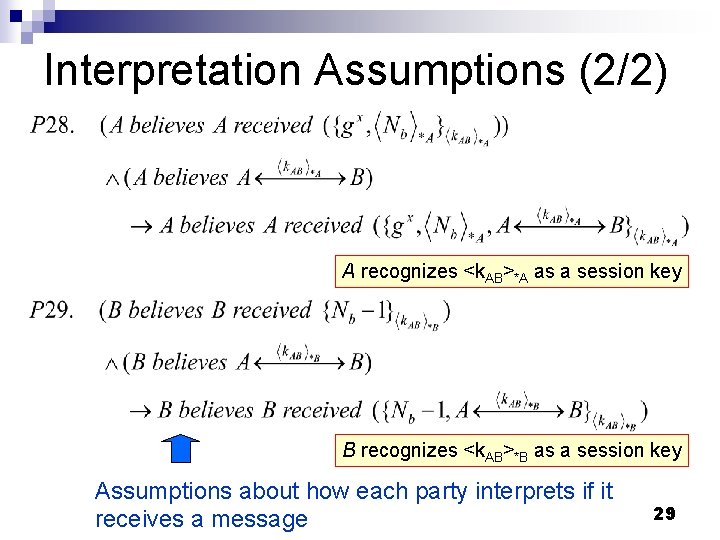
Interpretation Assumptions (2/2) A recognizes <k. AB>*A as a session key B recognizes <k. AB>*B as a session key Assumptions about how each party interprets if it receives a message 29
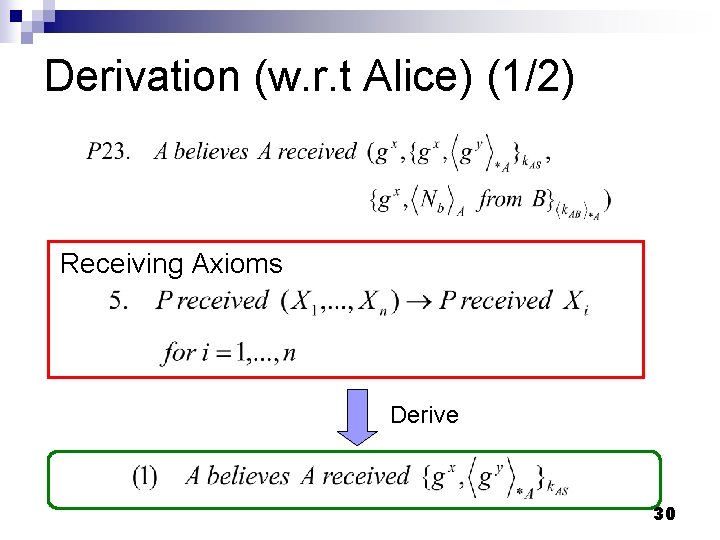
Derivation (w. r. t Alice) (1/2) Receiving Axioms Derive 30
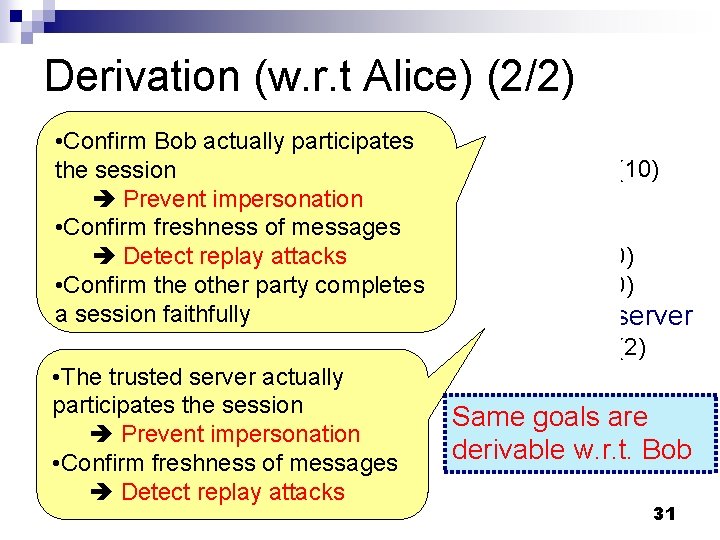
Derivation (w. r. t Alice) (2/2) • Confirm Bob actually participates the session Prevent impersonation • Confirm freshness of messages Detect replay attacks • Confirm the other party completes a session faithfully üFor Bob G 1, G 2 (10) G 3 (6) G 4 (7) G 5 (9, 10) G 6 (6, 10) üFor the server G 1, G 2 (2) • The trusted server actually participates the session Prevent impersonation • Confirm freshness of messages Detect replay attacks Same goals are derivable w. r. t. Bob 31

Derivation (w. r. t Server) • Confirm each party actually participates the session Prevent impersonation • Confirm freshness of messages Detect replay attacks üFor Alice G 1, G 2 (3) üFor Bob G 1, G 2 (5) Other authentication goals are unnecessary n. Because each user does not share a session key with the server 32
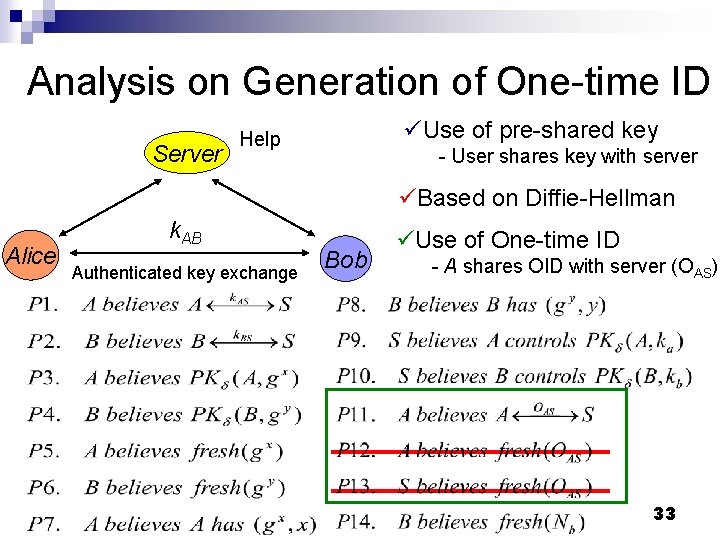
Analysis on Generation of One-time ID Server üUse of pre-shared key Help - User shares key with server üBased on Diffie-Hellman Alice k. AB Authenticated key exchange Bob üUse of One-time ID - A shares OID with server (OAS) 33
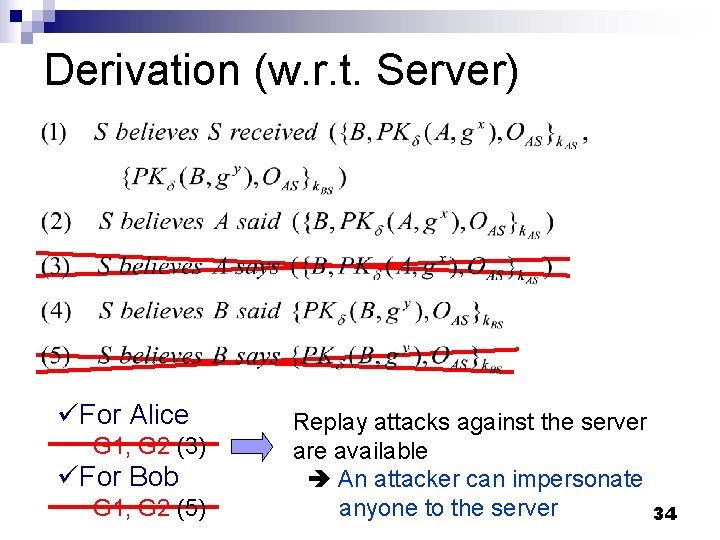
Derivation (w. r. t. Server) üFor Alice G 1, G 2 (3) üFor Bob G 1, G 2 (5) Replay attacks against the server are available An attacker can impersonate anyone to the server 34
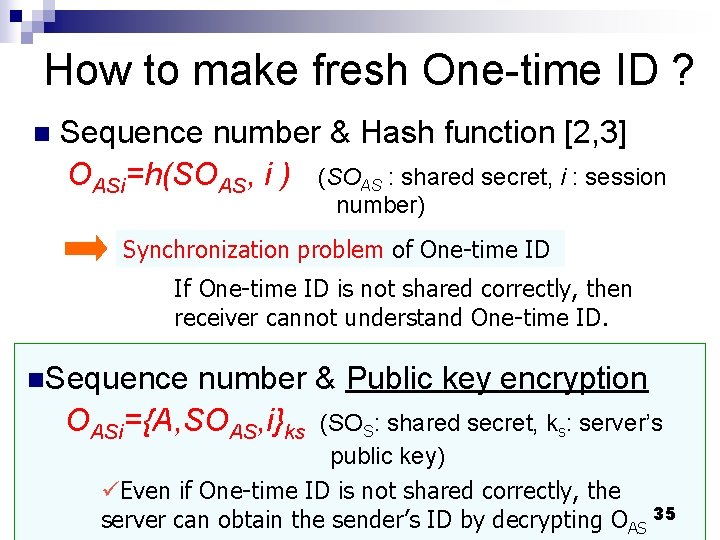
How to make fresh One-time ID ? n Sequence number & Hash function [2, 3] OASi=h(SOAS, i ) (SOAS : shared secret, i : session number) Synchronization problem of One-time ID If One-time ID is not shared correctly, then receiver cannot understand One-time ID. n. Sequence number & Public key encryption OASi={A, SOAS, i}ks (SOS: shared secret, ks: server’s public key) üEven if One-time ID is not shared correctly, the server can obtain the sender’s ID by decrypting OAS 35
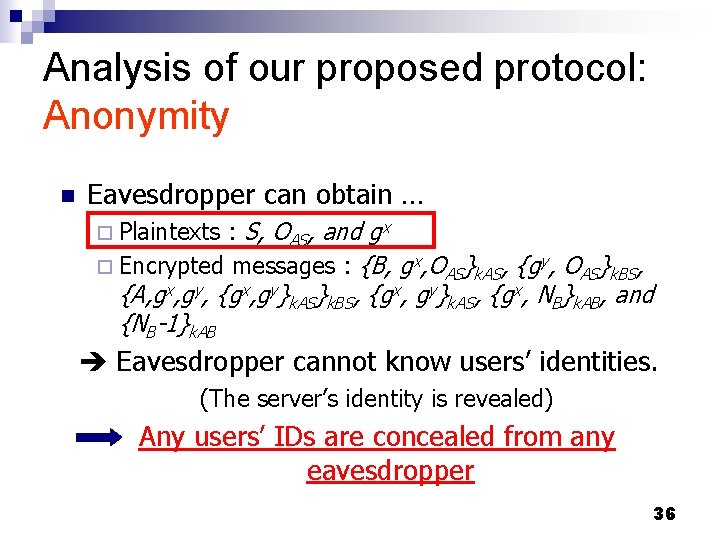
Analysis of our proposed protocol: Anonymity n Eavesdropper can obtain … : S, OAS, and gx ¨ Encrypted messages : {B, gx, OAS}k. AS, {gy, OAS}k. BS, ¨ Plaintexts {A, gx, gy, {gx, gy}k. AS}k. BS, {gx, gy}k. AS, {gx, NB}k. AB, and {NB-1}k. AB Eavesdropper cannot know users’ identities. (The server’s identity is revealed) Any users’ IDs are concealed from any eavesdropper 36
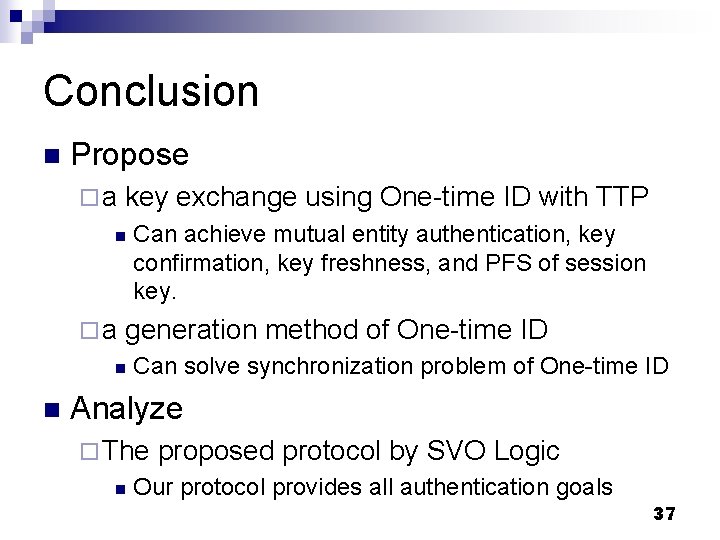
Conclusion n Propose ¨a key exchange using One-time ID with TTP n ¨a generation method of One-time ID n n Can achieve mutual entity authentication, key confirmation, key freshness, and PFS of session key. Can solve synchronization problem of One-time ID Analyze ¨ The n proposed protocol by SVO Logic Our protocol provides all authentication goals 37
- Slides: 37