Publicly verifiable authenticated encryption Author Changshe Ma and
Publicly verifiable authenticated encryption Author: Changshe Ma and Kefei Chen p Source: Electronics Letters 6 th February 2003, Vol. 39, No. 3 Page(s) 281 - 282 p Speaker: Jia-Chyi Wu p Team member : Kai-Jung Shih and Pei-Yu Lin p Date: 12/08/2003 p 2003/12/8
Outlines n n n Introduction Schnorr digital signature Proposed scheme Security considerations Conclusion 2003/12/8 2
Introduction n n Secure and authenticated message Lower expansion rate costs Lower communication costs Public verifiability q 2003/12/8 It is computationally feasible for a judge to verify the sender’s signature without divulging the receiver’s private key and the message 3
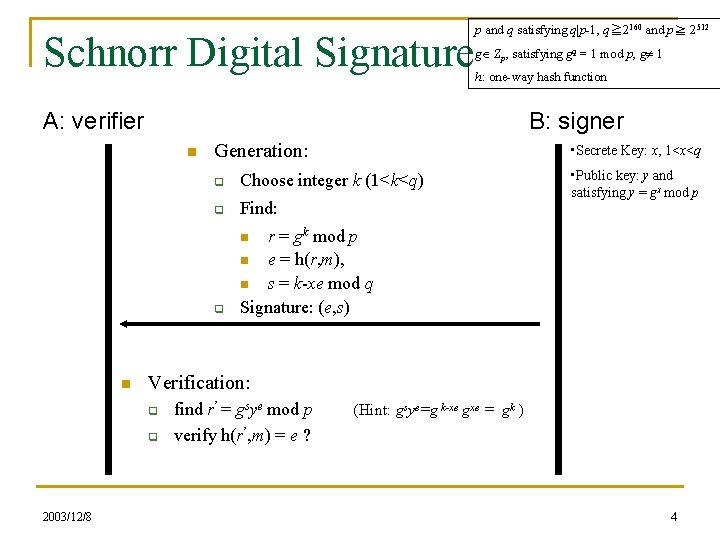
Schnorr Digital Signature p and q satisfying q|p-1, q≧ 2160 and p≧ 2512 g Zp, satisfying gq = 1 mod p, g 1 h: one-way hash function A: verifier B: signer n Generation: • Secrete Key: x, 1<x<q q Choose integer k (1<k<q) q Find: q r = gk mod p n e = h(r, m), n s = k-xe mod q Signature: (e, s) • Public key: y and satisfying y = gx mod p n n Verification: q q 2003/12/8 find r’ = gsye mod p verify h(r’, m) = e ? (Hint: gsye=g k-xe gxe = gk ) 4
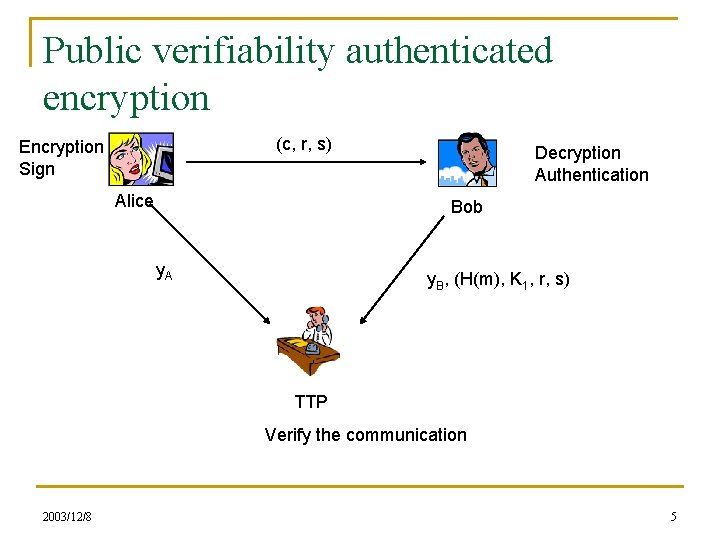
Public verifiability authenticated encryption (c, r, s) Encryption Sign Alice Decryption Authentication Bob y. A y. B, (H(m), K 1, r, s) TTP Verify the communication 2003/12/8 5
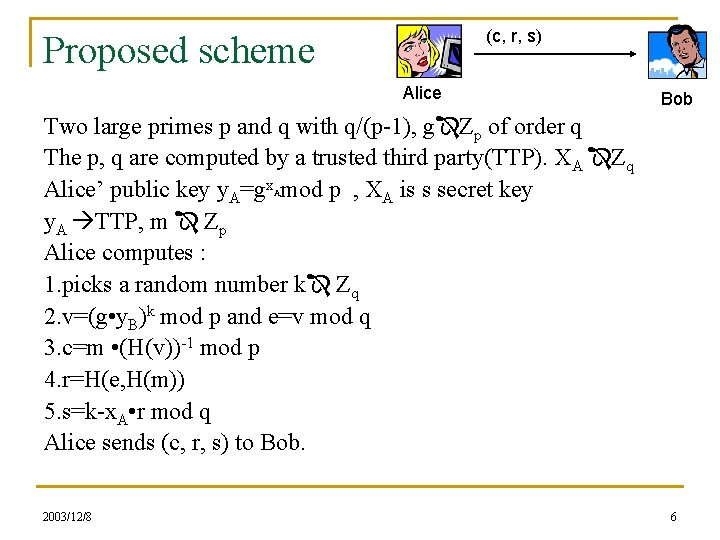
(c, r, s) Proposed scheme Alice Bob Two large primes p and q with q/(p-1), g Zp of order q The p, q are computed by a trusted third party(TTP). XA Zq Alice’ public key y. A=gx mod p , XA is s secret key y. A TTP, m Zp Alice computes : 1. picks a random number k Zq 2. v=(g • y. B)k mod p and e=v mod q 3. c=m • (H(v))-1 mod p 4. r=H(e, H(m)) 5. s=k-x. A • r mod q Alice sends (c, r, s) to Bob. A 2003/12/8 6
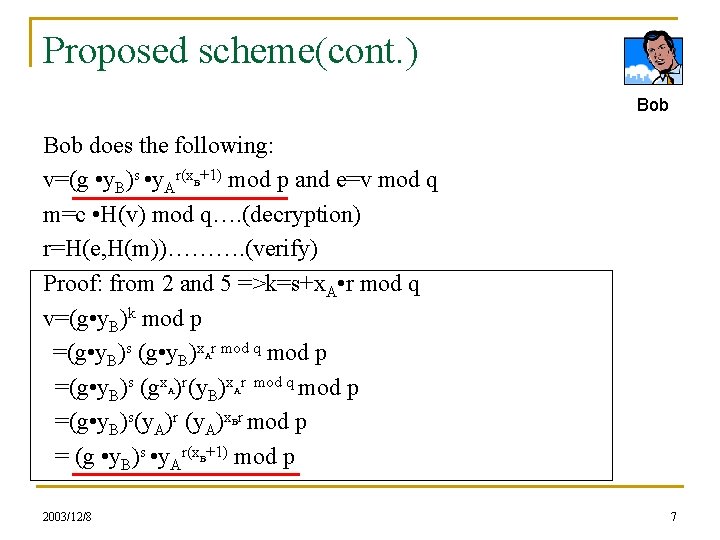
Proposed scheme(cont. ) Bob does the following: v=(g • y. B)s • y. Ar(x +1) mod p and e=v mod q m=c • H(v) mod q…. (decryption) r=H(e, H(m))………. (verify) Proof: from 2 and 5 =>k=s+x. A • r mod q v=(g • y. B)k mod p =(g • y. B)s (g • y. B)x r mod q mod p =(g • y. B)s (gx )r(y. B)x r mod q mod p =(g • y. B)s(y. A)r (y. A)x r mod p = (g • y. B)s • y. Ar(x +1) mod p B A A A B B 2003/12/8 7
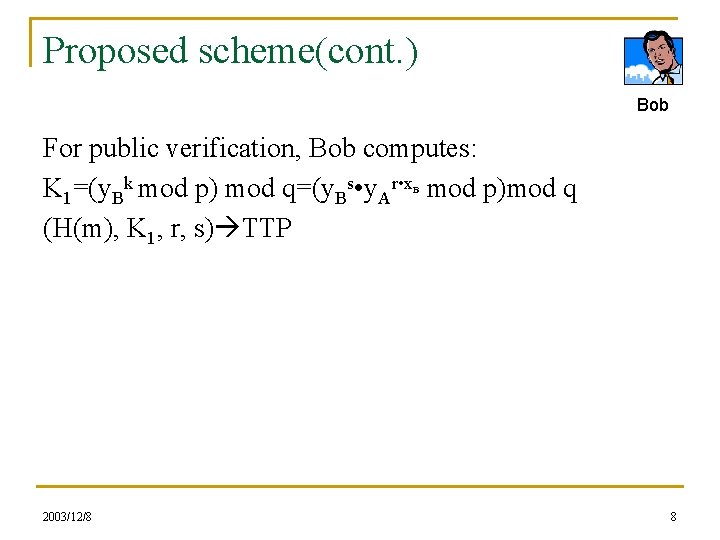
Proposed scheme(cont. ) Bob For public verification, Bob computes: K 1=(y. Bk mod p) mod q=(y. Bs • y. Ar • x mod p)mod q (H(m), K 1, r, s) TTP B 2003/12/8 8
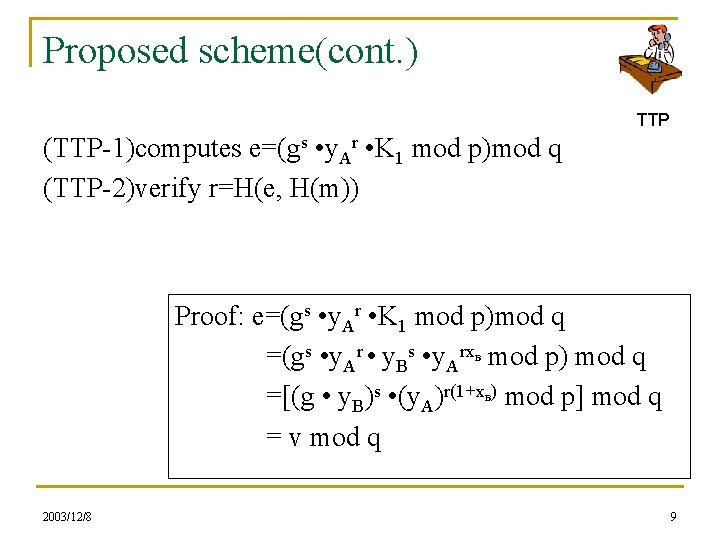
Proposed scheme(cont. ) TTP (TTP-1)computes e=(gs • y. Ar • K 1 mod p)mod q (TTP-2)verify r=H(e, H(m)) Proof: e=(gs • y. Ar • K 1 mod p)mod q =(gs • y. Ar • y. Bs • y. Arx mod p) mod q =[(g • y. B)s • (y. A)r(1+x ) mod p] mod q = v mod q B B 2003/12/8 9
Small message transmission n n Alice partitions message m into (|P|-1)-bit blocks m 1, m 2, …, mi She computes the ciphertext c 1, c 2, …, ci by ci=(mi cli-1) • (H(v))-1 mod p (where cli denotes the most left (|P|-1) bits of ci and c 0=v) Alice then sends (c 1, c 2, …, ci , r, s) to Bob. The rest of the scheme can be modified correspondingly. 2003/12/8 10
Security considerations n Unforgeability q q n Dishonest Bob can computes (m, r, s). The latter is equivalent to the Schnorr’s digital signature. Non-repudiation q q q 2003/12/8 Once Bob computes K 1 Every can verify the signature(r, s) of the message m Without divulging Bob’s private key and the message m 11
Security considerations(cont. ) n Confidentiality q q n Intruder must can x. B or k Once can know K 1 and computes e, but it is infeasible to compute v. Efficiency q q q 2003/12/8 Alice : one exponentiation mod p, one inversion mod p, and three hash function evaluations. Bob : two exponentiation mod p, and three hash function evaluations. The communication overhead between sender and receiver is |H|+|q| bits, for public verification being 2(|H|+|q|) bits. 12
Conclusion n Public verifiability n Authentication Encryption Non-repudiation Efficiency n n n 2003/12/8 13
- Slides: 13