SelfHealing Key Distribution with Revocation Presented by Matt
Self-Healing Key Distribution with Revocation Presented by Matt Palombi 11/18/2004
Authors n n n n Xerox PARC - May 28, 2002 Jessica Staddon Sara Miner Matt Franklin Dirk Balfanz Michael Malkin Drew Dean
Session Keys n n We want to ensure secure multicast communication. One solution is having a common session key shared by all group members.
Key Distribution n A central group manager that periodically distributes new keys. New key every session. How can this be conducted over an unreliable network, such as the Internet?
Interactive Approach n n Require user to contact the group manager in order to resend the session key. Not practical in large groups n n n Added traffic on a congested network Could overwhelm group manager Not desirable in certain high-security environments n User wants to avoid sending unnecessary messages
A Non-Interactive Approach n Self-Healing Key Distribution n n A group member that does not receive a key can recover it on its own Uses data from previous and subsequent key distribution broadcasts to recover the missing session key
Properties of Self Healing n n In a sequence of m sessions, all key broadcasts except the first and last could be lost, and all m sessions keys would be recoverable Using sandwiching broadcasts allows the use of a flat key management system
Flat Key Distribution n Benefits n n n Each user has a unique personal key Enables traceability Costs n Increased communication overhead due to a key for every user
Revoking and Adding Users n n The key distribution scheme must also allow the group manager to add or remove users from the group at any time. Must be resistant to collusion attacks
Meeting Requirements n n These requirements can be met with simple, polynomial-based secret sharing techniques An unconditionally secure construction can be achieved with (t 2 m) log q bits. n n n q is the session key size t is the size of the largest coalition the system is resistant to m is the number of sessions over which self healing is possible
Meeting requirements 2 n n Can reduce broadcasts to (t 2 + mt) log q bits by shifting some computation to user’s end. In all versions, recovery from loss is possible with no delay after receiving a key broadcast transmission.
Related Work n Other non-interactive methods of providing resistance to packet loss n n Error correcting codes provide information about previous keys (Keystone) Packets contain “hints” for previous keys, requires significant work on user’s end to recover (ELK)
Related Work (cont. ) n These approaches have some drawbacks n n Small broadcast size requires hierarchical key distribution Hierarchical keys apply to subsets of users, make traceability difficult Offline member cannot rejoin without intervention from group manager In ELK keying info is paired with content, only useful if group manager is only sender
Basic Definitions n n n Session key – the key used for group communication during a session Session – A fixed interval of time t-revocation capability – it is possible to prevent t users from learning the new session key
Basic Definitions (cont. ) n n There is a group manager and n users, U 1, … , U n All operations take place in a finite field Fq, where q is a prime greater than n Each user, Ui, stores a personal key Si k is a single key (an element of Fq)
Definition 1: Key Independence n n n There are m sessions and the session keys are K 1 through Km R is the set of revoked users. If a user is not in R, it is said to be a member or an active user For j Î {1, … , m}, Kj is sent to the group members through broadcast Bj
Definition 1 (Cont. ) n n The information that the user knows by having both Bj and Si is represented by zi, j If Ui is a group member, zi, j will include Kj and possibly information on other authorized group keys If Ui is not a group member, there is no information about Kj in zi, j Users’ personal keys contain sensitive information, this guards against collusion attacks
Definition 2: Session Key Distribution n n Let t, i Î {1, … , n}, and j Î {1, … , m} D is a session key distribution scheme if: n n n Kj is determined by zi, j A set of less than t users cannot determine anything about Si from the session key broadcasts What a user learns is not determined by their personal key or broadcasts alone
Definition 2 (Cont. ) n D has t-revocation capability if: n The size of R is less than t, and the group manager can generate a broadcast that allows all members to recover the key, but does not allow any user in R to recover it.
Definition 2 (Cont. ) n D is self-healing if for any 1 ≤ j 1 < j 2 ≤ m this is true: n n Kj is determined by the set of information known by any member in sessions j 1 and j 2 no information on Kj can be computed by two disjoint sets of users as long as they number less than t
Self Healing n n In every broadcast, a user learns either the actual key or a share of the actual key for all m sessions The following diagram gives a simple example of how this might work
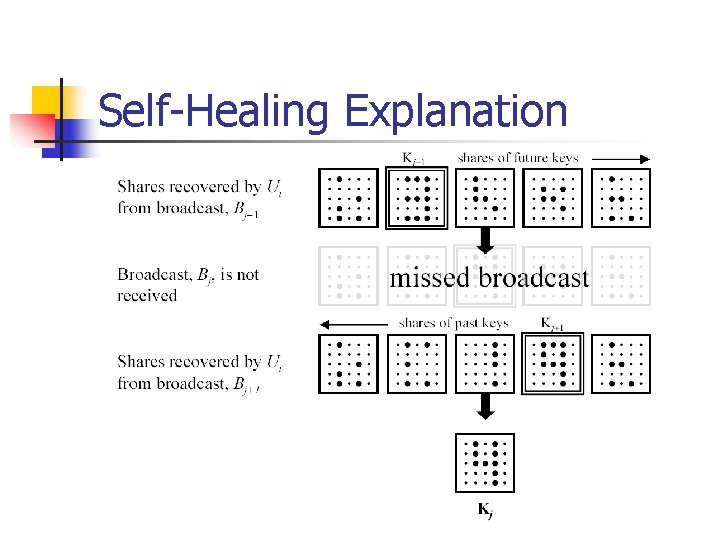
Self-Healing Explanation
Construction 1: Self-Healing without Revocation n n This meets the self-healing requirement, but not revocation Three phases n n n Setup Broadcast Session Key and Shares Recovery in Session j
Construction 1: Setup n n Pick t based on desired collusion resistance Group manager generates at random: n 2 m polynomials of degree t in the finite field Fq[x] n n h 1, … , hm and p 1, … , pm m session keys K 1 through Km
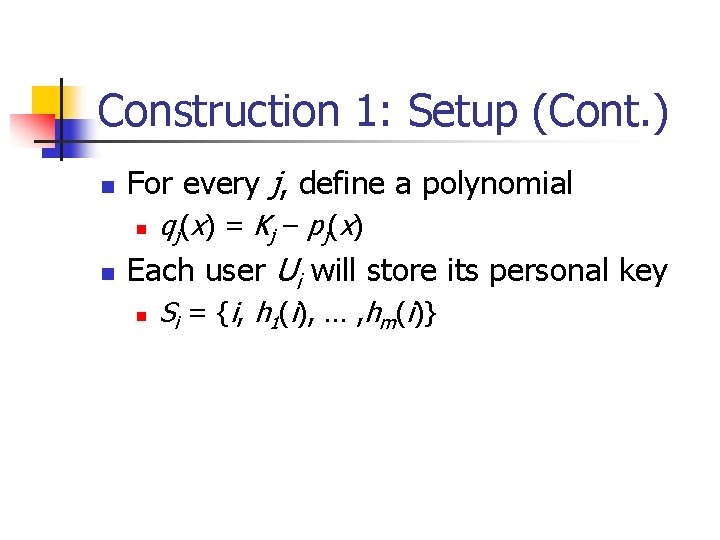
Construction 1: Setup (Cont. ) n For every j, define a polynomial n n q j ( x) = K j – p j ( x) Each user Ui will store its personal key n Si = {i, h 1(i), … , hm(i)}
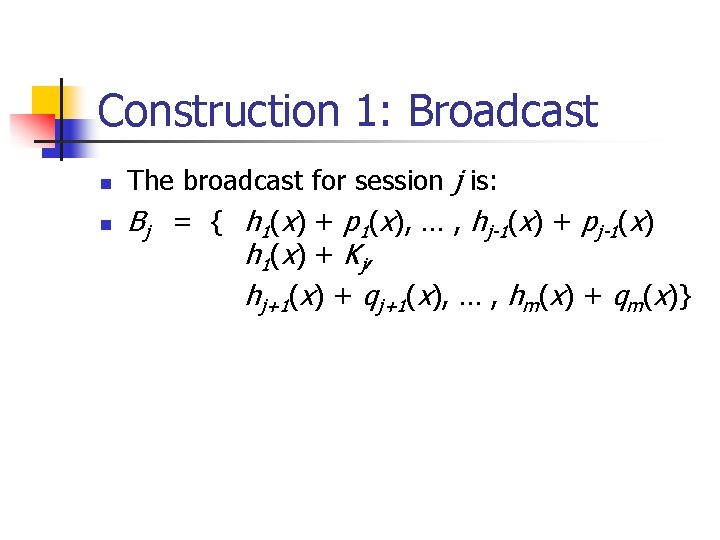
Construction 1: Broadcast n n The broadcast for session j is: Bj = { h 1(x) + p 1(x), … , hj-1(x) + pj-1(x) h 1 ( x) + K j , hj+1(x) + qj+1(x), … , hm(x) + qm(x)}
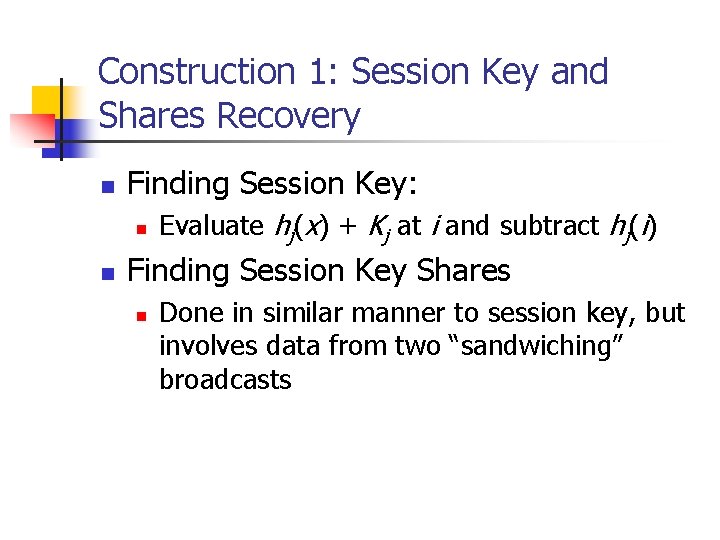
Construction 1: Session Key and Shares Recovery n Finding Session Key: n n Evaluate hj(x) + Kj at i and subtract hj(i) Finding Session Key Shares n Done in similar manner to session key, but involves data from two “sandwiching” broadcasts
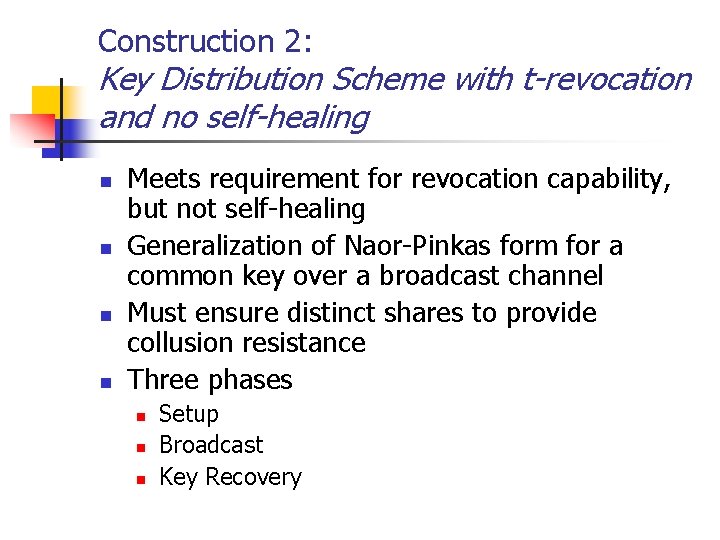
Construction 2: Key Distribution Scheme with t-revocation and no self-healing n n Meets requirement for revocation capability, but not self-healing Generalization of Naor-Pinkas form for a common key over a broadcast channel Must ensure distinct shares to provide collusion resistance Three phases n n n Setup Broadcast Key Recovery
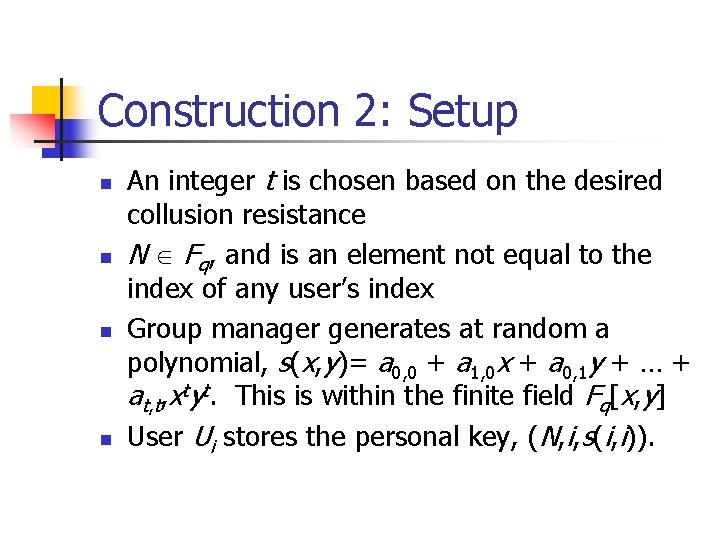
Construction 2: Setup n n An integer t is chosen based on the desired collusion resistance N Î Fq, and is an element not equal to the index of any user’s index Group manager generates at random a polynomial, s(x, y)= a 0, 0 + a 1, 0 x + a 0, 1 y + … + at, t, xtyt. This is within the finite field Fq[x, y] User Ui stores the personal key, (N, i, s(i, i)).
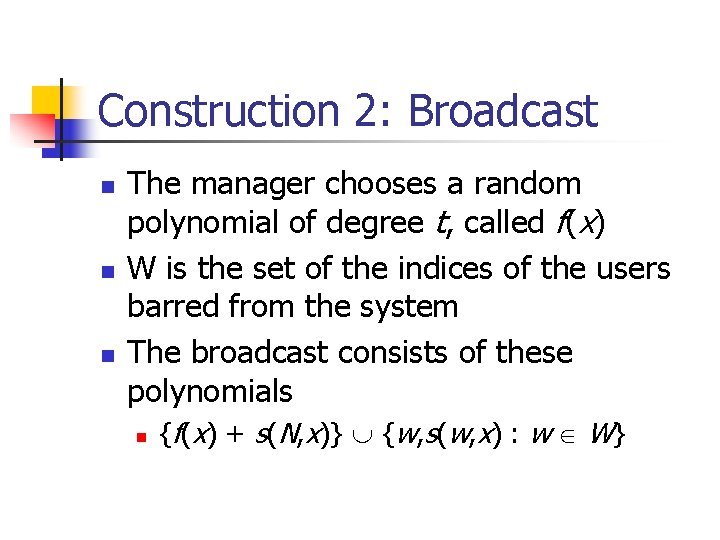
Construction 2: Broadcast n n n The manager chooses a random polynomial of degree t, called f(x) W is the set of the indices of the users barred from the system The broadcast consists of these polynomials n {f(x) + s(N, x)} È {w, s(w, x) : w Î W}
Construction 2: Key Recovery n A valid user (index not in W) evaluates s(w, x) at x = i and uses the results in combination with its personal key in a series of computations to produce the individual key f(i)
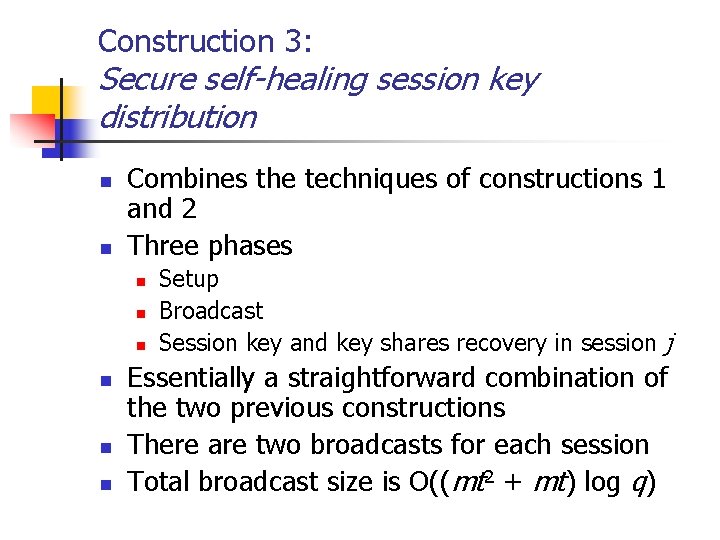
Construction 3: Secure self-healing session key distribution n n Combines the techniques of constructions 1 and 2 Three phases n n n Setup Broadcast Session key and key shares recovery in session j Essentially a straightforward combination of the two previous constructions There are two broadcasts for each session Total broadcast size is O((mt 2 + mt) log q)
Construction 4: Reduced overhead version of Construction 3 n n n The broadcast size of construction 3 can be reduced to O((t 2 + mt) log q) by a few small changes. A pseudorandom sequence is made public and the original list of polynomials is reduced in size. Users use this sequence to generate the remaining polynomials.
Proofs n n All these constructions are proved secure in the appendices of the paper To cover these proofs would be well beyond the scope of this presentation
Practical Issues 1 n Can these constructions be used in realworld applications? n n The authors considered groups of 10, 000 or more members with frequently changing membership Broadcast size isn’t related to number of members, and the parameters that affect the size grow much more slowly
Practical Issues 2 n Session keys late in the m sessions more prone to packet loss since less likelihood of getting a good broadcast after current session n n One solution – a sliding window version of the key distribution schemes Any two packets that “sandwich” a missing transmission closely enough can be used to recover the key
Contributions n n Extends older research on group key distribution to allow use in real-world applications where packet loss is an issue Puts forth a provably secure solution to these problems with a efficient broadcast solution
Weaknesses n Considers only a broadcast based approach with a non-interactive recovery from loss. n Mostly a result of the assumptions of a large group size; peer-to-peer solutions with interactive loss recovery could work quite well with smaller groups.
Any Questions?
- Slides: 39