Practical EPayment Scheme Author Mohammad AlFayoumi Sattar Aboud
Practical E-Payment Scheme Author: Mohammad Al-Fayoumi, Sattar Aboud, and Mustafa Al-Fayoumi. Source: International Journal of Computer Science Issues, 2010, Vol. 7, No. 3, pp. 18 -23. Presenter: Tsuei-Hung Sun (孫翠鴻) Date: 2010/12/17
Outline èIntroduction èMotivation èScheme èSecurity Analysis èPerformance Evaluation èAdvantage vs. Weakness èComment 2
R. Rivest, A. Shamir, 1996, “Pay. Word and Micro. Mint: two simple micropayment schemes, ” Proceedings of the International Workshop on Security Protocols, LNCS Vol. 1189, pp. 69 -87. Introduction èPay. Word Protocol êCredit-base êOff-line scheme êUsing RSA public key cryptography and hash chain. êDecreasing the number of on-line connections between Bank and Merchant. 3
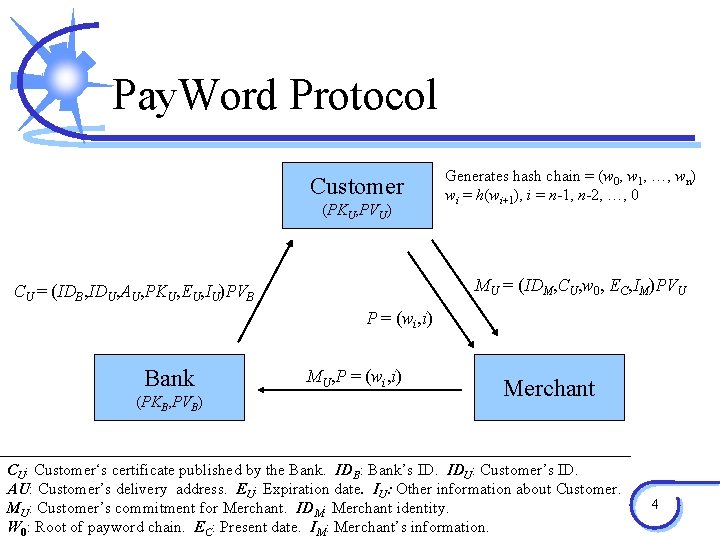
Pay. Word Protocol Customer (PKU, PVU) Generates hash chain = (w 0, w 1, …, wn) wi = h(wi+1), i = n-1, n-2, …, 0 MU = (IDM, CU, w 0, EC, IM)PVU CU = (IDB, IDU, AU, PKU, EU, IU)PVB P = (wi, i) Bank (PKB, PVB) MU, P = (wi, i) Merchant CU: Customer‘s certificate published by the Bank. IDB: Bank’s ID. IDU: Customer’s ID. AU: Customer’s delivery address. EU: Expiration date. IU: Other information about Customer. MU: Customer’s commitment for Merchant. IDM: Merchant identity. W 0: Root of payword chain. EC: Present date. IM: Merchant’s information. 4
Motivation èEach payword chain is spent only to a specific Merchant. èCustomer need to generate hash chain as many as the number of merchants he want to trade with. èNot providing anonymity for Customer. èProposing a new blind signature scheme using discrete logarithm problem. 5
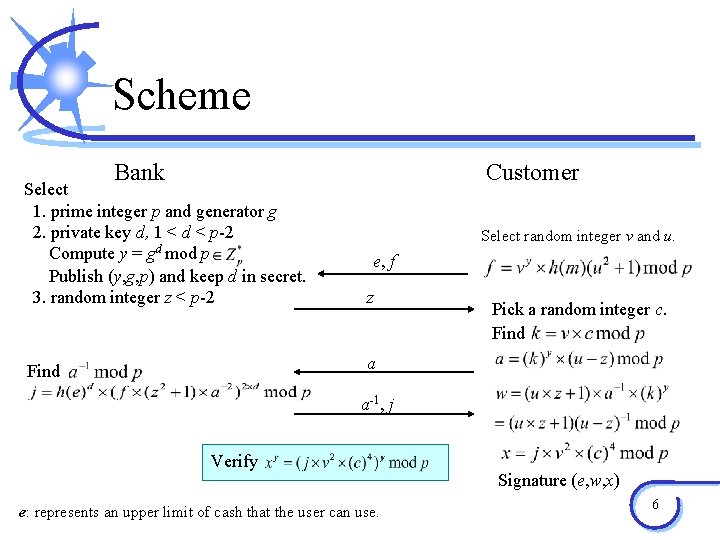
Scheme Bank Customer Select 1. prime integer p and generator g 2. private key d, 1 < d < p-2 Compute y = gd mod p Publish (y, g, p) and keep d in secret. 3. random integer z < p-2 z Find a Select random integer v and u. e, f Pick a random integer c. Find a-1, j Verify e: represents an upper limit of cash that the user can use. Signature (e, w, x) 6
Security Analysis èForgery Detection êIt is almost unfeasible to forge Customer’s payment without knowing Bank’s private key d. êIt is computationally intractable to obtain Bank’s private key without solving the discrete logarithm problem. èShort public key attack êEvery signature is being randomized by certain random numbers. 7
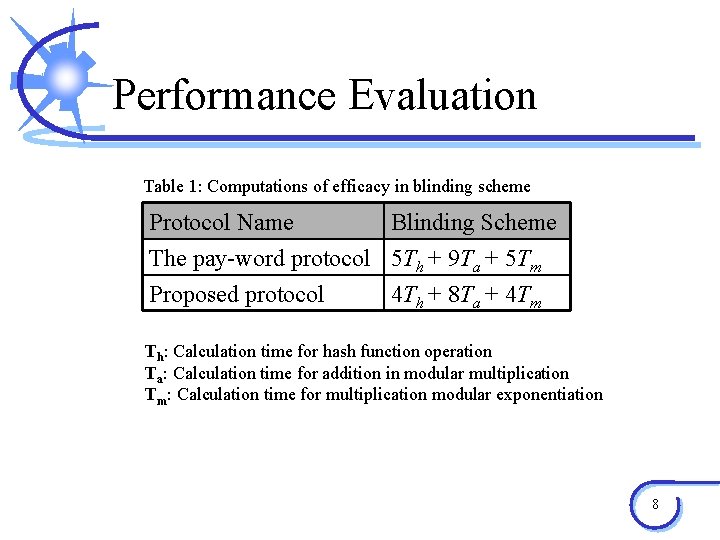
Performance Evaluation Table 1: Computations of efficacy in blinding scheme Protocol Name Blinding Scheme The pay-word protocol 5 Th + 9 Ta + 5 Tm Proposed protocol 4 Th + 8 Ta + 4 Tm Th: Calculation time for hash function operation Ta: Calculation time for addition in modular multiplication Tm: Calculation time for multiplication modular exponentiation 8
Advantage vs. Weakness èAdvantage êMore efficient than the payword protocol. êIt is fast to verify the signature. êGuarantee the payment is untraceable. èWeakness êUsing discrete logarithm is still takes more computing time. êMore complex than the payword protocol. 9
Comment èThe payword chain is generated by Customer. èThe cash can be verified with both Bank’s and Customer’s information. èThe scheme only reduce a little computing time but it bring more parameters and step than the payword protocol. èThe offline payword protocol bring fewer cost then online one. 10
- Slides: 10