Shibboleth and IIS Integration Tips Tricks Alternatives Scott

Shibboleth and IIS Integration Tips, Tricks, Alternatives Scott Cantor OSU / Shibboleth Consortium
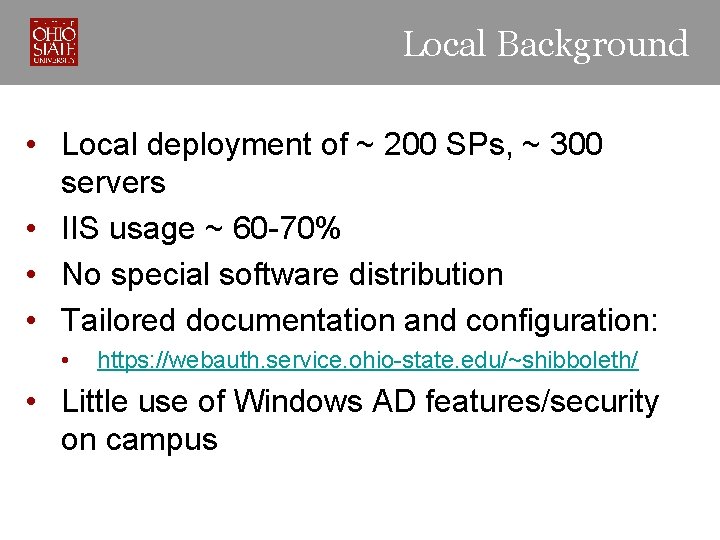
Local Background • Local deployment of ~ 200 SPs, ~ 300 servers • IIS usage ~ 60 -70% • No special software distribution • Tailored documentation and configuration: • https: //webauth. service. ohio-state. edu/~shibboleth/ • Little use of Windows AD features/security on campus
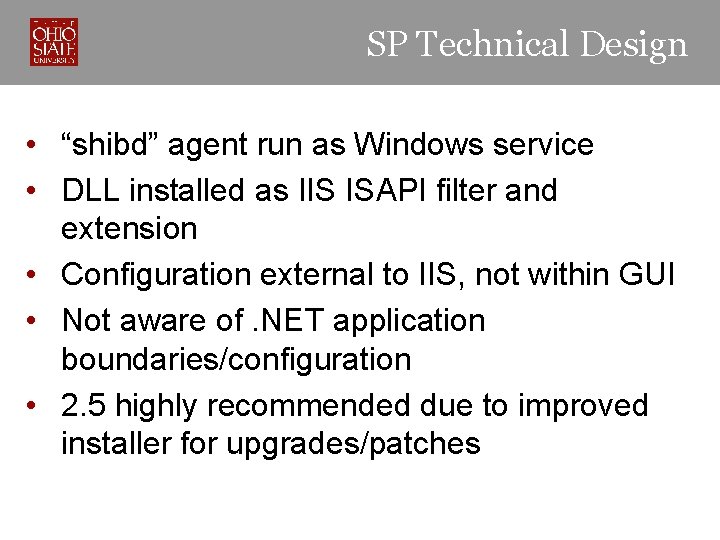
SP Technical Design • “shibd” agent run as Windows service • DLL installed as IIS ISAPI filter and extension • Configuration external to IIS, not within GUI • Not aware of. NET application boundaries/configuration • 2. 5 highly recommended due to improved installer for upgrades/patches
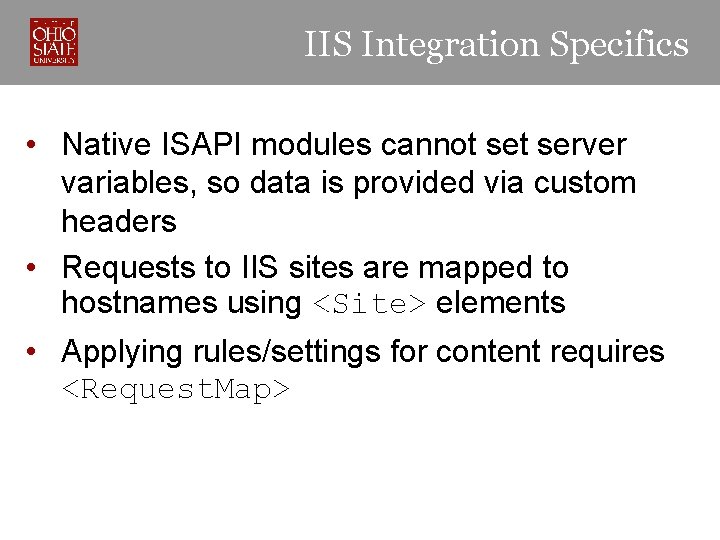
IIS Integration Specifics • Native ISAPI modules cannot server variables, so data is provided via custom headers • Requests to IIS sites are mapped to hostnames using <Site> elements • Applying rules/settings for content requires <Request. Map>
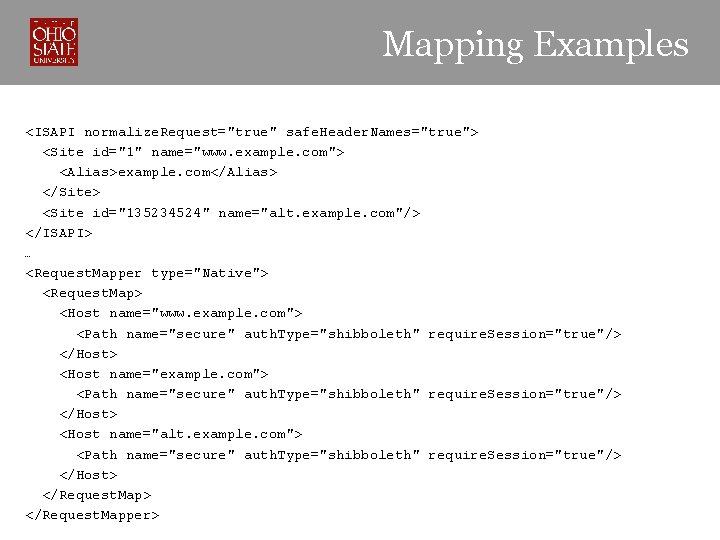
Mapping Examples <ISAPI normalize. Request="true" safe. Header. Names="true"> <Site id="1" name="www. example. com"> <Alias>example. com</Alias> </Site> <Site id="135234524" name="alt. example. com"/> </ISAPI> … <Request. Mapper type="Native"> <Request. Map> <Host name="www. example. com"> <Path name="secure" auth. Type="shibboleth" require. Session="true"/> </Host> <Host name="alt. example. com"> <Path name="secure" auth. Type="shibboleth" require. Session="true"/> </Host> </Request. Mapper>
Gotchas: File Permissions • All accounts used by IIS processes need read access to most files in the Shibboleth installation • Varies widely across IIS versions • No access to private key(s) required • Write access to log directory only
Gotchas: IIS Inheritance • IIS filters globally or per-site, extension script mappings globally, site-level, directory/filelevel • Installer tries to install filter globally, script/handler mapping at root of each site • Systems vary in overriding these settings at lower layers • GUI is buggy and does not accurately reflect when settings are overridden or missing
Gotchas: WOW 64 App. Pools • 2. 5 releases install 32 -bit and 64 -bit binaries, but only one can be active • IIS App. Pools on 64 -bit OS can be configured as 32 -bit: • Choose “Run as 32 -bit” during install • Run Set. Service 32. bat after install and manually edit IIS filter/handler mappings • Cannot run both types of App. Pool at once
Gotchas: Headers • The “safe. Header. Names” option removes punctuation from attribute names to avoid a. NET API vulnerability, but still advisable to avoid: • • System. Web. Http. Request. Server. Variables Request("HTTP_VARIABLE_NAME") • Setting REMOTE_USER not supported, sets HTTP_REMOTEUSER header • Avoid unless you need feature that picks first value from a set of possible attributes
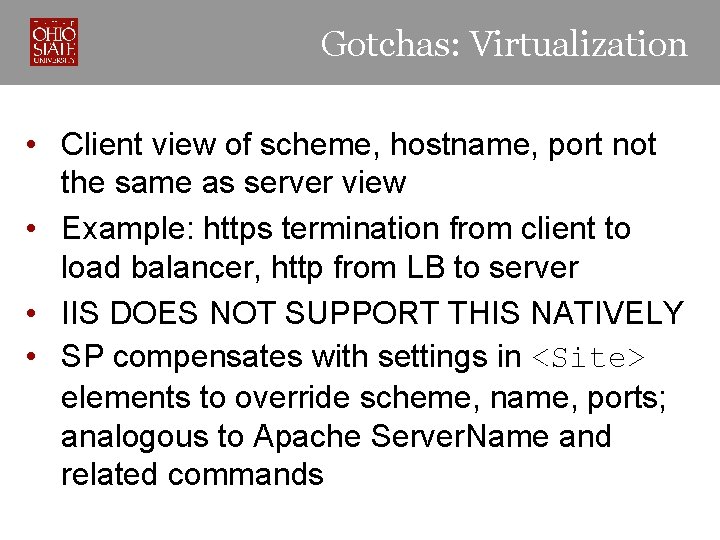
Gotchas: Virtualization • Client view of scheme, hostname, port not the same as server view • Example: https termination from client to load balancer, http from LB to server • IIS DOES NOT SUPPORT THIS NATIVELY • SP compensates with settings in <Site> elements to override scheme, name, ports; analogous to Apache Server. Name and related commands
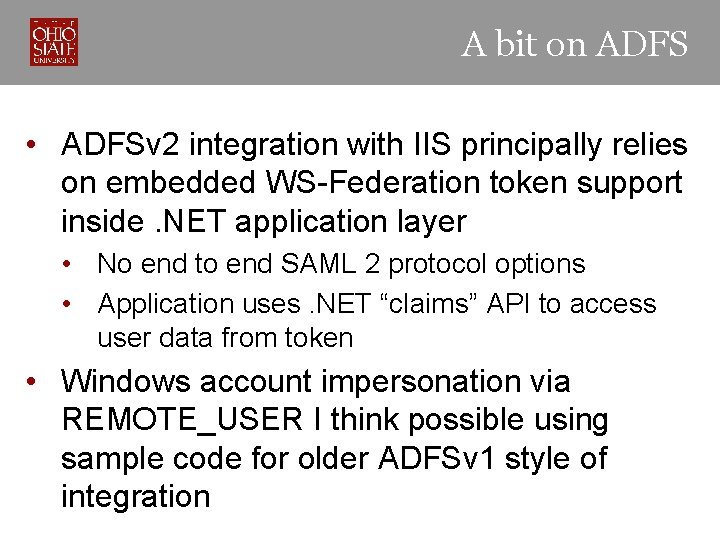
A bit on ADFS • ADFSv 2 integration with IIS principally relies on embedded WS-Federation token support inside. NET application layer • No end to end SAML 2 protocol options • Application uses. NET “claims” API to access user data from token • Windows account impersonation via REMOTE_USER I think possible using sample code for older ADFSv 1 style of integration
- Slides: 11