IOEfficient Construction of Constrained Delaunay Triangulations Pankaj K
![Extending the Plane Secondary sheet Primary sheet [Seidel, 1989] Extending the Plane Secondary sheet Primary sheet [Seidel, 1989]](https://slidetodoc.com/presentation_image_h2/52eed0d581ad7f445a65984bb416edcf/image-21.jpg)
![Extending the Plane Secondary sheets Primary sheet [Seidel, 1989] Extending the Plane Secondary sheets Primary sheet [Seidel, 1989]](https://slidetodoc.com/presentation_image_h2/52eed0d581ad7f445a65984bb416edcf/image-22.jpg)
![Traveling Rule x Secondary sheets z y Primary sheet [Seidel, 1989] Traveling Rule x Secondary sheets z y Primary sheet [Seidel, 1989]](https://slidetodoc.com/presentation_image_h2/52eed0d581ad7f445a65984bb416edcf/image-23.jpg)
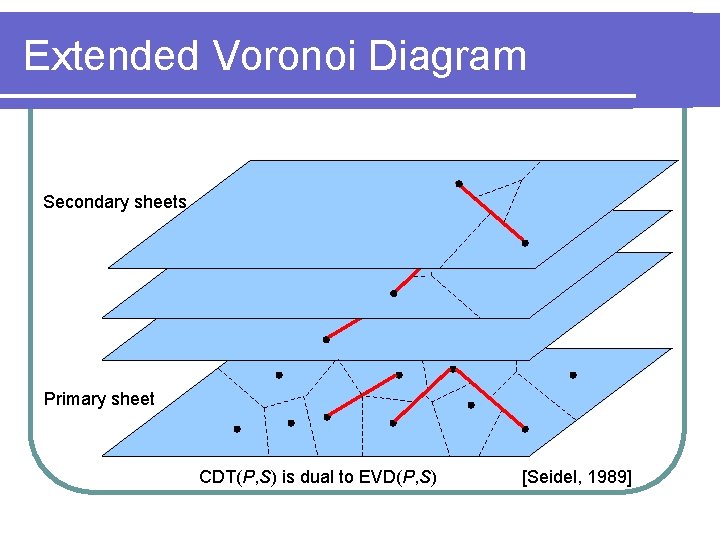
![Extended Voronoi Diagram Secondary sheets Primary sheet p [Seidel, 1989] Extended Voronoi Diagram Secondary sheets Primary sheet p [Seidel, 1989]](https://slidetodoc.com/presentation_image_h2/52eed0d581ad7f445a65984bb416edcf/image-24.jpg)
- Slides: 26
I/O-Efficient Construction of Constrained Delaunay Triangulations Pankaj K. Agarwal, Lars Arge, and Ke Yi Duke University
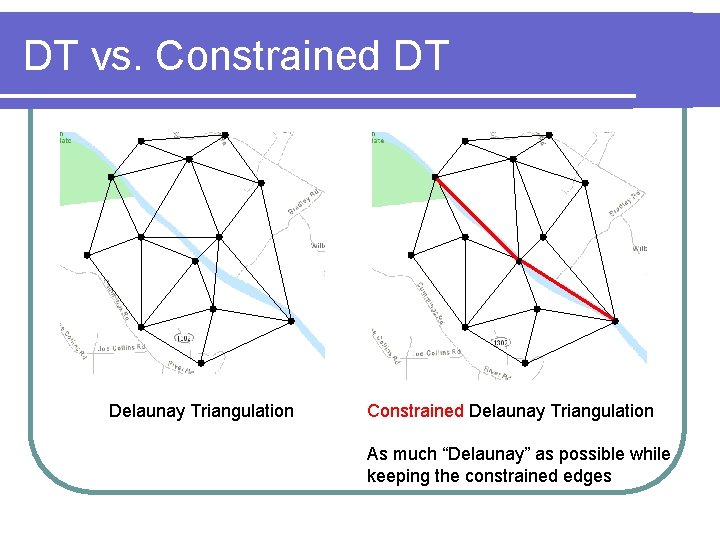
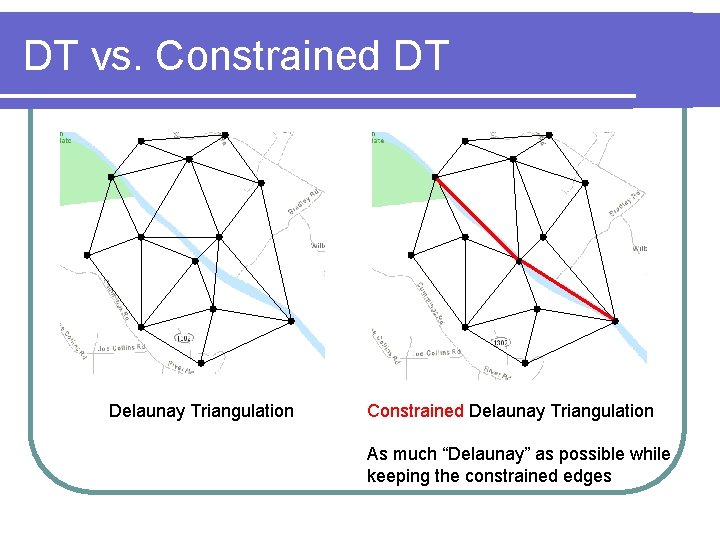
DT vs. Constrained DT Delaunay Triangulation Constrained Delaunay Triangulation As much “Delaunay” as possible while keeping the constrained edges
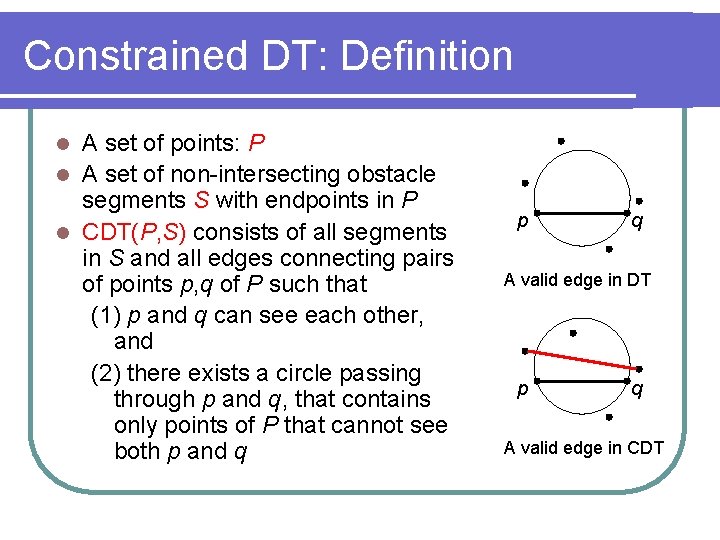
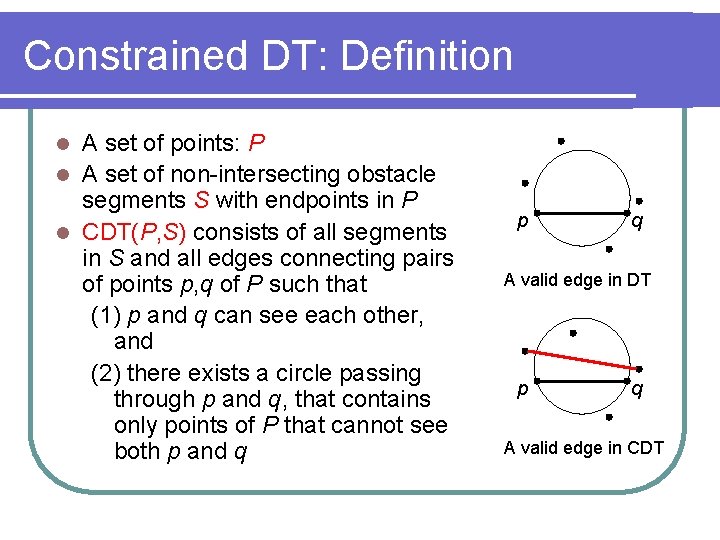
Constrained DT: Definition A set of points: P l A set of non-intersecting obstacle segments S with endpoints in P l CDT(P, S) consists of all segments in S and all edges connecting pairs of points p, q of P such that (1) p and q can see each other, and (2) there exists a circle passing through p and q, that contains only points of P that cannot see both p and q l p q A valid edge in DT p q A valid edge in CDT
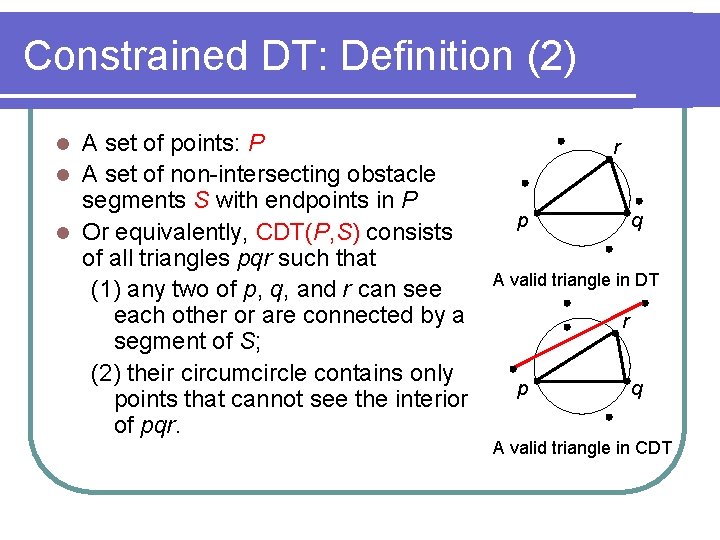
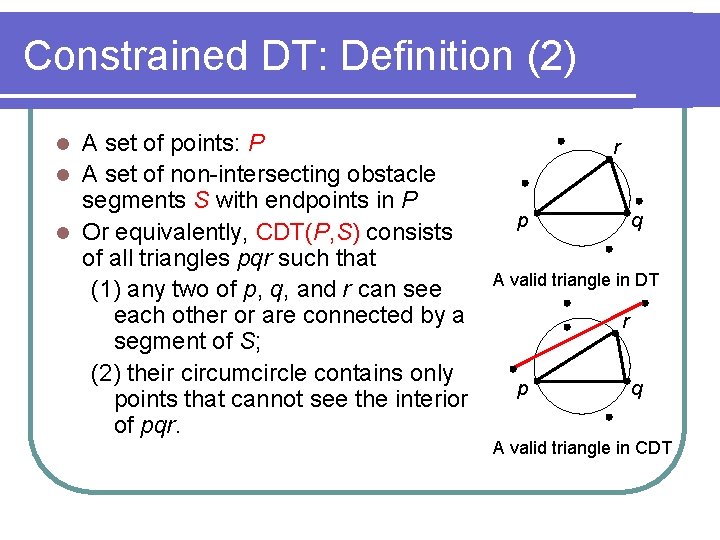
Constrained DT: Definition (2) A set of points: P l A set of non-intersecting obstacle segments S with endpoints in P l Or equivalently, CDT(P, S) consists of all triangles pqr such that (1) any two of p, q, and r can see each other or are connected by a segment of S; (2) their circumcircle contains only points that cannot see the interior of pqr. l r p q A valid triangle in DT r p q A valid triangle in CDT
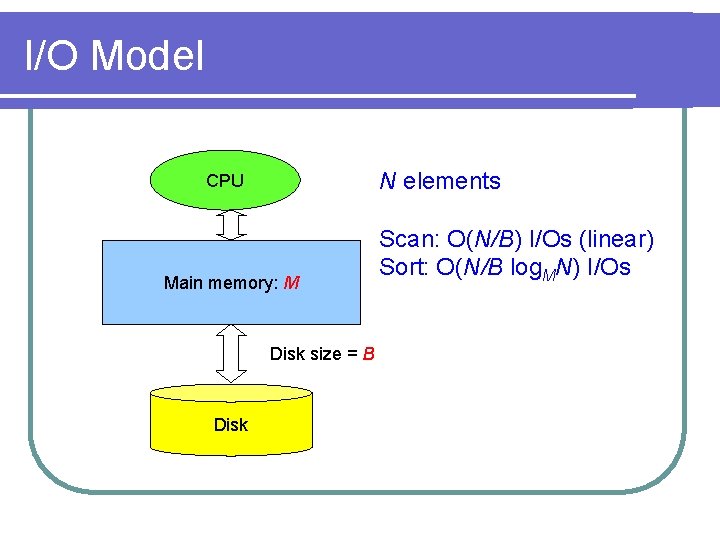
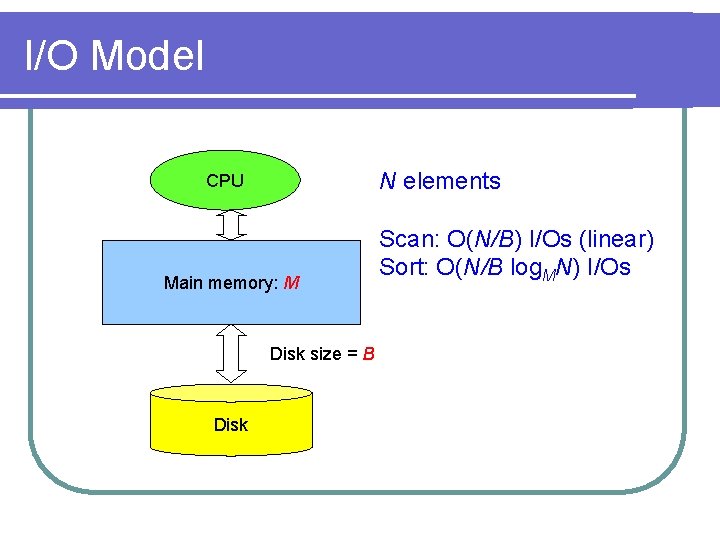
I/O Model N elements CPU Main memory: M Disk size = B Disk Scan: O(N/B) I/Os (linear) Sort: O(N/B log. MN) I/Os
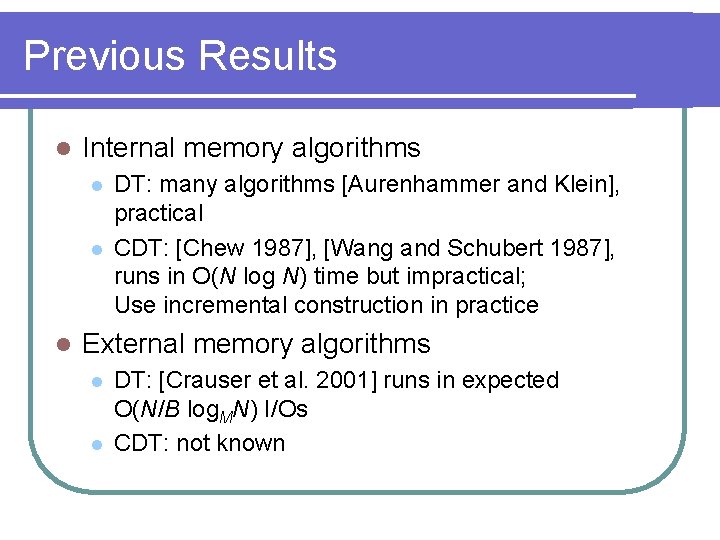
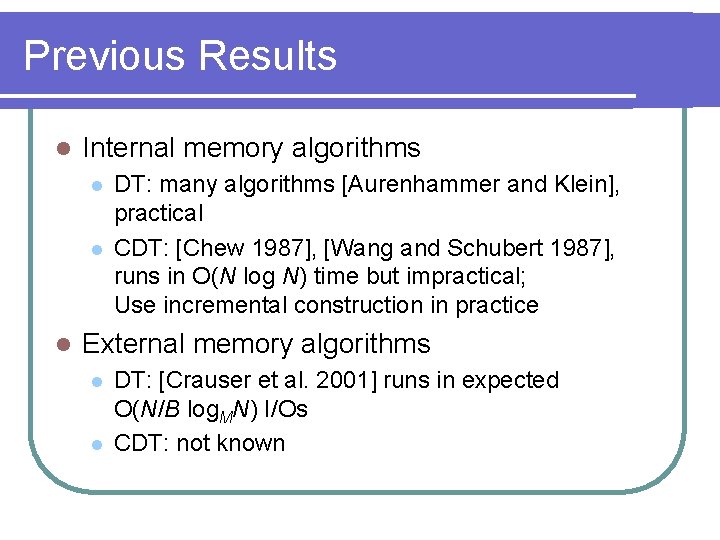
Previous Results l Internal memory algorithms l l l DT: many algorithms [Aurenhammer and Klein], practical CDT: [Chew 1987], [Wang and Schubert 1987], runs in O(N log N) time but impractical; Use incremental construction in practice External memory algorithms l l DT: [Crauser et al. 2001] runs in expected O(N/B log. MN) I/Os CDT: not known
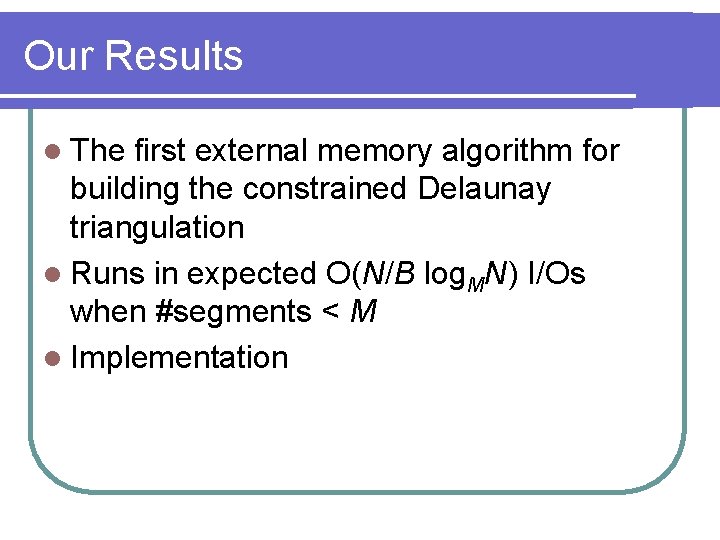
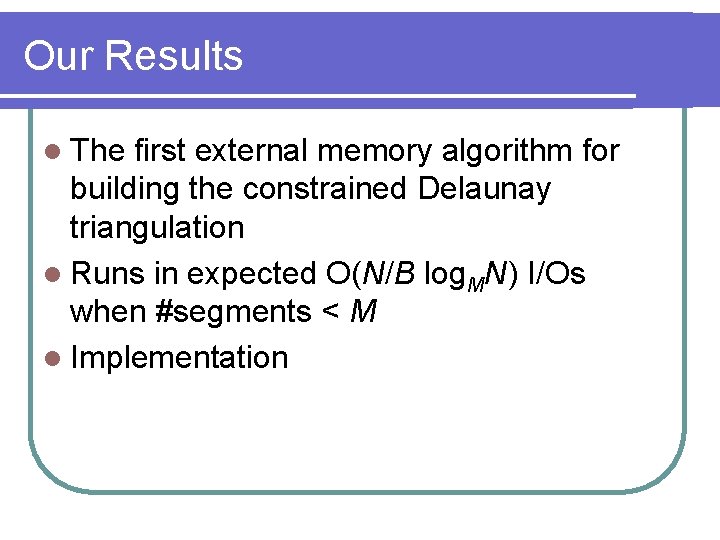
Our Results l The first external memory algorithm for building the constrained Delaunay triangulation l Runs in expected O(N/B log. MN) I/Os when #segments < M l Implementation
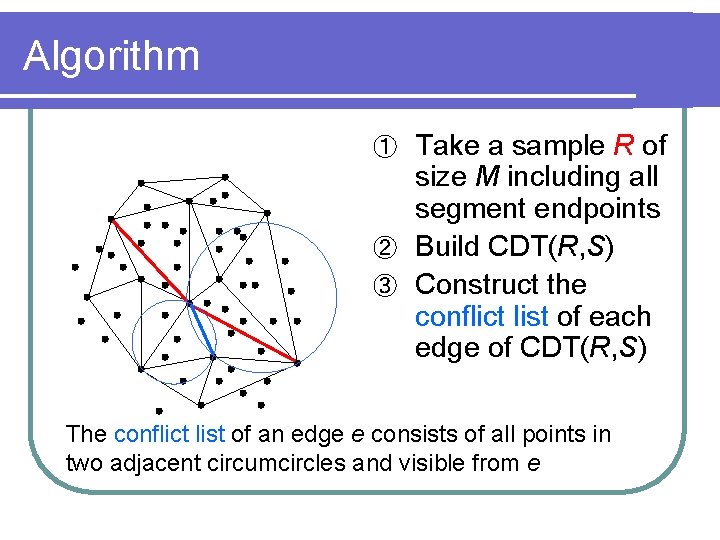
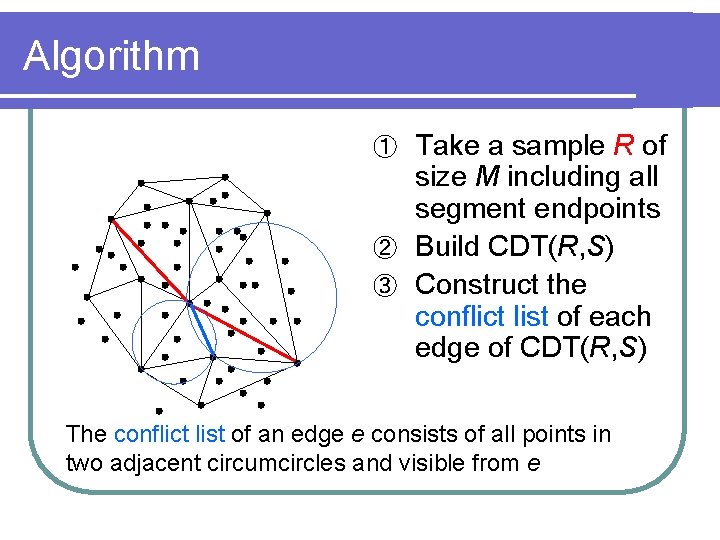
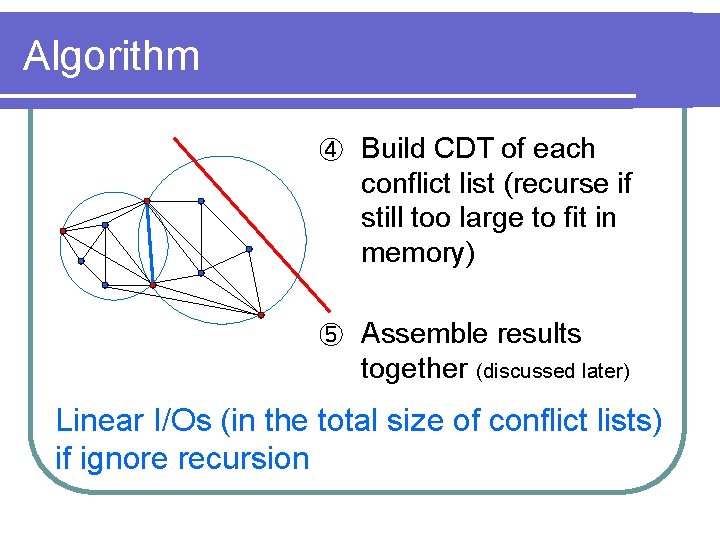
Algorithm Take a sample R of size M including all segment endpoints ② Build CDT(R, S) ③ Construct the conflict list of each edge of CDT(R, S) ① The conflict list of an edge e consists of all points in two adjacent circumcircles and visible from e
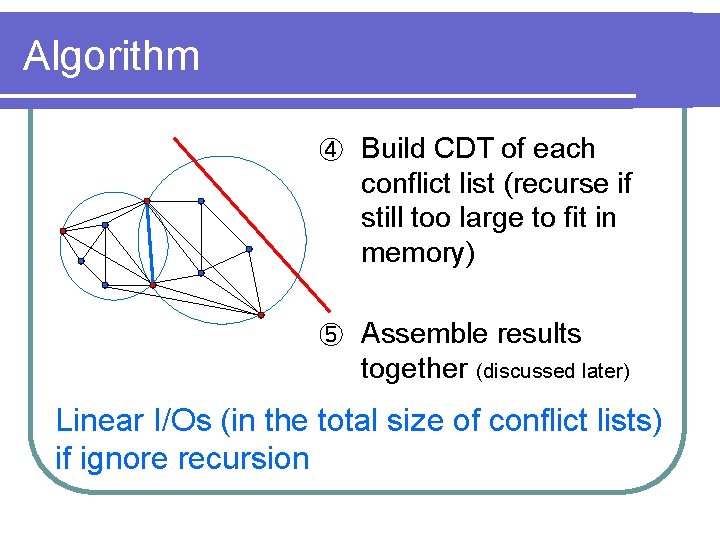
Algorithm ④ Build CDT of each conflict list (recurse if still too large to fit in memory) ⑤ Assemble results together (discussed later) Linear I/Os (in the total size of conflict lists) if ignore recursion
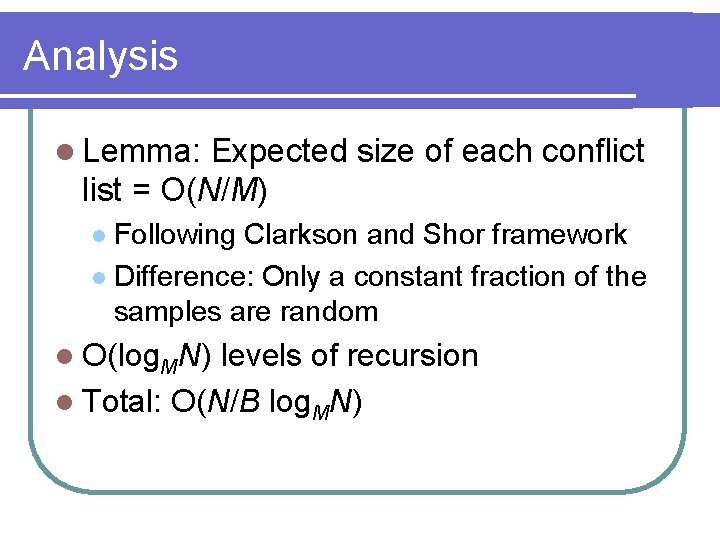
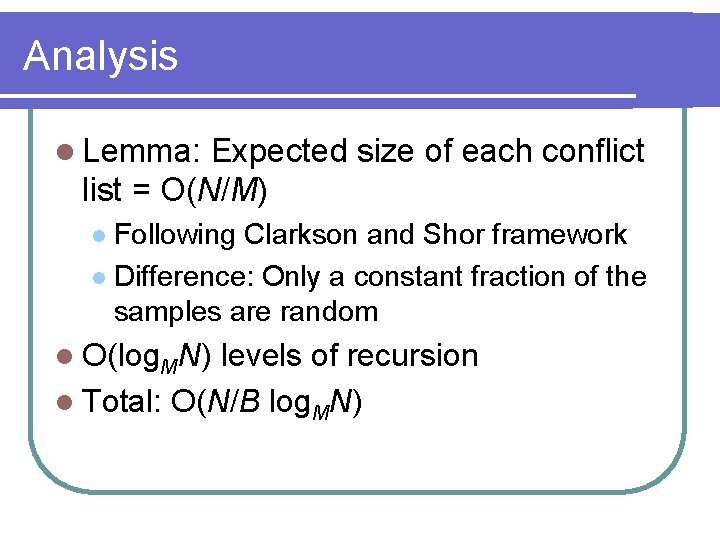
Analysis l Lemma: Expected size of each conflict list = O(N/M) Following Clarkson and Shor framework l Difference: Only a constant fraction of the samples are random l l O(log. MN) levels of recursion l Total: O(N/B log. MN)
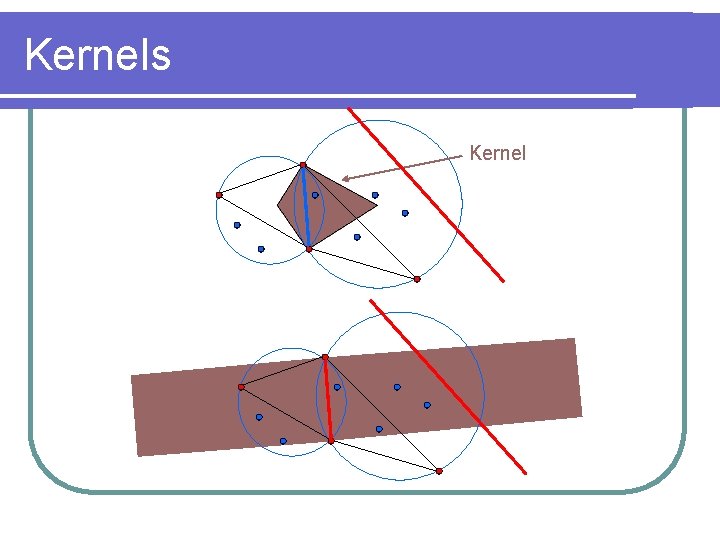
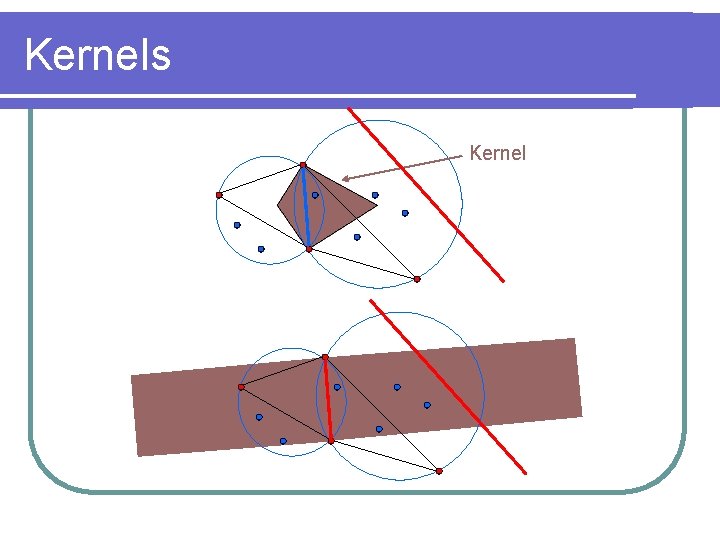
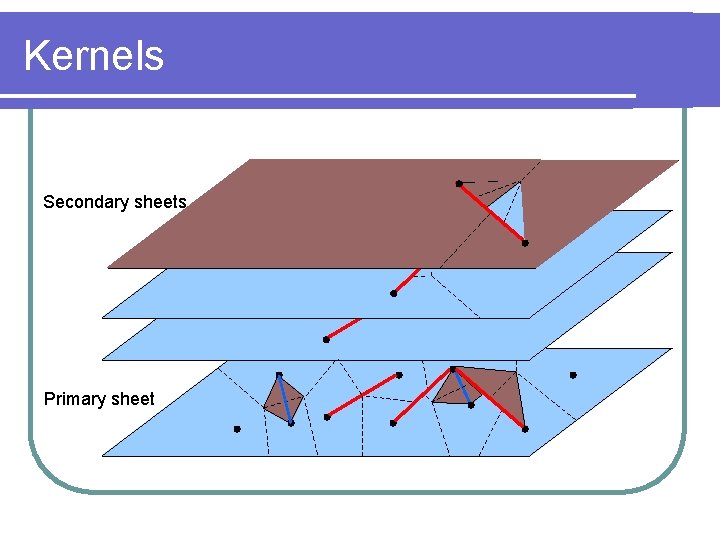
Kernels Kernel
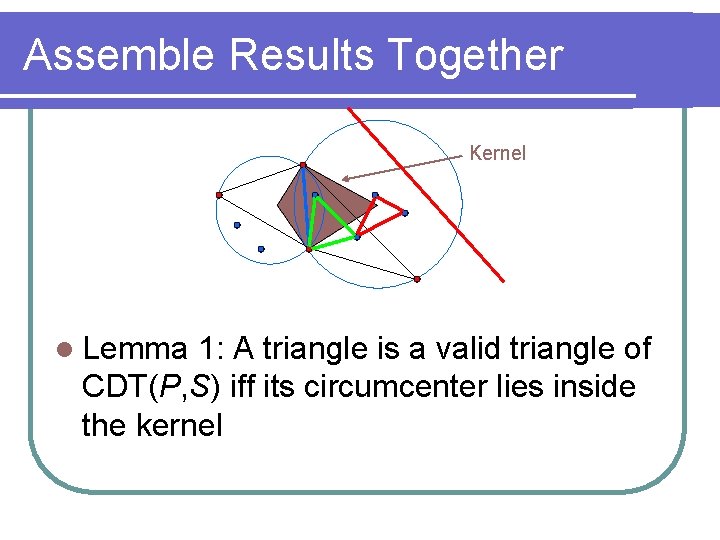
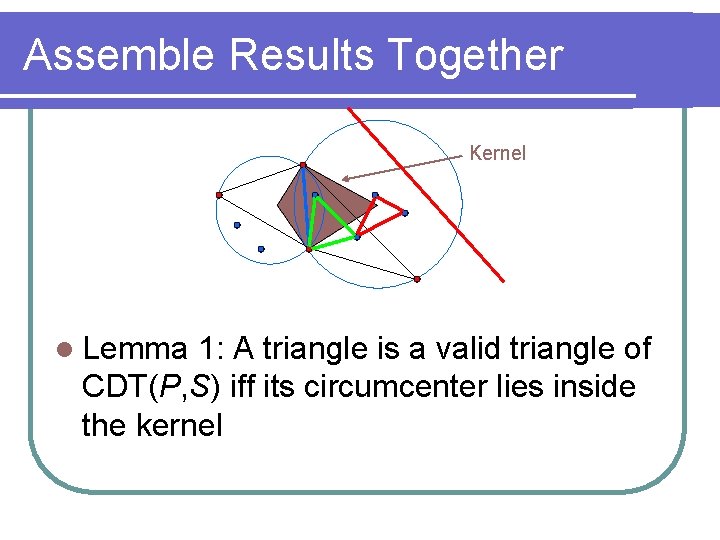
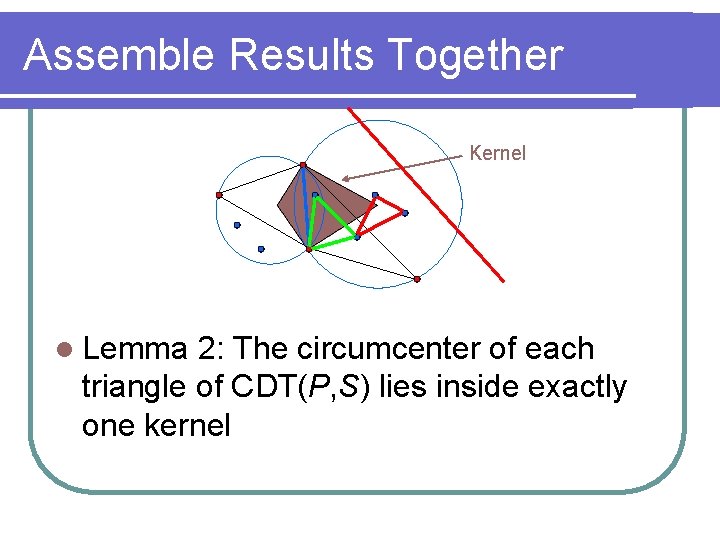
Assemble Results Together Kernel l Lemma 1: A triangle is a valid triangle of CDT(P, S) iff its circumcenter lies inside the kernel
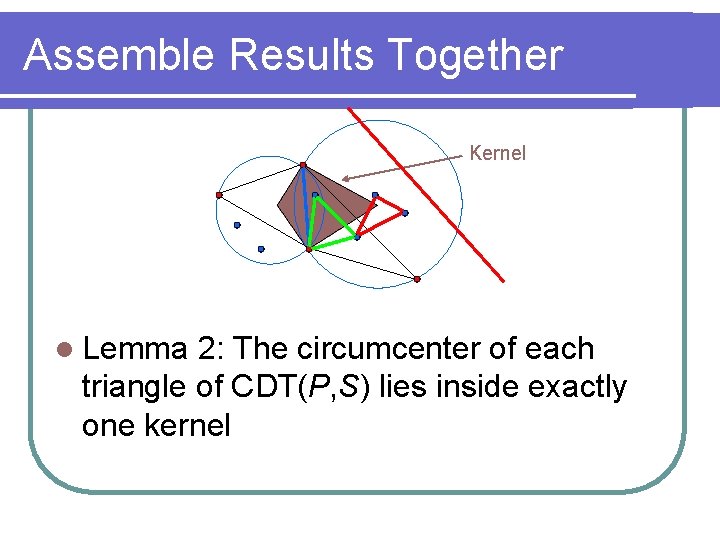
Assemble Results Together Kernel l Lemma 2: The circumcenter of each triangle of CDT(P, S) lies inside exactly one kernel
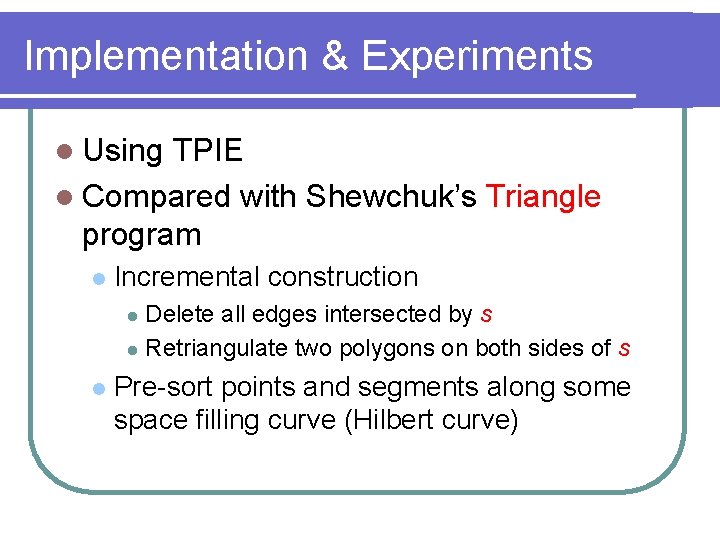
Implementation & Experiments l Using TPIE l Compared with Shewchuk’s Triangle program l Incremental construction Delete all edges intersected by s l Retriangulate two polygons on both sides of s l l Pre-sort points and segments along some space filling curve (Hilbert curve)
Experiment: Uniform Data 10 million points Varying #segments Ave segment length = 0. 003 Memory: 128 M
Experiment: Segment Length 10 million points 10, 000 segments Varying segment length Memory: 128 M
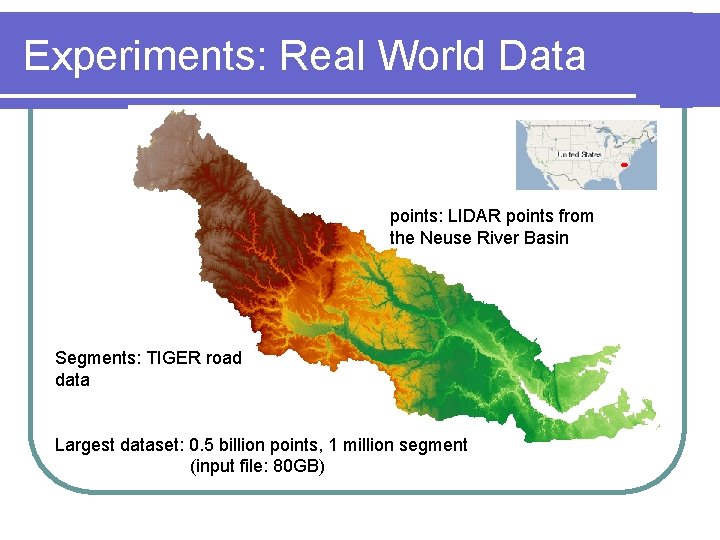
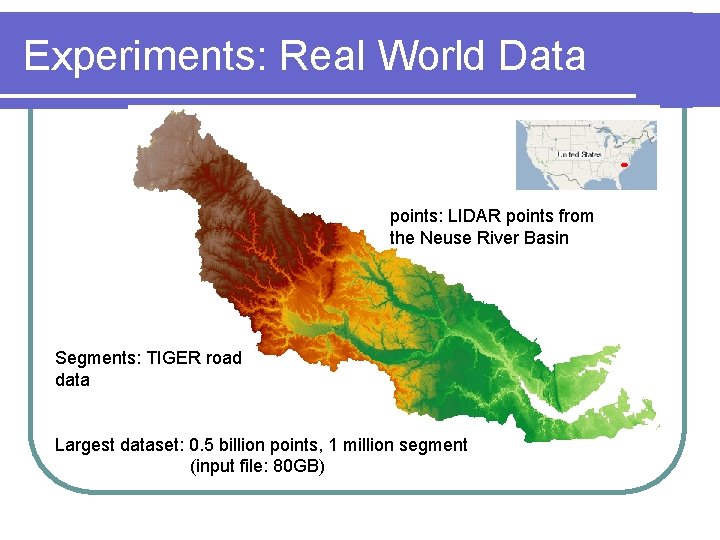
Experiments: Real World Data points: LIDAR points from the Neuse River Basin Segments: TIGER road data Largest dataset: 0. 5 billion points, 1 million segment (input file: 80 GB)
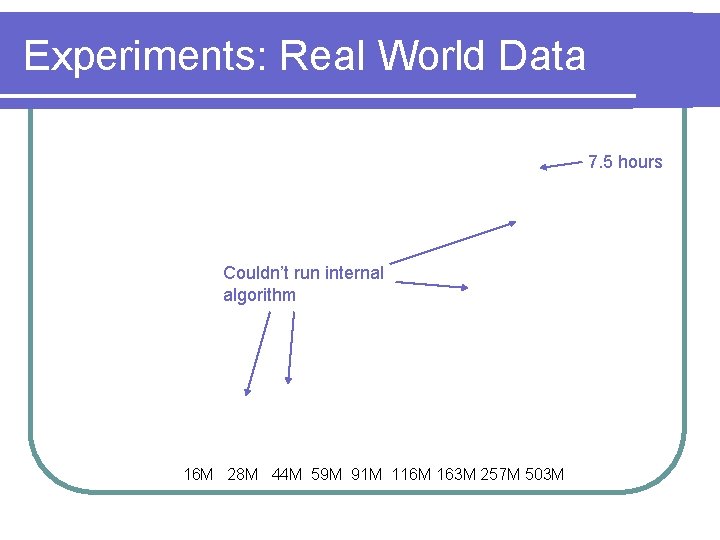
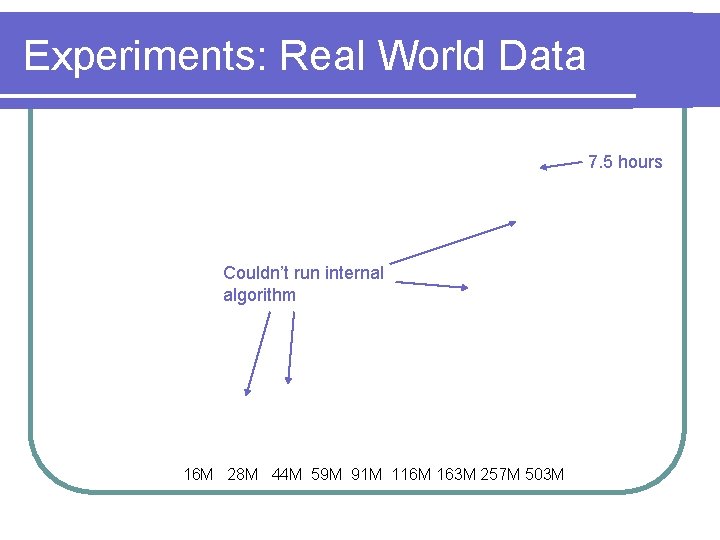
Experiments: Real World Data 7. 5 hours Couldn’t run internal algorithm 16 M 28 M 44 M 59 M 91 M 116 M 163 M 257 M 503 M
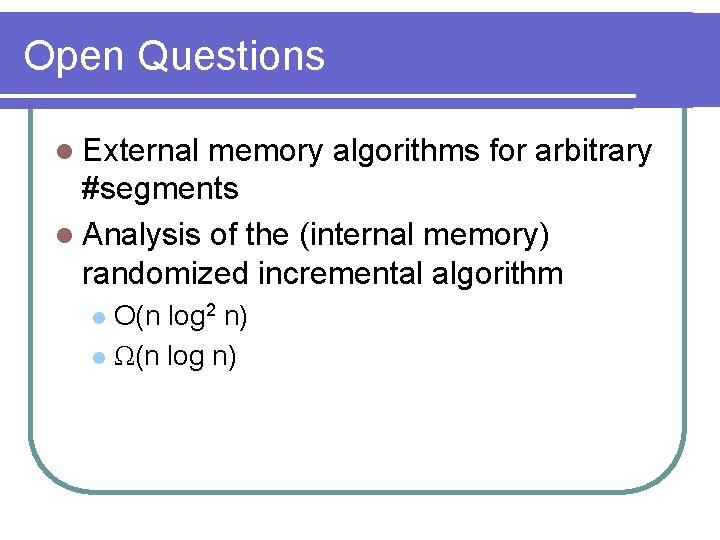
Open Questions l External memory algorithms for arbitrary #segments l Analysis of the (internal memory) randomized incremental algorithm O(n log 2 n) l Ω(n log n) l
Thank you!
![Extending the Plane Secondary sheet Primary sheet Seidel 1989 Extending the Plane Secondary sheet Primary sheet [Seidel, 1989]](https://slidetodoc.com/presentation_image_h2/52eed0d581ad7f445a65984bb416edcf/image-21.jpg)
Extending the Plane Secondary sheet Primary sheet [Seidel, 1989]
![Extending the Plane Secondary sheets Primary sheet Seidel 1989 Extending the Plane Secondary sheets Primary sheet [Seidel, 1989]](https://slidetodoc.com/presentation_image_h2/52eed0d581ad7f445a65984bb416edcf/image-22.jpg)
Extending the Plane Secondary sheets Primary sheet [Seidel, 1989]
![Traveling Rule x Secondary sheets z y Primary sheet Seidel 1989 Traveling Rule x Secondary sheets z y Primary sheet [Seidel, 1989]](https://slidetodoc.com/presentation_image_h2/52eed0d581ad7f445a65984bb416edcf/image-23.jpg)
Traveling Rule x Secondary sheets z y Primary sheet [Seidel, 1989]
![Extended Voronoi Diagram Secondary sheets Primary sheet p Seidel 1989 Extended Voronoi Diagram Secondary sheets Primary sheet p [Seidel, 1989]](https://slidetodoc.com/presentation_image_h2/52eed0d581ad7f445a65984bb416edcf/image-24.jpg)
Extended Voronoi Diagram Secondary sheets Primary sheet p [Seidel, 1989]
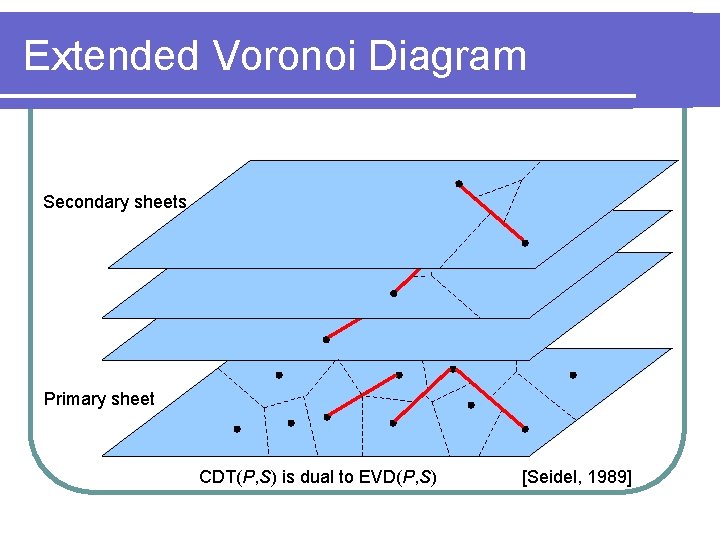
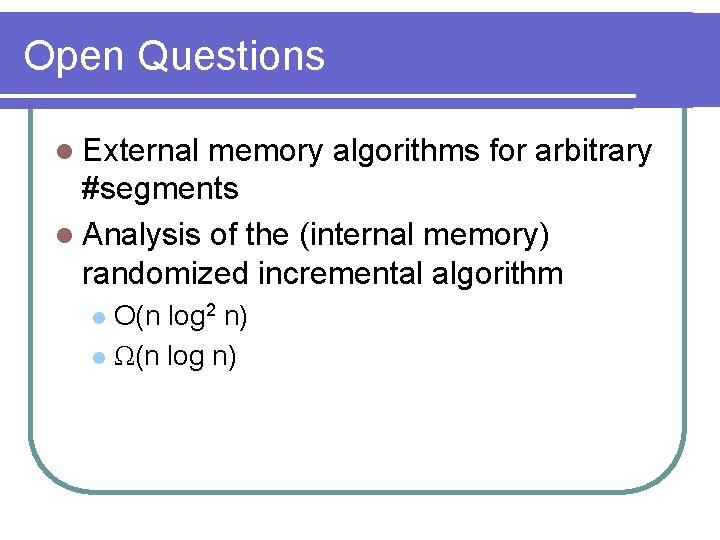
Extended Voronoi Diagram Secondary sheets Primary sheet CDT(P, S) is dual to EVD(P, S) [Seidel, 1989]
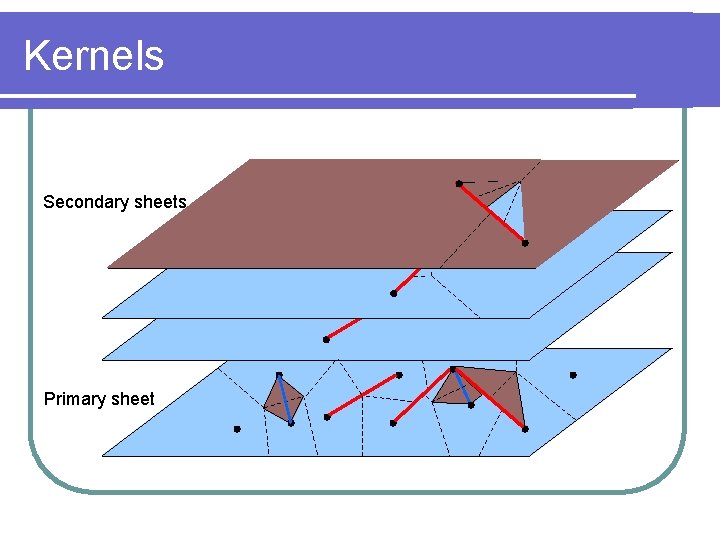
Kernels Secondary sheets Primary sheet