Security in mobile adhoc networks using soft encryption
Security in mobile ad-hoc networks using soft encryption and trust-based multi-path routing Authors: Prayag Narula, Sanjay Kumar Dhurandher, Sudip Misra, and Isaac Woungang. Sources: Computer Communications, article in press. Reporter: Chun-Ta Li (李俊達)
Outline o o o Motivation Proposed routing strategy Comments 2
Motivation o Message security using trust-based multi-path routing in MANETs n Multi-path routing (on-demand routing) o n Soft encryption o o n divide the message into different parts eliminate the need of Key Distribution Center and key transfer using the message itself for encryption Trustworthiness o trusted node is allowed to feature in more paths
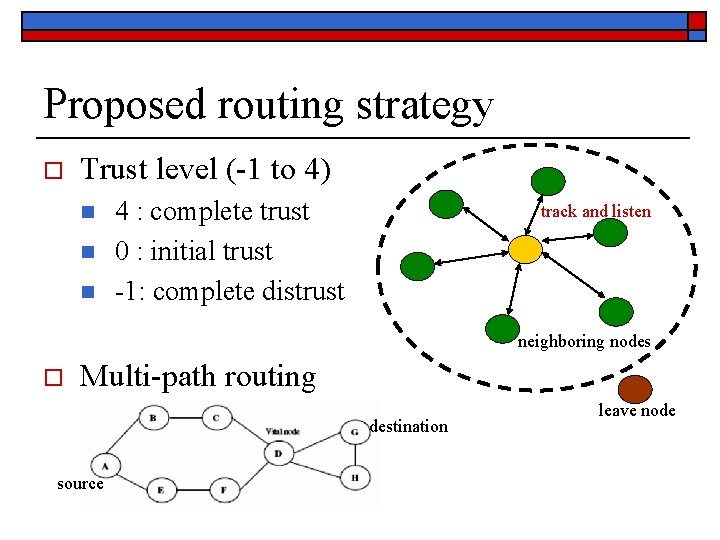
Proposed routing strategy o Trust level (-1 to 4) n n n 4 : complete trust 0 : initial trust -1: complete distrust track and listen neighboring nodes o Multi-path routing destination source leave node
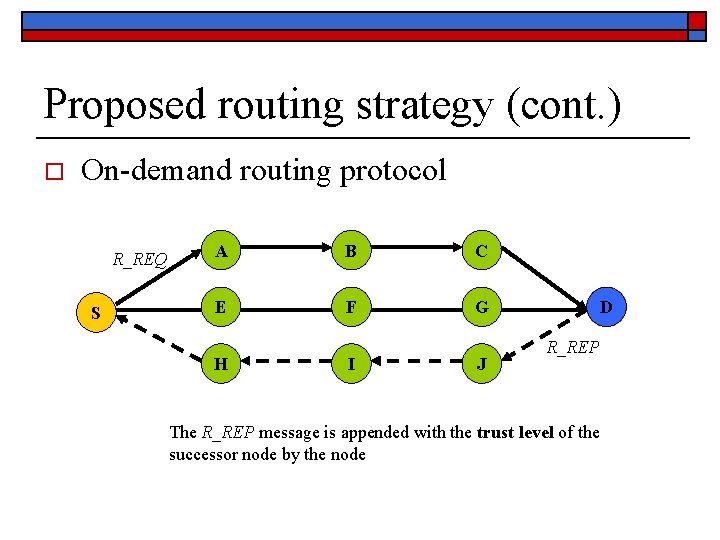
Proposed routing strategy (cont. ) o On-demand routing protocol R_REQ S A B C E F G H I J D R_REP The R_REP message is appended with the trust level of the successor node by the node
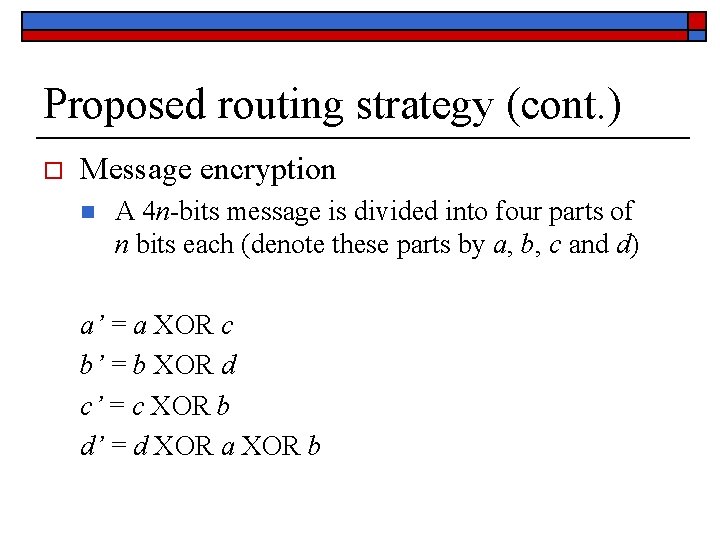
Proposed routing strategy (cont. ) o Message encryption n A 4 n-bits message is divided into four parts of n bits each (denote these parts by a, b, c and d) a’ = a XOR c b’ = b XOR d c’ = c XOR b d’ = d XOR a XOR b
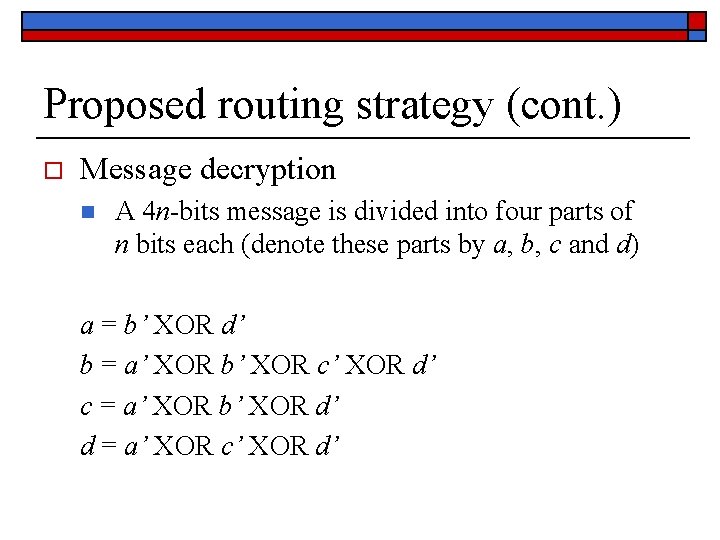
Proposed routing strategy (cont. ) o Message decryption n A 4 n-bits message is divided into four parts of n bits each (denote these parts by a, b, c and d) a = b’ XOR d’ b = a’ XOR b’ XOR c’ XOR d’ c = a’ XOR b’ XOR d’ d = a’ XOR c’ XOR d’
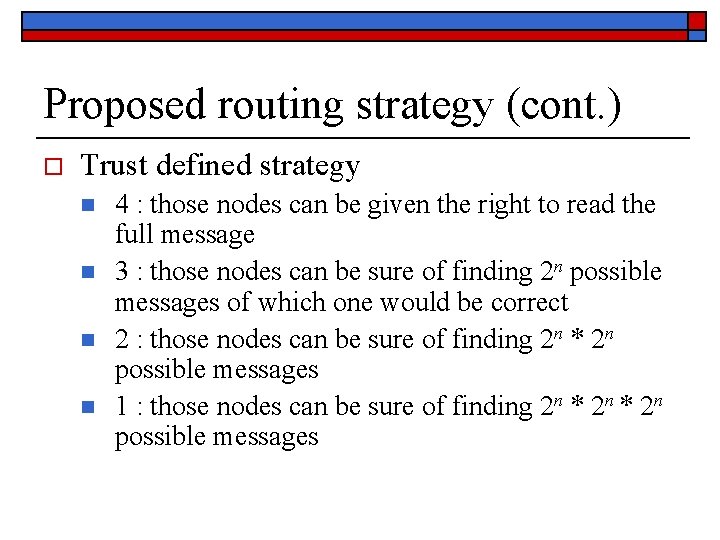
Proposed routing strategy (cont. ) o Trust defined strategy n n 4 : those nodes can be given the right to read the full message 3 : those nodes can be sure of finding 2 n possible messages of which one would be correct 2 : those nodes can be sure of finding 2 n * 2 n possible messages 1 : those nodes can be sure of finding 2 n * 2 n possible messages
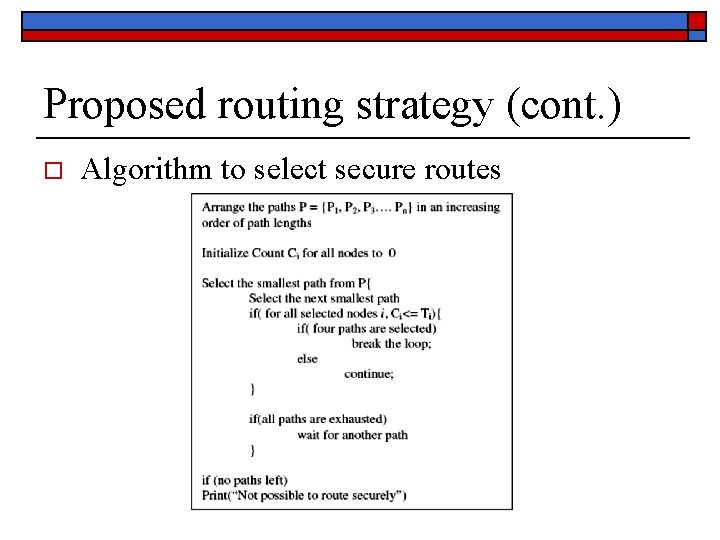
Proposed routing strategy (cont. ) o Algorithm to select secure routes
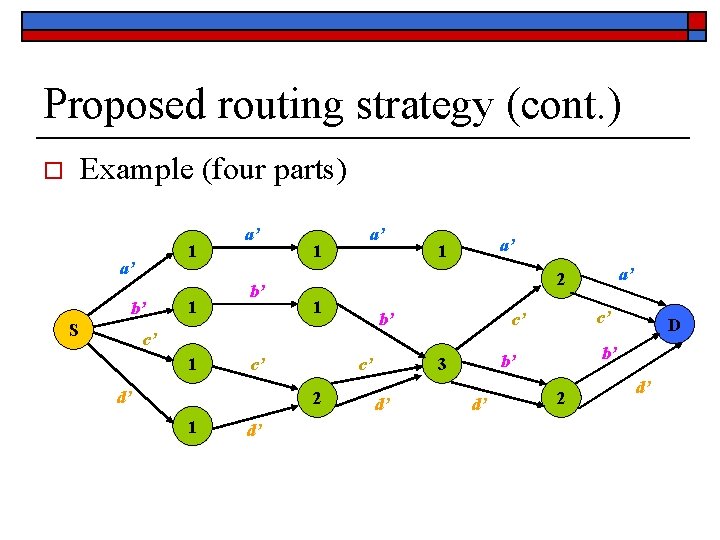
Proposed routing strategy (cont. ) Example (four parts) o 1 a’ b’ S 1 a’ b’ 1 a’ a’ 1 1 b’ c’ c’ c’ 1 c’ d’ d’ D b’ b’ 3 c’ 2 1 a’ 2 2 d’
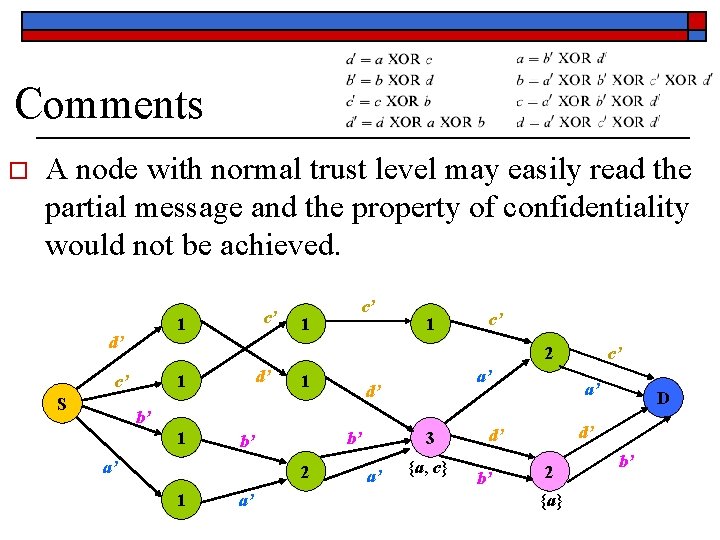
Comments o A node with normal trust level may easily read the partial message and the property of confidentiality would not be achieved. 1 d’ 1 c’ 2 d’ 1 c’ S c’ 1 a’ d’ b’ 1 a’ 2 1 a’ 3 b’ b’ a’ {a, c} a’ D d’ d’ b’ c’ 2 {a} b’
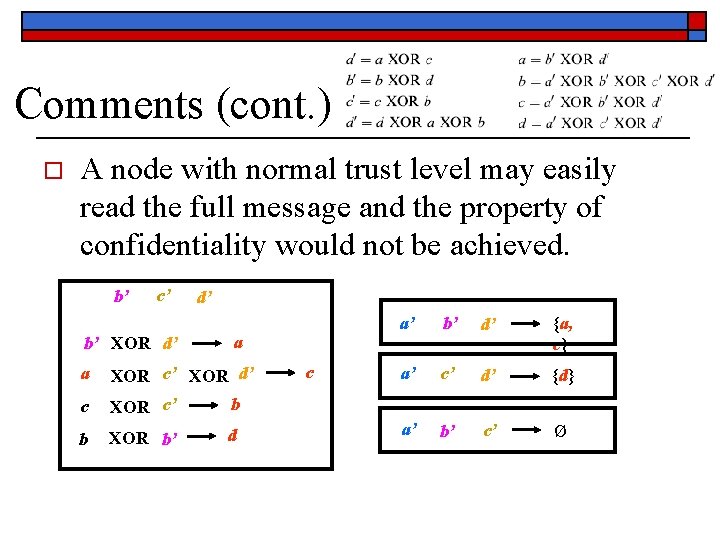
Comments (cont. ) o A node with normal trust level may easily read the full message and the property of confidentiality would not be achieved. b’ c’ b’ XOR d’ d’ a a XOR c’ XOR d’ c XOR c’ b b XOR b’ d c a’ b’ d’ {a, c} a’ c’ d’ {d} a’ b’ c’ Ø
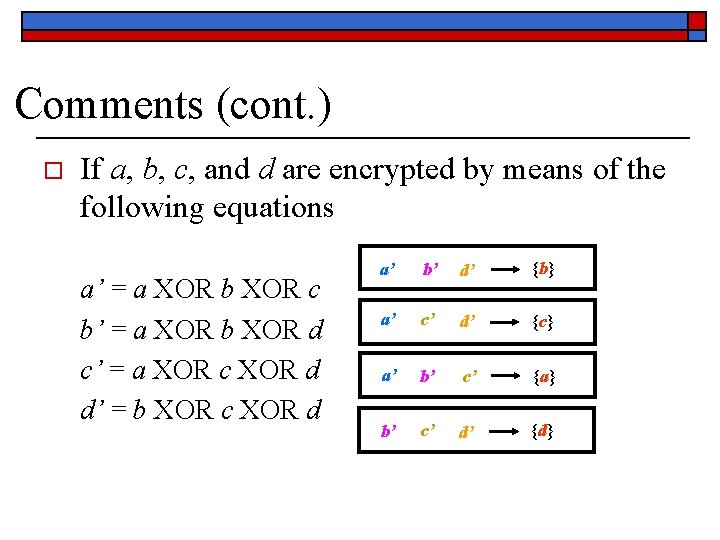
Comments (cont. ) o If a, b, c, and d are encrypted by means of the following equations a’ = a XOR b XOR c b’ = a XOR b XOR d c’ = a XOR c XOR d d’ = b XOR c XOR d a’ b’ d’ {b} a’ c’ d’ {c} a’ b’ c’ {a} b’ c’ d’ {d}
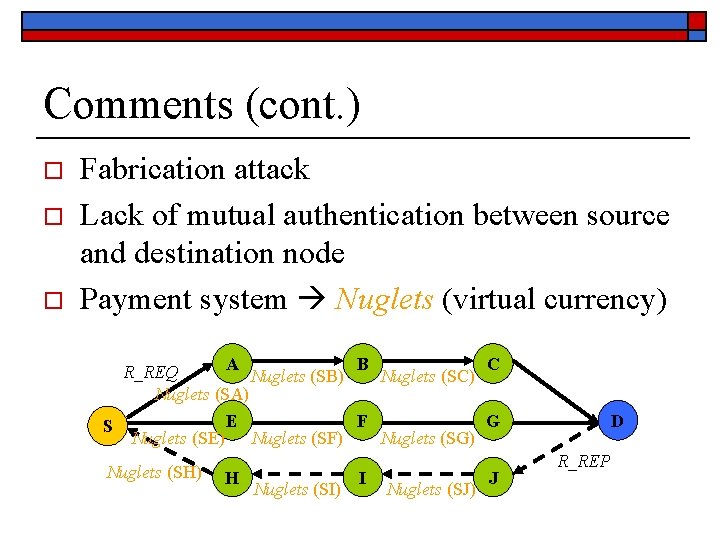
Comments (cont. ) o o o Fabrication attack Lack of mutual authentication between source and destination node Payment system Nuglets (virtual currency) A B C R_REQ Nuglets (SB) Nuglets (SC) Nuglets (SA) E F G S Nuglets (SE) Nuglets (SF) Nuglets (SG) Nuglets (SH) H Nuglets (SI) I Nuglets (SJ) J D R_REP
- Slides: 14