RoleBased Cascaded Delegation A Decentralized Delegation Model for
Role-Based Cascaded Delegation: A Decentralized Delegation Model for Roles Roberto Tamassia Danfeng Yao William H. Winsborough Brown University George Mason University 1
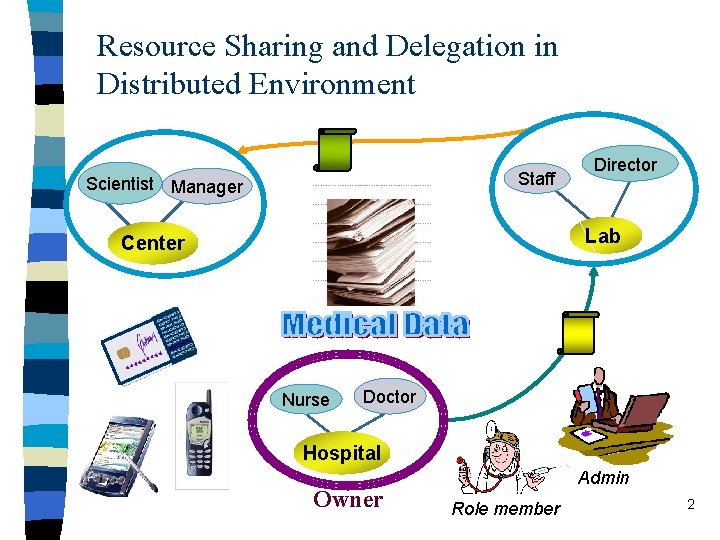
Resource Sharing and Delegation in Distributed Environment Staff Scientist Manager Director Lab Center Nurse Doctor Hospital Owner Admin Role member 2
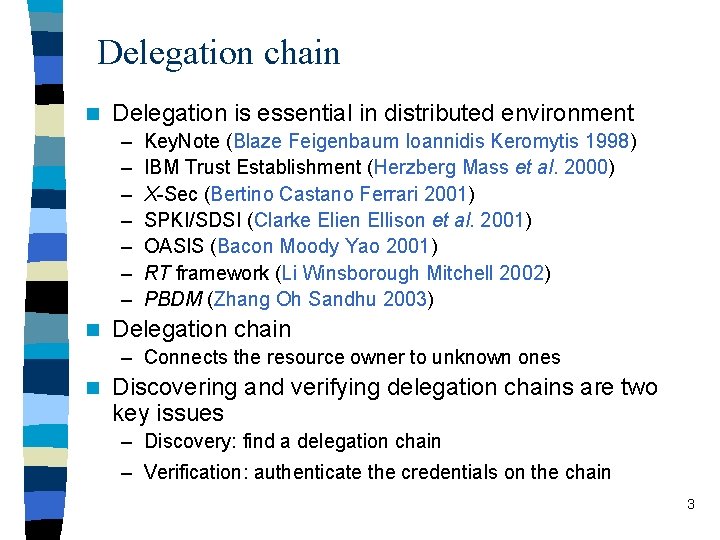
Delegation chain n Delegation is essential in distributed environment – – – – n Key. Note (Blaze Feigenbaum Ioannidis Keromytis 1998) IBM Trust Establishment (Herzberg Mass et al. 2000) X-Sec (Bertino Castano Ferrari 2001) SPKI/SDSI (Clarke Elien Ellison et al. 2001) OASIS (Bacon Moody Yao 2001) RT framework (Li Winsborough Mitchell 2002) PBDM (Zhang Oh Sandhu 2003) Delegation chain – Connects the resource owner to unknown ones n Discovering and verifying delegation chains are two key issues – Discovery: find a delegation chain – Verification: authenticate the credentials on the chain 3
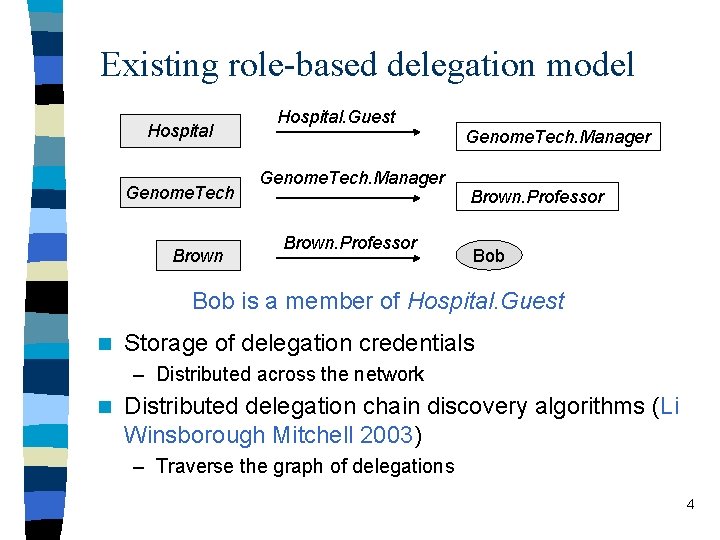
Existing role-based delegation model Hospital Genome. Tech Brown Hospital. Guest Genome. Tech. Manager Brown. Professor Bob is a member of Hospital. Guest n Storage of delegation credentials – Distributed across the network n Distributed delegation chain discovery algorithms (Li Winsborough Mitchell 2003) – Traverse the graph of delegations 4
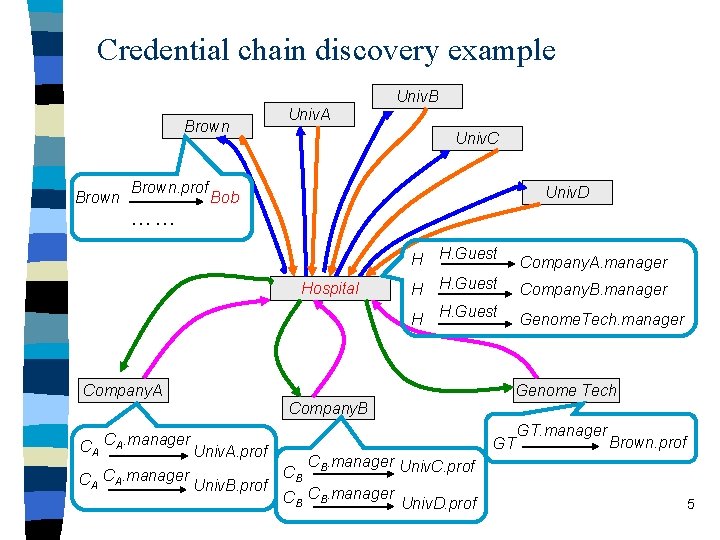
Credential chain discovery example Univ. B Brown. prof …… Univ. A Univ. C Univ. D Bob Hospital H H. Guest Company. A. manager Company. B. manager Genome. Tech. manager Genome Tech Company. B CA CA. manager Univ. A. prof CA CA. manager Univ. B. prof GT CB GT. manager Brown. prof CB. manager Univ. C. prof CB CB. manager Univ. D. prof 5
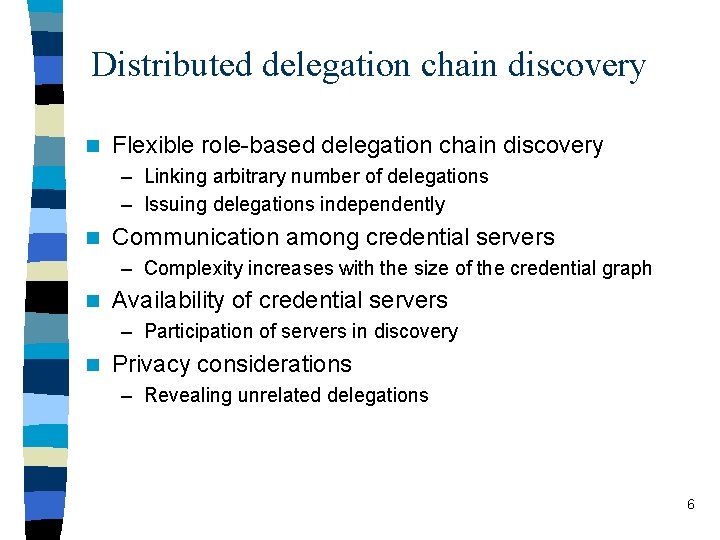
Distributed delegation chain discovery n Flexible role-based delegation chain discovery – Linking arbitrary number of delegations – Issuing delegations independently n Communication among credential servers – Complexity increases with the size of the credential graph n Availability of credential servers – Participation of servers in discovery n Privacy considerations – Revealing unrelated delegations 6
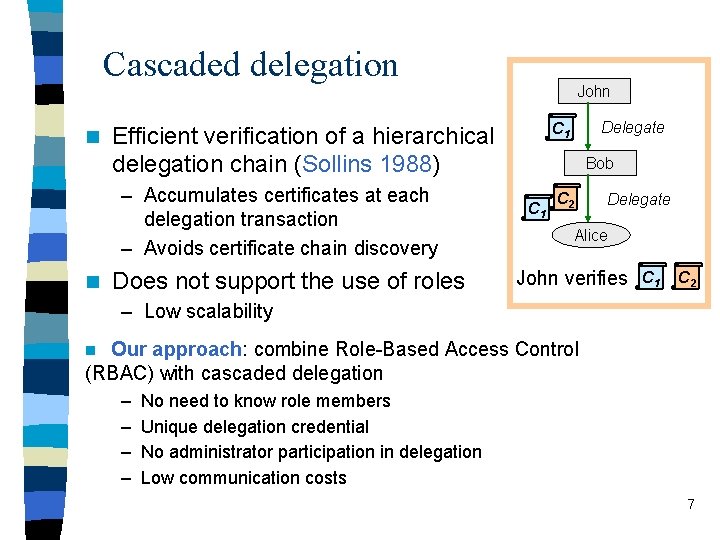
Cascaded delegation n Does not support the use of roles Delegate C 1 Efficient verification of a hierarchical delegation chain (Sollins 1988) – Accumulates certificates at each delegation transaction – Avoids certificate chain discovery n John Bob C 1 C 2 Delegate Alice John verifies C 1 C 2 – Low scalability Our approach: combine Role-Based Access Control (RBAC) with cascaded delegation n – – No need to know role members Unique delegation credential No administrator participation in delegation Low communication costs 7
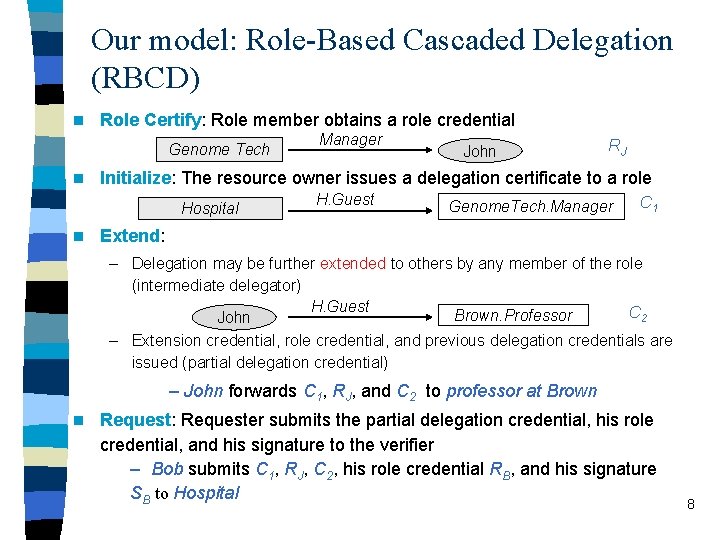
Our model: Role-Based Cascaded Delegation (RBCD) n Role Certify: Role member obtains a role credential Genome Tech n John RJ Initialize: The resource owner issues a delegation certificate to a role Hospital n Manager H. Guest Genome. Tech. Manager C 1 Extend: – Delegation may be further extended to others by any member of the role (intermediate delegator) H. Guest C 2 Brown. Professor John – Extension credential, role credential, and previous delegation credentials are issued (partial delegation credential) – John forwards C 1, RJ, and C 2 to professor at Brown n Request: Requester submits the partial delegation credential, his role credential, and his signature to the verifier – Bob submits C 1, RJ, C 2, his role credential RB, and his signature SB to Hospital 8
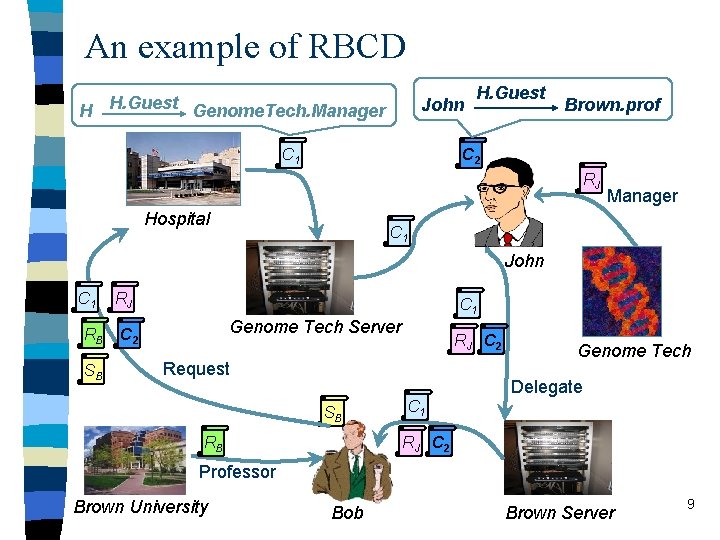
An example of RBCD H H. Guest Genome. Tech. Manager John C 1 H. Guest Brown. prof C 2 RJ Hospital Manager C 1 John C 1 RB SB RJ C 1 Genome Tech Server C 2 RJ C 2 Request Genome Tech Delegate SB RB C 1 RJ C 2 Professor Brown University Bob Brown Server 9
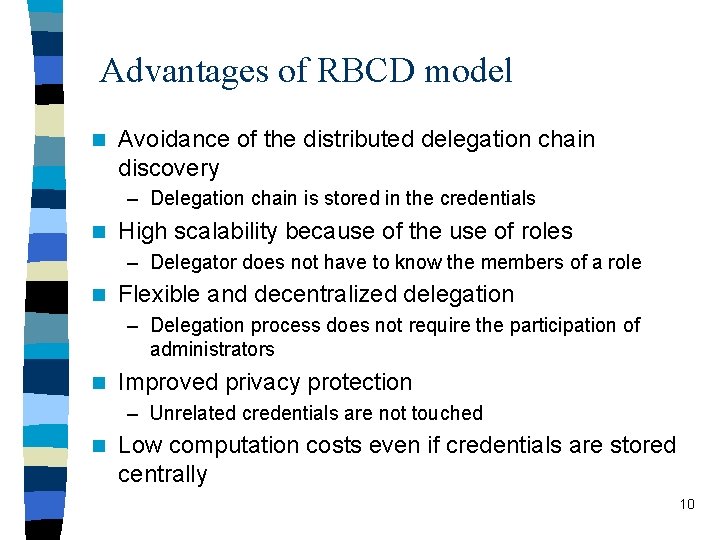
Advantages of RBCD model n Avoidance of the distributed delegation chain discovery – Delegation chain is stored in the credentials n High scalability because of the use of roles – Delegator does not have to know the members of a role n Flexible and decentralized delegation – Delegation process does not require the participation of administrators n Improved privacy protection – Unrelated credentials are not touched n Low computation costs even if credentials are stored centrally 10
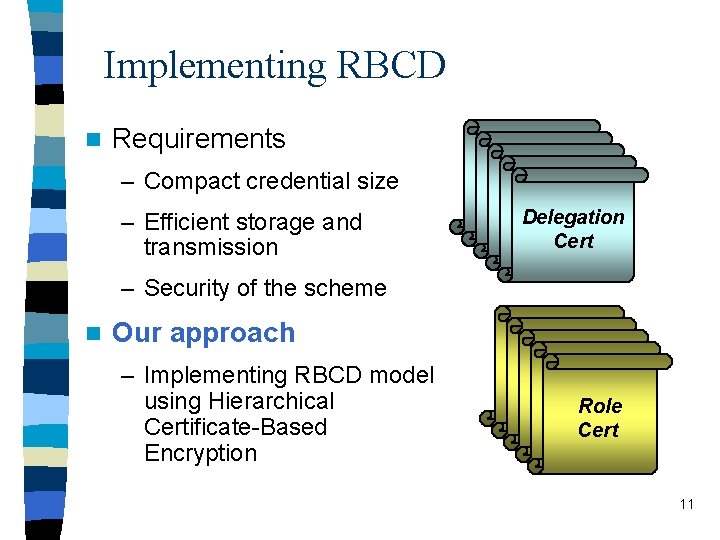
Implementing RBCD n Requirements – Compact credential size – Efficient storage and transmission Delegation Delegation Cert – Security of the scheme n Our approach – Implementing RBCD model using Hierarchical Certificate-Based Encryption Role Role Cert 11
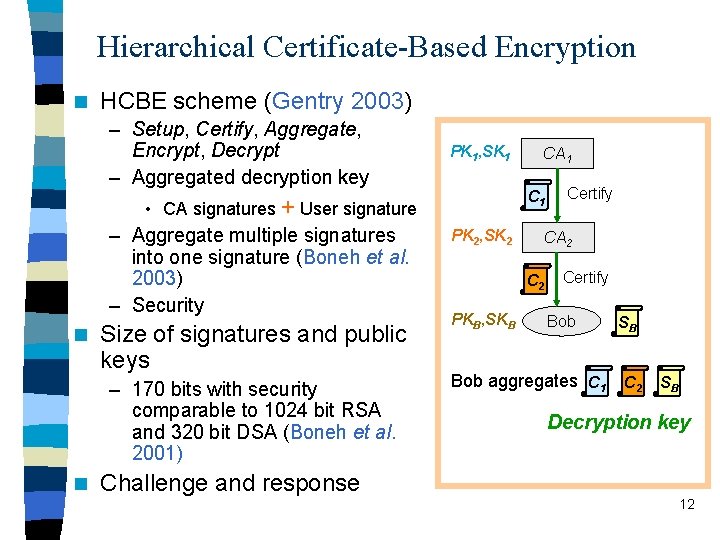
Hierarchical Certificate-Based Encryption n HCBE scheme (Gentry 2003) – Setup, Certify, Aggregate, Encrypt, Decrypt – Aggregated decryption key PK 1, SK 1 C 1 • CA signatures + User signature – Aggregate multiple signatures into one signature (Boneh et al. 2003) – Security n Size of signatures and public keys – 170 bits with security comparable to 1024 bit RSA and 320 bit DSA (Boneh et al. 2001) n CA 1 PK 2, SK 2 CA 2 C 2 PKB, SKB Certify Bob aggregates C 1 SB C 2 SB Decryption key Challenge and response 12
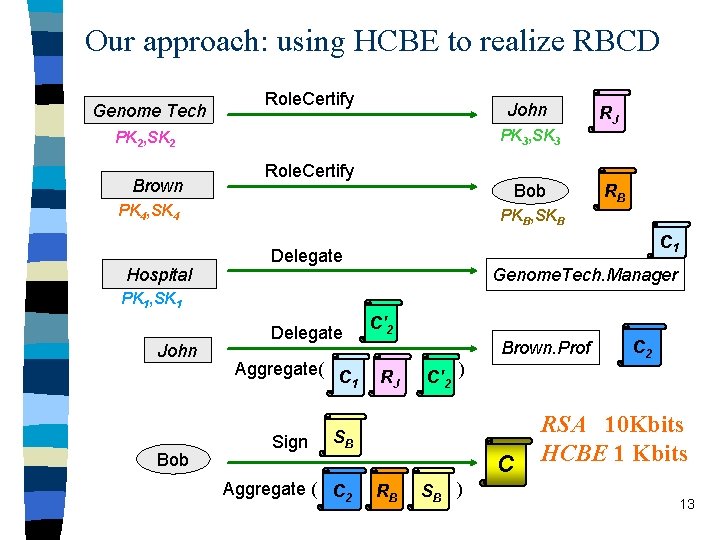
Our approach: using HCBE to realize RBCD Genome Tech Role. Certify John PK 3, SK 3 PK 2, SK 2 Brown Role. Certify Bob PK 4, SK 4 Hospital RJ RB PKB, SKB C 1 Delegate Genome. Tech. Manager PK 1, SK 1 John Bob Delegate Aggregate( C 1 Sign C'2 Brown. Prof RJ C'2 ) SB Aggregate ( C 2 C RB SB ) C 2 RSA 10 Kbits HCBE 1 Kbits 13
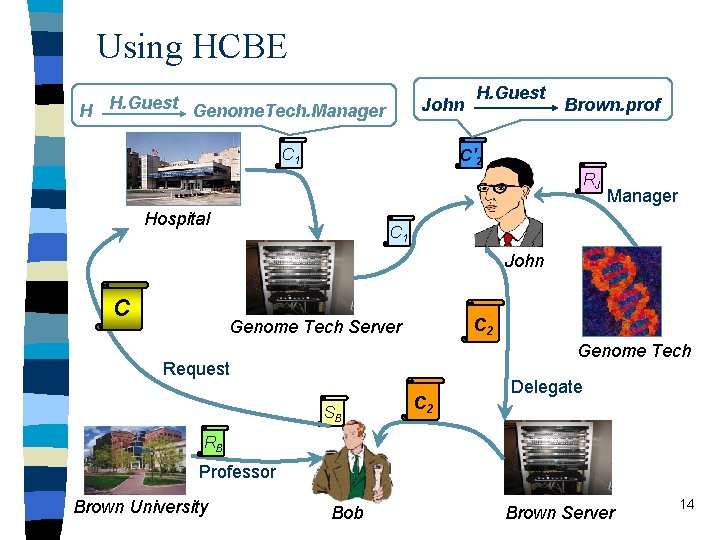
Using HCBE H H. Guest Genome. Tech. Manager John H. Guest Brown. prof C' 2 C 1 RJ Hospital Manager C 1 John C C 2 Genome Tech Server Genome Tech Request SB C 2 Delegate RB Professor Brown University Bob Brown Server 14
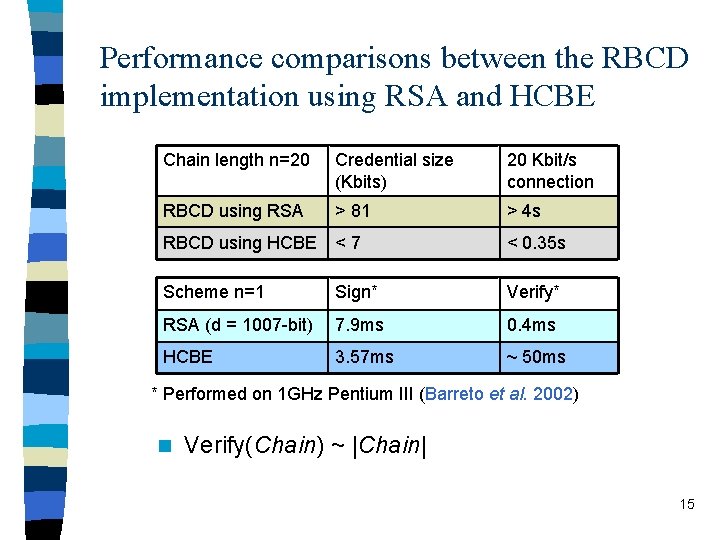
Performance comparisons between the RBCD implementation using RSA and HCBE Chain length n=20 Credential size (Kbits) 20 Kbit/s connection RBCD using RSA > 81 > 4 s RBCD using HCBE < 7 < 0. 35 s Scheme n=1 Sign* Verify* RSA (d = 1007 -bit) 7. 9 ms 0. 4 ms HCBE 3. 57 ms ~ 50 ms * Performed on 1 GHz Pentium III (Barreto et al. 2002) n Verify(Chain) ~ |Chain| 15
Conclusions n Contributions – Role-Based Cascaded Delegation (RBCD) model • • Eliminating credential chain discovery Supporting decentralized delegation Scalable Minimizing exposure of sensitive credentials – Implementation of RBCD using HCBE • Compact credentials n Future work – Integration • Combining RT framework with RBCD • Using XACML as the policy language – Experimental study • Detailed evaluation of communication and computation costs 16
- Slides: 16