MPTCP IDS EVASION MITIGATION ZEESHAN AFZAL STEFAN LINDSKOG
![FLEXIBLE PACKET SCHEDULING Data[0] Data[1] Data[3] Data[2] Data Client Data Server 7 FLEXIBLE PACKET SCHEDULING Data[0] Data[1] Data[3] Data[2] Data Client Data Server 7](https://slidetodoc.com/presentation_image_h2/ddc9f9b59952448d342bc04ca3fae9b6/image-7.jpg)


- Slides: 24
MPTCP IDS EVASION & MITIGATION ZEESHAN AFZAL & STEFAN LINDSKOG KARLSTAD UNIVERSITY, SWEDEN
OUTLINE • BACKGROUND • QUESTIONS • METHODOLOGY • RESULTS • SOLUTION • FUTURE 2
MPTCP IN THE MEDIA 3
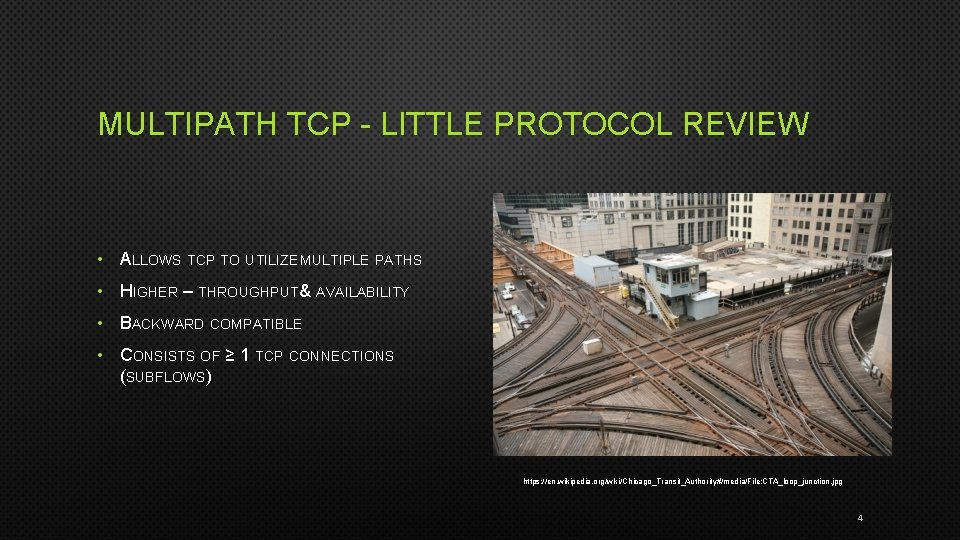
MULTIPATH TCP - LITTLE PROTOCOL REVIEW • ALLOWS TCP TO UTILIZE MULTIPLE PATHS • HIGHER – THROUGHPUT& AVAILABILITY • BACKWARD COMPATIBLE • CONSISTS OF ≥ 1 TCP CONNECTIONS (SUBFLOWS) https: //en. wikipedia. org/wiki/Chicago_Transit_Authority#/media/File: CTA_loop_junction. jpg 4
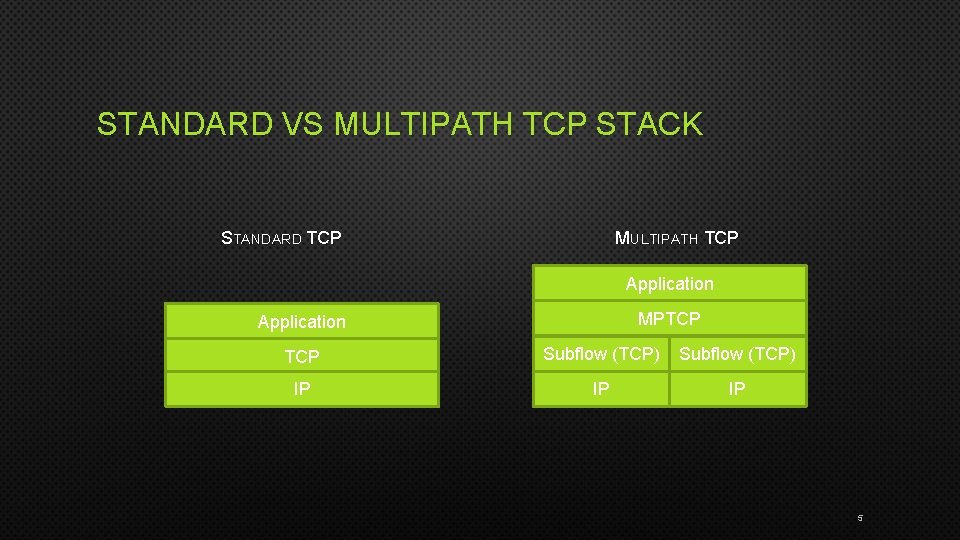
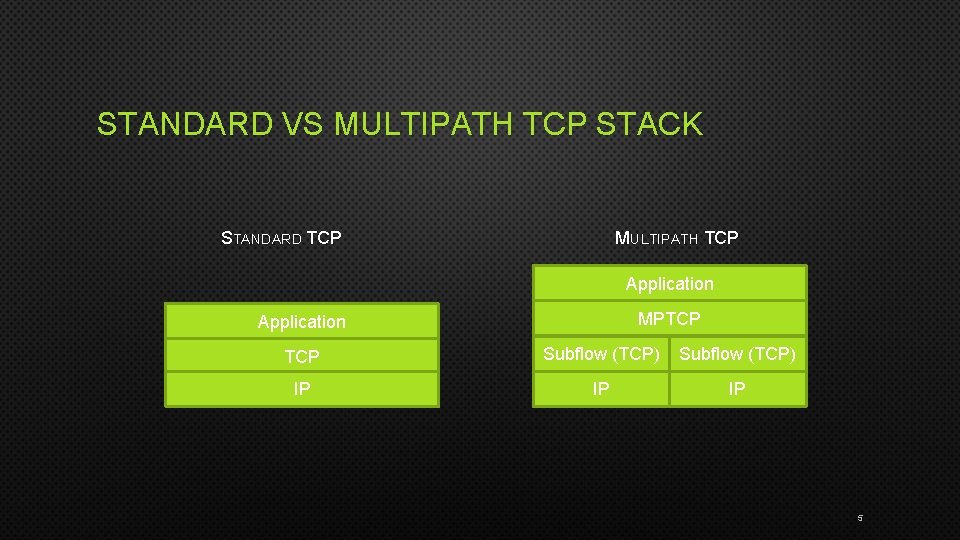
STANDARD VS MULTIPATH TCP STACK STANDARD TCP MULTIPATH TCP Application MPTCP Application TCP Subflow (TCP) IP IP IP 5
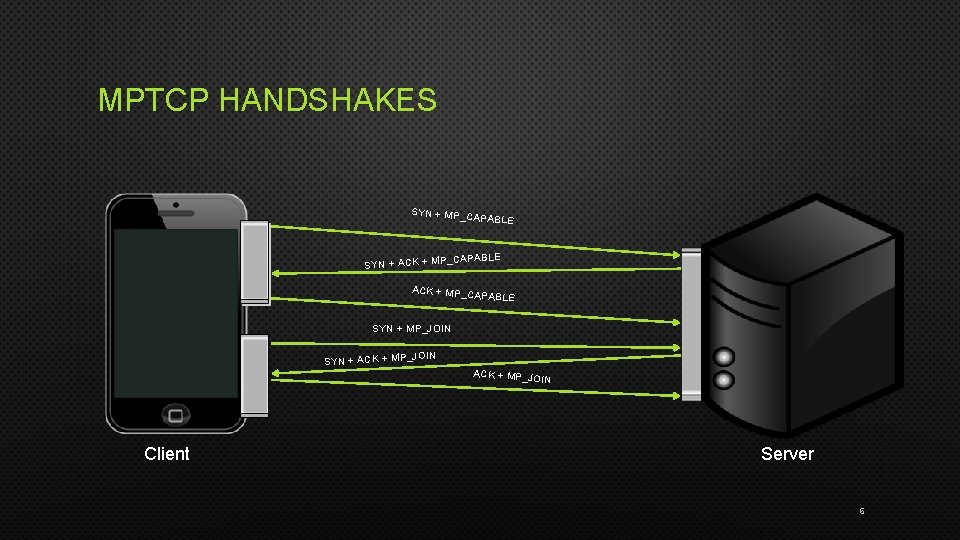
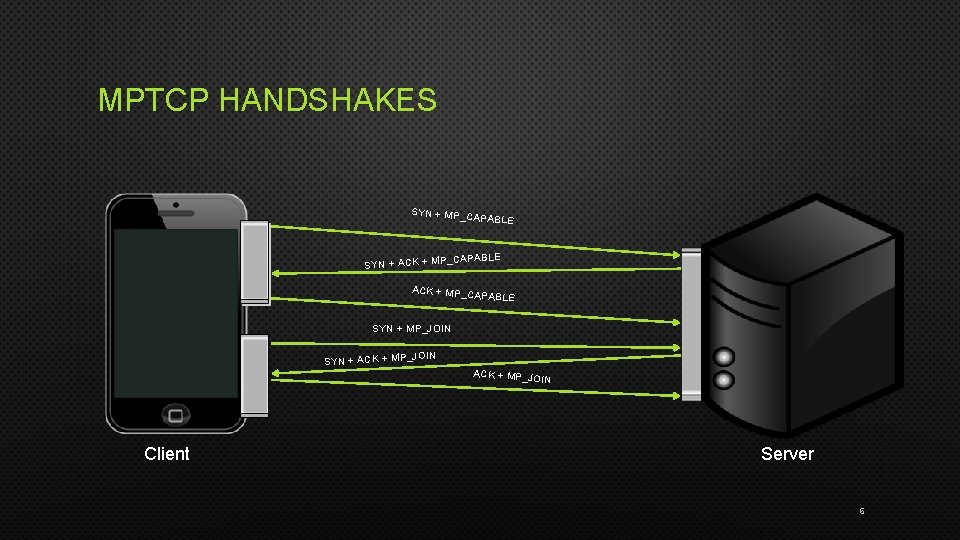
MPTCP HANDSHAKES SYN + MP_C APABLE CAPABLE SYN + ACK + MP_C APABLE SYN + MP_JOIN SYN + ACK + MP_JO IN Client Server 6
![FLEXIBLE PACKET SCHEDULING Data0 Data1 Data3 Data2 Data Client Data Server 7 FLEXIBLE PACKET SCHEDULING Data[0] Data[1] Data[3] Data[2] Data Client Data Server 7](https://slidetodoc.com/presentation_image_h2/ddc9f9b59952448d342bc04ca3fae9b6/image-7.jpg)
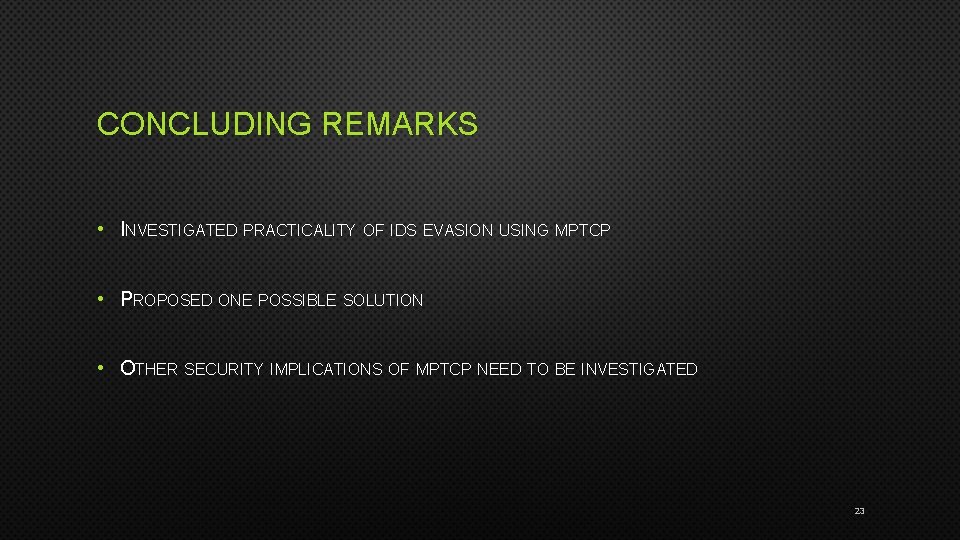
FLEXIBLE PACKET SCHEDULING Data[0] Data[1] Data[3] Data[2] Data Client Data Server 7
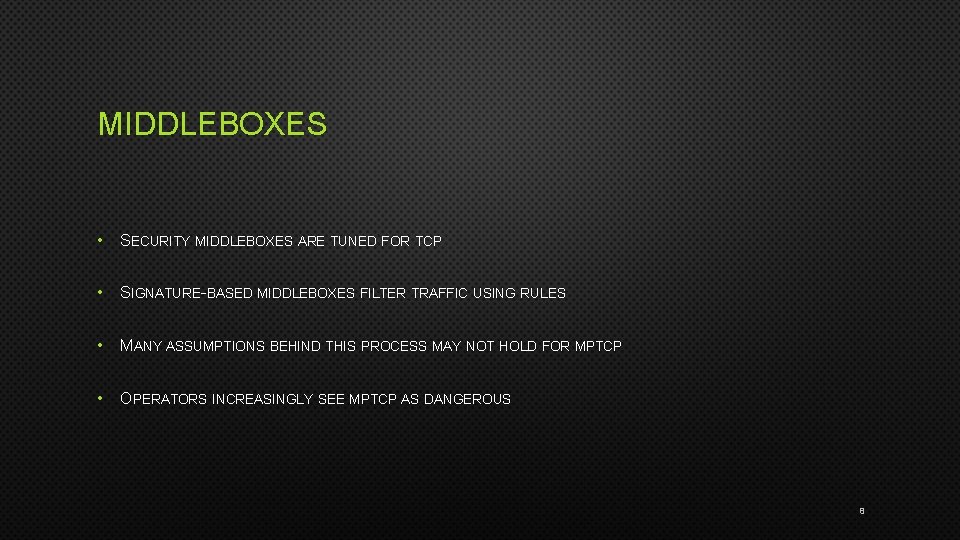
MIDDLEBOXES • SECURITY MIDDLEBOXES ARE TUNED FOR TCP • SIGNATURE-BASED MIDDLEBOXES FILTER TRAFFIC USING RULES • MANY ASSUMPTIONS BEHIND THIS PROCESS MAY NOT HOLD FOR MPTCP • OPERATORS INCREASINGLY SEE MPTCP AS DANGEROUS 8
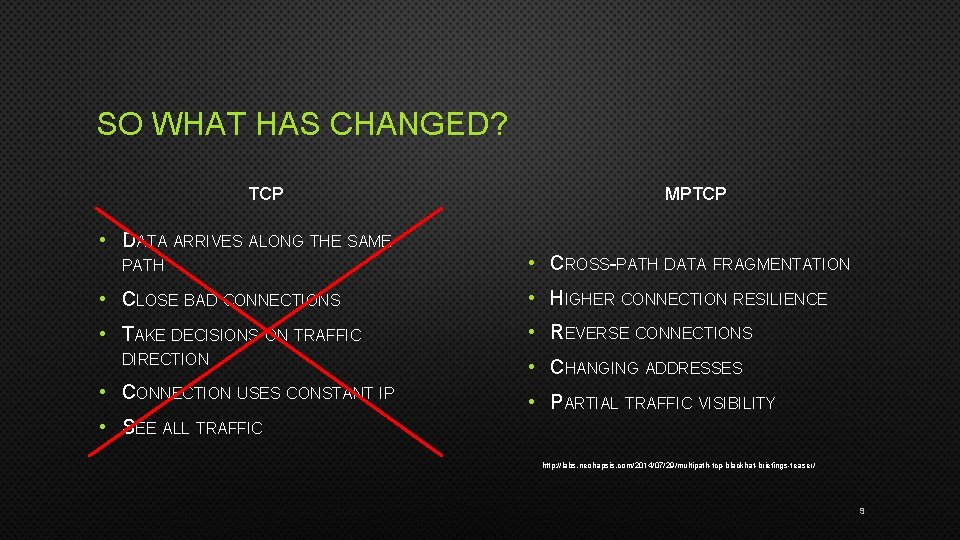
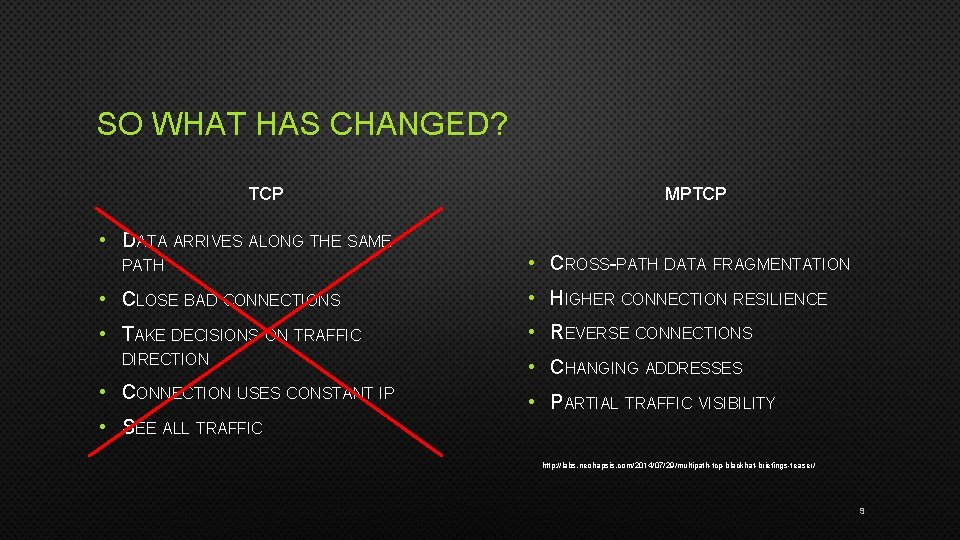
SO WHAT HAS CHANGED? TCP • DATA ARRIVES ALONG THE SAME PATH MPTCP • CROSS-PATH DATA FRAGMENTATION • CLOSE BAD CONNECTIONS • HIGHER CONNECTION RESILIENCE • TAKE DECISIONS ON TRAFFIC • REVERSE CONNECTIONS DIRECTION • CONNECTION USES CONSTANT IP • CHANGING ADDRESSES • PARTIAL TRAFFIC VISIBILITY • SEE ALL TRAFFIC http: //labs. neohapsis. com/2014/07/29/multipath-tcp-blackhat-briefings-teaser/ 9
QUESTIONS • HOW MANY RULES WILL BE AFFECTED BY CROSS-PATH DATA FRAGMENTATION? • HOW DO THE CURRENT IDS SOLUTIONS REACT TO IT? • WHAT IS THE SEVERITY OF THE SITUATION? • IS THERE A SOLUTION TO THE PROBLEM? 10
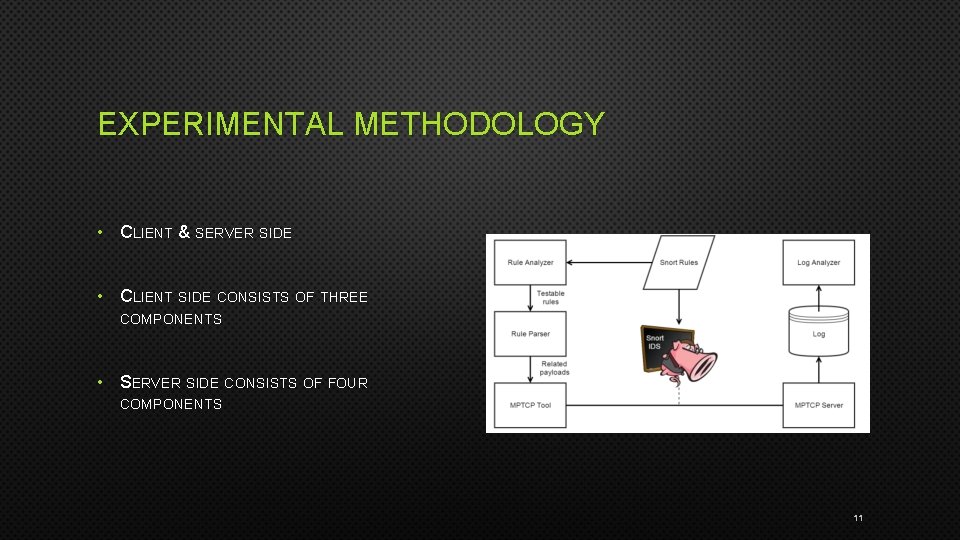
EXPERIMENTAL METHODOLOGY • CLIENT & SERVER SIDE • CLIENT SIDE CONSISTS OF THREE COMPONENTS • SERVER SIDE CONSISTS OF FOUR COMPONENTS 11
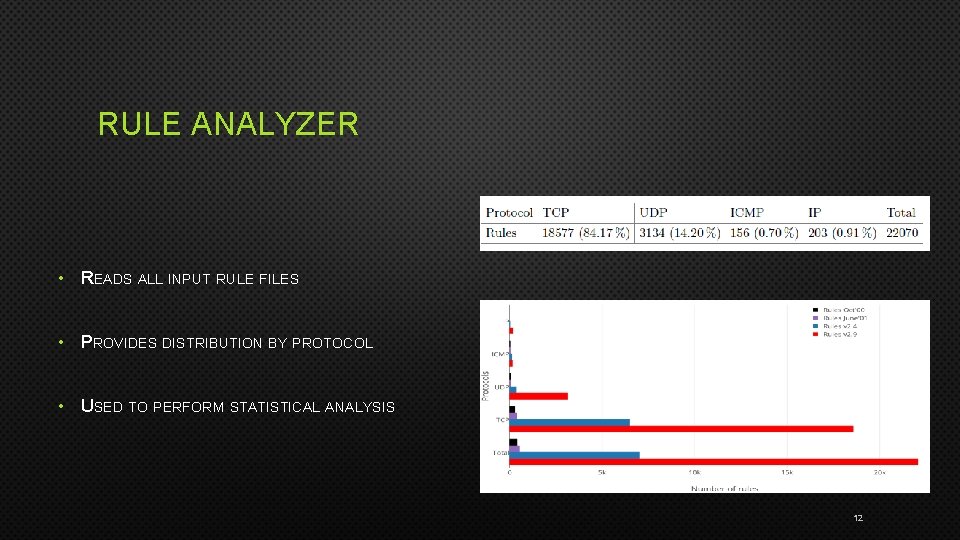
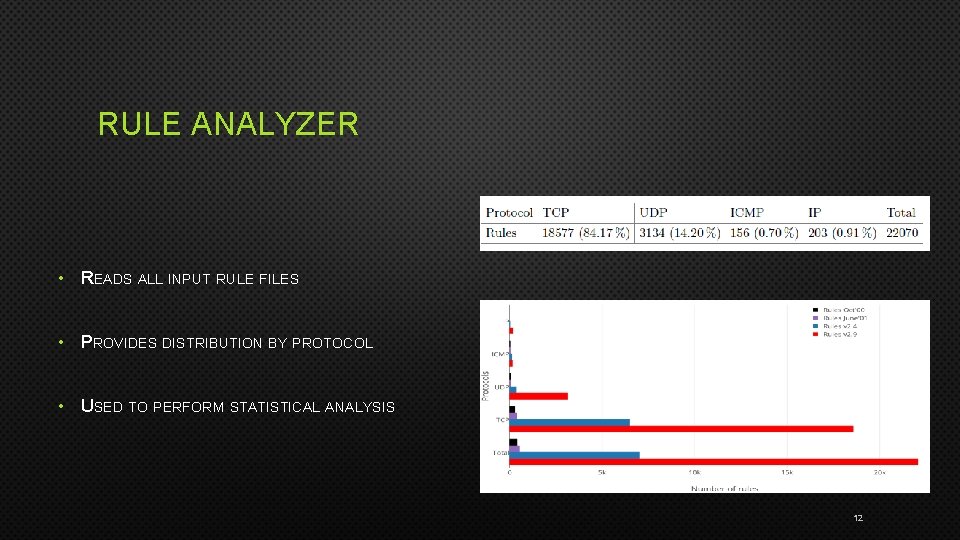
RULE ANALYZER • READS ALL INPUT RULE FILES • PROVIDES DISTRIBUTION BY PROTOCOL • USED TO PERFORM STATISTICAL ANALYSIS 12
RULE PARSER • A MECHANISM TO TRANSLATE RULES TO PAYLOADS • PARSES EVERY RULE AND CRAFTS A CONSISTENT PAYLOAD • SUPPORTS A LARGE VARIETY OF COMMON KEYWORDS 13

MPTCP TOOL/CLIENT • 14
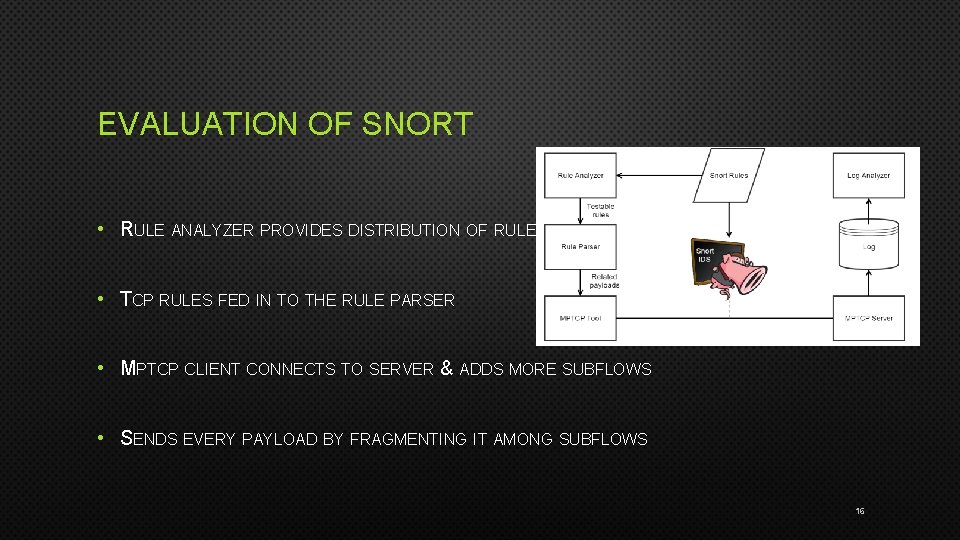
SERVER SIDE • MPTCP SERVER RECEIVES THE DATA • SNORT OPERATES ON THE PATH WITH SAME RULES AND WRITES ALERTS TO A LOG FILE • LOG ANALYZER READS THE LOG FILE AND GENERATES RESULTS 15
EVALUATION OF SNORT • RULE ANALYZER PROVIDES DISTRIBUTION OF RULES • TCP RULES FED IN TO THE RULE PARSER • MPTCP CLIENT CONNECTS TO SERVER & ADDS MORE SUBFLOWS • SENDS EVERY PAYLOAD BY FRAGMENTING IT AMONG SUBFLOWS 16
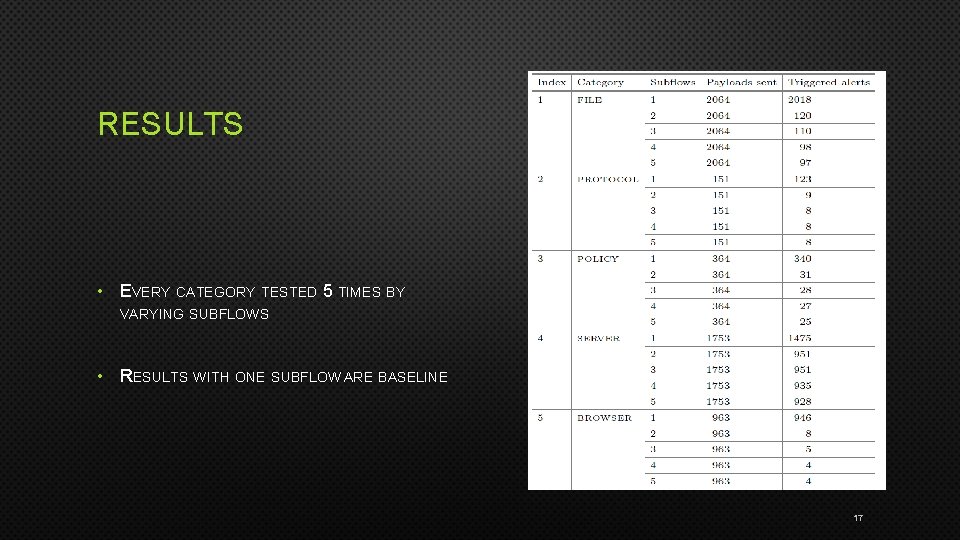
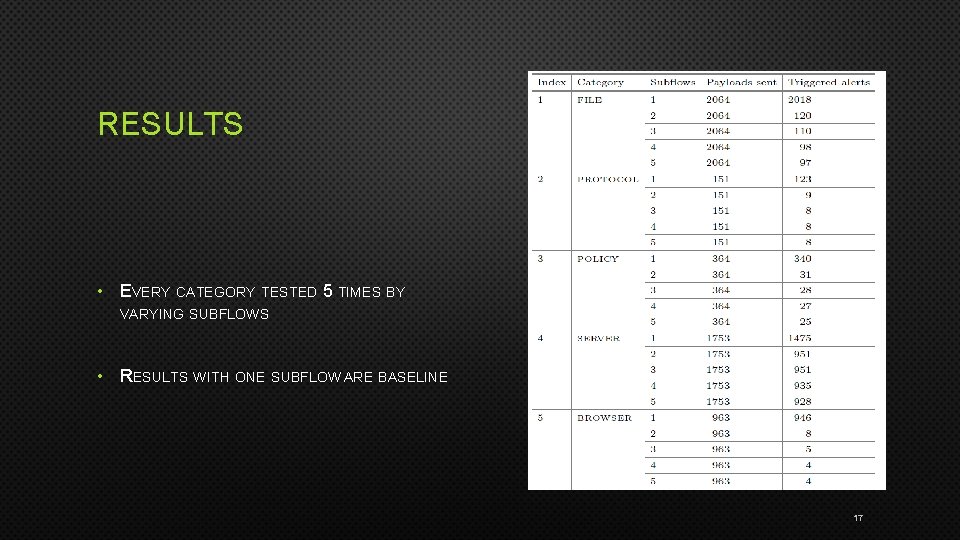
RESULTS • EVERY CATEGORY TESTED 5 TIMES BY VARYING SUBFLOWS • RESULTS WITH ONE SUBFLOW ARE BASELINE 17
SNORT IS CONFUSED! • LOWER NUMBER OF DETECTED ALERTS BY SNORT THAN EXPECTED • SNORT TREATS EVERY SUBFLOW AS AN INDEPENDENT TCP CONNECTION • TRIES TO MATCH SIGNATURES WITHIN EACH SUBFLOW WITH NO CORRELATION 18

DEFENSE • PEOPLE • TECHNOLOGY - INFRASTRUCTURE NEEDS TO BECOME MPTCP AWARE • FULL TRAFFIC VISIBILITY • PARTIAL TRAFFIC VISIBILITY 19
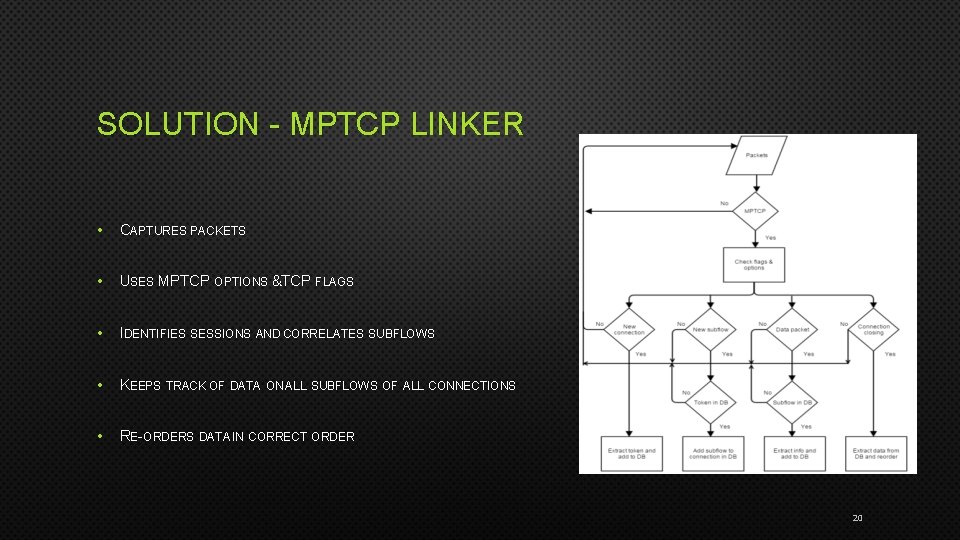
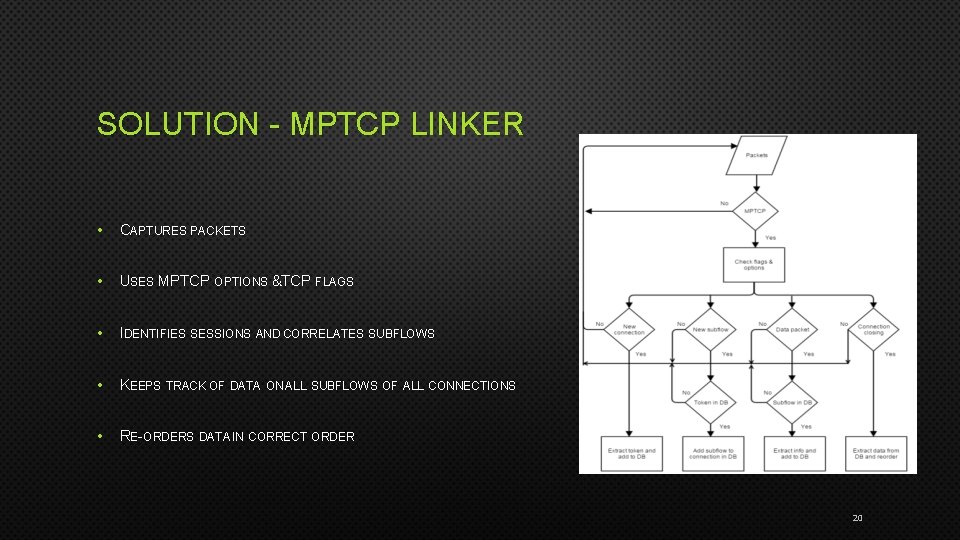
SOLUTION - MPTCP LINKER • CAPTURES PACKETS • USES MPTCP OPTIONS &TCP FLAGS • IDENTIFIES SESSIONS AND CORRELATES SUBFLOWS • KEEPS TRACK OF DATA ON ALL SUBFLOWS OF ALL CONNECTIONS • RE-ORDERS DATA IN CORRECT ORDER 20
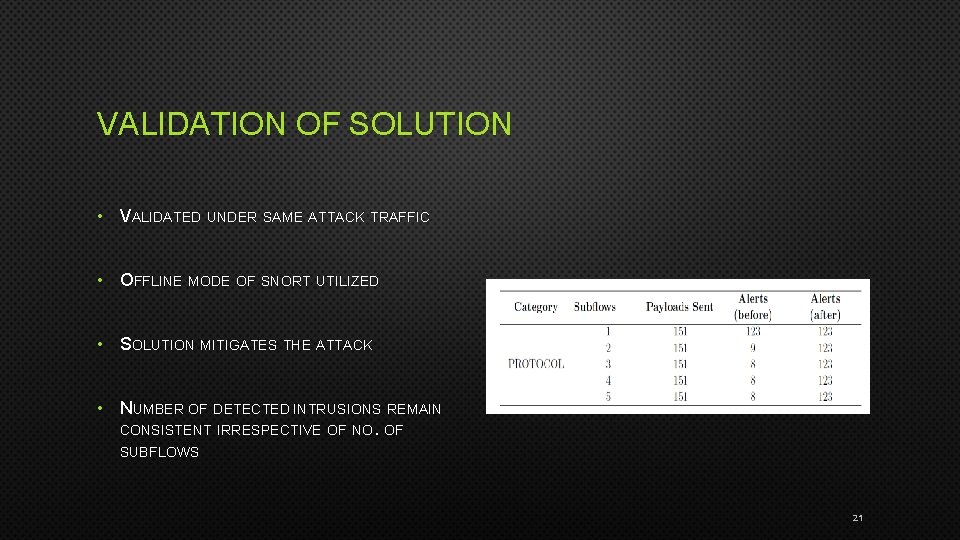
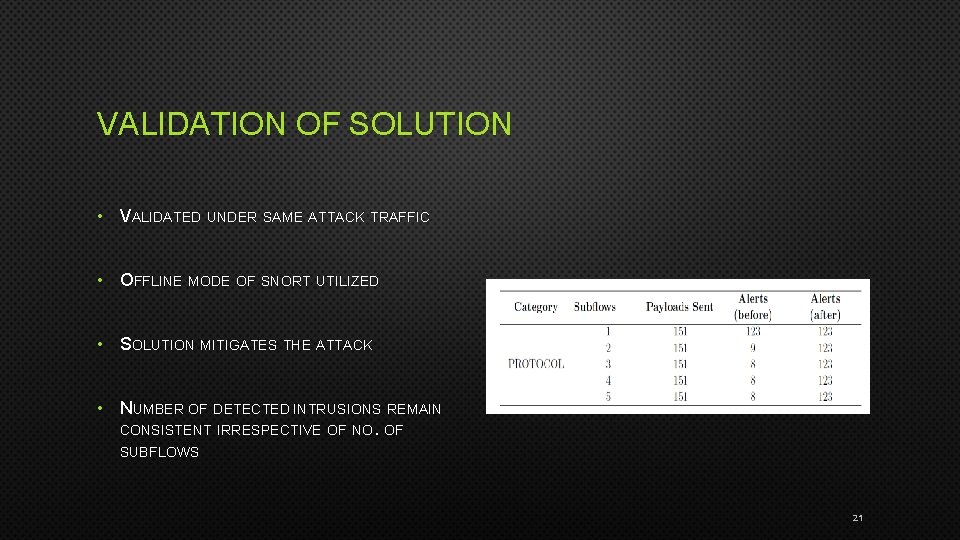
VALIDATION OF SOLUTION • VALIDATED UNDER SAME ATTACK TRAFFIC • OFFLINE MODE OF SNORT UTILIZED • SOLUTION MITIGATES THE ATTACK • NUMBER OF DETECTED INTRUSIONS REMAIN CONSISTENT IRRESPECTIVE OF NO. OF SUBFLOWS 21
OUTLOOK • NEW COMMUNICATION TECHNOLOGIES ARE COMING • NETWORK SECURITY NEEDS TO EVOLVE • “DETECTING DISTRIBUTED SIGNATURE-BASED INTRUSION: THE CASE OF MULTI-PATH ROUTING ATTACKS’’ BY MA ET AL. IN PROC. OF IEEE INFOCOM. 2015 • MPTCP PROXY SOLUTION UNDER DEVELOPMENT • PARADIGM SHIFTS MIGHT BE REQUIRED 22
CONCLUDING REMARKS • INVESTIGATED PRACTICALITY OF IDS EVASION USING MPTCP • PROPOSED ONE POSSIBLE SOLUTION • OTHER SECURITY IMPLICATIONS OF MPTCP NEED TO BE INVESTIGATED 23
THANK YOU. QUESTIONS?