SECURITY PRINCIPLES Isolate and Containerize Trust Software by
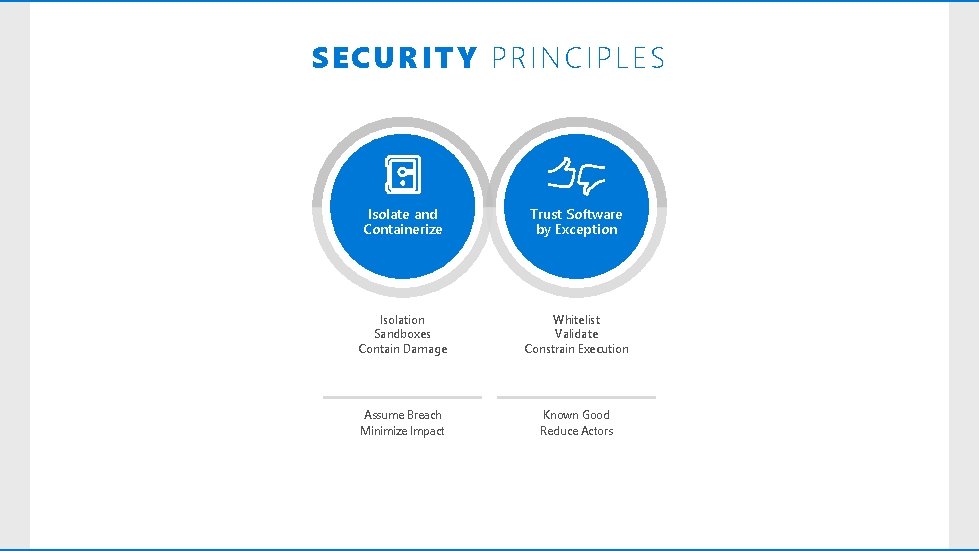
SECURITY PRINCIPLES Isolate and Containerize Trust Software by Exception Isolation Sandboxes Contain Damage Whitelist Validate Constrain Execution Assume Breach Minimize Impact Known Good Reduce Actors

ISOLATE AND CONTAINERIZE SAP Outlook Edge Visual Studio Word
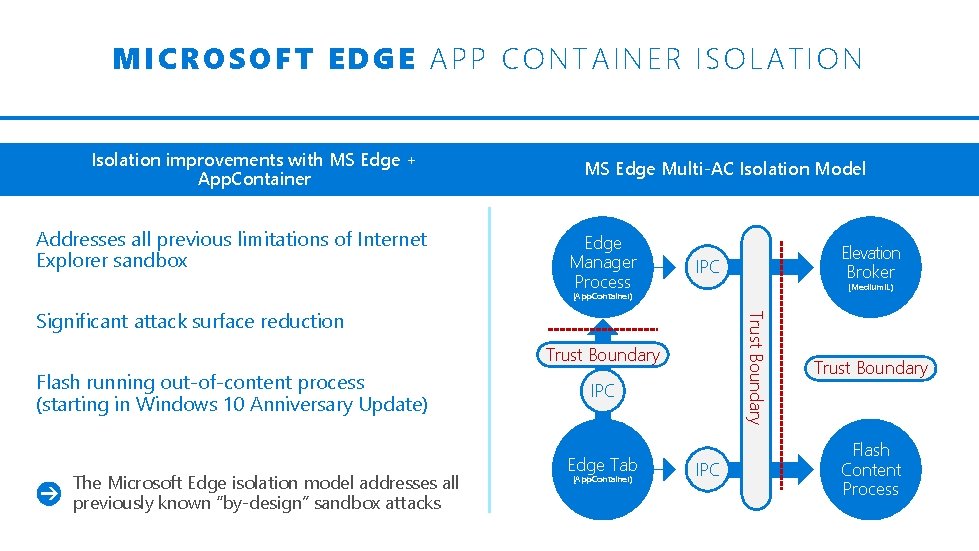
M ICROSOFT E DGE APP CONTAINER ISOLATION Isolation improvements with MS Edge + App. Container Addresses all previous limitations of Internet Explorer sandbox MS Edge Multi-AC Isolation Model Edge Manager Process Elevation Broker IPC (Medium. IL) (App. Container) Trust Boundary Significant attack surface reduction Trust Boundary Flash running out-of-content process (starting in Windows 10 Anniversary Update) The Microsoft Edge isolation model addresses all previously known “by-design” sandbox attacks IPC Edge Tab (App. Container) IPC Trust Boundary Flash Content Process
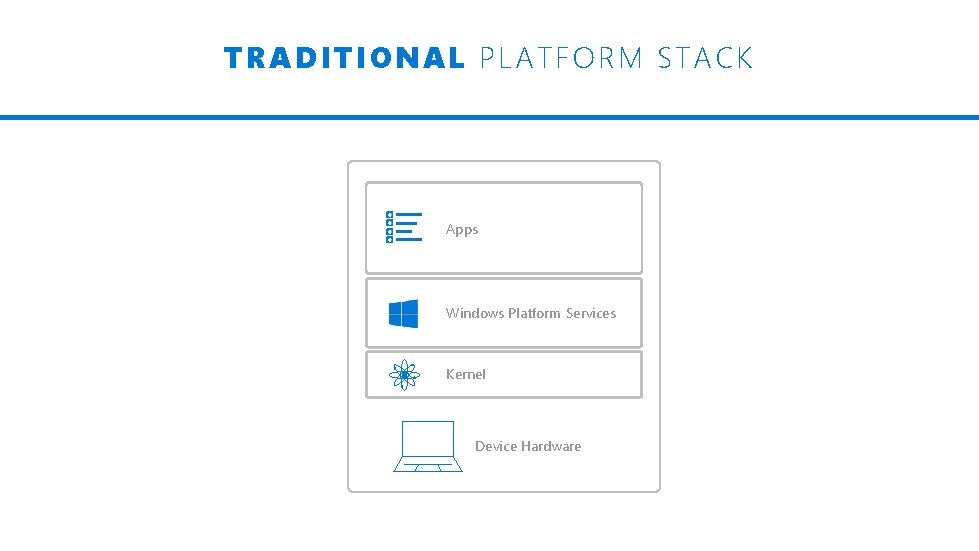
TRADITIONAL PL ATFORM STACK Apps Windows Platform Services Kernel Device Hardware
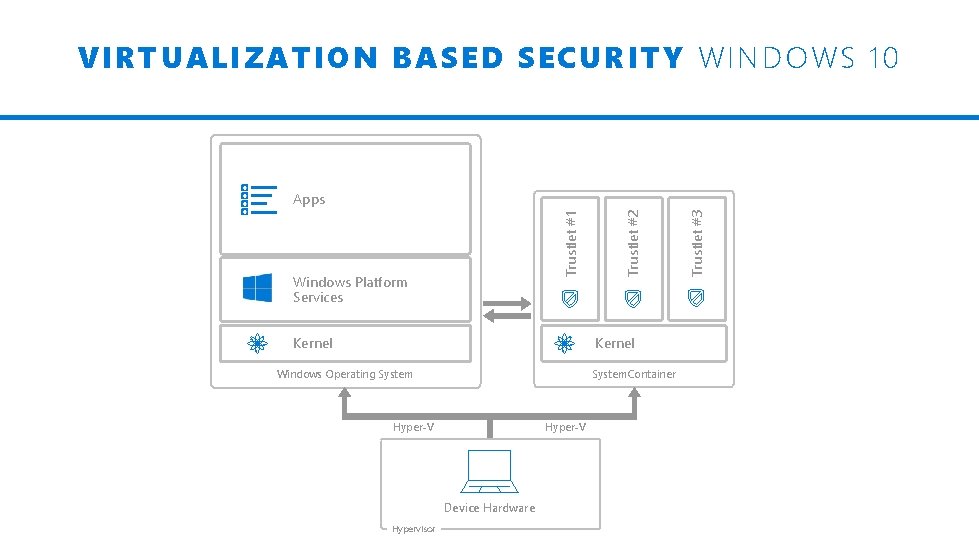
VIRTUALIZATION BASED SE CURITY WINDOWS 10 Kernel Windows Operating System. Container Hyper-V Device Hardware Hypervisor Trustlet #3 Windows Platform Services Trustlet #2 Trustlet #1 Apps


TODAY ’S CH ALLENGE: APPS
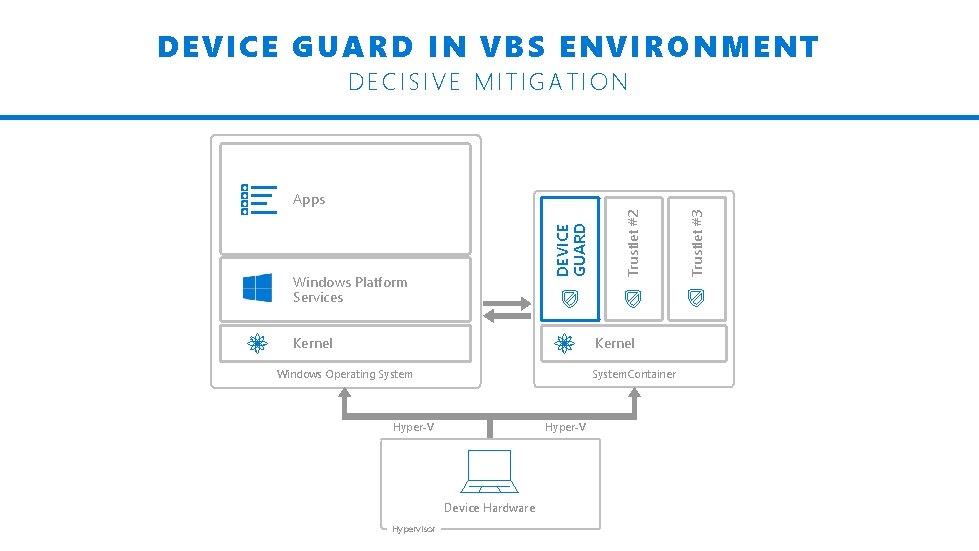
DEVICE GUARD IN VBS ENVIRONMENT DECISIVE MITIGATION Kernel Windows Operating System. Container Hyper-V Device Hardware Hypervisor Trustlet #3 Windows Platform Services Trustlet #2 DEVICE GUARD Apps
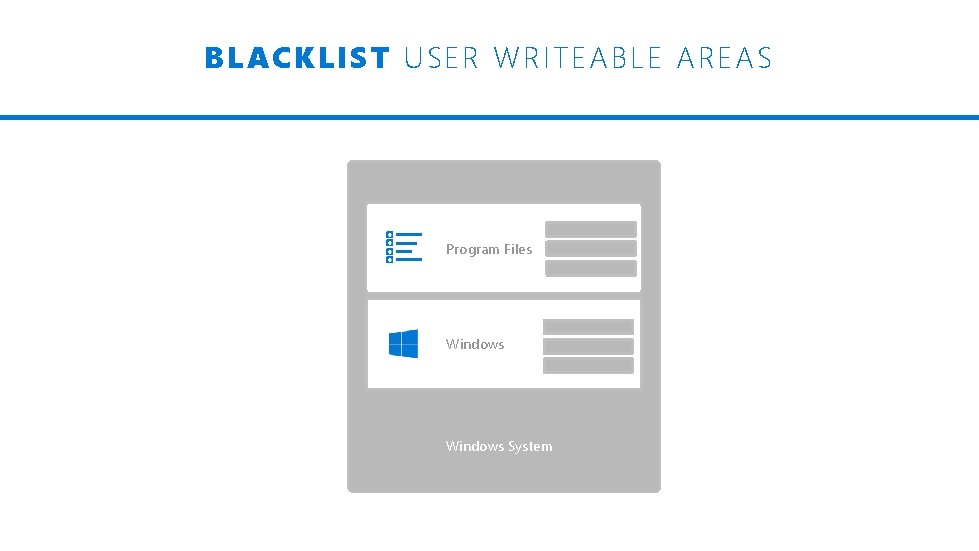
BLACKLIST USER WRITE ABLE AREAS Program Files Windows System
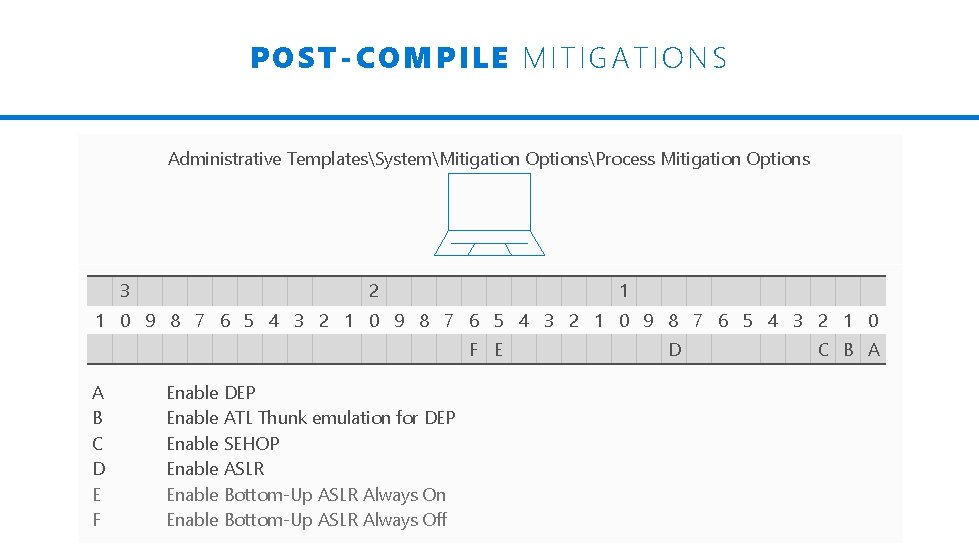
P OST-COMPILE MITIGATIONS Administrative TemplatesSystemMitigation OptionsProcess Mitigation Options 3 2 1 1 0 9 8 7 6 5 4 3 2 1 0 F E A B C D E F Enable DEP Enable ATL Thunk emulation for DEP Enable SEHOP Enable ASLR Enable Bottom-Up ASLR Always On Enable Bottom-Up ASLR Always Off D C B A
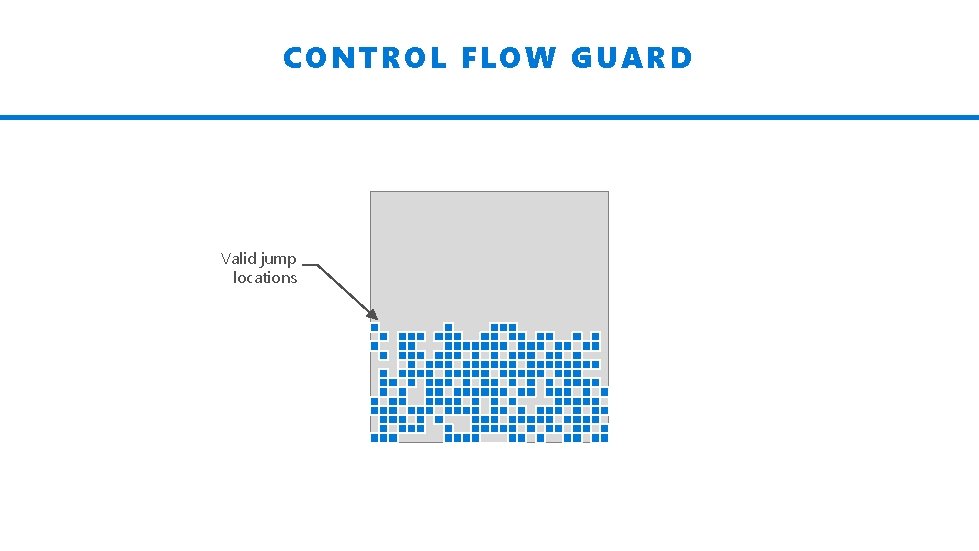
CONTROL FLOW GUARD Valid jump locations Y YY
- Slides: 14