Transport Layer Security Privacy Enhancing Technologies Tobias Pulls
Transport Layer Security Privacy Enhancing Technologies Tobias Pulls CC-BY-4. 0
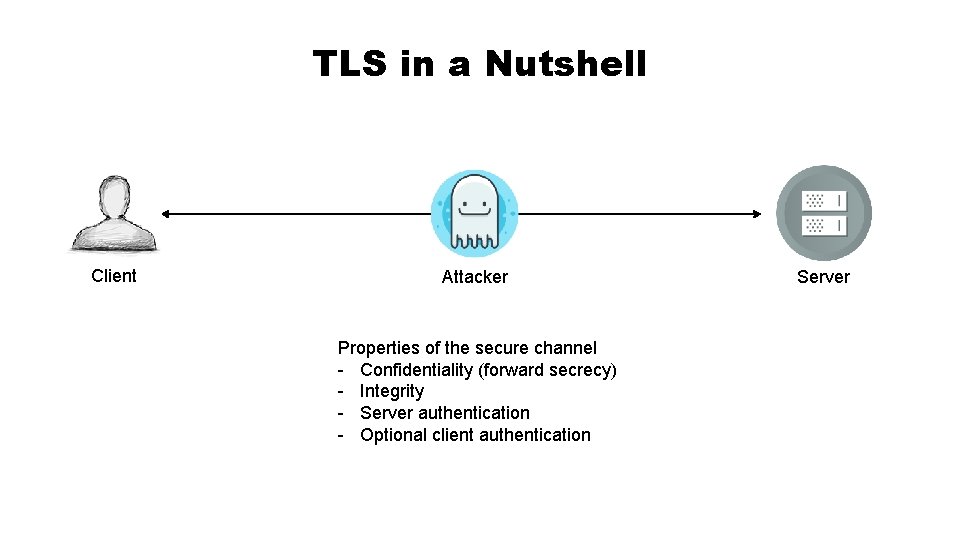
TLS in a Nutshell Client Attacker Properties of the secure channel - Confidentiality (forward secrecy) - Integrity - Server authentication - Optional client authentication Server
History • Secure Sockets Layer (SSL) in ~1996 • TLS versions • • 1. 0 in 1999 1. 1 in 2006 1. 2 in 2008 1. 3 as draft in January 2018 • A subset of TLS 1. 1 and 1. 2 secure today • Depends on selected algorithms • . . . and implementation!
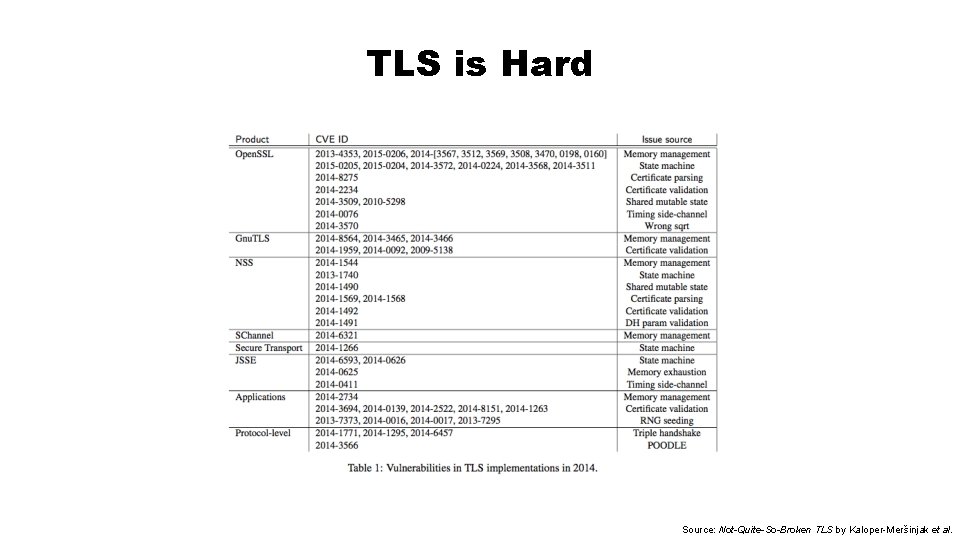
TLS is Hard Source: Not-Quite-So-Broken TLS by Kaloper-Meršinjak et al.
Improvements to TLS • TLS 1. 3 makes the protocol simpler • No legacy algorithms, compression, renegotiation • Encrypt as much as possible of handshake • Split between authentication, key exchange, cipher • Significant efforts around implementation • • • Remove old code, support for old versions, architectures, refactoring Boring. SSL Open. SSL cleanup (Levchin prize 2018) Formal methods to verify implementations. . .
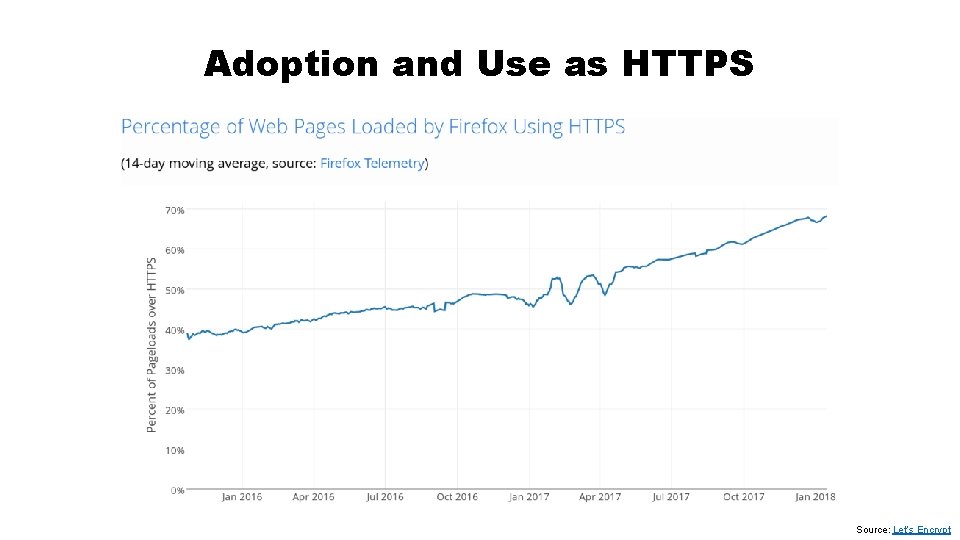
Adoption and Use as HTTPS Source: Let’s Encrypt
Conclusions • TLS = secure channel between client and server • Confidentiality (forward secrecy) • Integrity • Authentication (client optional) • Long history • TLS 1. 1 and 1. 2 widely adopted • TLS 1. 3 soon here • Soon (already? ) a must default • The S in HTTPS, but many other applications as well Image source: Adrienne Porter Felt, Google, @__apf__
- Slides: 7