Rootkits ECE 4112 Internetwork Security Agenda n n
- Slides: 51
Rootkits ECE 4112 Internetwork Security
Agenda n n n Introduction Definition of a Rootkit Existing Methodologies to Detect Rootkits Lrk 4 Knark Conclusion
Introduction n n Current Vulnerabilities on the Internet Current Techniques Used by System Administrators to monitor the status of Systems n n n Intrusion Detection Systems File Integrity Programs Signature Analysis Programs
Agenda n n n Introduction Definition of a Rootkit Existing Methodologies to Detect Rootkits Lrk 4 Knark Conclusion
Definition of a Rootkit n n n “Trojan Horse” into a Computer System Malicious Programs that pretend to be normal programs May also be programs: n n n that masquerade as “possible” programs with names that approximate existing program already running and not easily identifiable by user
Definition of a Rootkit n Installing a Rootkit on a Target System n n n Hacker MUST already have root level access on target system Gain root level access by compromising system via buffer overflow, password attack, social engineering Rootkit allows hacker to get back onto system with root level privilege
Definition of a Rootkit n n Rootkits are a recent phenomenon Developed by hackers to conceal their activities One method is to replace existing binary system files that continue to function as normal but allow hacker back door access Can be developed by skilled hacker with programming expertise
Agenda n n n Introduction Definition of a Rootkit Existing Methodologies to Detect Rootkits Lrk 4 Knark Conclusion
Existing Methodologies to Detect Rootkits n Use of Host Based Intrusion Detection System (IDS) n n n TRIPWIRE Advanced Intrusion Detection Environment (AIDE) Downloadable on Internet n n http: //www. cs. tut. fi/~rammer/aide. html. Chkrootkit n chkrootkit is available at: http: //www. chkrootkit. org
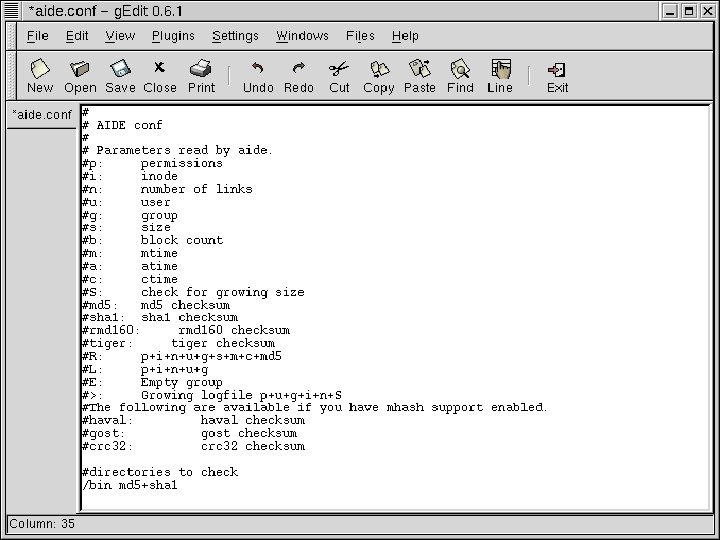
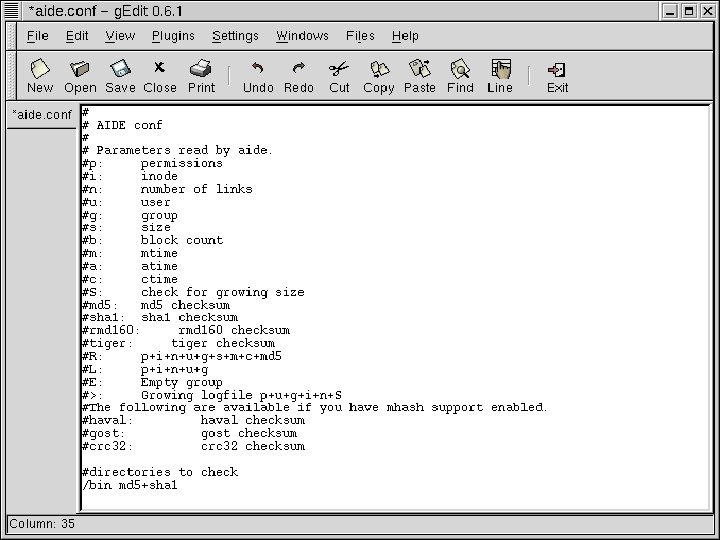
Existing Methodologies to Detect Rootkits n AIDE n n n Open Source Product Can support multiple Integrity Checking Algorithms Customized Configuration File (aide. conf) is necessary
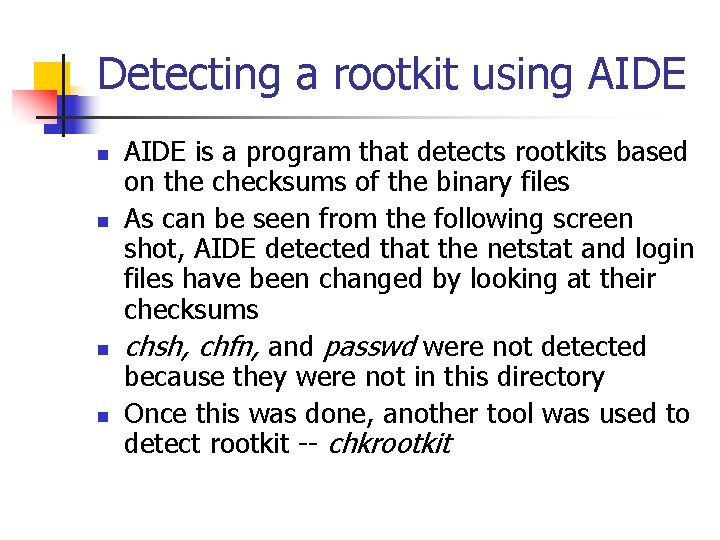
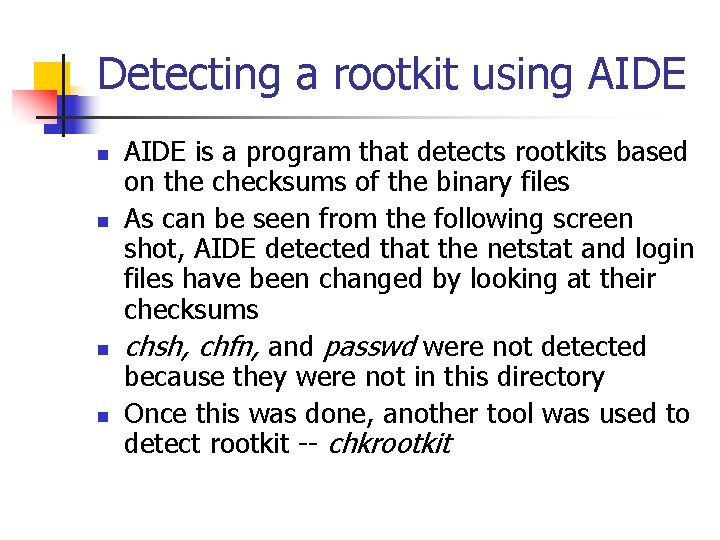
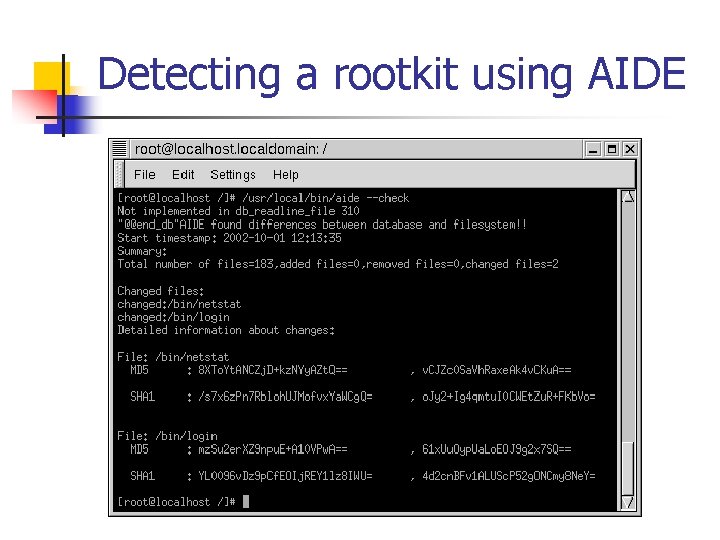
Detecting a rootkit using AIDE n n AIDE is a program that detects rootkits based on the checksums of the binary files As can be seen from the following screen shot, AIDE detected that the netstat and login files have been changed by looking at their checksums chsh, chfn, and passwd were not detected because they were not in this directory Once this was done, another tool was used to detect rootkit -- chkrootkit
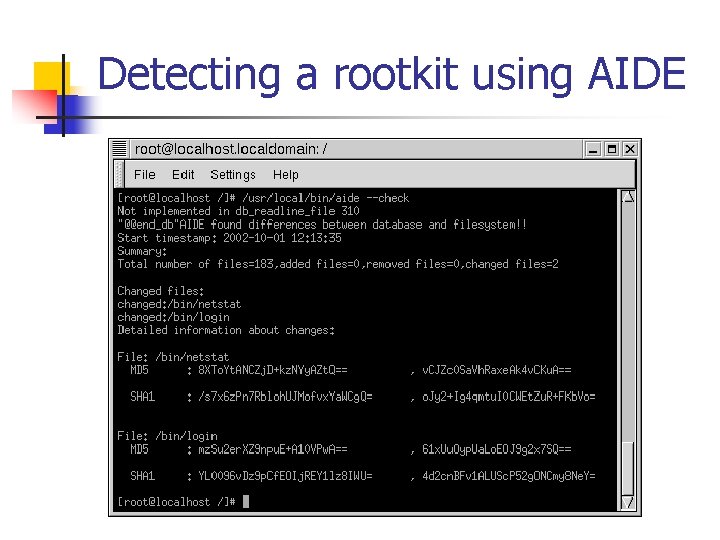
Detecting a rootkit using AIDE
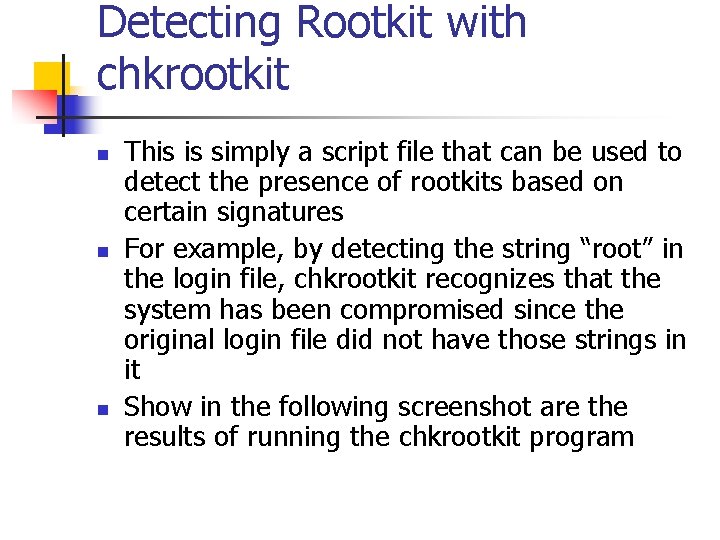
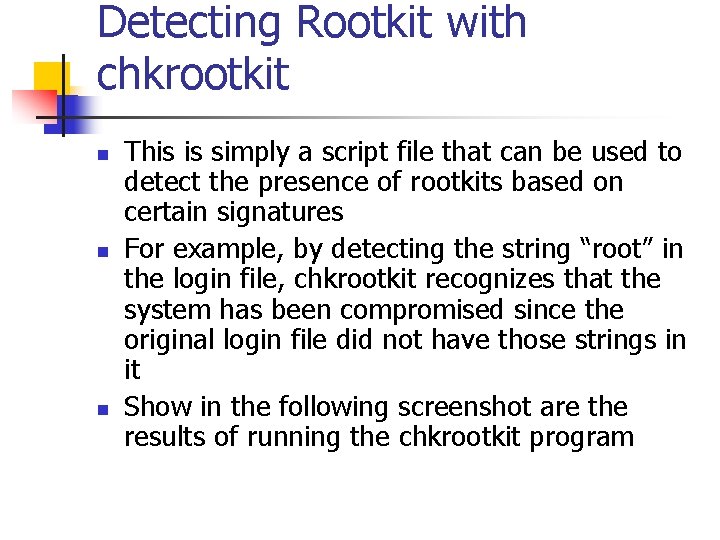
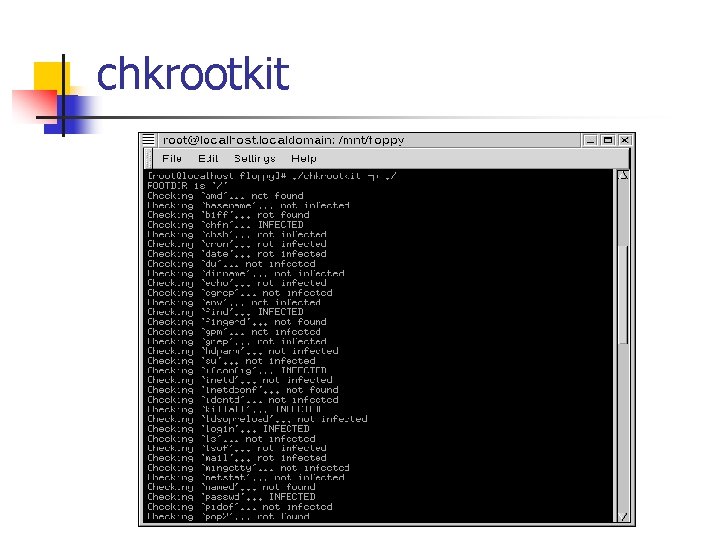
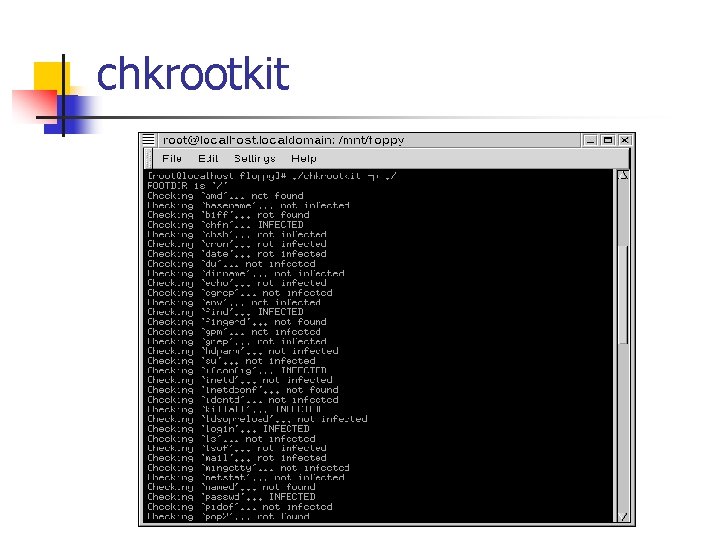
Detecting Rootkit with chkrootkit n n n This is simply a script file that can be used to detect the presence of rootkits based on certain signatures For example, by detecting the string “root” in the login file, chkrootkit recognizes that the system has been compromised since the original login file did not have those strings in it Show in the following screenshot are the results of running the chkrootkit program
chkrootkit
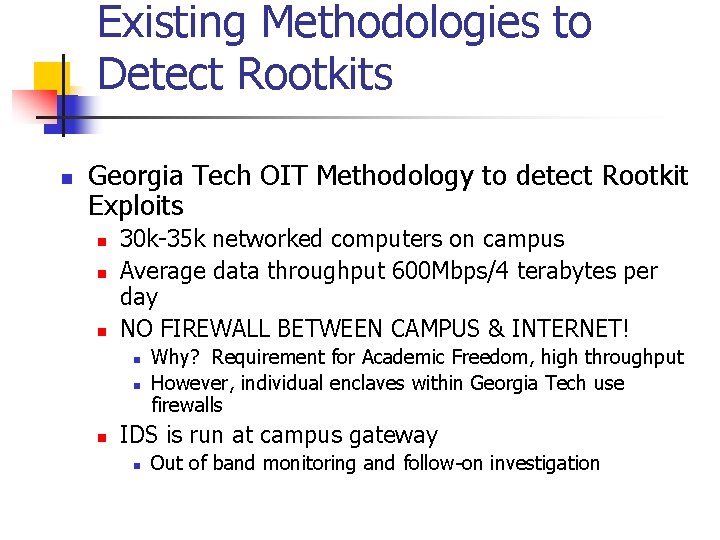
Existing Methodologies to Detect Rootkits n Georgia Tech OIT Methodology to detect Rootkit Exploits n n n 30 k-35 k networked computers on campus Average data throughput 600 Mbps/4 terabytes per day NO FIREWALL BETWEEN CAMPUS & INTERNET! n n n Why? Requirement for Academic Freedom, high throughput However, individual enclaves within Georgia Tech use firewalls IDS is run at campus gateway n Out of band monitoring and follow-on investigation
Existing Methodologies to Detect Rootkits n Installation of IDS n n Prior to installation – 5 investigations per week After installation – up to 5 investigations per day Anomaly Based IDS monitors machines on campus A Honeynet is currently running at Georgia Tech
Existing Methodologies to Detect Rootkits n Steps taken upon investigation of a compromised system: n n n Contact responsible system administrator System may be rebooted with known good media with suspect hard drive mounted read-only Duplicate copy of hard drive may be produced with cryptographic checksum signature for possible criminal investigation
Existing Methodologies to Detect Rootkits n Forensic Investigation of compromised system: n n No formalized methodology currently exists forensic investigation Logs will be examined first n n May have no record of exploit or may be deleted entirely Steps may be taken to retrieve deleted log files
Existing Methodologies to Detect Rootkits n Previously know target directories will be examined for suspicious files or entries n n eg. t 0 rn rootkit creates /etc/ttyhash which is a copy of the original /bin/login progam chkrootkit program may be run to check for previously known exploits n chkrootkit is available at: http: //www. chkrootkit. org
Existing Methodologies to Detect Rootkits n For LINUX/UNIX systems various commands will be used to check for compromises: n n find & locate to look for suspicious files and directories file & strings to examine suspect files ldd (load library dependencies) & strace Similar methodology used for other operating systems
Agenda n n n Introduction Definition of a Rootkit Existing Methodologies to Detect Rootkits Lrk 4 Knark Conclusion
Lrk 4 Background n n n Written by Lord Somer Released in November 1998 Several more recent versions are available (lrk 5 and lrk 6); however, lrk 4 is the most stable out of all of them Updates for lrk 4 still being posted However, to run lrk 4, it is necessary to install old libraries since lrk 4 was built against these earlier libraries
Installing lrk 4 n Although a Makefile is included with lrk 4, compilation results in several errors n n This is due to uniqueness of each operating system For this lab, red Hat 7. 2 is used One major problem – numerous references to pre-defined library functions Other problems n n n Failure to reference necessary libraries Failure to define referenced variables Getting the rootkit to work requires some knowledge of programming
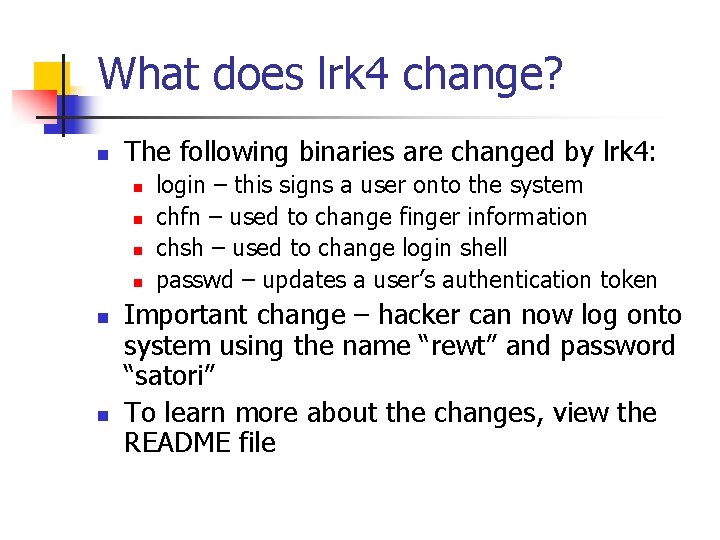
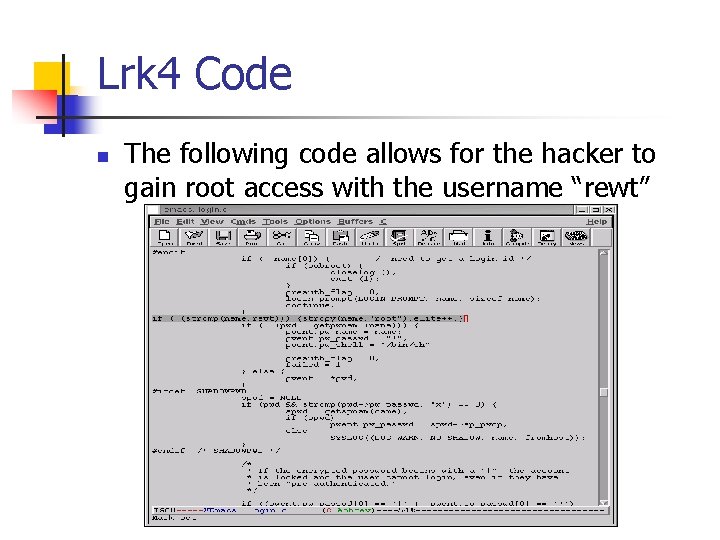
What does lrk 4 change? n The following binaries are changed by lrk 4: n n n login – this signs a user onto the system chfn – used to change finger information chsh – used to change login shell passwd – updates a user’s authentication token Important change – hacker can now log onto system using the name “rewt” and password “satori” To learn more about the changes, view the README file
Hiding lrk 4 on the system n n How do you make sure you’re changed binaries are not easily detected? Run “fix” tool (normally comes with the rootkit) n This changes the date of the binaries so that it looks like they are old binaries
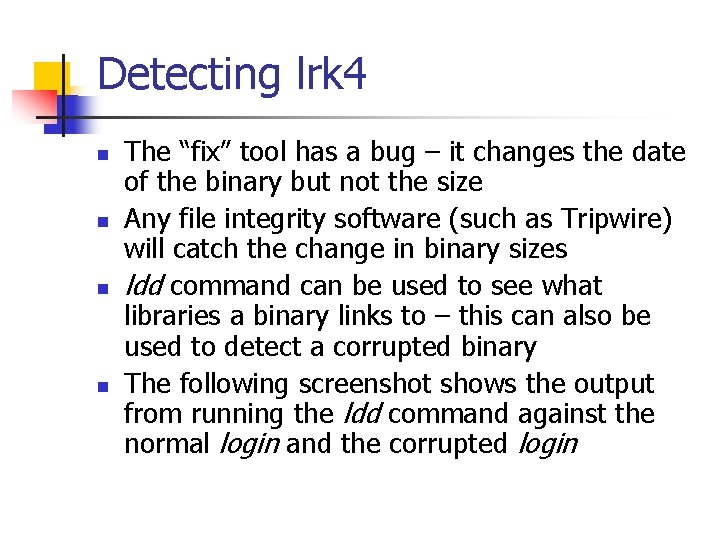
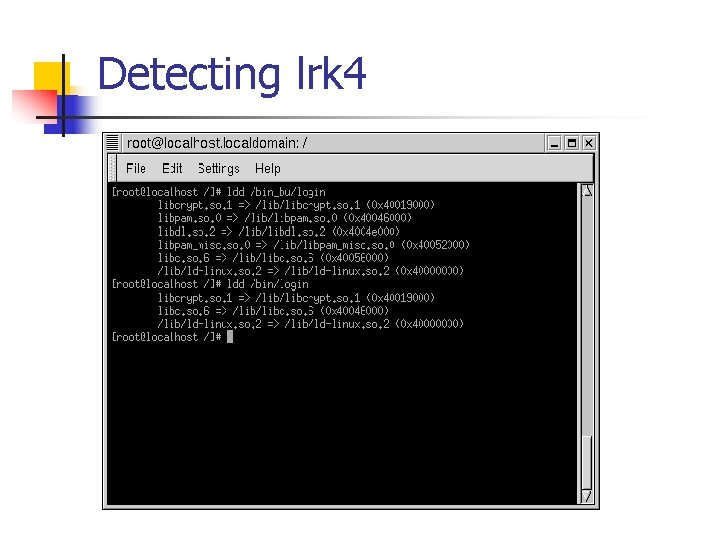
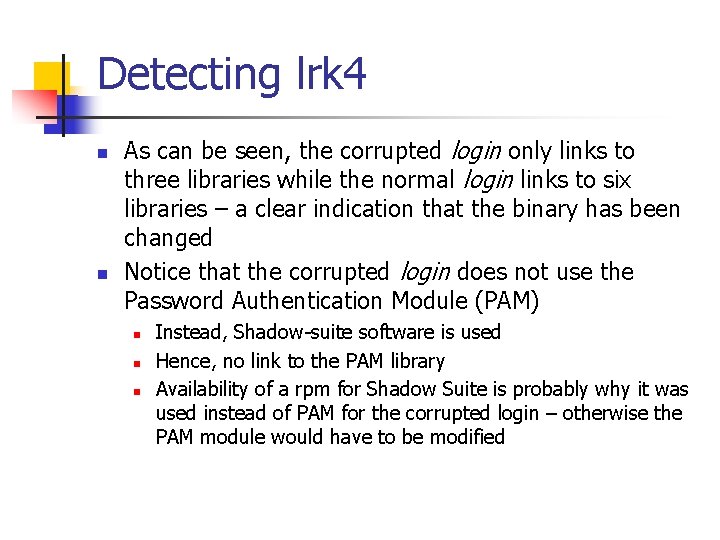
Detecting lrk 4 n n The “fix” tool has a bug – it changes the date of the binary but not the size Any file integrity software (such as Tripwire) will catch the change in binary sizes ldd command can be used to see what libraries a binary links to – this can also be used to detect a corrupted binary The following screenshot shows the output from running the ldd command against the normal login and the corrupted login
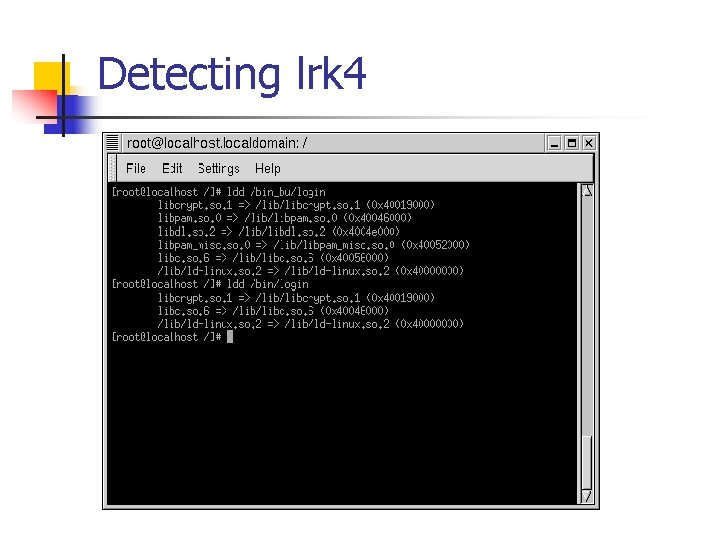
Detecting lrk 4
Detecting lrk 4 n n As can be seen, the corrupted login only links to three libraries while the normal login links to six libraries – a clear indication that the binary has been changed Notice that the corrupted login does not use the Password Authentication Module (PAM) n n n Instead, Shadow-suite software is used Hence, no link to the PAM library Availability of a rpm for Shadow Suite is probably why it was used instead of PAM for the corrupted login – otherwise the PAM module would have to be modified
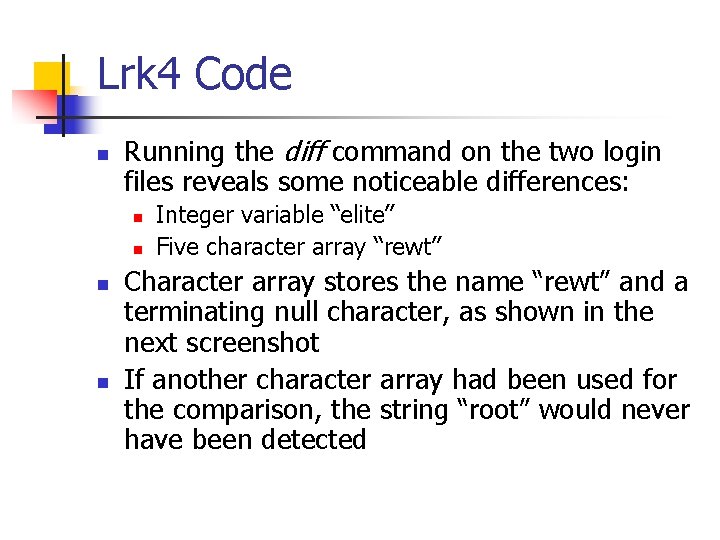
Lrk 4 Code n Running the diff command on the two login files reveals some noticeable differences: n n Integer variable “elite” Five character array “rewt” Character array stores the name “rewt” and a terminating null character, as shown in the next screenshot If another character array had been used for the comparison, the string “root” would never have been detected
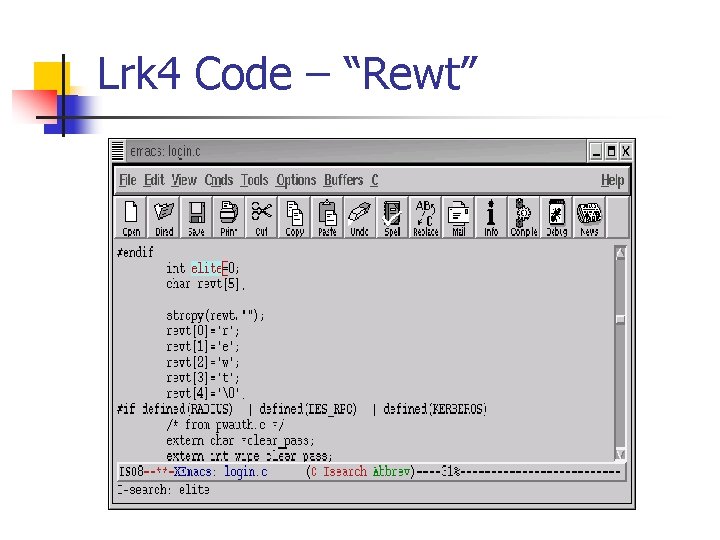
Lrk 4 Code – “Rewt”
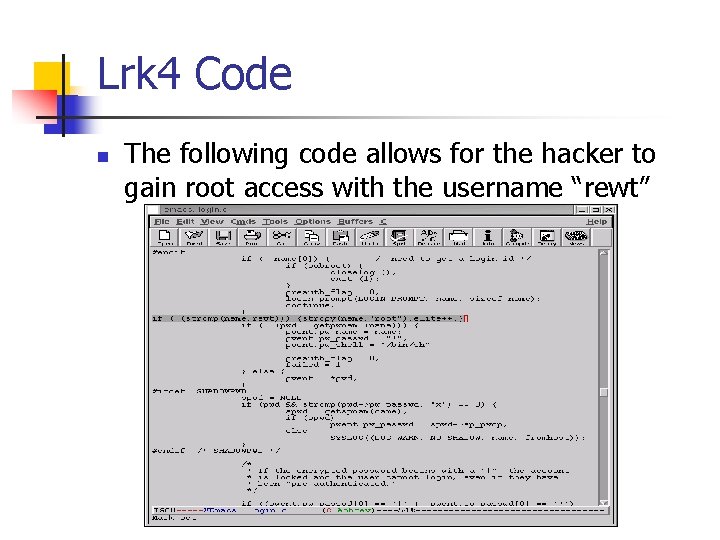
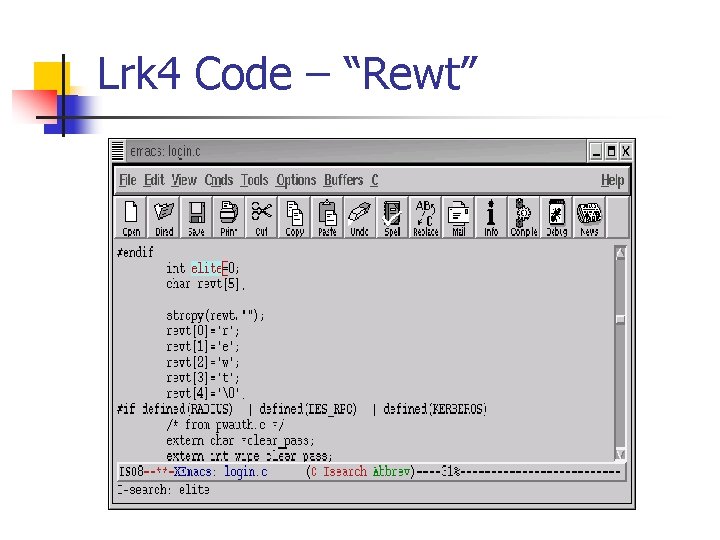
Lrk 4 Code n The following code allows for the hacker to gain root access with the username “rewt”
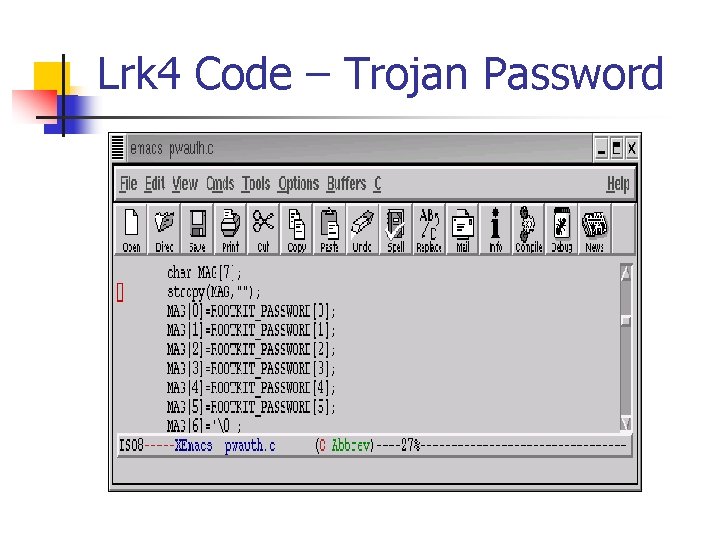
Lrk 4 Code – Trojan Password n Ok, so we have root being passed in … what about the password? n n n pw_auth program check’s to see if a user’s password is valid pw_auth code is modified so that trojan password “satori” is added to password list Trojan password stored in a seven character array and values copied from rootkit. h header file
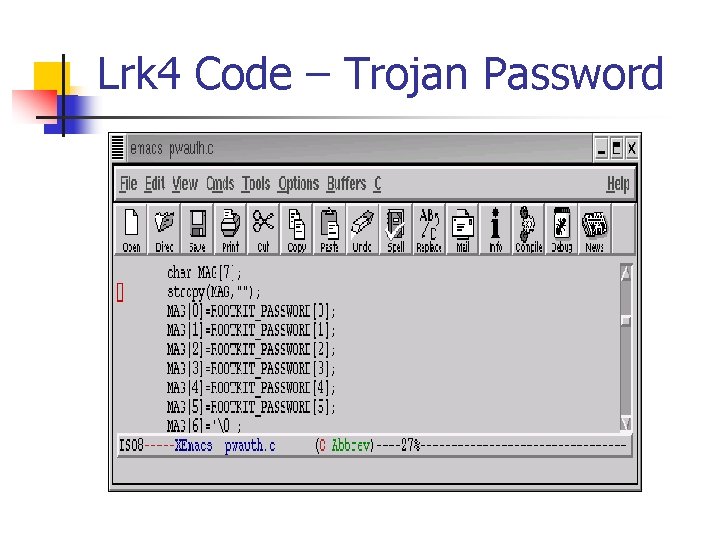
Lrk 4 Code – Trojan Password
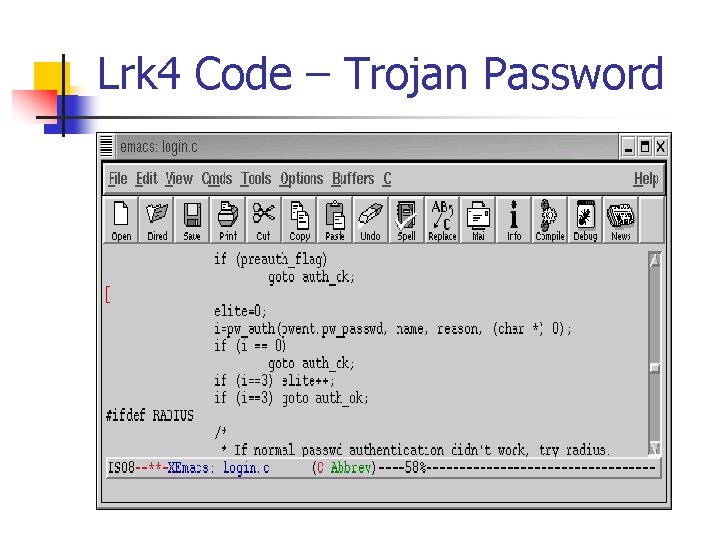
Lrk 4 Code – Trojan Password n n Clean pw_auth would return value of ‘ 0’ whenever password validated Edited pw_auth returns value of ‘ 3’ when input password matches password in rootkit. h Program then transitions to the auth_ok portion of login. c Elite variable is set to ‘ 1’ n Significant for remainder of login. c program
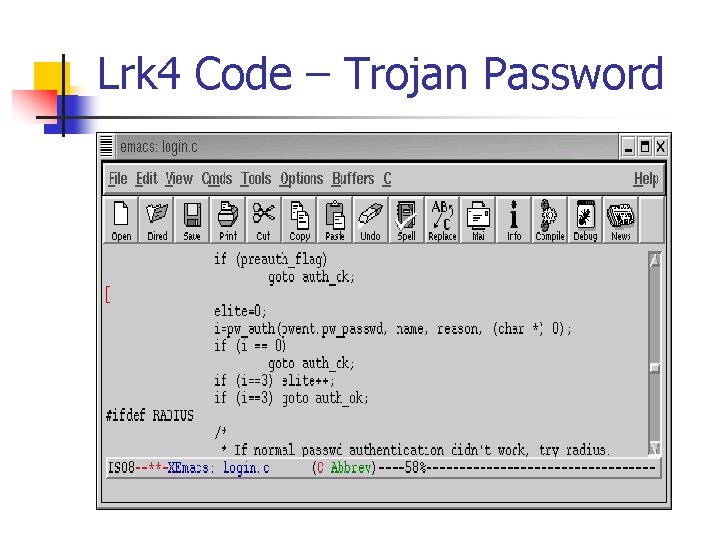
Lrk 4 Code – Trojan Password
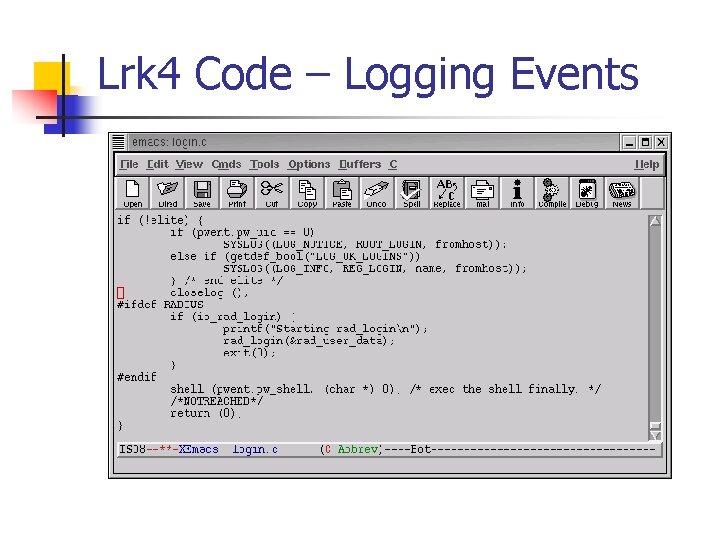
Lrk 4 Code – Logging Events n So we’ve gained access to the machine … how can we make sure our activities aren’t logged? n n n Check to see if the user has entered the trojan password and username “rewt” If so, then bypass logging activities to the SYSLOG file This is accomplished with the following code fragment:
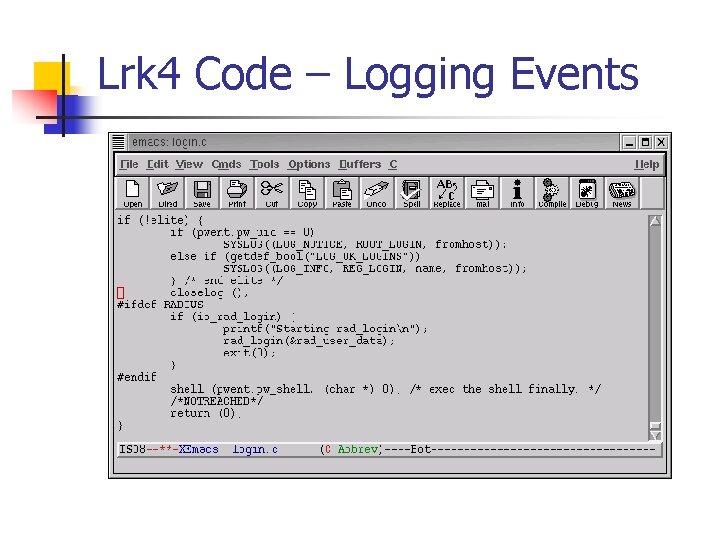
Lrk 4 Code – Logging Events
Lrk 4 Summary n n Lrk 4 is a very powerful tool Trojan username and password can be used to gain root access on a system Not easy to get lrk 4 to work sometimes – requires a degree of programming skill Tracks can be covered to a certain extent – however, file integrity systems will still detect that a rootkit has been installed
Agenda n n n Introduction Definition of a Rootkit Existing Methodologies to Detect Rootkits Lrk 4 Knark Conclusion
KNARK Background n n Written by Creed Released in 1999 Versions exist for Linux 2. 2 and 2. 4 kernels Very popular in ‘script kiddie’ community
KNARK Capabilities n n n n Hide/Unhide files or directories Hide TCP/UDP connections Execution Redirection Unauthenticated privilege escalation via the rootme program within knark Ability to change UID/GID of a running process Unauthenticated, privileged remote execution daemon Kill – 31 to hide a running process
Installing KNARK n KNARK IS installed as a Loadable Kernel Module (LKM) n n n System must have LKM enabled in order to be able to load KNARK Can be defeated if LKM is disabled, HOWEVER, updating system becomes much more complicated The KNARK rootkit has an additional LKM module to hide the presence of KNARK from the insmod (installed module) command.
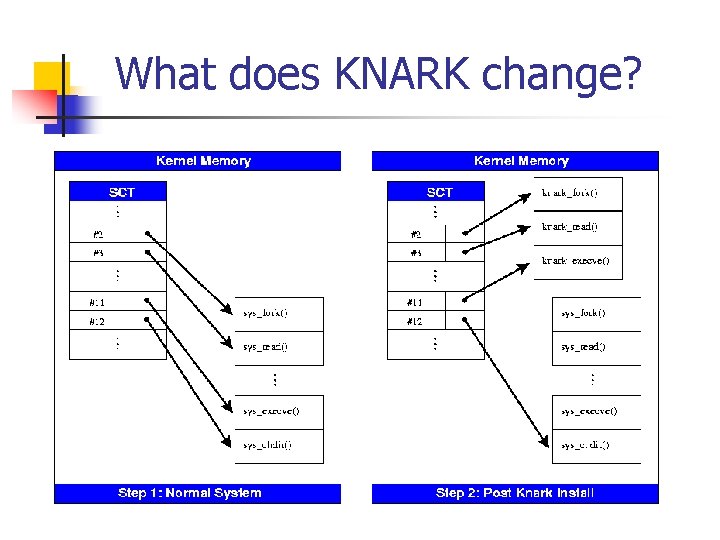
What does KNARK Change? n n KNARK modifies the system call table (sys_call_table) within kernel memory by redirecting some system calls (sys_read, sys_getdents) to malicous system calls written by CREED. These new malicious system calls function as normal except in certain circumstances.
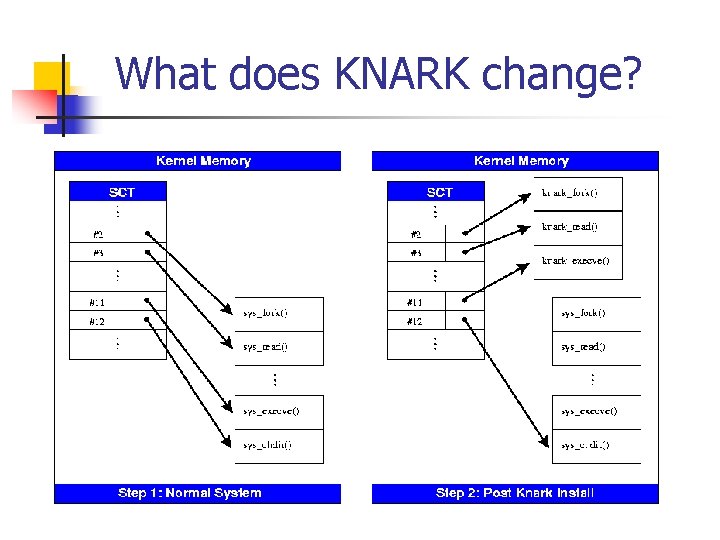
What does KNARK change?
What does KNARK Change? n n Can no longer trust the output of the system calls? Very difficult to detect rootkits such as KNARK using conventional methods n n System utility files (ls, ps) are not modified Kernel Output to system utility files IS modified.
Detecting KNARK n Cyptographic Checksums of system utilities will NOT change when KNARK is installed n n May be possible to take cryptographic checksum of selected region of kernel in order to detect rootkit modification of kernel (St. Michael) Can detect presence of KNARK type rootkits by examining sys_call_table
Detecting KNARK n The file /boot/System. map is created when system is initially compiled n n n /boot/System. map contains correct address of kernel system calls /boot/system map can be archived or retrieved from a known good system for comparison Must have Superuser (ROOT) privilege in order to read /dev/kmem (kernel memory)
Detecting KNARK using the kern_check program n n Developed by Samhain labs GPL (‘free’) software Compares /boot/System. map file against the system call table in kernel memory Will not work against later versions of Red Hat Linux 2. 4 or the Linux 2. 6 kernel
KNARK Summary n n KNARK is a very powerful tool that was very popular with ‘script kiddies’ Very difficult to detect with conventional methods Can no longer trust system output once kernel is compromised Other kernel rootkits can defeat kern_check program (Suck. IT)
Rootkit Summary n n Prevent hackers from gaining root access in order to prevent rootkits from being installed Must check systems on a periodic basis for rootkit exploits Current advice for a rootkitted system: Wipe out files and re-install operating system. Is it possible to re-establish trust on a Rootkited System?