Backdoors Trojans and Rootkits CIS 413 This presentation
Backdoors, Trojans and Rootkits CIS 413 This presentation is an amalgam of presentations by Mark Michael, Randy Marchany and Ed Skoudis. I have edited and added material. Dr. Stephen C. Hayne

Back Doors n An alternative entryway n n No fancy authentication needed Maintains access on a system n n Usually access is needed initially Still works when front door is closed
Back Doors n n n An attacker with back door access “owns” the system Attackers might make the system more secure to keep ownership The attacker does the work of the administrator
Back Doors Melded into Trojan Horses n n n Application-level Trojan Horse Backdoors Traditional Root. Kits Kernel-level Root. Kits
Application-Level Trojan Horse Backdoor Tools Adds a separate application to the system n Made up of a server and client part n n n server is installed on victims machine client is installed on attackers machine Victim must install the server portion n Once installed the attacker “owns” the victims machine n
Application-Level Trojan Horse Backdoor Tools n n n n Log Keystrokes Gather system information Get passwords from the SAM database Control the file system Edit the registry Control applications and services Redirect Packets
Application-Level Trojan Horse Backdoor Tools n Application redirection n n n Any DOS application can be spawned useful for setting up command-line backdoors Multimedia control View files in a browser Hidden mode Encryption between client and server
Application-Level Trojan Horse Backdoor Tools n Plug-ins: n n Streaming video from server machine More encryption methods n n n Blowfish, CAST-256, IDEA, Serpent, RC 6 Stronger security than a lot of commercial products! Stealthier methods for transport
Defenses against Application. Level Trojan Backdoors n n Most Anti-virus programs will notice and remove the tools mentioned Update virus definitions regularly Don’t run programs downloaded from untrusted sources Don’t auto-run Active. X controls
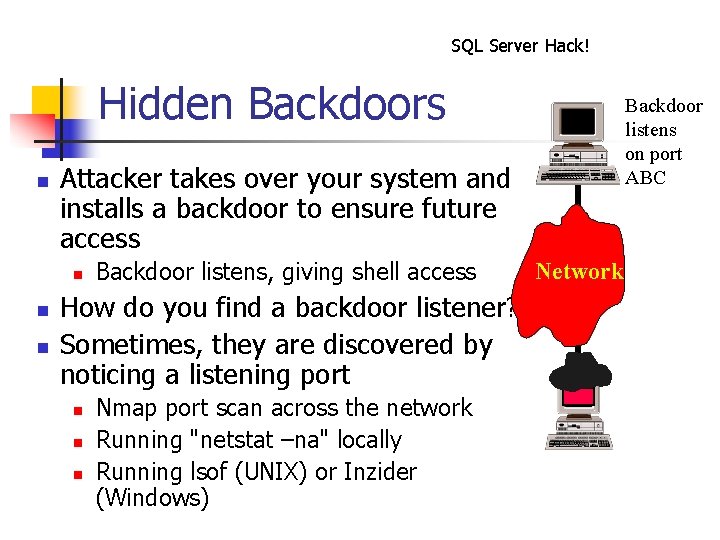
SQL Server Hack! Hidden Backdoors n Attacker takes over your system and installs a backdoor to ensure future access n n n Backdoor listens on port ABC Backdoor listens, giving shell access How do you find a backdoor listener? Sometimes, they are discovered by noticing a listening port n n n Nmap port scan across the network Running "netstat –na" locally Running lsof (UNIX) or Inzider (Windows) Network
Sniffing Backdoors Who says a backdoor has to wait listening on a port? n Attackers don't want to get caught n n n They are increasingly using stealthy backdoors A sniffer can gather the traffic, rather than listening on an open port n Non-promiscuous sniffing backdoors n n Grab traffic just for one host Promiscuous sniffing backdoors n Grab all traffic on the LAN
Non-Promiscuous Backdoor – Cd 00 r n Written by FX n n Includes a non-promiscuous sniffer n n Gathers only packets destined for the single target machine Several packets directed to specific ports (where there is no listener) will trigger the backdoor n n http: //www. phenoelit. de/stuff/cd 00 r. c Sniffer grabs packets, not a listener on the ports Backdoor root shell starts to listen on TCP port 5002 only when packets arrive to the trigger ports
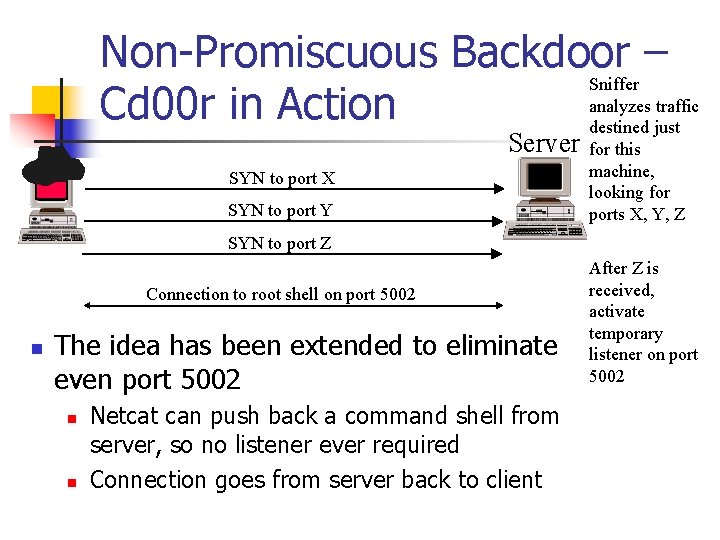
Non-Promiscuous Backdoor – Sniffer analyzes traffic Cd 00 r in Action destined just Server SYN to port X SYN to port Y for this machine, looking for ports X, Y, Z SYN to port Z Connection to root shell on port 5002 n The idea has been extended to eliminate even port 5002 n n Netcat can push back a command shell from server, so no listener ever required Connection goes from server back to client After Z is received, activate temporary listener on port 5002

Promiscuous Backdoor Can be used to help throw off an investigation n Attacker sends data for destination on same network n But the backdoor isn't located at the destination of the backdoor traffic n n Huh? How does that work?
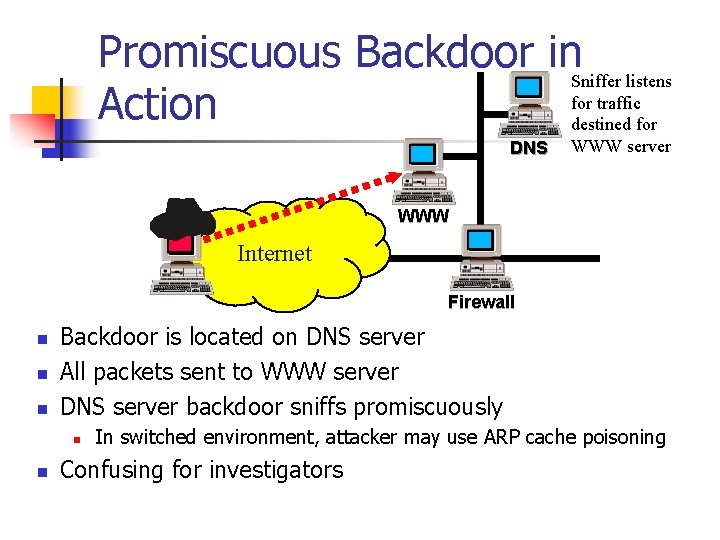
Promiscuous Backdoor in. Sniffer listens for traffic Action destined for DNS WWW server WWW Internet Firewall n n n Backdoor is located on DNS server All packets sent to WWW server DNS server backdoor sniffs promiscuously n n In switched environment, attacker may use ARP cache poisoning Confusing for investigators
Sniffing Backdoor Defenses Prevent attacker from getting on system in the first place (of course) n Know which processes are supposed to be running on the system n n Especially if they have root privileges! Not easy, but very important Beware of stealthy names (like "UPS" or "SCSI") Look for anomalous traffic n Look for sniffers n
- Slides: 16