Malicious Software Index Introduction Terminologies Categories Backdoors Logic
Malicious Software

Index �Introduction �Terminologies �Categories �Backdoors �Logic Bomb �Trojan Horse �Nimda attack �Important questions
Introduction Malicious software also known commonly as malware refers to a more sophisticated type of threat to the computer system which are presented by programs that exploit vulnerabilities in computing systems.
More about Malware �Malware is a software designed to cause damage to or use up the resources of a target computer �It is concealed within or masquerades as legitimate software �In some cases it spreads itself via email or infected floppy disks
Terminologies �Virus: malware that when executed tries to replicate itself into another executable code , this code is said to be infected. when the infected code is executed the virus also executes. �Worm: a program that can run independently and propagate a working version of itself onto other hosts.
�Mobile code: software that can be shipped to a collection of platforms and execute with identical semantics. �Auto-rooter: malicious hacker tools used to break into new machines remotely. �Kit : set of tools to generate virus automatically. �Spammer programs : used to send large volumes of unwanted emails. �Flooder : used to attack networked computer with a large volume of traffic to carry out a denial of service attack.
�Root kit : set of tools used after attacker has broken into a system and gained root level control. �Zombie , bot : program activated on infected machine that is further activated to launch attacks on other machines. �Spyware : software that collects information from a computer and transmits it into another system. �Adware : advertising that is integrated into software that can result in pop ups or redirection of a browser onto a commercial site.
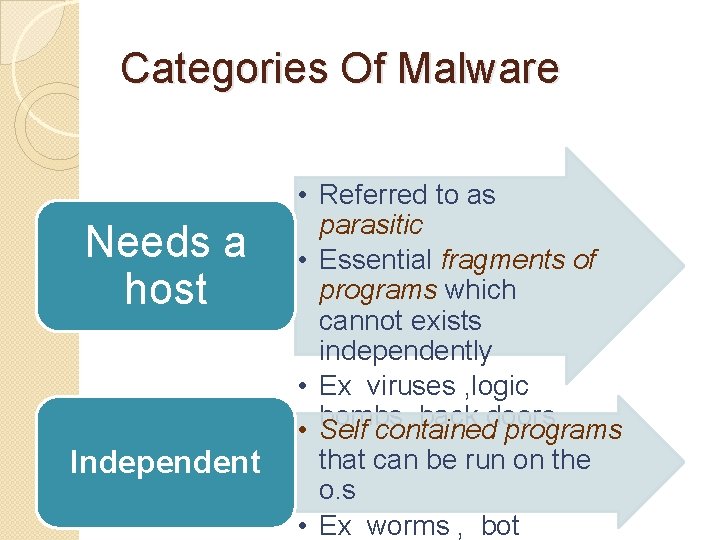
Categories Of Malware Needs a host Independent • Referred to as parasitic • Essential fragments of programs which cannot exists independently • Ex viruses , logic bombs , back doors • Self contained programs that can be run on the o. s • Ex worms , bot
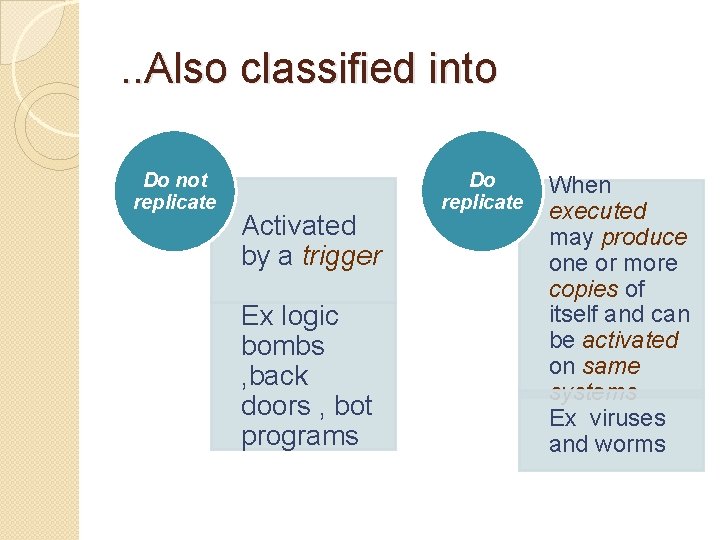
. . Also classified into Do not replicate Activated by a trigger Ex logic bombs , back doors , bot programs Do replicate When executed may produce one or more copies of itself and can be activated on same systems Ex viruses and worms
Backdoors �It is a secret entry point into a program that allows to gain access without going through usual security procedures. It is a threat when unscrupulous programmers use them for unauthorized access. �Programmers use backdoors legitimately to debug and test programs such a backdoor is called maintenance hook. This is usually done when programmers develop application that has an authorization procedure in it. �To secure the backdoor the security measures should focus on the program development and software update activities.
Logic Bombs �This is one of the oldest type of program threat. �Logic bomb is basically a program embedded into a software by an intruder , which lies dormant until a predefined condition is met after which the program then triggers an unauthorized act.
Trojan horse �It is a program or a command procedure containing a hidden code that when invoked performs some unwanted or harmful function. �Trojan horse can be used to change the file permission for the file to be shared within many users. �It can be also used for destroying the file when it seems to be doing a particular task.
Nimda Attack �Referred to as a simple worm , it uses four distribution methods which are as follows: �Email: a user on a host opens an infected email attachment , nimda looks for email addresses on the host and sends copies of itself to these addresses. �Windows shares : it scans hosts for unsecured file shares and infects the files on that host , so as when a user runs an infected file , which will
�Web Servers : Nimda scans web serves and if it finds a vulnerable server , it attempts to transfer a copy of itself and infect it. �Web Clients : if a vulnerable web client visits a web server that has been infected by Nimda the workstation of the web client will become infected.
Important Questions �What is malicious software ? What are the categories of malicious software? �Define : virus , worm , bot programs , mobile code , flooder , root kit , spyware , adware. �Write short notes on backdoors , logic bomb , trojan horse. �Explain in detail nimda attack.
The end Thank You Referred from operating systems internals and design principles by William Stallings(sixth edition) Page no. (647 -651) -By Rusha Lawande 411127
- Slides: 16