Analyzing and Securing Social Networks Dr Bhavani Thuraisingham
Analyzing and Securing Social Networks Dr. Bhavani Thuraisingham The University of Texas at Dallas Introduction to the Course August 28 – December 4, 2015
Objective of the Unit l This unit provides an overview of the course. The course describes concepts, developments, challenges, and directions in analyzing social networks and securing social networks l Recommended Book for first part of the course: l Social Networks and the Semantic Web by Peter Mika, Springer 2007 l Focus for second part of the course - Selected papers on Analyzing and Securing Social Networks from the ACM/IEEE ASONAM Conferences 2009 -2015
Outline of the Unit l Outline of Course l Course Work l Course Rules l Contact l Appendix
Course Work l Two term papers; each worth 8 points l. Due: Oct 2, Nov 20 l Two exams each worth 24 points - Oct 16, Dec 11 l Programming project worth 16 points - Due: Dec 4 l Four homework assignments each worth 5 points l. Due: Sept 25, Oct 9, Oct 30, Nov 13 l Total 100 points
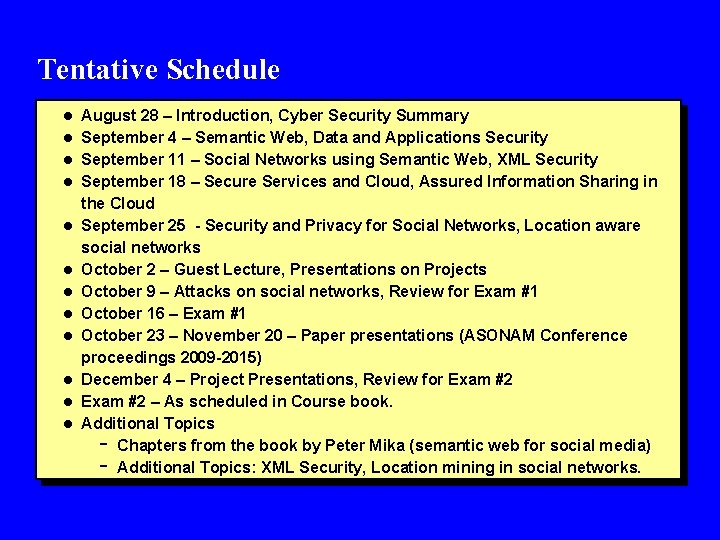
Tentative Schedule l August 28 – Introduction, Cyber Security Summary l September 4 – Semantic Web, Data and Applications Security l September 11 – Social Networks using Semantic Web, XML Security l September 18 – Secure Services and Cloud, Assured Information Sharing in l l l l the Cloud September 25 - Security and Privacy for Social Networks, Location aware social networks October 2 – Guest Lecture, Presentations on Projects October 9 – Attacks on social networks, Review for Exam #1 October 16 – Exam #1 October 23 – November 20 – Paper presentations (ASONAM Conference proceedings 2009 -2015) December 4 – Project Presentations, Review for Exam #2 – As scheduled in Course book. Additional Topics Chapters from the book by Peter Mika (semantic web for social media) Additional Topics: XML Security, Location mining in social networks. -
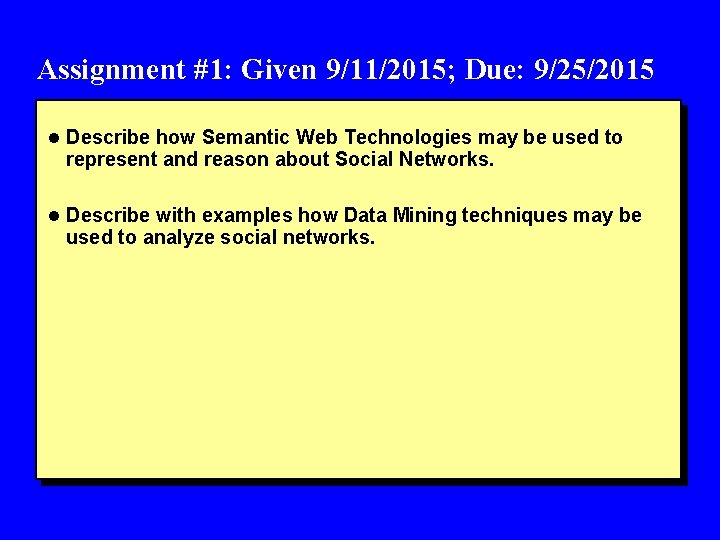
Assignment #1: Given 9/11/2015; Due: 9/25/2015 l Describe how Semantic Web Technologies may be used to represent and reason about Social Networks. l Describe with examples how Data Mining techniques may be used to analyze social networks.
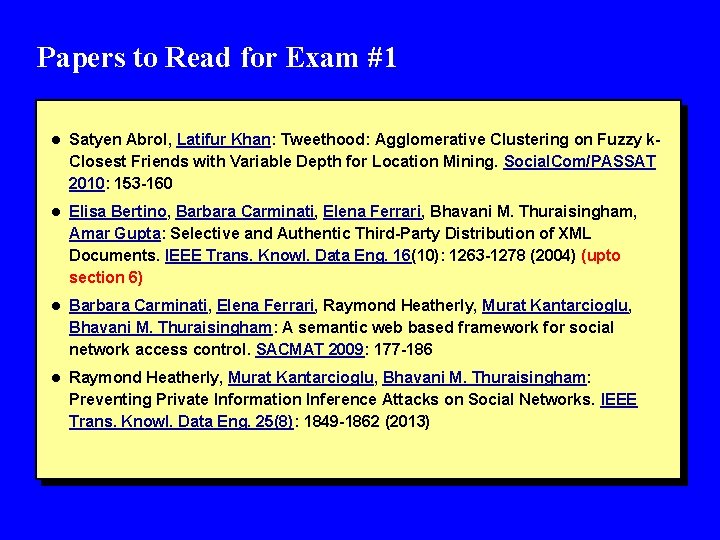
Papers to Read for Exam #1 l Satyen Abrol, Latifur Khan: Tweethood: Agglomerative Clustering on Fuzzy k- Closest Friends with Variable Depth for Location Mining. Social. Com/PASSAT 2010: 153 -160 l Elisa Bertino, Barbara Carminati, Elena Ferrari, Bhavani M. Thuraisingham, Amar Gupta: Selective and Authentic Third-Party Distribution of XML Documents. IEEE Trans. Knowl. Data Eng. 16(10): 1263 -1278 (2004) (upto section 6) l Barbara Carminati, Elena Ferrari, Raymond Heatherly, Murat Kantarcioglu, Bhavani M. Thuraisingham: A semantic web based framework for social network access control. SACMAT 2009: 177 -186 l Raymond Heatherly, Murat Kantarcioglu, Bhavani M. Thuraisingham: Preventing Private Information Inference Attacks on Social Networks. IEEE Trans. Knowl. Data Eng. 25(8): 1849 -1862 (2013)
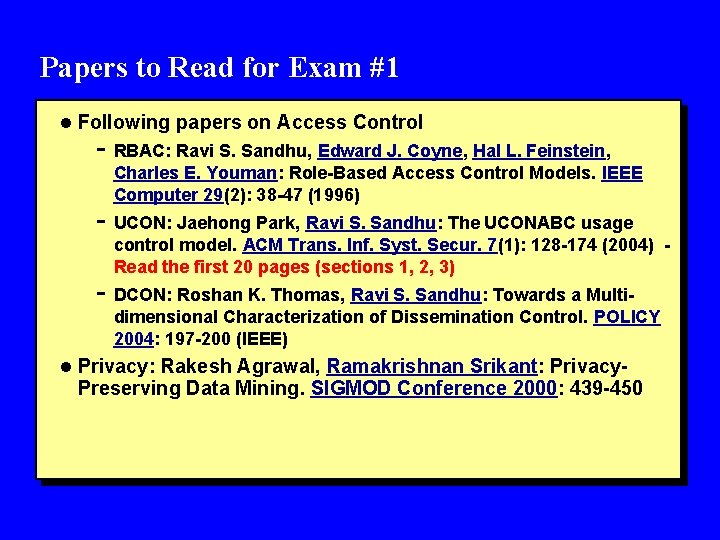
Papers to Read for Exam #1 l Following papers on Access Control - RBAC: Ravi S. Sandhu, Edward J. Coyne, Hal L. Feinstein, Charles E. Youman: Role-Based Access Control Models. IEEE Computer 29(2): 38 -47 (1996) - UCON: Jaehong Park, Ravi S. Sandhu: The UCONABC usage control model. ACM Trans. Inf. Syst. Secur. 7(1): 128 -174 (2004) Read the first 20 pages (sections 1, 2, 3) - DCON: Roshan K. Thomas, Ravi S. Sandhu: Towards a Multi- dimensional Characterization of Dissemination Control. POLICY 2004: 197 -200 (IEEE) l Privacy: Rakesh Agrawal, Ramakrishnan Srikant: Privacy- Preserving Data Mining. SIGMOD Conference 2000: 439 -450
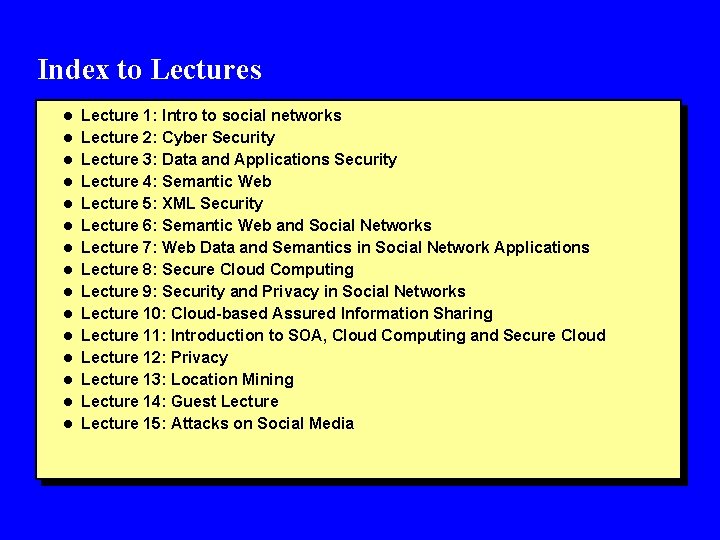
Index to Lectures l Lecture 1: Intro to social networks l Lecture 2: Cyber Security l Lecture 3: Data and Applications Security l Lecture 4: Semantic Web l Lecture 5: XML Security l Lecture 6: Semantic Web and Social Networks l Lecture 7: Web Data and Semantics in Social Network Applications l Lecture 8: Secure Cloud Computing l Lecture 9: Security and Privacy in Social Networks l Lecture 10: Cloud-based Assured Information Sharing l Lecture 11: Introduction to SOA, Cloud Computing and Secure Cloud l Lecture 12: Privacy l Lecture 13: Location Mining l Lecture 14: Guest Lecture l Lecture 15: Attacks on Social Media
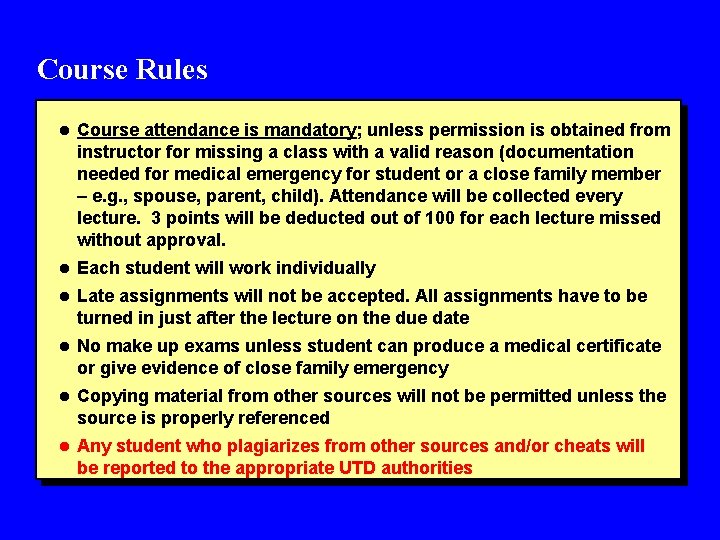
Course Rules l Course attendance is mandatory; unless permission is obtained from instructor for missing a class with a valid reason (documentation needed for medical emergency for student or a close family member – e. g. , spouse, parent, child). Attendance will be collected every lecture. 3 points will be deducted out of 100 for each lecture missed without approval. l Each student will work individually l Late assignments will not be accepted. All assignments have to be turned in just after the lecture on the due date l No make up exams unless student can produce a medical certificate or give evidence of close family emergency l Copying material from other sources will not be permitted unless the source is properly referenced l Any student who plagiarizes from other sources and/or cheats will be reported to the appropriate UTD authorities
Contact l For more information please contact - Dr. Bhavani Thuraisingham - Professor of Computer Science and - Director of Cyber Security Research Center Erik Jonsson School of Engineering and Computer Science EC 31, The University of Texas at Dallas Richardson, TX 75080 - Phone: 972 -883 -4738 - Fax: 972 -883 -2399 - Email: bhavani. thuraisingham@utdallas. edu - URL: http: //www. utdallas. edu/~bxt 043000/
Papers to Read for presentations IEEE/ACM Joint Conference Advances in Social Network Analysis and Mining, 2009 (ASONAM)
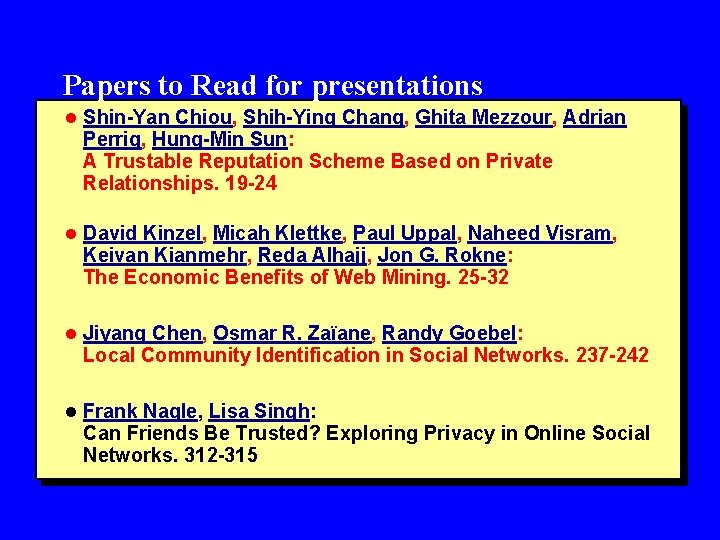
Papers to Read for presentations l Shin-Yan Chiou, Shih-Ying Chang, Ghita Mezzour, Adrian Perrig, Hung-Min Sun: A Trustable Reputation Scheme Based on Private Relationships. 19 -24 l David Kinzel, Micah Klettke, Paul Uppal, Naheed Visram, Keivan Kianmehr, Reda Alhajj, Jon G. Rokne: The Economic Benefits of Web Mining. 25 -32 l Jiyang Chen, Osmar R. Zaïane, Randy Goebel: Local Community Identification in Social Networks. 237 -242 l Frank Nagle, Lisa Singh: Can Friends Be Trusted? Exploring Privacy in Online Social Networks. 312 -315
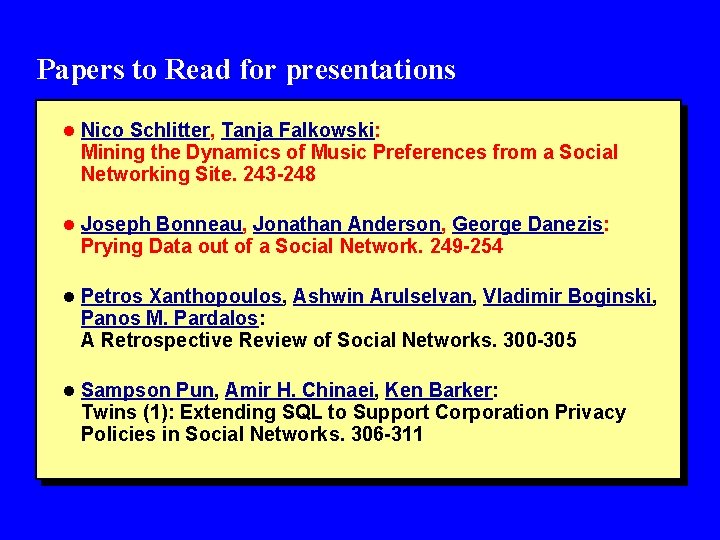
Papers to Read for presentations l Nico Schlitter, Tanja Falkowski: Mining the Dynamics of Music Preferences from a Social Networking Site. 243 -248 l Joseph Bonneau, Jonathan Anderson, George Danezis: Prying Data out of a Social Network. 249 -254 l Petros Xanthopoulos, Ashwin Arulselvan, Vladimir Boginski, Panos M. Pardalos: A Retrospective Review of Social Networks. 300 -305 l Sampson Pun, Amir H. Chinaei, Ken Barker: Twins (1): Extending SQL to Support Corporation Privacy Policies in Social Networks. 306 -311
Papers to Read for presentations IEEE/ACM Joint Conference Advances in Social Network Analysis and Mining, 2010 (ASONAM)
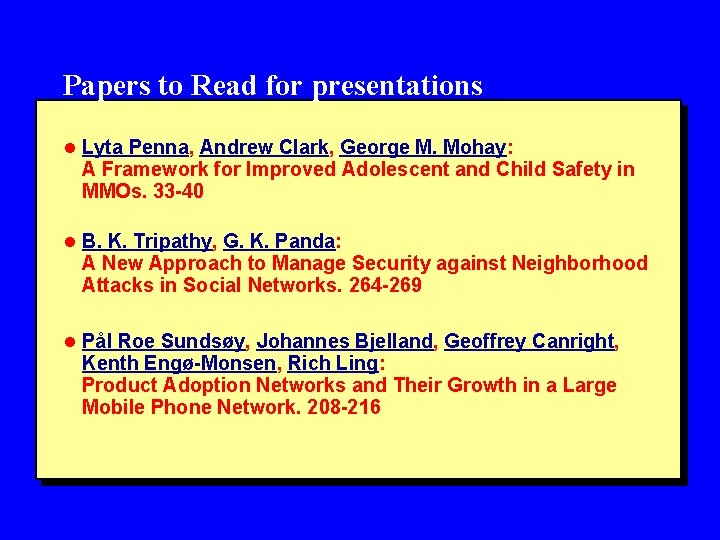
Papers to Read for presentations l Lyta Penna, Andrew Clark, George M. Mohay: A Framework for Improved Adolescent and Child Safety in MMOs. 33 -40 l B. K. Tripathy, G. K. Panda: A New Approach to Manage Security against Neighborhood Attacks in Social Networks. 264 -269 l Pål Roe Sundsøy, Johannes Bjelland, Geoffrey Canright, Kenth Engø-Monsen, Rich Ling: Product Adoption Networks and Their Growth in a Large Mobile Phone Network. 208 -216
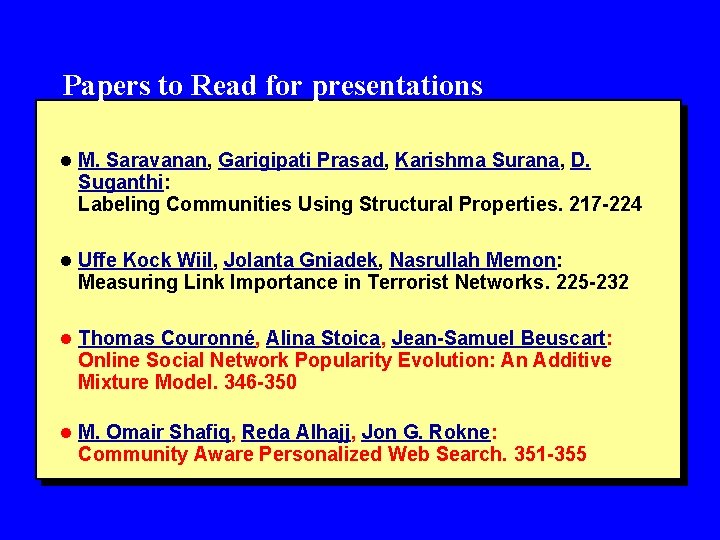
Papers to Read for presentations l M. Saravanan, Garigipati Prasad, Karishma Surana, D. Suganthi: Labeling Communities Using Structural Properties. 217 -224 l Uffe Kock Wiil, Jolanta Gniadek, Nasrullah Memon: Measuring Link Importance in Terrorist Networks. 225 -232 l Thomas Couronné, Alina Stoica, Jean-Samuel Beuscart: Online Social Network Popularity Evolution: An Additive Mixture Model. 346 -350 l M. Omair Shafiq, Reda Alhajj, Jon G. Rokne: Community Aware Personalized Web Search. 351 -355
Papers to Read for presentations IEEE/ACM Joint Conference Advances in Social Network Analysis and Mining, 2011 (ASONAM)
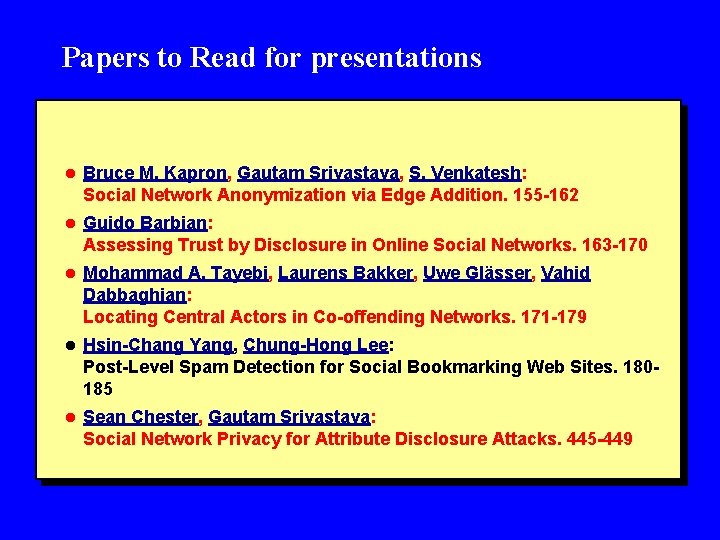
Papers to Read for presentations l Bruce M. Kapron, Gautam Srivastava, S. Venkatesh: Social Network Anonymization via Edge Addition. 155 -162 l Guido Barbian: Assessing Trust by Disclosure in Online Social Networks. 163 -170 l Mohammad A. Tayebi, Laurens Bakker, Uwe Glässer, Vahid Dabbaghian: Locating Central Actors in Co-offending Networks. 171 -179 l Hsin-Chang Yang, Chung-Hong Lee: Post-Level Spam Detection for Social Bookmarking Web Sites. 180185 l Sean Chester, Gautam Srivastava: Social Network Privacy for Attribute Disclosure Attacks. 445 -449
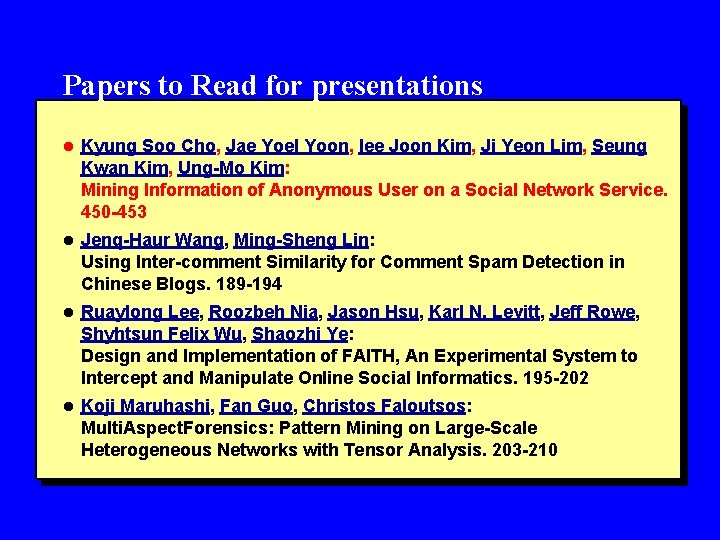
Papers to Read for presentations l Kyung Soo Cho, Jae Yoel Yoon, Iee Joon Kim, Ji Yeon Lim, Seung Kwan Kim, Ung-Mo Kim: Mining Information of Anonymous User on a Social Network Service. 450 -453 l Jenq-Haur Wang, Ming-Sheng Lin: Using Inter-comment Similarity for Comment Spam Detection in Chinese Blogs. 189 -194 l Ruaylong Lee, Roozbeh Nia, Jason Hsu, Karl N. Levitt, Jeff Rowe, Shyhtsun Felix Wu, Shaozhi Ye: Design and Implementation of FAITH, An Experimental System to Intercept and Manipulate Online Social Informatics. 195 -202 l Koji Maruhashi, Fan Guo, Christos Faloutsos: Multi. Aspect. Forensics: Pattern Mining on Large-Scale Heterogeneous Networks with Tensor Analysis. 203 -210
Papers to Read for presentations IEEE/ACM Joint Conference Advances in Social Network Analysis and Mining, 2012 (ASONAM)
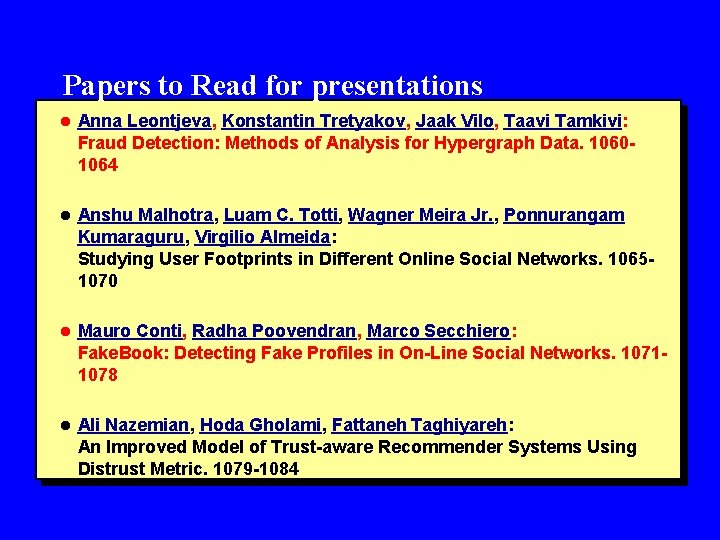
Papers to Read for presentations l Anna Leontjeva, Konstantin Tretyakov, Jaak Vilo, Taavi Tamkivi: Fraud Detection: Methods of Analysis for Hypergraph Data. 10601064 l Anshu Malhotra, Luam C. Totti, Wagner Meira Jr. , Ponnurangam Kumaraguru, Virgilio Almeida: Studying User Footprints in Different Online Social Networks. 10651070 l Mauro Conti, Radha Poovendran, Marco Secchiero: Fake. Book: Detecting Fake Profiles in On-Line Social Networks. 10711078 l Ali Nazemian, Hoda Gholami, Fattaneh Taghiyareh: An Improved Model of Trust-aware Recommender Systems Using Distrust Metric. 1079 -1084
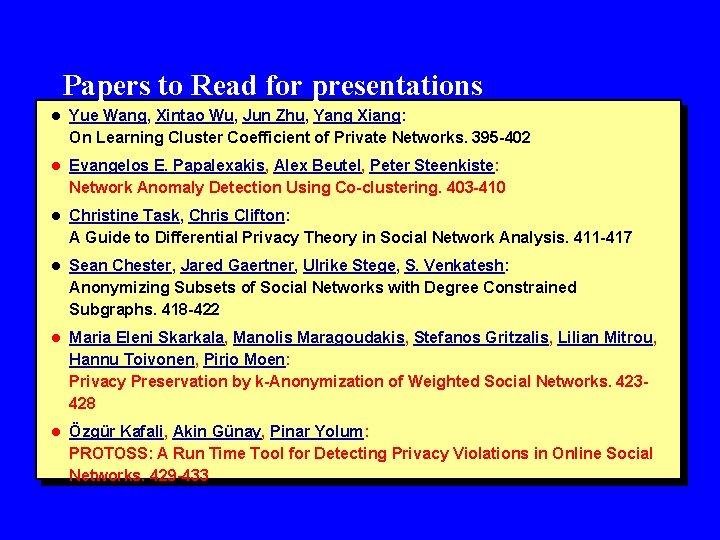
Papers to Read for presentations l Yue Wang, Xintao Wu, Jun Zhu, Yang Xiang: On Learning Cluster Coefficient of Private Networks. 395 -402 l Evangelos E. Papalexakis, Alex Beutel, Peter Steenkiste: Network Anomaly Detection Using Co-clustering. 403 -410 l Christine Task, Chris Clifton: A Guide to Differential Privacy Theory in Social Network Analysis. 411 -417 l Sean Chester, Jared Gaertner, Ulrike Stege, S. Venkatesh: Anonymizing Subsets of Social Networks with Degree Constrained Subgraphs. 418 -422 l Maria Eleni Skarkala, Manolis Maragoudakis, Stefanos Gritzalis, Lilian Mitrou, Hannu Toivonen, Pirjo Moen: Privacy Preservation by k-Anonymization of Weighted Social Networks. 423428 l Özgür Kafali, Akin Günay, Pinar Yolum: PROTOSS: A Run Time Tool for Detecting Privacy Violations in Online Social Networks. 429 -433
Papers to Read for presentations IEEE/ACM Joint Conference Advances in Social Network Analysis and Mining, 2015 (ASONAM)
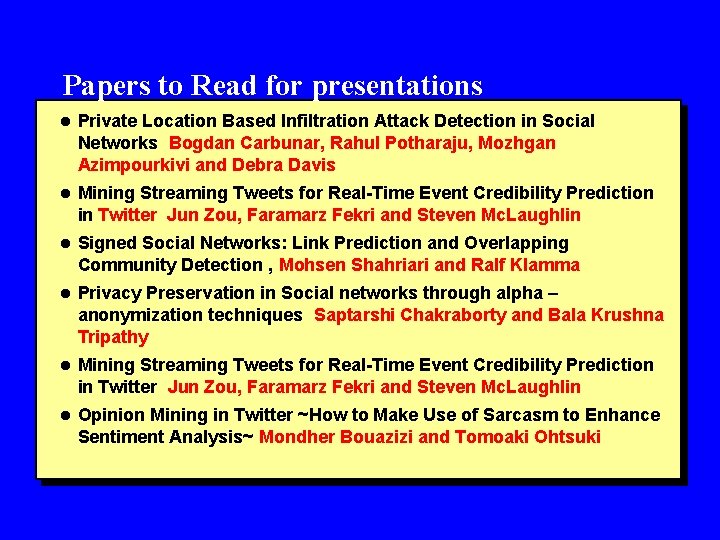
Papers to Read for presentations l Private Location Based Infiltration Attack Detection in Social Networks Bogdan Carbunar, Rahul Potharaju, Mozhgan Azimpourkivi and Debra Davis l Mining Streaming Tweets for Real-Time Event Credibility Prediction in Twitter Jun Zou, Faramarz Fekri and Steven Mc. Laughlin l Signed Social Networks: Link Prediction and Overlapping Community Detection , Mohsen Shahriari and Ralf Klamma l Privacy Preservation in Social networks through alpha – anonymization techniques Saptarshi Chakraborty and Bala Krushna Tripathy l Mining Streaming Tweets for Real-Time Event Credibility Prediction in Twitter Jun Zou, Faramarz Fekri and Steven Mc. Laughlin l Opinion Mining in Twitter ~How to Make Use of Sarcasm to Enhance Sentiment Analysis~ Mondher Bouazizi and Tomoaki Ohtsuki
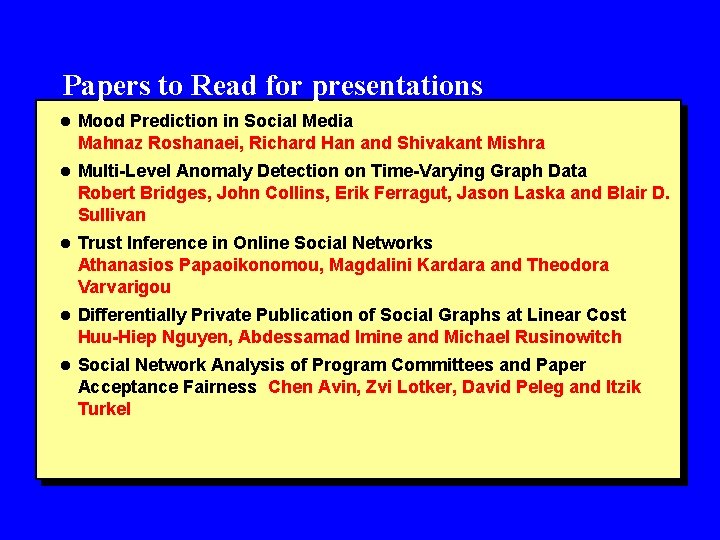
Papers to Read for presentations l Mood Prediction in Social Media Mahnaz Roshanaei, Richard Han and Shivakant Mishra l Multi-Level Anomaly Detection on Time-Varying Graph Data Robert Bridges, John Collins, Erik Ferragut, Jason Laska and Blair D. Sullivan l Trust Inference in Online Social Networks Athanasios Papaoikonomou, Magdalini Kardara and Theodora Varvarigou l Differentially Private Publication of Social Graphs at Linear Cost Huu-Hiep Nguyen, Abdessamad Imine and Michael Rusinowitch l Social Network Analysis of Program Committees and Paper Acceptance Fairness Chen Avin, Zvi Lotker, David Peleg and Itzik Turkel
Papers to Read for presentations IEEE/ACM Joint Conference Advances in Social Network Analysis and Mining, 2014 (ASONAM)
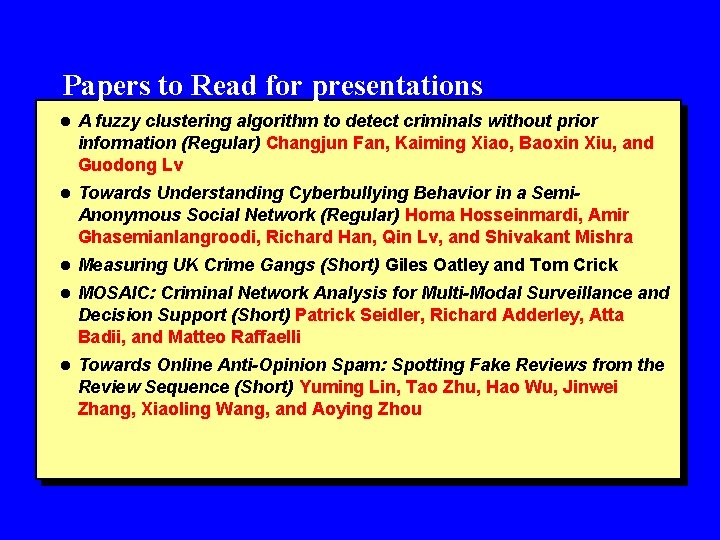
Papers to Read for presentations l A fuzzy clustering algorithm to detect criminals without prior information (Regular) Changjun Fan, Kaiming Xiao, Baoxin Xiu, and Guodong Lv l Towards Understanding Cyberbullying Behavior in a Semi- Anonymous Social Network (Regular) Homa Hosseinmardi, Amir Ghasemianlangroodi, Richard Han, Qin Lv, and Shivakant Mishra l Measuring UK Crime Gangs (Short) Giles Oatley and Tom Crick l MOSAIC: Criminal Network Analysis for Multi-Modal Surveillance and Decision Support (Short) Patrick Seidler, Richard Adderley, Atta Badii, and Matteo Raffaelli l Towards Online Anti-Opinion Spam: Spotting Fake Reviews from the Review Sequence (Short) Yuming Lin, Tao Zhu, Hao Wu, Jinwei Zhang, Xiaoling Wang, and Aoying Zhou
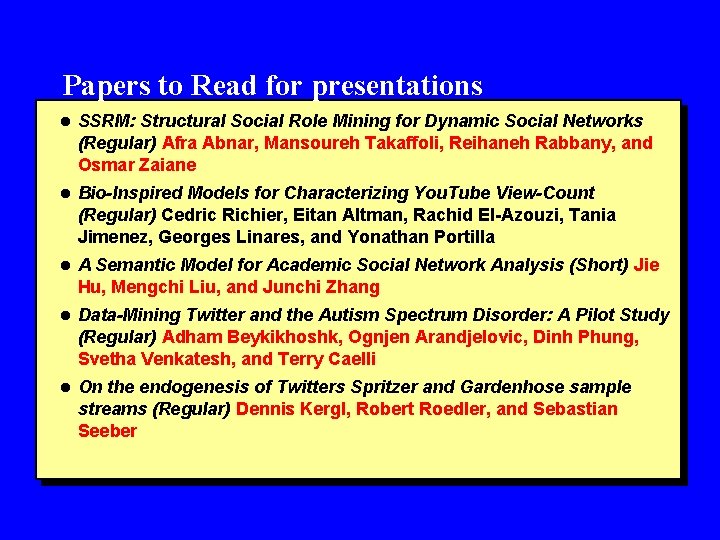
Papers to Read for presentations l SSRM: Structural Social Role Mining for Dynamic Social Networks (Regular) Afra Abnar, Mansoureh Takaffoli, Reihaneh Rabbany, and Osmar Zaiane l Bio-Inspired Models for Characterizing You. Tube View-Count (Regular) Cedric Richier, Eitan Altman, Rachid El-Azouzi, Tania Jimenez, Georges Linares, and Yonathan Portilla l A Semantic Model for Academic Social Network Analysis (Short) Jie Hu, Mengchi Liu, and Junchi Zhang l Data-Mining Twitter and the Autism Spectrum Disorder: A Pilot Study (Regular) Adham Beykikhoshk, Ognjen Arandjelovic, Dinh Phung, Svetha Venkatesh, and Terry Caelli l On the endogenesis of Twitters Spritzer and Gardenhose sample streams (Regular) Dennis Kergl, Robert Roedler, and Sebastian Seeber
Papers to Read for presentations IEEE/ACM Joint Conference Advances in Social Network Analysis and Mining, 2013 (ASONAM)
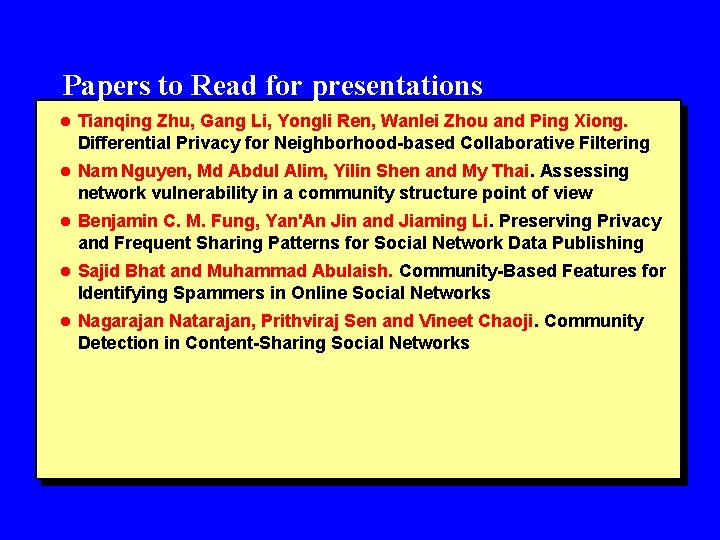
Papers to Read for presentations l Tianqing Zhu, Gang Li, Yongli Ren, Wanlei Zhou and Ping Xiong. Differential Privacy for Neighborhood-based Collaborative Filtering l Nam Nguyen, Md Abdul Alim, Yilin Shen and My Thai. Assessing network vulnerability in a community structure point of view l Benjamin C. M. Fung, Yan'An Jin and Jiaming Li. Preserving Privacy and Frequent Sharing Patterns for Social Network Data Publishing l Sajid Bhat and Muhammad Abulaish. Community-Based Features for Identifying Spammers in Online Social Networks l Nagarajan Natarajan, Prithviraj Sen and Vineet Chaoji. Community Detection in Content-Sharing Social Networks
- Slides: 31