A Space Efficient Backdoor in RSA and its
A Space Efficient Backdoor in RSA and its Applications Adam L. Young n LECG LLC n n joint work with Moti Yung n RSA Labs and Columbia University n Selected Areas in Cryptography 2005 n Queen’s University n Kingston, Ontario, Canada n
SETUP – Informal Definition • Informally, a Secretly Embedded Trapdoor with Universal Protection (SETUP) is a backdoor that exhibits robust security properties. • The goal of a SETUP is to give the attacker an algorithm that provides as much security as possible. • Another term for a SETUP is an “asymmetric backdoor” • Backdoors have traditionally been symmetric. . . anyone that finds it can use it • A primary novelty behind an asymmetric backdoor [YY 96] is that only the attacker can use it since it utilizes public key crypto. 2 of 25
SETUP Attack on RSA Key Generation • Backdoor algorithm covertly embeds backdoor info. into the RSA public modulus n that is being generated. • A database of public keys is a database of public keys plus recovery fields w. r. t. the attacker. • Attacker obtains public key of victim, extracts backdoor info. from n, and factors n using private info. (his/her private key). • Eavesdropper seeks to factor moduli n without private info. of attacker • Inquirer seeks to distinguish backdoored RSA key pairs from “normal” RSA key pairs. 3 of 25
Secretly Embedded Trapdoor with Universal Protection Before games start the eavesdropper and inquirer are given access to the SETUP key generator code in its entirety. D is a key generator with a SETUP in it. Game 1: The inquirer is given oracle access to two devices A and B. So, the inquirer obtains RSA key pairs from the devices. With 50% probability A has a SETUP in it iff B does not. The inquirer wins if he determines whether or not A has the SETUP in it with probability significantly greater than 1/2. Property 1: (indistinguishability) Inquirer fails Game 1 with overwhelming prob. Game 2: The eavesdropper may query D but is only given the public keys that result, not the corresponding private keys. He wins if he can learn one of the corresponding private keys. Property 2: (confidentiality) Eavesdropper fails Game 2 with overwhelming prob. Property 3: (completeness) Let (y, x) be a public/private key generated using D. With overwhelming probability the designer computes x on input y (and his own private inputs) Property 4: (uniformity) The SETUP is the same in every black-box device. If an RSA key generation algorithm satisfies properties 1, 2, 3, and 4 then it is a strong SETUP. 4 of 25
Binary Curves n Curve Ea, b is given by the Weierstrass equation, y 2 +xy = x 3 +ax 2 + b n Here the coefficients a and b are in F 2 m and b ≠ 0. n m is prime to avoid the GHS attack [GHS 02]. n curve must provide a suitable setting for EC-DDH [JN 03] n curve must satisfy the MOV condition (Menezes-Okamoto-Vanstone) 5 of 25
Property of Twisted Curves n Recall that if the trace Tr F m/F (a) 2 2 ≠ Tr (a') then Ea, b and Ea', b F 2 m/F 2 are “twists” of one another [Ka 86, Ka 88, Ka 91]. n When two such curves are twists of one another then for every F 2 m there exists a y F 2 m such that (x, y) is a point on Ea, b or Ea', b. n The two possibilities are as follows. n Either (x, y) and (x, x+y) are points on the same curve, or n (x, y) = (0, b) is on both curves. x 6 of 25
Intuition Behind the Approach n Elliptic Curve Cryptography gives smaller ciphertexts (with point compression) than RSA with a comparable security parameter. → The use of ECC in kleptography [YY 96, YY 97] is a “no-brainer”. n BUT, the use of a twisted pair of binary curves gives a Diffie. Hellman key exchange value that is (essentially) a bit string selected uniformly at random [Mo 04]. → This suggests that we can embed a DH key exchange value in the upper order bits of n = pq and achieve indistinguishability of RSA backdoor public keys vs. “normal” public keys. 7 of 25
EC Diffie-Hellman Key Generation n designer chooses base point G 0 having order q 0 that is on E 0, b(F 2 m) n designer chooses base point G 1 having order q 1 that is on E 1, b(F 2 m) n designer generates: n EC private key x 0 R {1, 2, . . . , q 0 - 1} n corresponding public key Y 0 = x 0 G 0 n designer generates: n EC private key x 1 R {1, 2, . . , q 1 - 1} n corresponding public key Y 1 = x 1 G 1 n The values (G 0, G 1, Y 0, Y 1) are included in the RSA key generation device. 8 of 25
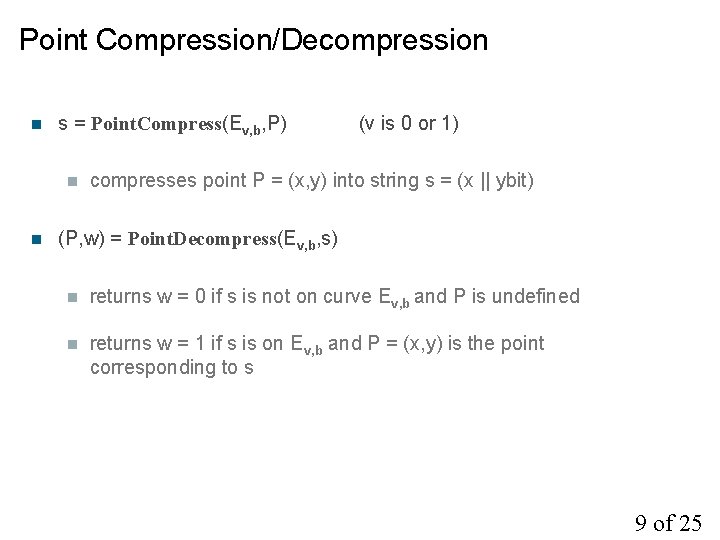
Point Compression/Decompression n s = Point. Compress(Ev, b, P) n n (v is 0 or 1) compresses point P = (x, y) into string s = (x || ybit) (P, w) = Point. Decompress(Ev, b, s) n returns w = 0 if s is not on curve Ev, b and P is undefined n returns w = 1 if s is on Ev, b and P = (x, y) is the point corresponding to s 9 of 25
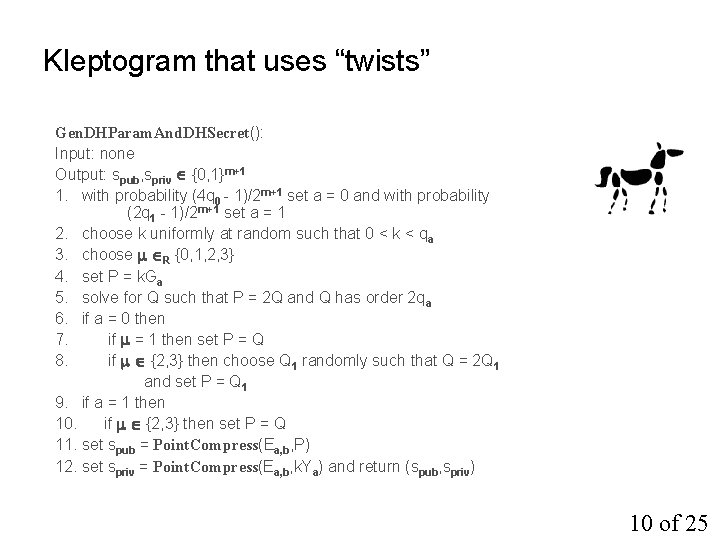
Kleptogram that uses “twists” Gen. DHParam. And. DHSecret(): Input: none Output: spub, spriv {0, 1}m+1 1. with probability (4 q 0 - 1)/2 m+1 set a = 0 and with probability (2 q 1 - 1)/2 m+1 set a = 1 2. choose k uniformly at random such that 0 < k < qa 3. choose R {0, 1, 2, 3} 4. set P = k. Ga 5. solve for Q such that P = 2 Q and Q has order 2 qa 6. if a = 0 then 7. if = 1 then set P = Q 8. if {2, 3} then choose Q 1 randomly such that Q = 2 Q 1 and set P = Q 1 9. if a = 1 then 10. if {2, 3} then set P = Q 11. set spub = Point. Compress(Ea, b, P) 12. set spriv = Point. Compress(Ea, b, k. Ya) and return (spub, spriv) 10 of 25
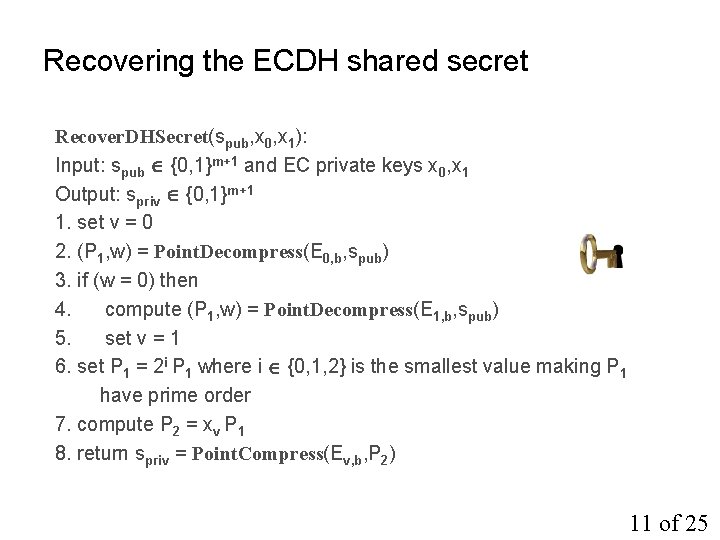
Recovering the ECDH shared secret Recover. DHSecret(spub, x 0, x 1): Input: spub {0, 1}m+1 and EC private keys x 0, x 1 Output: spriv {0, 1}m+1 1. set v = 0 2. (P 1, w) = Point. Decompress(E 0, b, spub) 3. if (w = 0) then 4. compute (P 1, w) = Point. Decompress(E 1, b, spub) 5. set v = 1 6. set P 1 = 2 i P 1 where i {0, 1, 2} is the smallest value making P 1 have prime order 7. compute P 2 = xv P 1 8. return spriv = Point. Compress(Ev, b, P 2) 11 of 25
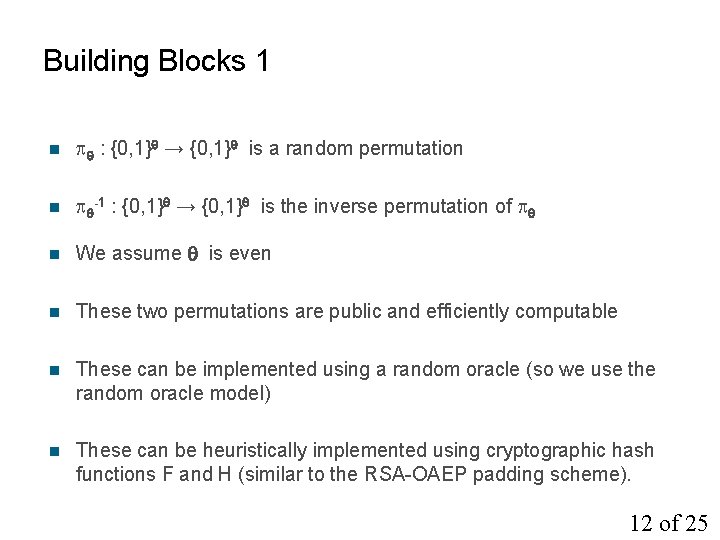
Building Blocks 1 n : {0, 1} → {0, 1} is a random permutation n -1 : {0, 1} → {0, 1} is the inverse permutation of n We assume is even n These two permutations are public and efficiently computable n These can be implemented using a random oracle (so we use the random oracle model) n These can be heuristically implemented using cryptographic hash functions F and H (similar to the RSA-OAEP padding scheme). 12 of 25
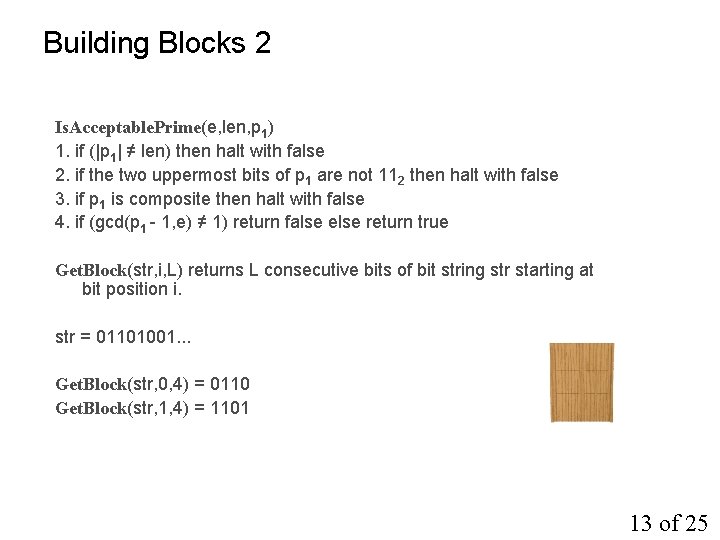
Building Blocks 2 Is. Acceptable. Prime(e, len, p 1) 1. if (|p 1| ≠ len) then halt with false 2. if the two uppermost bits of p 1 are not 112 then halt with false 3. if p 1 is composite then halt with false 4. if (gcd(p 1 - 1, e) ≠ 1) return false else return true Get. Block(str, i, L) returns L consecutive bits of bit string str starting at bit position i. str = 01101001. . . Get. Block(str, 0, 4) = 0110 Get. Block(str, 1, 4) = 1101 13 of 25
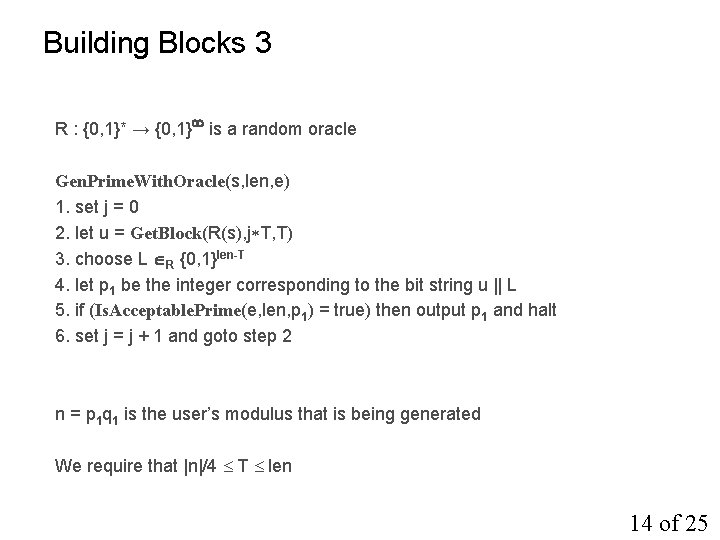
Building Blocks 3 R : {0, 1}* → {0, 1} is a random oracle Gen. Prime. With. Oracle(s, len, e) 1. set j = 0 2. let u = Get. Block(R(s), j T, T) 3. choose L R {0, 1}len-T 4. let p 1 be the integer corresponding to the bit string u || L 5. if (Is. Acceptable. Prime(e, len, p 1) = true) then output p 1 and halt 6. set j = j + 1 and goto step 2 n = p 1 q 1 is the user’s modulus that is being generated We require that |n|/4 T len 14 of 25
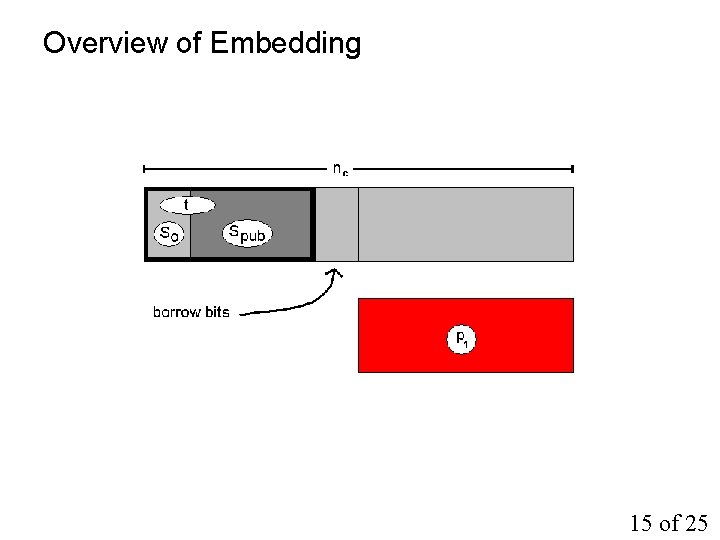
Overview of Embedding 15 of 25
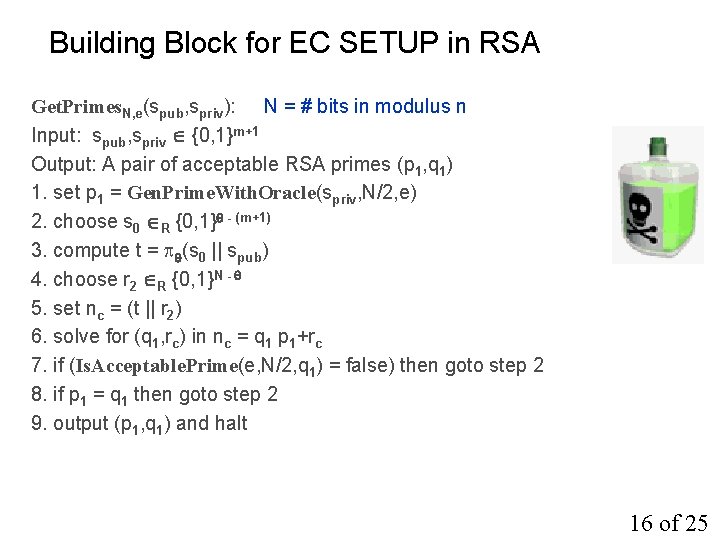
Building Block for EC SETUP in RSA Get. Primes. N, e(spub, spriv): N = # bits in modulus n Input: spub, spriv {0, 1}m+1 Output: A pair of acceptable RSA primes (p 1, q 1) 1. set p 1 = Gen. Prime. With. Oracle(spriv, N/2, e) 2. choose s 0 R {0, 1} - (m+1) 3. compute t = (s 0 || spub) 4. choose r 2 R {0, 1}N - 5. set nc = (t || r 2) 6. solve for (q 1, rc) in nc = q 1 p 1+rc 7. if (Is. Acceptable. Prime(e, N/2, q 1) = false) then goto step 2 8. if p 1 = q 1 then goto step 2 9. output (p 1, q 1) and halt 16 of 25
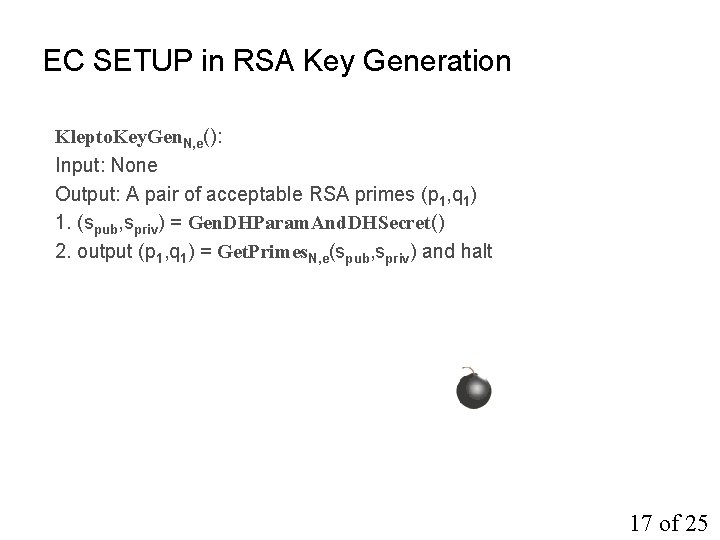
EC SETUP in RSA Key Generation Klepto. Key. Gen. N, e(): Input: None Output: A pair of acceptable RSA primes (p 1, q 1) 1. (spub, spriv) = Gen. DHParam. And. DHSecret() 2. output (p 1, q 1) = Get. Primes. N, e(spub, spriv) and halt 17 of 25
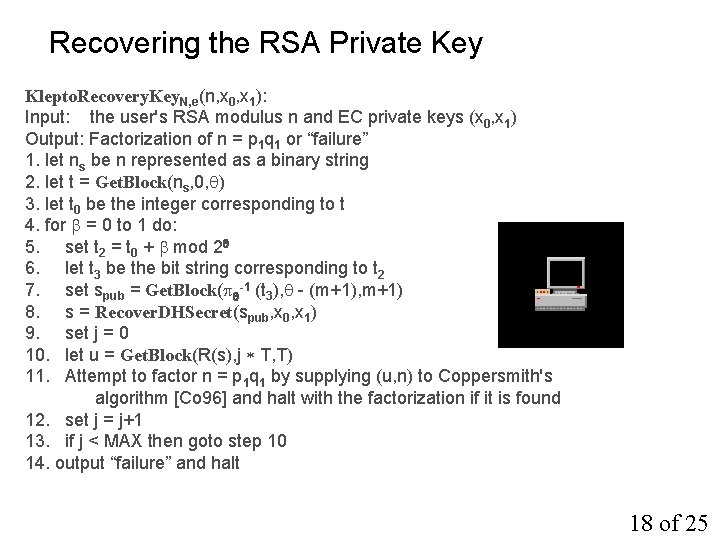
Recovering the RSA Private Key Klepto. Recovery. Key. N, e(n, x 0, x 1): Input: the user's RSA modulus n and EC private keys (x 0, x 1) Output: Factorization of n = p 1 q 1 or “failure” 1. let ns be n represented as a binary string 2. let t = Get. Block(ns, 0, ) 3. let t 0 be the integer corresponding to t 4. for = 0 to 1 do: 5. set t 2 = t 0 + mod 2 6. let t 3 be the bit string corresponding to t 2 7. set spub = Get. Block( -1 (t 3), - (m+1), m+1) 8. s = Recover. DHSecret(spub, x 0, x 1) 9. set j = 0 10. let u = Get. Block(R(s), j T, T) 11. Attempt to factor n = p 1 q 1 by supplying (u, n) to Coppersmith's algorithm [Co 96] and halt with the factorization if it is found 12. set j = j+1 13. if j < MAX then goto step 10 14. output “failure” and halt 18 of 25
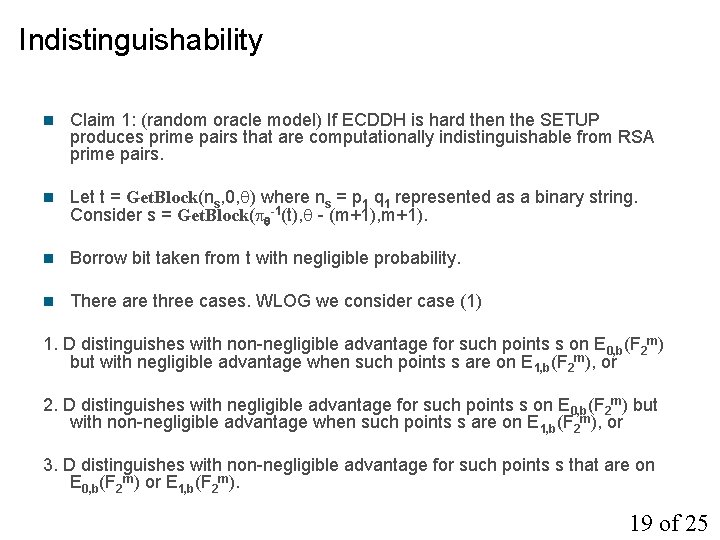
Indistinguishability n Claim 1: (random oracle model) If ECDDH is hard then the SETUP produces prime pairs that are computationally indistinguishable from RSA prime pairs. n Let t = Get. Block(ns, 0, ) where ns = p 1 q 1 represented as a binary string. Consider s = Get. Block( -1(t), - (m+1), m+1). n Borrow bit taken from t with negligible probability. n There are three cases. WLOG we consider case (1) 1. D distinguishes with non-negligible advantage for such points s on E 0, b(F 2 m) but with negligible advantage when such points s are on E 1, b(F 2 m), or 2. D distinguishes with negligible advantage for such points s on E 0, b(F 2 m) but with non-negligible advantage when such points s are on E 1, b(F 2 m), or 3. D distinguishes with non-negligible advantage for such points s that are on E 0, b(F 2 m) or E 1, b(F 2 m). 19 of 25
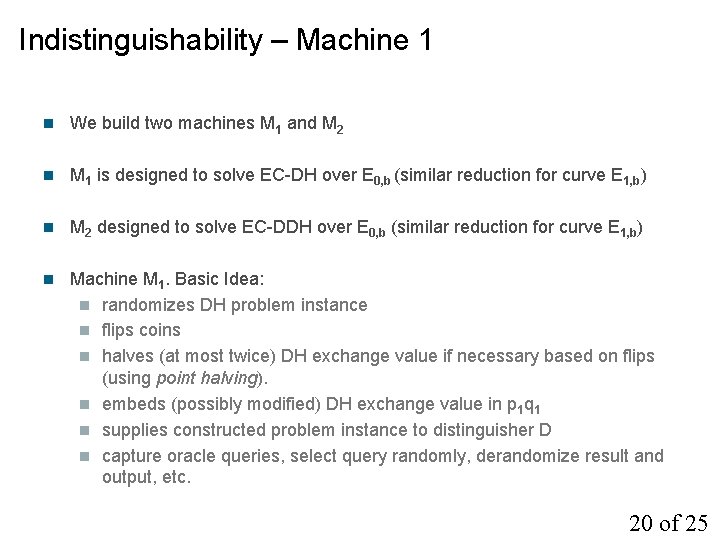
Indistinguishability – Machine 1 n We build two machines M 1 and M 2 n M 1 is designed to solve EC-DH over E 0, b (similar reduction for curve E 1, b) n M 2 designed to solve EC-DDH over E 0, b (similar reduction for curve E 1, b) n Machine M 1. Basic Idea: n randomizes DH problem instance n flips coins n halves (at most twice) DH exchange value if necessary based on flips (using point halving). n embeds (possibly modified) DH exchange value in p 1 q 1 n supplies constructed problem instance to distinguisher D n capture oracle queries, select query randomly, derandomize result and output, etc. 20 of 25
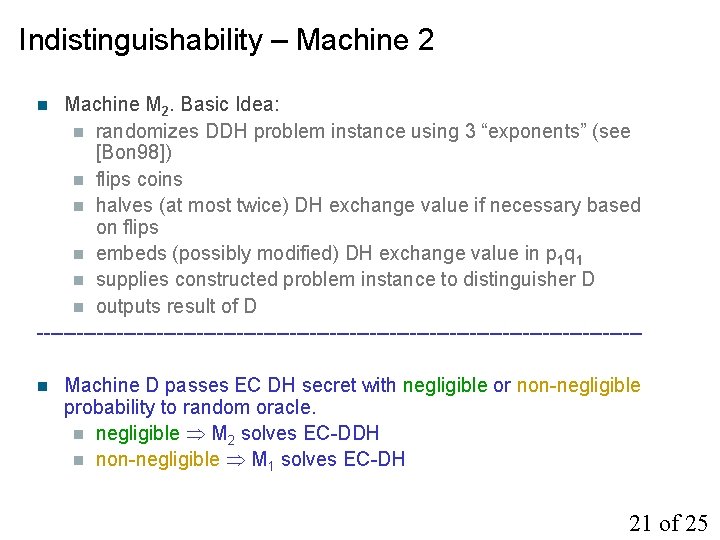
Indistinguishability – Machine 2 Machine M 2. Basic Idea: n randomizes DDH problem instance using 3 “exponents” (see [Bon 98]) n flips coins n halves (at most twice) DH exchange value if necessary based on flips n embeds (possibly modified) DH exchange value in p 1 q 1 n supplies constructed problem instance to distinguisher D n outputs result of D ---------------------------------------------n n Machine D passes EC DH secret with negligible or non-negligible probability to random oracle. n negligible M 2 solves EC-DDH n non-negligible M 1 solves EC-DH 21 of 25
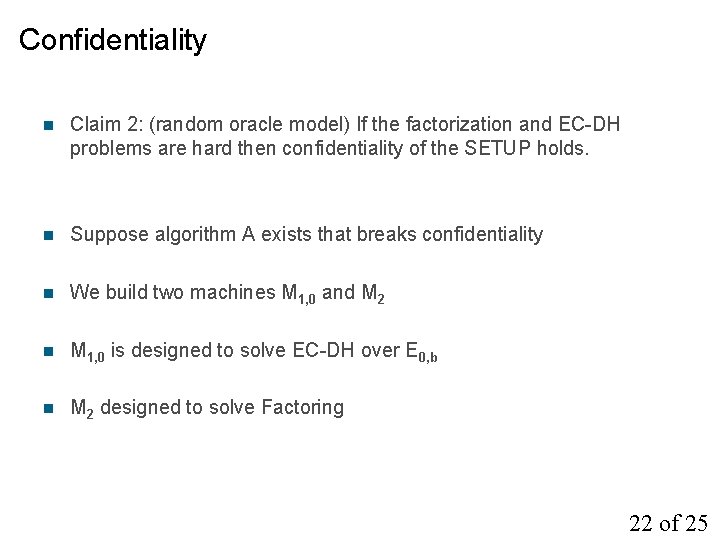
Confidentiality n Claim 2: (random oracle model) If the factorization and EC-DH problems are hard then confidentiality of the SETUP holds. n Suppose algorithm A exists that breaks confidentiality n We build two machines M 1, 0 and M 2 n M 1, 0 is designed to solve EC-DH over E 0, b n M 2 designed to solve Factoring 22 of 25
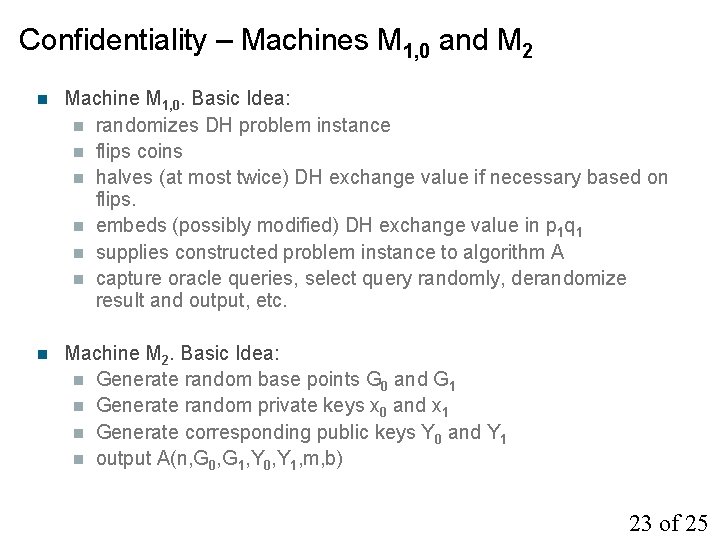
Confidentiality – Machines M 1, 0 and M 2 n Machine M 1, 0. Basic Idea: n randomizes DH problem instance n flips coins n halves (at most twice) DH exchange value if necessary based on flips. n embeds (possibly modified) DH exchange value in p 1 q 1 n supplies constructed problem instance to algorithm A n capture oracle queries, select query randomly, derandomize result and output, etc. n Machine M 2. Basic Idea: n Generate random base points G 0 and G 1 n Generate random private keys x 0 and x 1 n Generate corresponding public keys Y 0 and Y 1 n output A(n, G 0, G 1, Y 0, Y 1, m, b) 23 of 25
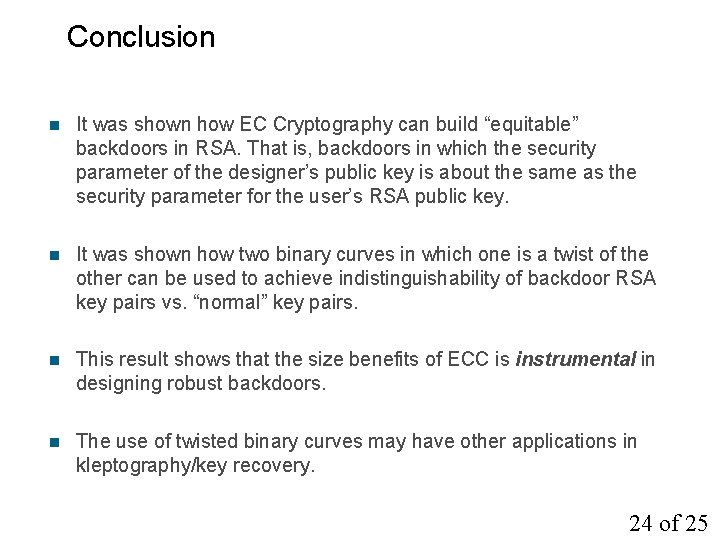
Conclusion n It was shown how EC Cryptography can build “equitable” backdoors in RSA. That is, backdoors in which the security parameter of the designer’s public key is about the same as the security parameter for the user’s RSA public key. n It was shown how two binary curves in which one is a twist of the other can be used to achieve indistinguishability of backdoor RSA key pairs vs. “normal” key pairs. n This result shows that the size benefits of ECC is instrumental in designing robust backdoors. n The use of twisted binary curves may have other applications in kleptography/key recovery. 24 of 25
![References n n n n n [Bon 98] D. Boneh. The Decision Diffie-Hellman Problem. References n n n n n [Bon 98] D. Boneh. The Decision Diffie-Hellman Problem.](http://slidetodoc.com/presentation_image_h2/641727fbb459af1a9fcb7bf49424899a/image-25.jpg)
References n n n n n [Bon 98] D. Boneh. The Decision Diffie-Hellman Problem. In 3 rd Algorithmic Number Theory Symposium, pages 48 -63, 1998. [Co 96] D. Coppersmith. Finding a small root of a bivariate integer equation; factoring with high bits known. In Eurocrypt '96, pages 178 -189, 1996. [GHS 02] P. Gaudry, F. Hess, N. Smart. Constructive and Destructive Facets of Weil Descent on Elliptic Curves, In J. of Cryptology, v. 15, pages 19 -46, 2002. [JN 03] A. Joux, K. Nguyen. Separating DDH from CDH in Cryptographic Groups. In Journal of Cryptology, v. 16, n. 4, pages 239 -247, 2003. [Ka 86] B. S. Kaliski. A Pseudo-Random Bit Generator Based on Elliptic Logarithms. In Advances in Cryptology - Crypto '86, pages 84 -103, 1986. [Ka 88] B. S. Kaliski. Elliptic Curves and Cryptography: A Pseudorandom Bit Generator and Other Tools. Ph. D Thesis, MIT, Feb. 1988. [Ka 91] B. S. Kaliski. One-Way Permutations on Elliptic Curves. In Journal of Cryptology, v. 3, n. 3, pages 187 -199, 1991. [Mo 04] B. Moller. A Public-Key Encryption Scheme with Pseudo-Random Ciphertexts. In ESORICS '04, pages 335 -351, 2004. [YY 96] A. Young, M. Yung. The Dark Side of Black-Box Cryptography, or: Should we trust Capstone? In Advances in Cryptology - Crypto '96, pages 89 -103, 1996. [YY 97] A. Young, M. Yung. Kleptography: Using Cryptography Against Cryptography. In Advances in Cryptology - Eurocrypt '97, pages 62 -74, 1997. 25 of 25
- Slides: 25