CLOUD STORAGE SECURITY Prepared By Hiral Vashi What
CLOUD STORAGE SECURITY Prepared By: Hiral Vashi
What is cloud storage? • Cloud storage is a cloud computing model in which data is stored on remote servers accessed from the Internet. • It is maintained, operated and managed by a cloud storage service provider on a storage servers that are built on virtualization techniques.
Cloud Storage (cont. ) • Several large web companies are now exploiting the fact that they have data storage capacity that can be hired out to others. • Allows data stored remotely to be temporarily cached on desktop computers, mobile phones or other internetlinked devices. • Amazon’s elastic compute cloud (ec 2) and simple storage solution (s 3) are well known examples
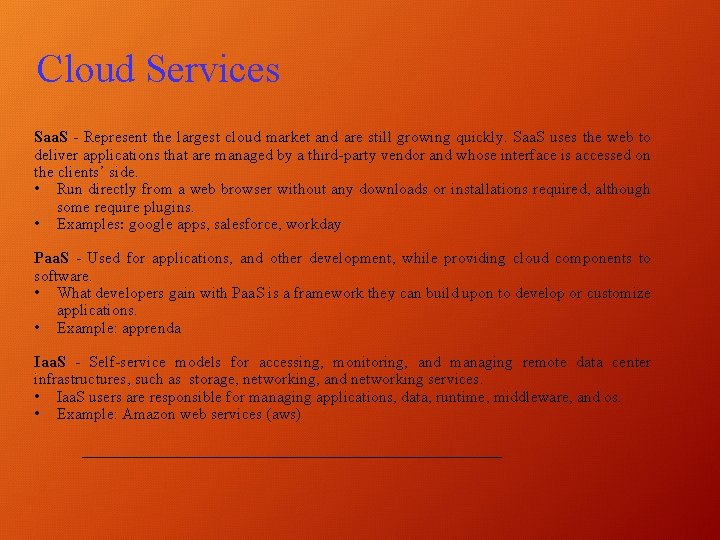
Cloud Services Saa. S - Represent the largest cloud market and are still growing quickly. Saa. S uses the web to deliver applications that are managed by a third-party vendor and whose interface is accessed on the clients’ side. • Run directly from a web browser without any downloads or installations required, although some require plugins. • Examples: google apps, salesforce, workday Paa. S - Used for applications, and other development, while providing cloud components to software. • What developers gain with Paa. S is a framework they can build upon to develop or customize applications. • Example: apprenda Iaa. S - Self-service models for accessing, monitoring, and managing remote data center infrastructures, such as storage, networking, and networking services. • Iaa. S users are responsible for managing applications, data, runtime, middleware, and os. • Example: Amazon web services (aws)
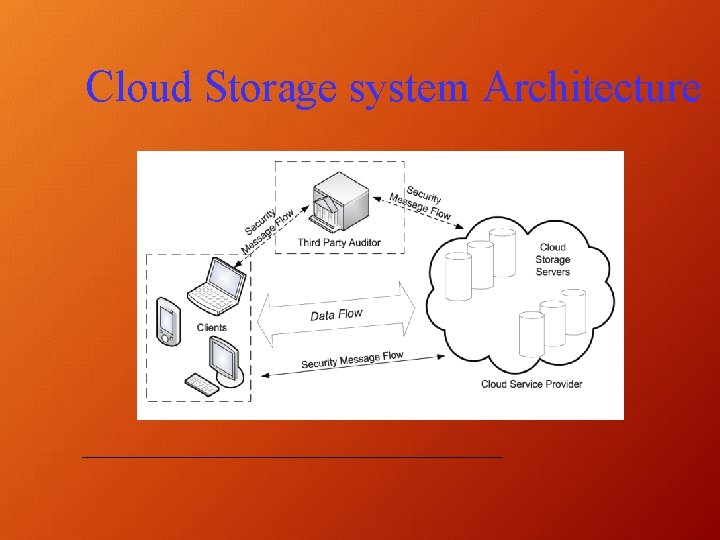
Cloud Storage system Architecture
Security Requirement • • Data confidentiality Collusion resistance User revocation Scalability
Data Storage Security techniques in Cloud computing Implicit Storage Security to Data in Online: • Data is partitioned in implicitly secured manner and those are not on encrypted format. • Portions are stored on various servers on the network (known for the user) • Partitioned data pieces cannot reveal any user information. • In case user forgot in which server the partitioned data is stored, it will become difficult to reconstruct original data.
Data Storage Security techniques in Cloud computing Identify –Based Authentication: • To encrypt a message using the recipient’s identity as a public key • Resources and services are distributed in this scheme over numerous users. So there is a chance of more security risks in this scheme. Effective and Secure Storage Protocol: • A secure and efficient storage protocol is proposed that will guarantees of confidentiality and integrity of stored data on server
Data Storage Security techniques in Cloud computing Dynamically Store Data: • Clients did not have local copy of data stored in cloud • Data reading protocol algorithm to check the data integrity services providers help the clients to check the data security File storage security management: • It is a system consists of a master server and a set of slave server. • Not direct commutation link between clients and slave servers in the proposed model. • Master server is responsible to process the client’s request and at slave server chunking operation in order to provide data backup for file recovery in future.
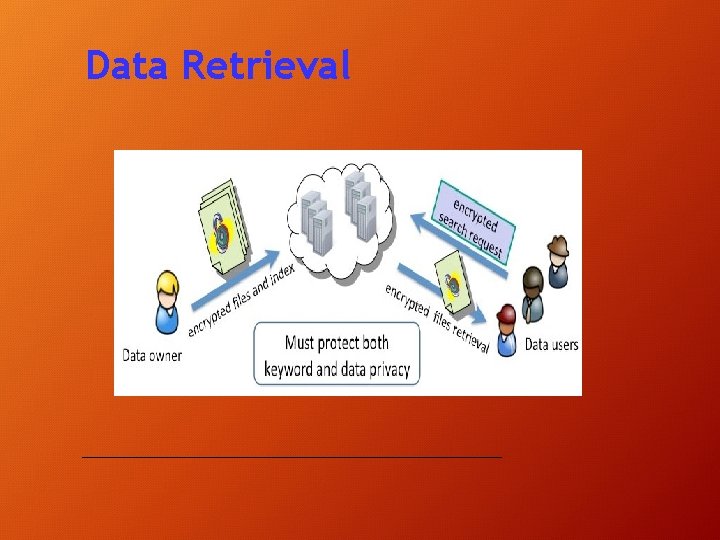
Data Retrieval
Searchable Encryption Definition: A cryptographic technique that allows search of specific information in an encrypted content. • A message exchange process between sender and receiver will be perform by mail server. Symmetric searchable encryption (SSE) • A user encrypts the information utilizing symmetric/private key encryption schemes (e. g. AES) before outsourcing it to the cloud server. Asymmetric searchable encryption (ASE): • ASE schemes are suitable in any setting where the party searching over the data is unique in relation to the party that creates it.
Attribute-based Encryption § Attribute based encryption is a type of public key encryption in which the secret key of a user and cipher text are depend upon the attributes. § The decryption of a cipher text is possible only if the set of attributes of the user key matches the attributes of the cipher text. § There are mainly two types of Attribute-Based Encryption schemes: 1. Key-Policy Attribute-Based Encryption (KP-ABE) 2. Cipher text-Policy Attribute-Based Encryption (CP-ABE). • In KP-ABE, users' secret keys are generated based on an access tree that defines the privileges scope of the concerned user, and data are encrypted over a set of attribute. • CP-ABE uses access trees to encrypt data and users' secret keys are generated over a set of attribute.
Thank You
- Slides: 13