Robust Group Key Management with Revocation and Collusion
Robust Group Key Management with Revocation and Collusion Resistance for SCADA in Smart Grid Rong Jiang 2013. 07. 31

Agenda � � Introduction The proposed group key management Security analysis and performance evaluation Conclusion 2/19
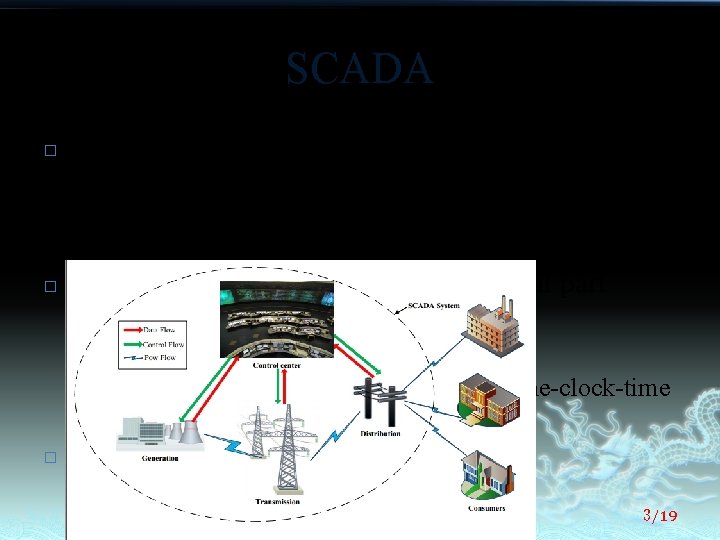
SCADA � � Supervisory Control And Data Acquisition (SCADA) systems are used to monitor and manage the electric distribution, transmission and generation environments. the group communication is an essential part ³ ³ ³ � a status scan request measured value scan request an emergent shutdown message or a set-the-clock-time message Requirement: availability 3/19
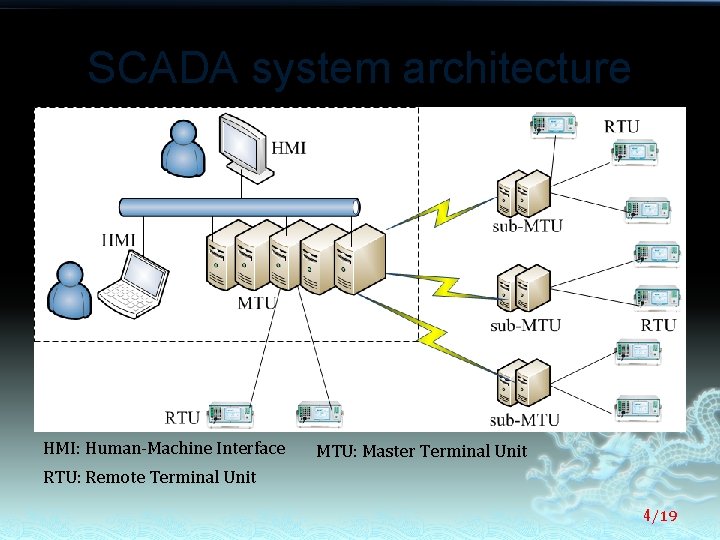
SCADA system architecture HMI: Human-Machine Interface MTU: Master Terminal Unit RTU: Remote Terminal Unit 4/19
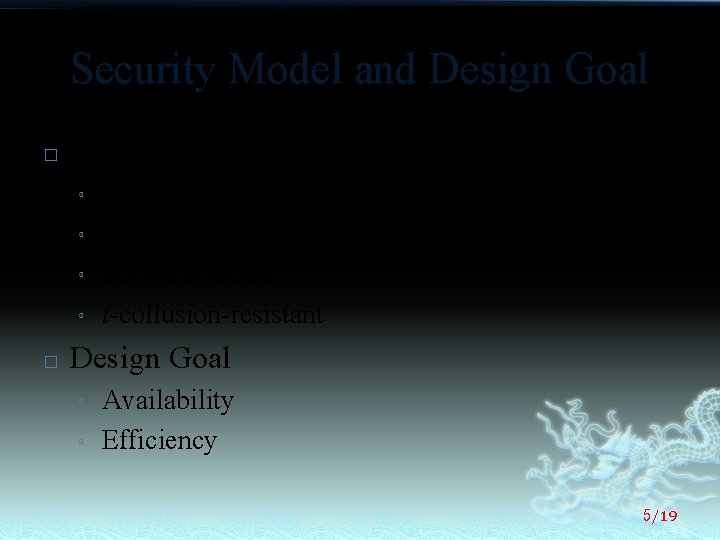
Security Model and Design Goal � Security Model ³ ³ � Group confidentiality Backward secrecy Forward secrecy t-collusion-resistant Design Goal ³ ³ Availability Efficiency 5/19
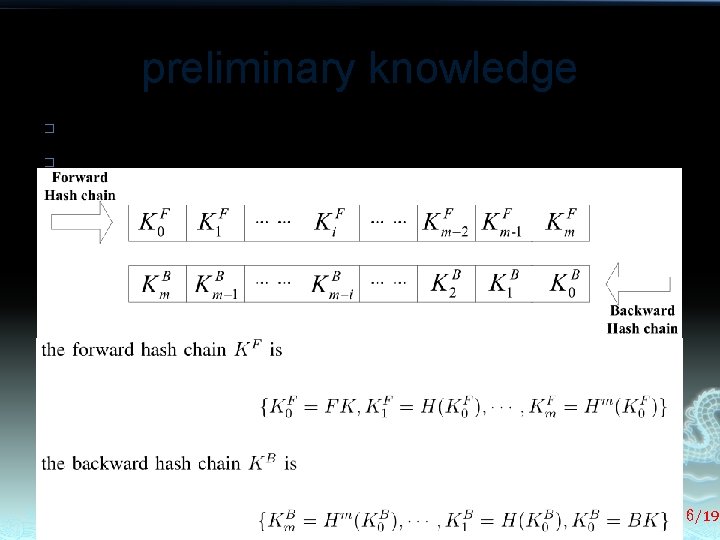
preliminary knowledge � � � Session key DDHC(dual directional hash chain) bivariate polynomial 6/19
Description of Li. SH � � � Initialization Re-keying Self-healing mechanism Adding new member nodes re-initialization mechanism 7/19
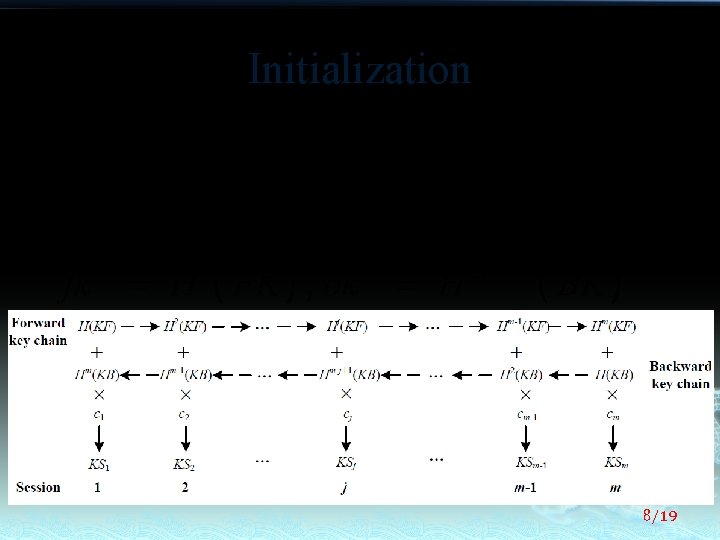
Initialization 8/19
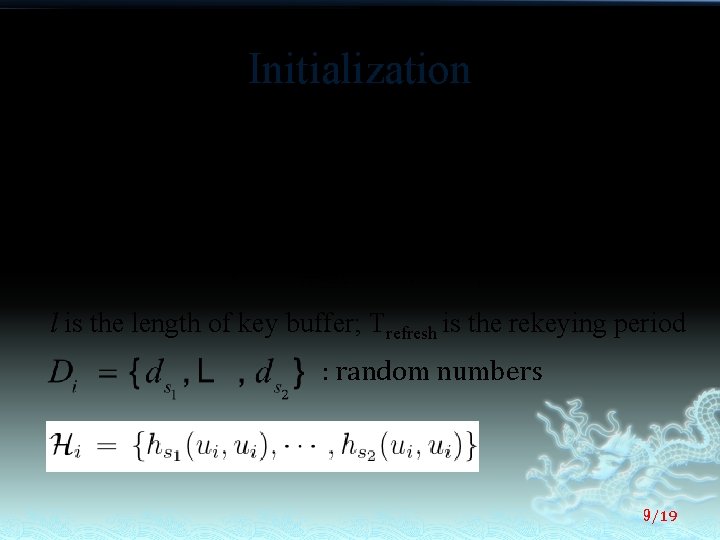
Initialization l is the length of key buffer; Trefresh is the rekeying period : random numbers 9/19
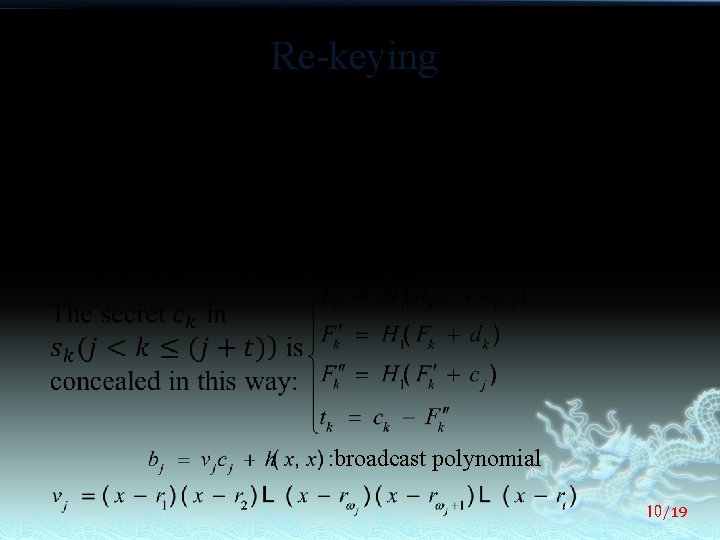
Re-keying the KDC periodically discloses the next secret number C and constructs a selfhealing set T and a revocation set R to expel some illegal nodes. : the set of users all revoked in and before sj : a set of irrelevant users : self-healing set : broadcast polynomial 10/19
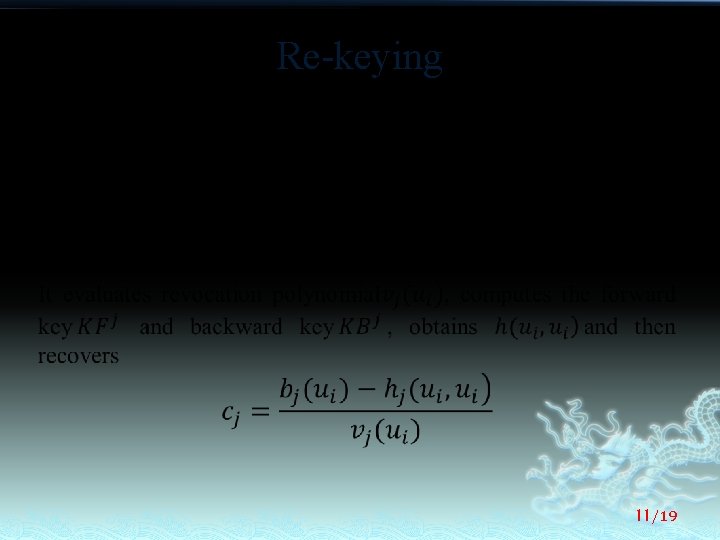
Re-keying 11/19
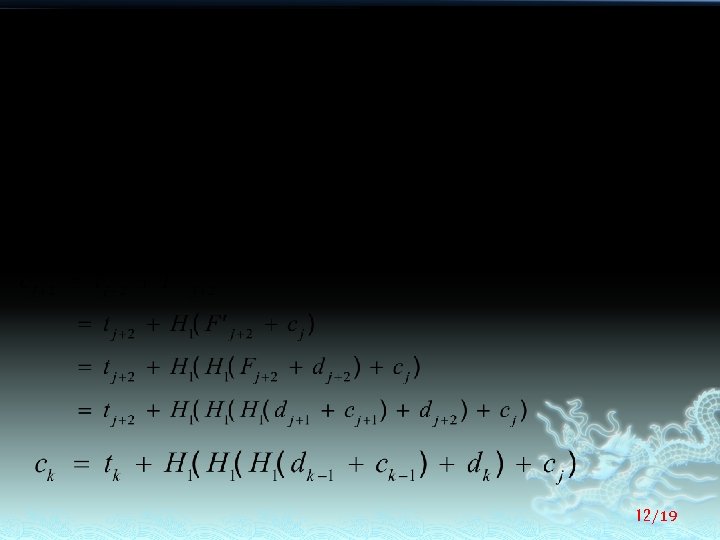
12/19
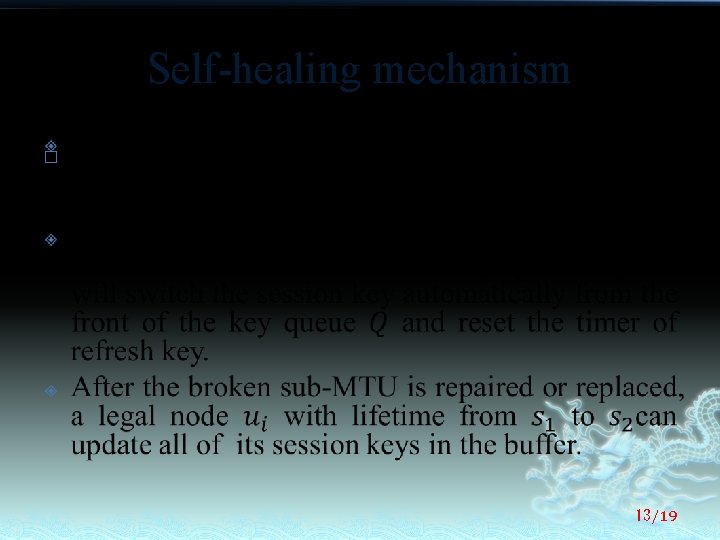
Self-healing mechanism � 13/19
Adding new member nodes � 14/19
Determination of self-healing period � 15/19
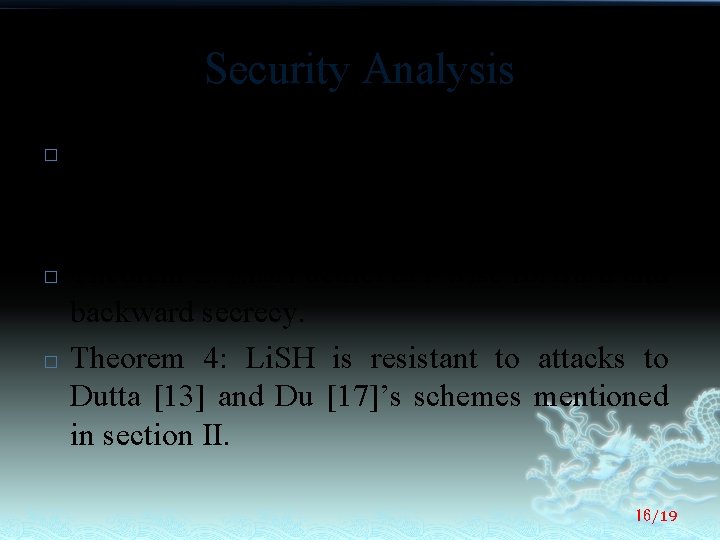
Security Analysis � � � Theorem 1: Li. SH is a session key distribution with privacy and achieves self-healing with time-limited t-revocation capability. Theorem 2: Li. SH achieves t-wise forward and backward secrecy. Theorem 4: Li. SH is resistant to attacks to Dutta [13] and Du [17]’s schemes mentioned in section II. 16/19
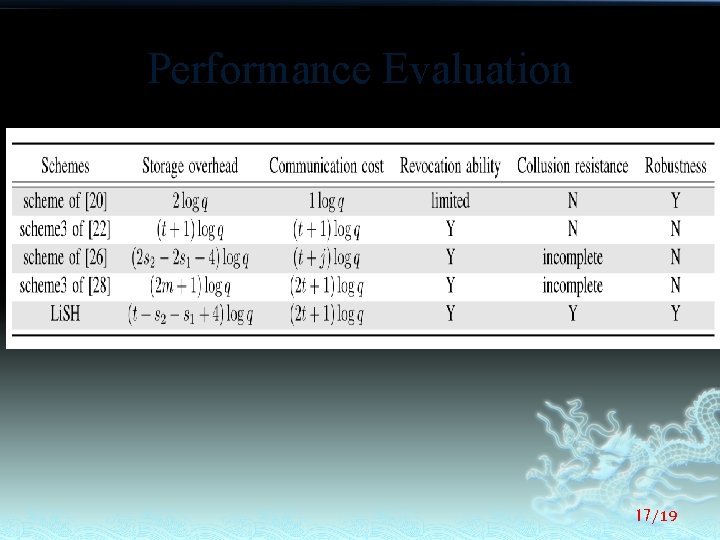
Performance Evaluation 17/19
Conclusion � � � In this paper, we have proposed a robust and efficient group key management, named Li. SH, to secure SCADA system in smart grid. The proposed Li. SH scheme is characterized by adopting self-healing key to tolerant failures of the sub-MTUs. Security analysis has shown that the proposed Li. SH is a collusion-free and selfhealing key distribution scheme with t-wise forward and backward security. In addition, performance evaluation has also demonstrated its efficiency. 18/19
Thank you! 19/19
- Slides: 19