Chapter 18 OneWay Hash Functions Based on Schneier
Chapter 18: One-Way Hash Functions Based on Schneier
Background • M, message of arbitrary size • Hash function H(M) returns a value h of m bits: h = H(M) • Characteristics of H(M) – Easy to compute h – Hard to compute M given h – Hard to find another message, M’ such that H(M) = H(M’) • Birthday attack – Find any two messages M and M’ such that H(M) = H(M’) • To survive a birthday attack, most one-way hash functions produce 128 -bit or larger hashes
Overview of One-way Hash Functions • Built-on idea of compression function • Divide a message into blocks • Hash of block Mi is hi = f(Mi, hi-1) • Hash of the last block is the hash of the entire message
MD 5 • Message digest version 5, an extension of MD 4 • Produces 128 -bit hash • Conjectured that it is computationally infeasible to produce two messages having the same message digest • Intended for digital signature applications
Terminology and Notation • "word“ – A 32 -bit quantity, a group of four bytes with the loworder (least significant) byte given first • “+” – Denotes addition of words, mod 232 • X << s – Circular shifting (rotating) bits of X by s positions
MD 5 Algorithm Description • Message of b bits as m 0, m 1, . . . mb-1 • Step 1. Append Padding Bits – A single “ 1” bit appended and then “ 0” bits are appended so that the length in bits of the padded message becomes congruent to 448 mod 512 – Padding is always performed, even if the length is already congruent to 448 mod 512 – In all at least one bit and at most 512 bits are appended
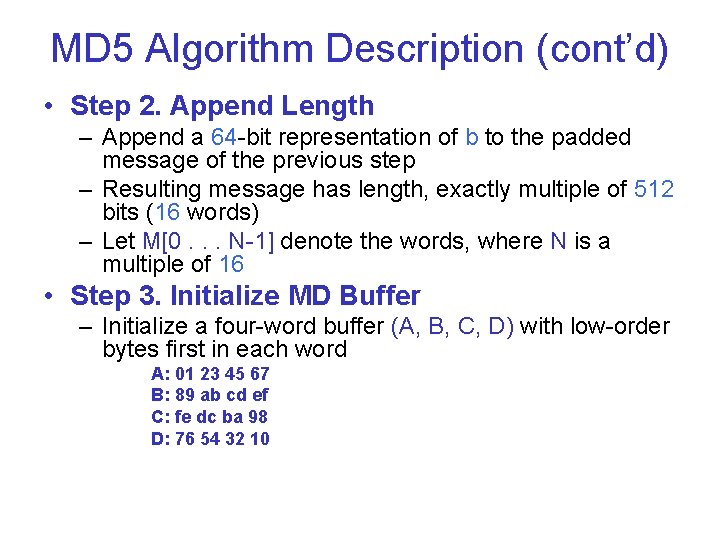
MD 5 Algorithm Description (cont’d) • Step 2. Append Length – Append a 64 -bit representation of b to the padded message of the previous step – Resulting message has length, exactly multiple of 512 bits (16 words) – Let M[0. . . N-1] denote the words, where N is a multiple of 16 • Step 3. Initialize MD Buffer – Initialize a four-word buffer (A, B, C, D) with low-order bytes first in each word A: 01 23 45 67 B: 89 ab cd ef C: fe dc ba 98 D: 76 54 32 10
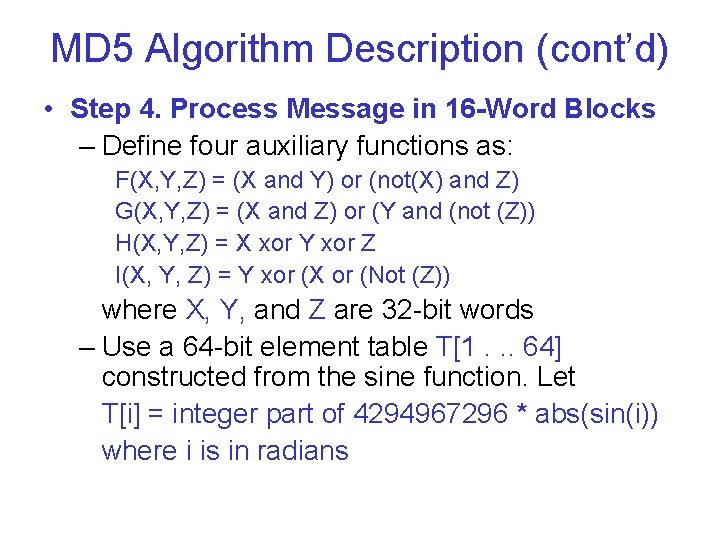
MD 5 Algorithm Description (cont’d) • Step 4. Process Message in 16 -Word Blocks – Define four auxiliary functions as: F(X, Y, Z) = (X and Y) or (not(X) and Z) G(X, Y, Z) = (X and Z) or (Y and (not (Z)) H(X, Y, Z) = X xor Y xor Z I(X, Y, Z) = Y xor (X or (Not (Z)) where X, Y, and Z are 32 -bit words – Use a 64 -bit element table T[1. . . 64] constructed from the sine function. Let T[i] = integer part of 4294967296 * abs(sin(i)) where i is in radians
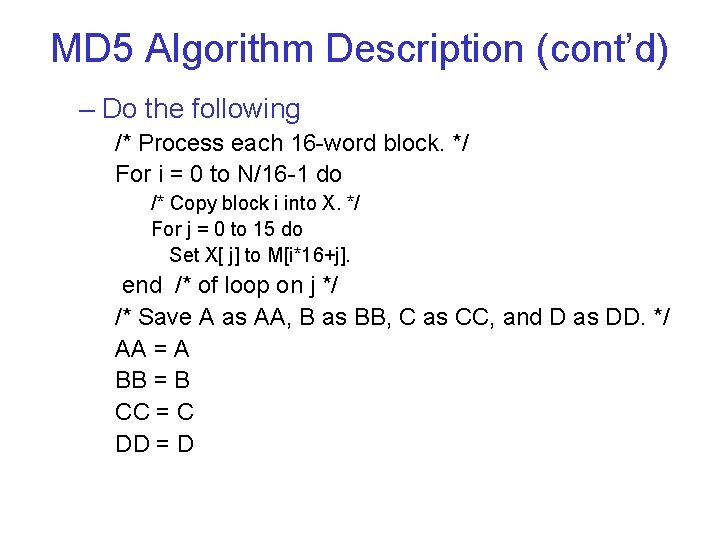
MD 5 Algorithm Description (cont’d) – Do the following /* Process each 16 -word block. */ For i = 0 to N/16 -1 do /* Copy block i into X. */ For j = 0 to 15 do Set X[ j] to M[i*16+j]. end /* of loop on j */ /* Save A as AA, B as BB, C as CC, and D as DD. */ AA = A BB = B CC = C DD = D

MD 5 Algorithm Description (cont’d) /* Round 1. */ /* Let [abcd k s i] denote the operation a = b + ((a + F(b, c, d) + X[k] + T[i]) <<< s). */ /* Do the following 16 operations. */ [ABCD 0 7 1] [ABCD 4 7 5] [ABCD 8 7 9] [ABCD 12 7 13] [DABC 1 12 2] [CDAB 2 17 3] [BCDA 3 22 4] 5 12 6] [CDAB 6 17 7] [BCDA 7 22 8] 9 12 10] [CDAB 10 17 11] [BCDA 11 22 12] 13 12 14] [CDAB 14 17 15] [BCDA 15 22 16] /* Round 2. */ /* Let [abcd k s i] denote the operation a = b + ((a + G(b, c, d) + X[k] + T[i]) <<< s). */ /* Do the following 16 operations. */ [ABCD 1 5 17] [DABC 6 9 18] [CDAB 11 14 19] [BCDA 0 20 20] [ABCD 5 5 21] [DABC 10 9 22] [CDAB 15 14 23] [BCDA 4 20 24] [ABCD 9 5 25] [DABC 14 9 26] [CDAB 3 14 27] [BCDA 8 20 28] [ABCD 13 5 29] [DABC 2 9 30] [CDAB 7 14 31] [BCDA 12 20 32]
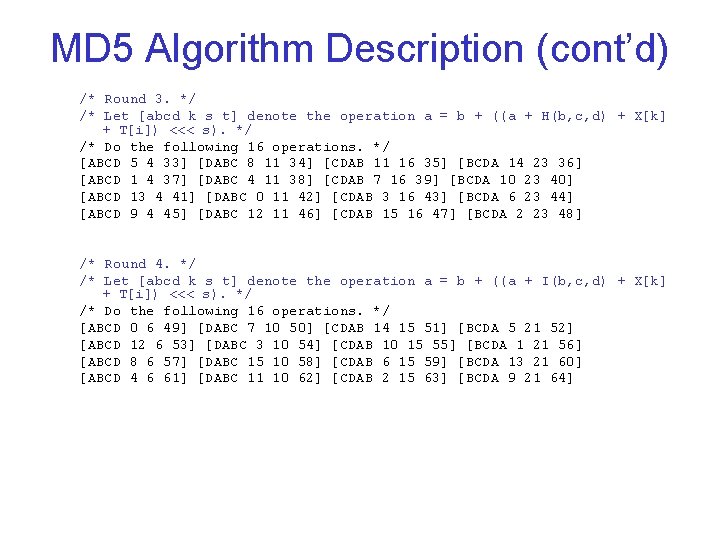
MD 5 Algorithm Description (cont’d) /* Round 3. */ /* Let [abcd k s t] denote the operation a = b + ((a + H(b, c, d) + X[k] + T[i]) <<< s). */ /* Do the following 16 operations. */ [ABCD 5 4 33] [DABC 8 11 34] [CDAB 11 16 35] [BCDA 14 23 36] [ABCD 1 4 37] [DABC 4 11 38] [CDAB 7 16 39] [BCDA 10 23 40] [ABCD 13 4 41] [DABC 0 11 42] [CDAB 3 16 43] [BCDA 6 23 44] [ABCD 9 4 45] [DABC 12 11 46] [CDAB 15 16 47] [BCDA 2 23 48] /* Round 4. */ /* Let [abcd k s t] denote the operation a = b + ((a + I(b, c, d) + X[k] + T[i]) <<< s). */ /* Do the following 16 operations. */ [ABCD 0 6 49] [DABC 7 10 50] [CDAB 14 15 51] [BCDA 5 21 52] [ABCD 12 6 53] [DABC 3 10 54] [CDAB 10 15 55] [BCDA 1 21 56] [ABCD 8 6 57] [DABC 15 10 58] [CDAB 6 15 59] [BCDA 13 21 60] [ABCD 4 6 61] [DABC 11 10 62] [CDAB 2 15 63] [BCDA 9 21 64]
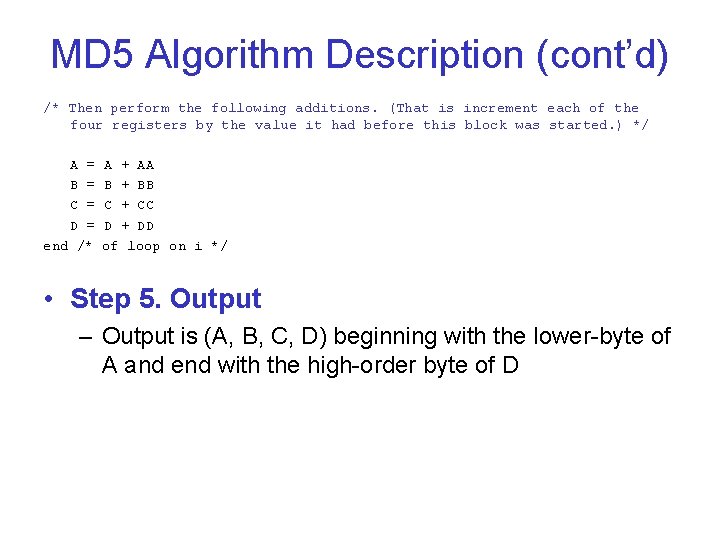
MD 5 Algorithm Description (cont’d) /* Then perform the following additions. (That is increment each of the four registers by the value it had before this block was started. ) */ A = B = C = D = end /* A + AA B + BB C + CC D + DD of loop on i */ • Step 5. Output – Output is (A, B, C, D) beginning with the lower-byte of A and end with the high-order byte of D
Security of MD 5 • Check these sites: • http: //www. schneier. com/blog/archives/20 05/06/more_md 5_collis. html • http: //userpages. umbc. edu/~mabzug 1/cs/ md 5/md 5. html
Secure Hash Algorithm (SHA-1) • Message length < 264 bits • Produces a 160 -bit message digest • NIST and NSA involved in designing the algorithm • Computationally infeasible – to find a message which corresponds to a given message digest, or – to find two different messages which produce the same message digest
SHA-1 RFC Convention • OPERATIONS ON WORDS • Bitwise logical word operations X ^ Y = bitwise logical "and" of X and Y X / Y = bitwise logical "inclusive-or" of X and Y X XOR Y = bitwise logical "exclusive-or" of X and Y ~ X = bitwise logical "complement" of X. • The operation X + Y is defined as follows: – words X and Y represent integers x and y, where 0 <= x < 232 and 0 <= y < 232 – For positive integers n and m, let n mod m be the remainder upon dividing n by m – Compute z = (x + y) mod 232. Then 0 <= z < 232. Convert z to a word, Z, and define Z = X + Y.
SHA-1 RFC Convention (cont’d) • OPERATIONS ON WORDS • Circular left shift operation Sn(X), where X is a word and n is an integer with 0 <= n <= 32, is defined by Sn(X) = (X << n) OR (X >> 32 -n). In the above, X << n is obtained as follows: discard the left-most n bits of X and then pad the result with n zeroes on the right (the result will still be 32 bits). X >> n is obtained by discarding the right-most n bits of X and then padding the result with n zeroes on the left. Thus Sn(X) is equivalent to a circular shift of X by n positions to the left.
SHA-1 Description • Message Padding – make the total length of a padded message a multiple of 512 – Padding process is exactly same as in MD 5 – The padded message will contain 16 * n words for some n > 0 – The padded message is regarded as a sequence of n blocks M 1 , M 2, . . . , Mn, where each Mi contains 16 words and M 1 contains the first characters (or bits) of the message
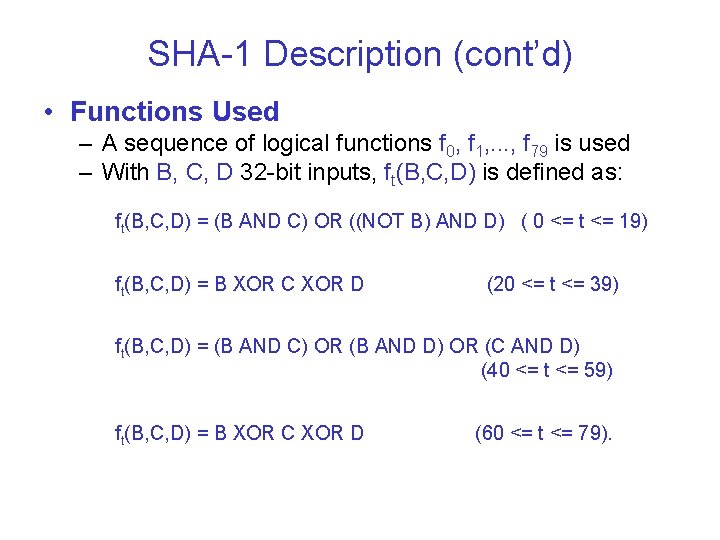
SHA-1 Description (cont’d) • Functions Used – A sequence of logical functions f 0, f 1, . . . , f 79 is used – With B, C, D 32 -bit inputs, ft(B, C, D) is defined as: ft(B, C, D) = (B AND C) OR ((NOT B) AND D) ( 0 <= t <= 19) ft(B, C, D) = B XOR C XOR D (20 <= t <= 39) ft(B, C, D) = (B AND C) OR (B AND D) OR (C AND D) (40 <= t <= 59) ft(B, C, D) = B XOR C XOR D (60 <= t <= 79).
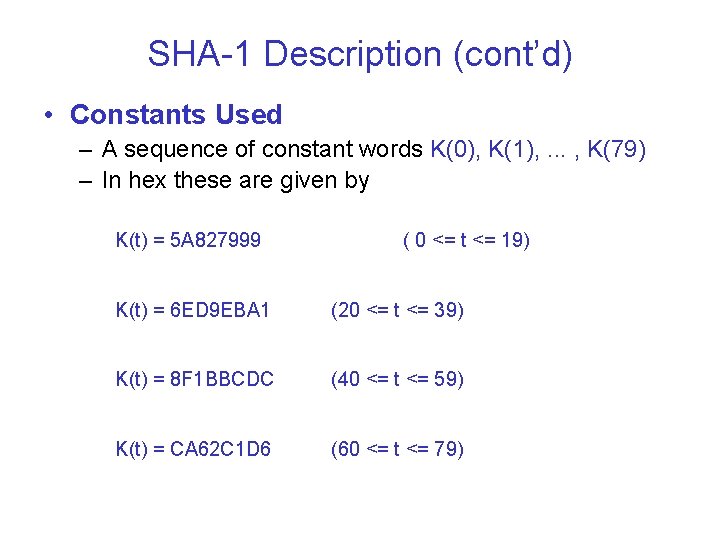
SHA-1 Description (cont’d) • Constants Used – A sequence of constant words K(0), K(1), . . . , K(79) – In hex these are given by K(t) = 5 A 827999 ( 0 <= t <= 19) K(t) = 6 ED 9 EBA 1 (20 <= t <= 39) K(t) = 8 F 1 BBCDC (40 <= t <= 59) K(t) = CA 62 C 1 D 6 (60 <= t <= 79)
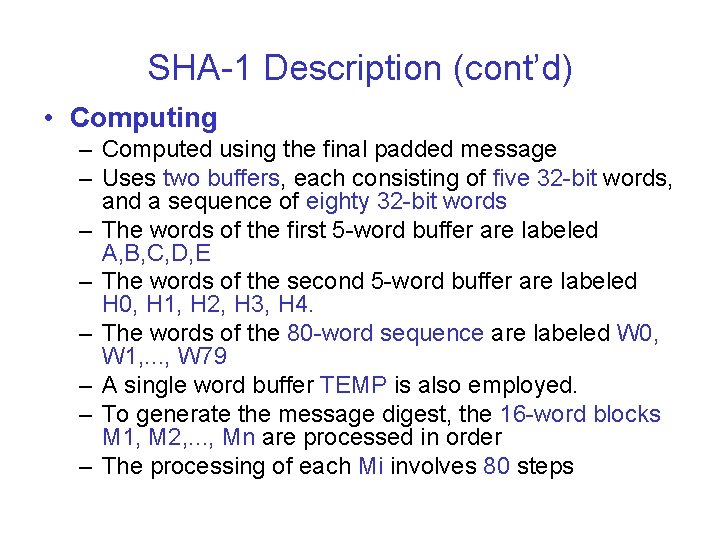
SHA-1 Description (cont’d) • Computing – Computed using the final padded message – Uses two buffers, each consisting of five 32 -bit words, and a sequence of eighty 32 -bit words – The words of the first 5 -word buffer are labeled A, B, C, D, E – The words of the second 5 -word buffer are labeled H 0, H 1, H 2, H 3, H 4. – The words of the 80 -word sequence are labeled W 0, W 1, . . . , W 79 – A single word buffer TEMP is also employed. – To generate the message digest, the 16 -word blocks M 1, M 2, . . . , Mn are processed in order – The processing of each Mi involves 80 steps
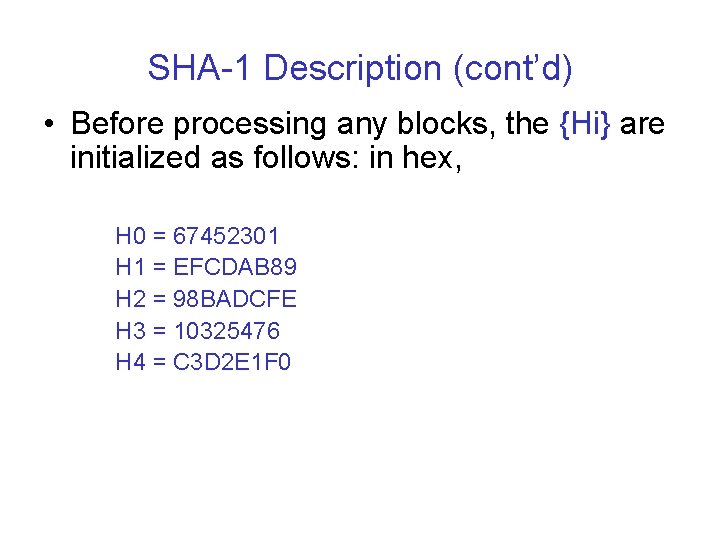
SHA-1 Description (cont’d) • Before processing any blocks, the {Hi} are initialized as follows: in hex, H 0 = 67452301 H 1 = EFCDAB 89 H 2 = 98 BADCFE H 3 = 10325476 H 4 = C 3 D 2 E 1 F 0
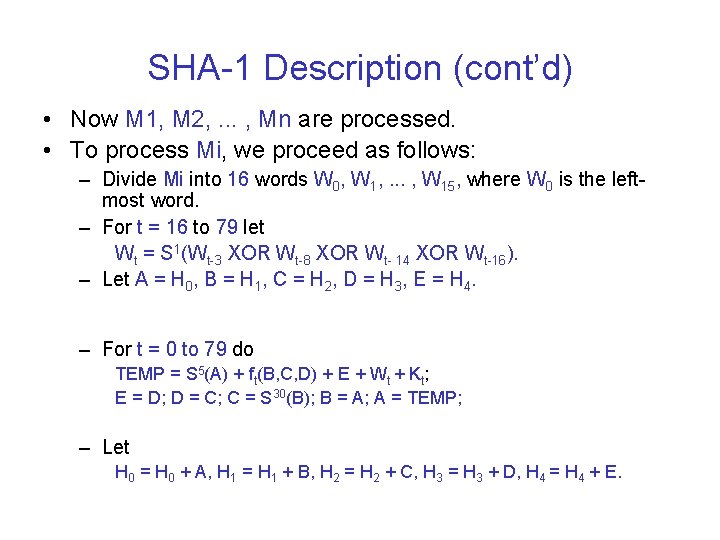
SHA-1 Description (cont’d) • Now M 1, M 2, . . . , Mn are processed. • To process Mi, we proceed as follows: – Divide Mi into 16 words W 0, W 1, . . . , W 15, where W 0 is the leftmost word. – For t = 16 to 79 let Wt = S 1(Wt-3 XOR Wt-8 XOR Wt- 14 XOR Wt-16). – Let A = H 0, B = H 1, C = H 2, D = H 3, E = H 4. – For t = 0 to 79 do TEMP = S 5(A) + ft(B, C, D) + E + Wt + Kt; E = D; D = C; C = S 30(B); B = A; A = TEMP; – Let H 0 = H 0 + A, H 1 = H 1 + B, H 2 = H 2 + C, H 3 = H 3 + D, H 4 = H 4 + E.
SHA-1 Description (cont’d) • After processing Mn, the message digest is the 160 -bit string represented by the 5 words – H 0 H 1 H 2 H 3 H 4.
Security of SHA-1 • Check these sites – http: //www. schneier. com/blog/archives/2005/0 2/sha 1_broken. html – http: //www. schneier. com/blog/archives/2009/0 6/ever_better_cry. html – New hash algorithm: SHA 2 published by NIST
- Slides: 24