MODEL BASED SECURITY WITH UMLsec Pankaj Chechani 005240093
MODEL BASED SECURITY WITH UMLsec Pankaj Chechani 005240093
AGENDA Approach for secure software Security requirements provided by UMLsec UML Extension Mechanism UMLsec Analysis Conclusion
APPROACH FOR SECURE SOFTWARE Penetrate-and-Patch insecure, Formal verification Very delay, annoying expensive Security at design time
SECURITY REQUIREMENTS PROVIDED BY UMLSEC Fair Exchange Secure Information Flow Secure Communication Link Role-based Access Control Authenticity
UML EXTENSION MECHANISM “Light-Weight” Extension Mechanism Constrains Properties that have to hold {xor} Tagged values Describe properties of model elements {username=“abc”, pass =“xyz”} Stereotypes “Lots of” constraints and tagged values • Class + <<interface>> = Interface
![EXAMPLE <<SECURE LINK>>[1] Security requirements dependency stereotypes Physical layer link stereotypes Communication partners Node EXAMPLE <<SECURE LINK>>[1] Security requirements dependency stereotypes Physical layer link stereotypes Communication partners Node](http://slidetodoc.com/presentation_image_h2/5d8aca1a9a302660e9cb4d90d02a00a6/image-6.jpg)
EXAMPLE <<SECURE LINK>>[1] Security requirements dependency stereotypes Physical layer link stereotypes Communication partners Node stereotypes
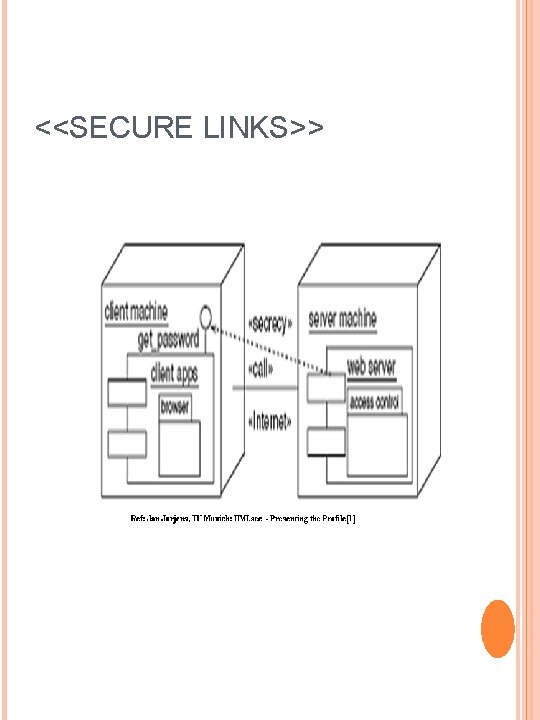
<<SECURE LINKS>>
UMLSEC ANALYSIS Two popular approaches: 1. Formulate requirements with a special logic 2. Use term-algebra Ref: [2] UMLsec follows term-algebra approach Both are quite successful
CONT… Term algebra generated by Variables, Keys and Data Operations: _: : _(concatenation), Head(_) {_}_ and Tail (_), (encryption), Dec_{_} (decryption), Ref: [1] & [3] o Equations(some): Deck-1 ({E}K) = E (for K E Keys), Ext. K (Sign. K-1(E)) = E(for K E Keys). Ref: [1] & [3]
CONCLUSION UMLsec provide security at design phase Automatisms security analysis by tool support Concentrates on data security, ecommerce scenarios, protocols UMLsec itself is extensible
![REFERENCE [1] Jan Jurjens, TU Munich: UMLsec - Presenting the Profile [2] Jan Jurjens, REFERENCE [1] Jan Jurjens, TU Munich: UMLsec - Presenting the Profile [2] Jan Jurjens,](http://slidetodoc.com/presentation_image_h2/5d8aca1a9a302660e9cb4d90d02a00a6/image-11.jpg)
REFERENCE [1] Jan Jurjens, TU Munich: UMLsec - Presenting the Profile [2] Jan Jurjens, Secure System Development With UML [3]Matthias Wurm, Seminar Advanced System: Development of Secure Systems with UMLsec [4] Joe Combs, 15 Feb 2006: Discussing “Developing Secure Systems with UMLSec”
THANK YOU
- Slides: 12