Raising The Bar For Windows Rootkit Detection Aurthors
Raising The Bar For Windows Rootkit Detection Aurthors: Sherri Sparks, Jamie Butler Publication: Phrack Magazine, 2005 Presenter : Richard Bares
What is a Rootkit n n n Code that tries to hide itself along with other components from detection by other software Can be used by virus detection software to hide from malicious code Can also be used by malicious code to hide from virus detection software
First generation Rootkits n n n Replaced or modified key system files with maliciously enhanced versions Designed to avoid detection or perform other malicious actions Example changing login programs to record password as well as verify them
Second Generation Rootkits n n Moved from changing files on hard disk to memory Altered execution path of application and operating system components instead of changing the targeted files themselves
Third generation Rootkits n n Direct Kernel Object Manipulation Targeted dynamically changing kernel data structure in operating system Prevented detection software from getting a baseline reading Example the FU rootkit
Detection of Rootkits n n n Misuse detection based on Signatures Anomaly Detection based on statistical deviations from normal behavior Integrity Detection based on snapshots of file systems or memory compared to a baseline
Rootkit of the Future n n n Code that does not try to hide by altering it’s code but changes what detection software sees When detection software tries to access memory the rootkit will return a fake view of the memory without itself Does this by gaining control of virtual memory on computer system
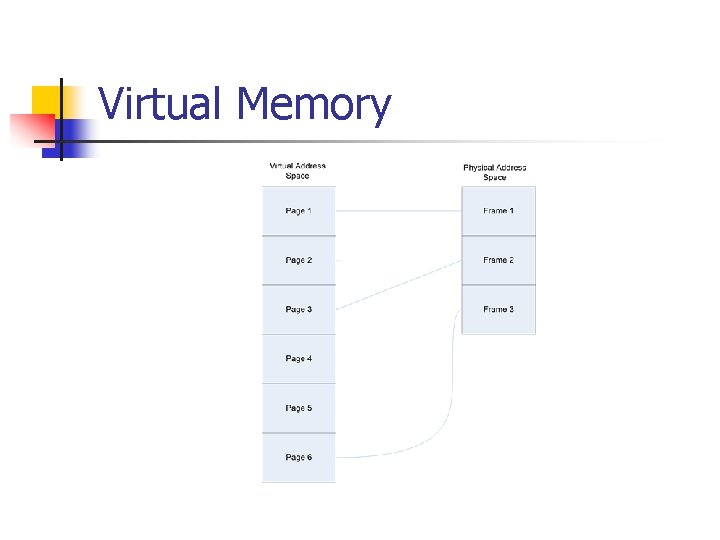
Virtual Memory
Keeping Track Of Virtual Memory n n Page Fault handler which allows for swapping of large files Two Translation Lookaside Buffer (TLB) which is used to keep track of frequently used instruction and data
Modified FU Rootkit n n Replaces page fault handler code Modifies Data TLB to redirect data access of rookit data by detection software to wrong location
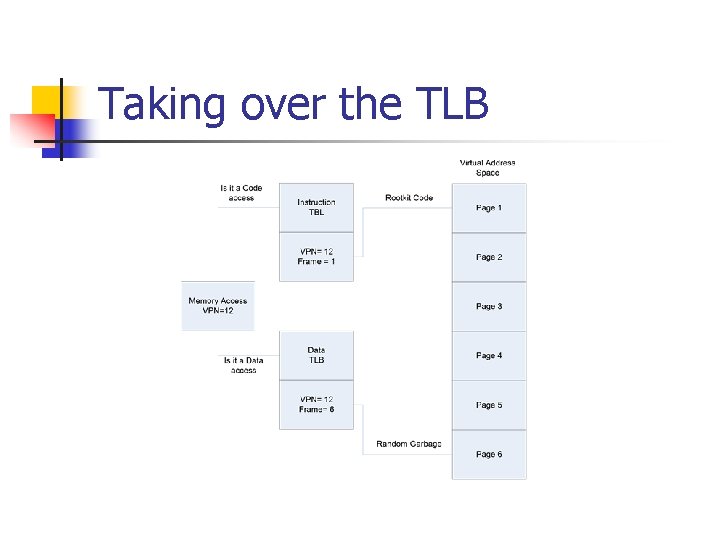
Taking over the TLB
Conclusion n Could be a valid new form of rootkit on some systems The modified FU rootkit was able to hide from most detection attempts But more tested and modification are needed
Contributions n n Added a new understanding of possible future development in rootkits by attacking system x 86 architecture Ways to detect these attacks by looking at the page fault handler
Weaknesses n n Does not work on 4 MB page block No way to hide the replaced page fault handler Modified rootkit has a performance impact of the installed system Only works on x 86 CPUs
- Slides: 14