Securing a Network Virtualized with Containers and Kubernetes
Securing a Network Virtualized with Containers and Kubernetes Example Solutions and Current Gaps #ONESummit Samuli Kuusela and Amy Zwarico
Outline - Isolation - Container signing & Notary v 2 - CIS Benchmarks - Operating a Service Mesh - Securing Managed Apps in an SMO #ONESummit
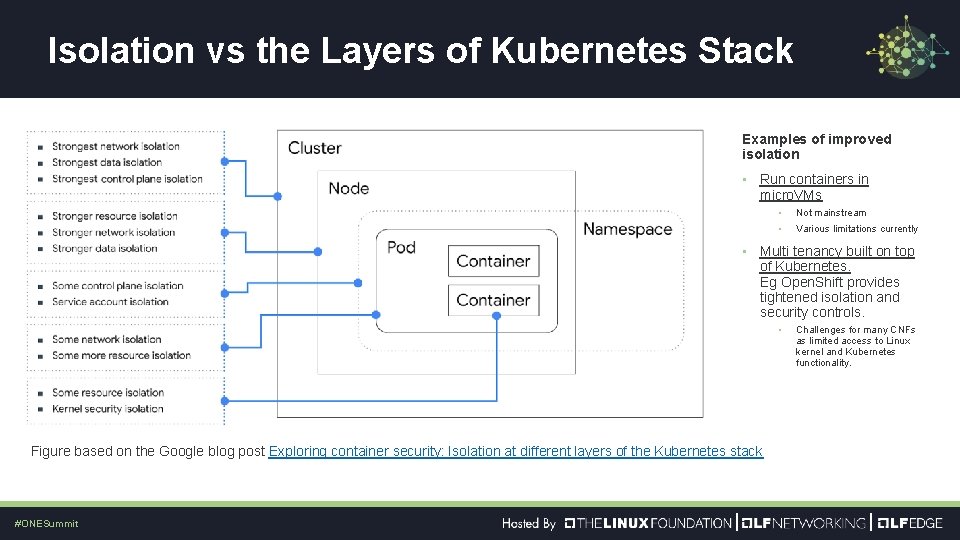
Isolation vs the Layers of Kubernetes Stack Examples of improved isolation • Run containers in micro. VMs • Not mainstream • Various limitations currently • Multi tenancy built on top of Kubernetes. Eg Open. Shift provides tightened isolation and security controls. • Figure based on the Google blog post Exploring container security: Isolation at different layers of the Kubernetes stack #ONESummit Challenges for many CNFs as limited access to Linux kernel and Kubernetes functionality.
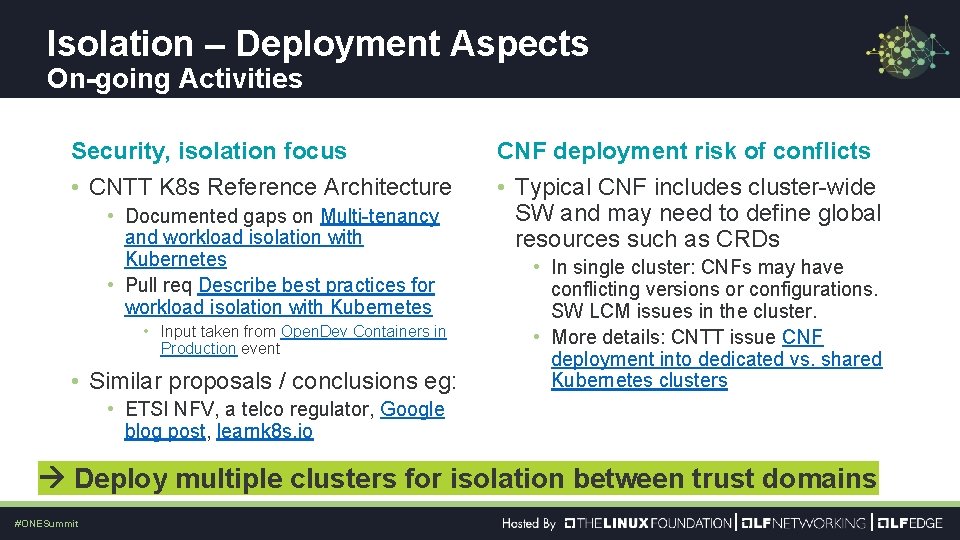
Isolation – Deployment Aspects On-going Activities Security, isolation focus • CNTT K 8 s Reference Architecture • Documented gaps on Multi-tenancy and workload isolation with Kubernetes • Pull req Describe best practices for workload isolation with Kubernetes • Input taken from Open. Dev Containers in Production event • Similar proposals / conclusions eg: CNF deployment risk of conflicts • Typical CNF includes cluster-wide SW and may need to define global resources such as CRDs • In single cluster: CNFs may have conflicting versions or configurations. SW LCM issues in the cluster. • More details: CNTT issue CNF deployment into dedicated vs. shared Kubernetes clusters • ETSI NFV, a telco regulator, Google blog post, learnk 8 s. io Deploy multiple clusters for isolation between trust domains #ONESummit
Container Signing & Notary v 2 • Proprietary signing solutions exist, but no industry standard. Eg: • Red. Hat simple signing • Docker Content Trust • Notary v 2 • Kickoff end of 2019, with: Amazon, Microsoft, Docker, IBM, Google, Red Hat, Sylabs, Jfrog • Kickoff media announcementions the goals: • • Integrate signatures into registries Movement of signatures between registries OCI standardization Improving usability • Notary v 2 scenarios document Telco needs to join in & ensure the solution will fit for CNFs #ONESummit
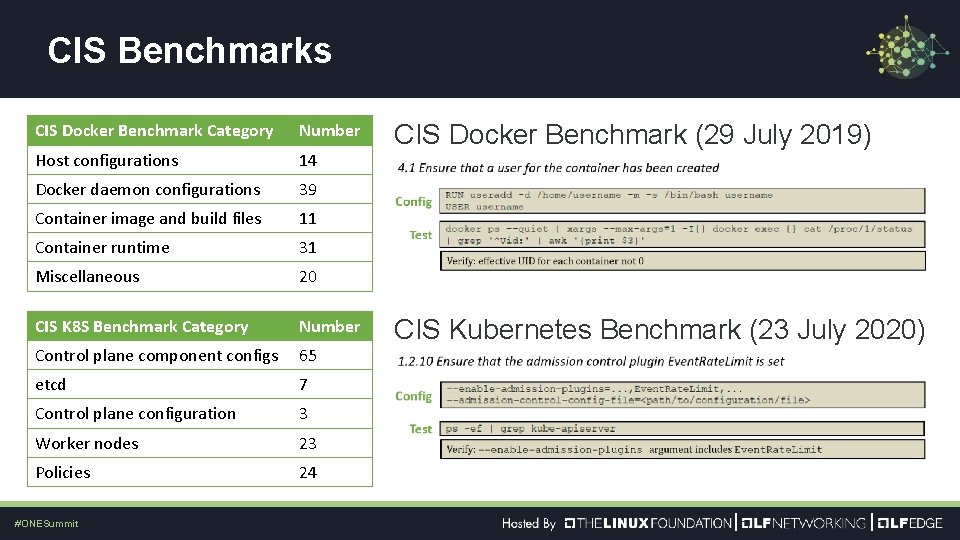
CIS Benchmarks CIS Docker Benchmark Category Number Host configurations 14 Docker daemon configurations 39 Container image and build files 11 Container runtime 31 Miscellaneous 20 CIS K 8 S Benchmark Category Number Control plane component configs 65 etcd 7 Control plane configuration 3 Worker nodes 23 Policies 24 #ONESummit CIS Docker Benchmark (29 July 2019) CIS Kubernetes Benchmark (23 July 2020)
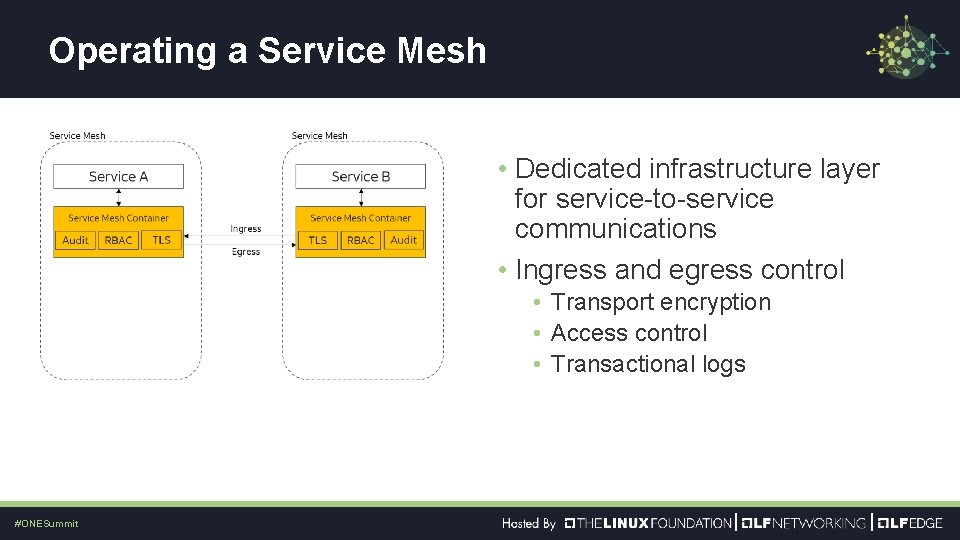
Operating a Service Mesh • Dedicated infrastructure layer for service-to-service communications • Ingress and egress control • Transport encryption • Access control • Transactional logs #ONESummit
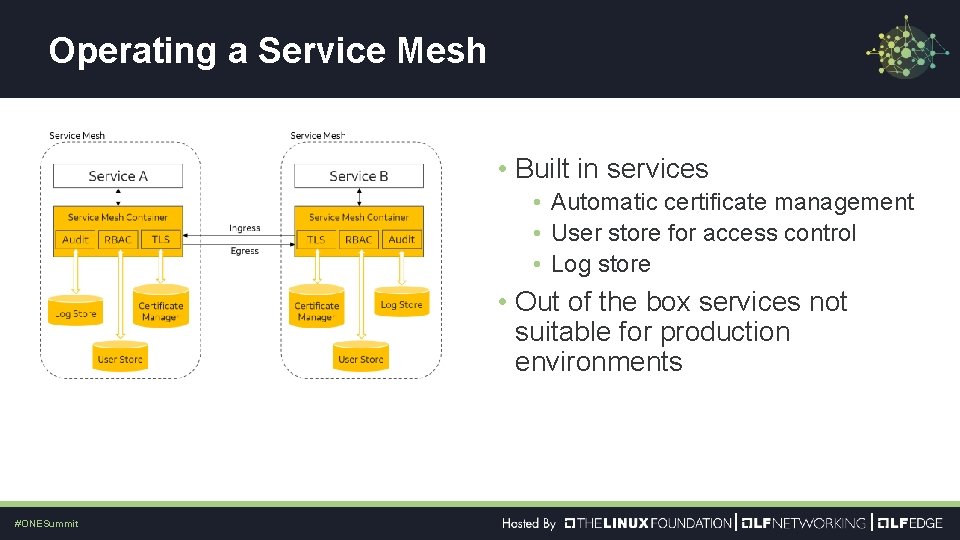
Operating a Service Mesh • Built in services • Automatic certificate management • User store for access control • Log store • Out of the box services not suitable for production environments #ONESummit
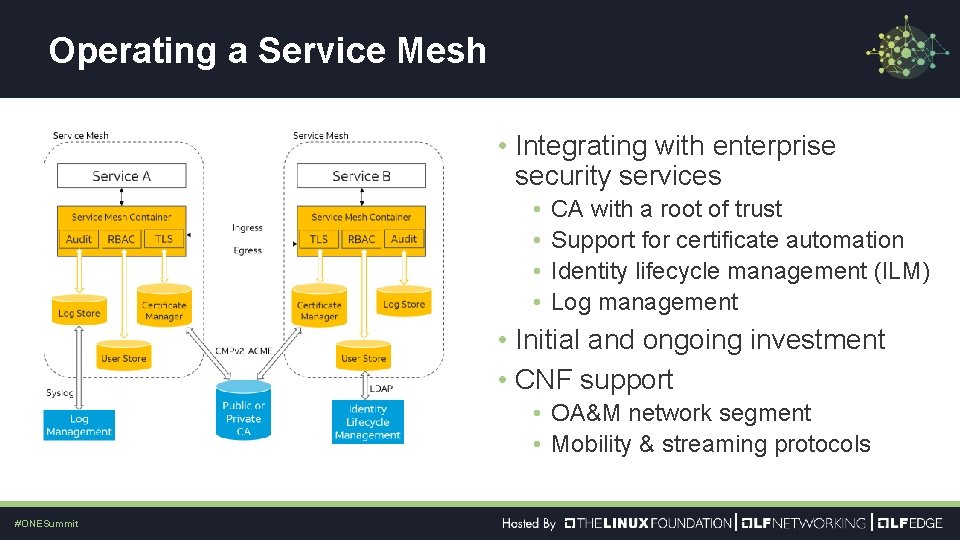
Operating a Service Mesh • Integrating with enterprise security services • • CA with a root of trust Support for certificate automation Identity lifecycle management (ILM) Log management • Initial and ongoing investment • CNF support • OA&M network segment • Mobility & streaming protocols #ONESummit
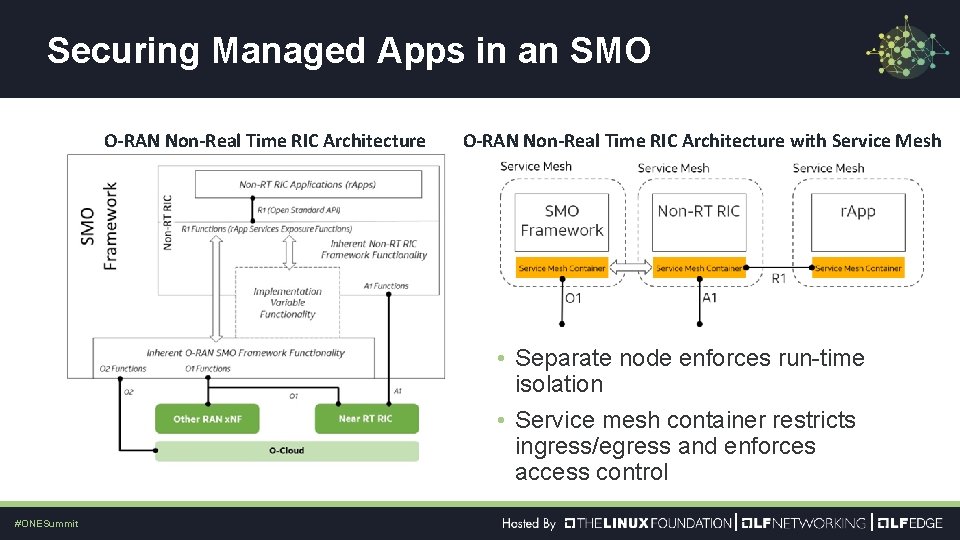
Securing Managed Apps in an SMO O-RAN Non-Real Time RIC Architecture • Click to add Text O-RAN Non-Real Time RIC Architecture with Service Mesh • Separate node enforces run-time isolation • Service mesh container restricts ingress/egress and enforces access control #ONESummit

- Slides: 11