Subject Network Security Dr Qazi Ejaz Ali Assistant
Subject: Network Security Dr. Qazi Ejaz Ali Assistant Professor Department of computer Science University of Peshawar 1

Network Security 2
Course outlines • • • Introduction of Network Security, Introduction to Cryptography, Cipher , Key Plain text, Cipher Text, Encipher , Decipher/Decryption, Services of Cryptography, Confidentiality, integrity, authentication, non-repudiation, access control, availability. Ceaser cipher, Information Security, Examples Types of Cryptography, Secret Key Cryptography, Public Key Cryptography, Message Digest/Hash Algorithm Famous Algorithm of Secret Key Cryptography, Data Encryption standard Initial Permutation in DES, Final Permutation in DES, Example DES round for Encryption, Des round for Decryption, Per-round key generation Using Secret key cryptography to encrypt messages larger than 64 -bits, Electronic Code Book 3 •
Course Outlines (continue) • • • • Cipher block Chaining, introduction of IV in Cipher block chaining Output Feed back Mode, Cipher Feed back Mode, Introduction to International Data Encryption Algorithm (IDEA) Multiple Encryption through DES i. e. Triple DES Introduction to Advanced Encryption Standard (AES) Modular Arithmetic’s Public Key Cryptography, Congruence, Totient Function Types of Public Key Cryptography, RSA Algorithm Examples of RSA, how to encrypt and decrypt messages. 4
• • • • • Deffie-Hellman Algorithm, Step in Deffie-Hellman Algorithm for PKI Hash Algorithm/Message Digest, Message Digest-2. Message Digest 4, Message Digest 5, Secure Hash Standard Digital Signature, Digital Signature Generation and Verification Scheme Authentication, Types of Authentication, Password based, Address based and Cryptographic based Authentication. Trusted Intermediaries, Key Distribution Center/Key management Center. Digital Certificate, Certifying Authority, Certificate Revocation List. Firewall, Types of Firewalls Kerberos, Simple authentication, AS, TGS, V/Server. Kerberos protocol Working process Privacy Enhanced Mail Digital Watermarking Viruses, Worms, Trojan horse, Denial of Service Attack Hyper text Transfer Protocol Secure, HTTP, SSL Attacks against Internet Protocol, IP Spoofing, IP Session Hijacking Not limited to the above , Many more Research Papers 5
Course outlines (continue) • Recommended Books: • Network Security, Charlie Kaufman, Radia Perlman and Mike Speciner (Pub. Prentice Hall). • Network Security Essentials, William Stallings, 3 rd Edition. • Fundamentals of Network Security, Eric Maiwald, Edition 2007. 6
Network Security • Crptography • Why is there need of security 6
Attacks, Services and Mechanisms • Security Attack: Any action that compromises the security of information. • Security Mechanism: A mechanism that is designed to detect, prevent, or recover from a security attack. • Security Service: A service that enhances the security of data processing systems and information transfers. A security service makes use of one or more security mechanisms. 8
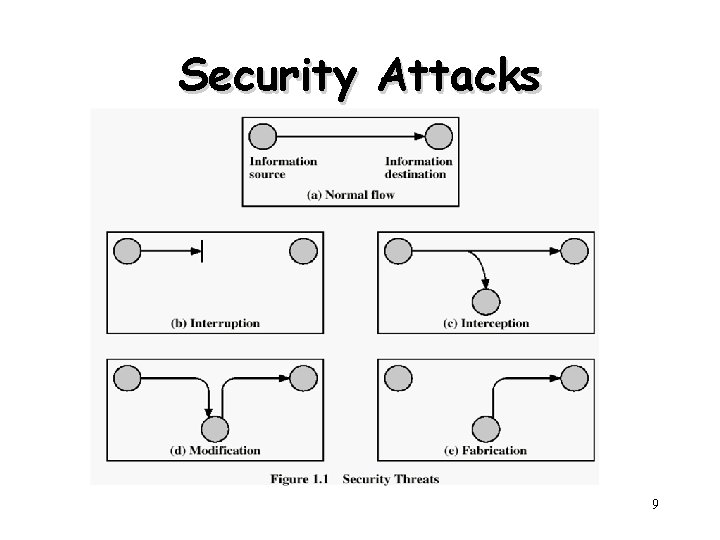
Security Attacks 9
Security Attacks • Interruption: This is an attack on availability • Interception: This is an attack on confidentiality • Modfication: This is an attack on integtrity • Fabrication: This is an attack on authenticity 10

Security Goals Confidentiality Integrity Avaliability 11
Security Services • Confidentiality (privacy) • Authentication (who created or sent the data) • Integrity (has not been altered) • Non-repudiation (the order is final) • Access control (prevent misuse of resources) • Availability (permanence, non-erasure) – Denial of Service Attacks – Virus that deletes files 12
Caesar Cipher 13
- Slides: 13