KRAck Key Reinstallation Attacks Breaking WPA 2 PRESENTED
KRAck Key Reinstallation Attacks: Breaking WPA 2 PRESENTED BY MATT SIRKIS UNIVERSITY OF TULSA (CS 6013)
About KRACK Exploit of WPA 2 4 -way handshake Discovered by Mathy Vanhoef and Frank Piessens of the University of Leuven Published findings October 2017 US-CERT: VU#228519 CVE-2017 -13077, CVE-2017 -13078, CVE-2017 -13079, CVE-2017 -13080, CVE-2017 -13081, CVE-2017 -13082, CVE-2017 -13084, CVE-2017 -13086, CVE-2017 -13087 and CVE-2017 -13088.
Wi-Fi Security Protocols Nearly all modern protected Wi. Fi networks use a variation of WPA (or should!!) WPA vs WPA 2 (all about ciphers) WPA (2004): Designed as a fast replacement to WEP TKIP / 256 bit keys WPA 2 (2006): AES-CCMP
Wi-Fi Security Protocols (contd. ) Personal vs Enterprise Personal uses pre-shared keys Enterprise Supplicant is not aware of a pre-shared key Shared via EAP tunnel - post do 1 x authentication End result is the same
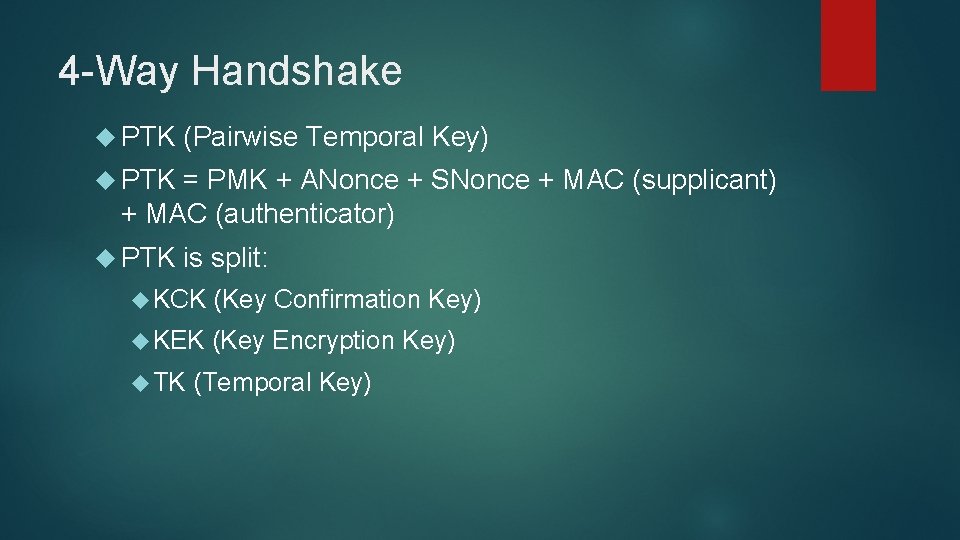
4 -Way Handshake PTK (Pairwise Temporal Key) PTK = PMK + ANonce + SNonce + MAC (supplicant) + MAC (authenticator) PTK is split: KCK (Key Confirmation Key) KEK (Key Encryption Key) TK (Temporal Key)
![WPA 4 -Way Handshake [2] WPA 4 -Way Handshake [2]](http://slidetodoc.com/presentation_image_h2/681627b972a8bf69cc1628943eef68ca/image-6.jpg)
WPA 4 -Way Handshake [2]
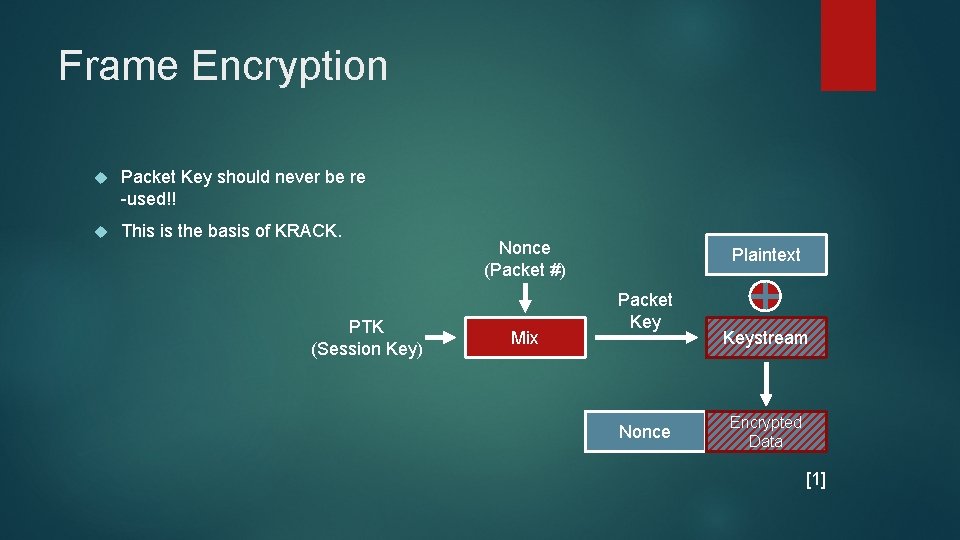
Frame Encryption Packet Key should never be re -used!! This is the basis of KRACK. PTK (Session Key) Nonce (Packet #) Mix Plaintext Packet Key Nonce Keystream Encrypted Data [1]
![PTK Reinstallation Attack [2] PTK Reinstallation Attack [2]](http://slidetodoc.com/presentation_image_h2/681627b972a8bf69cc1628943eef68ca/image-8.jpg)
PTK Reinstallation Attack [2]
![PTK Reinstallation Attack [2] Nonce Re-use!!! PTK Reinstallation Attack [2] Nonce Re-use!!!](http://slidetodoc.com/presentation_image_h2/681627b972a8bf69cc1628943eef68ca/image-9.jpg)
PTK Reinstallation Attack [2] Nonce Re-use!!!
![Nonce Reuse [5] Given packets P 1 and P 2 are encrypted with PTK: Nonce Reuse [5] Given packets P 1 and P 2 are encrypted with PTK:](http://slidetodoc.com/presentation_image_h2/681627b972a8bf69cc1628943eef68ca/image-10.jpg)
Nonce Reuse [5] Given packets P 1 and P 2 are encrypted with PTK: E 1 = P 1 ⊕ KS 1 E 2 = P 2 ⊕ KS 2 If P 1 and P 2 were to use the same nonce, then: KS 1 = KS 2 E 1 ⊕ E 2 = P 1 ⊕ P 2 Since P 1 was already sent unencrypted, we can derive P 2.
![Keystream PTK Reinstallation Attack [2] Keystream PTK Reinstallation Attack [2]](http://slidetodoc.com/presentation_image_h2/681627b972a8bf69cc1628943eef68ca/image-11.jpg)
Keystream PTK Reinstallation Attack [2]
![Keystream PTK Reinstallation Attack [2] Plaintext!! Keystream PTK Reinstallation Attack [2] Plaintext!!](http://slidetodoc.com/presentation_image_h2/681627b972a8bf69cc1628943eef68ca/image-12.jpg)
Keystream PTK Reinstallation Attack [2] Plaintext!!

Impact Nonce re-use = decrypt frames sent from client Replay frames towards victim Cipher suite specific AES-CCMP - can decrypt and replay / no forging attacks possible WPA-TKIP - can decrypt and replay / able to inject to the client GCMP (Wi. Gig) - able to inject in both directions (not widely used though)
![Key Takeaway Proven secure: WPA 4 -way handshake has proven to be secure [4] Key Takeaway Proven secure: WPA 4 -way handshake has proven to be secure [4]](http://slidetodoc.com/presentation_image_h2/681627b972a8bf69cc1628943eef68ca/image-14.jpg)
Key Takeaway Proven secure: WPA 4 -way handshake has proven to be secure [4] Encryption ciphers have been mathematically proven to be secure [4] Combination is not proven secure Exploited by the others weakness Enterprise PMK was just as vulnerable as Personal preshared keys. Creates a false sense of security.
Sources 1. KEY REINSTALLATION ATTACKS: BREAKING THE WPA 2 PROTOCOL – YOUTUBE, 27 DEC. 2017, HTTPS: //WWW. YOUTUBE. COM/WATCH? V=FZ 1 R 9 RLIM 1 W 2. MATHY VANHOEF AND FRANK PIESSENS. 2017. “KEY REINSTALLATION ATTACKS: FORCING NONCE REUSE IN WPA 2”. IN PROCEEDINGS OF THE 24 TH ACM CONFERENCE ON COMPUTER AND COMMUNICATIONS SERCURITY (CCS). ACM. HTTPS: //PAPERS. MATHYVANHOEF. COM/CCS 2017. PDF 3. ROUSE, MARGARET. "WI-FI PROTECTED ACCESS (WPA). " TECHTARGET. HTTPS: //SEARCHMOBILECOMPUTING. TECHTARGET. COM/DEFINITION/WI-FI-PROTECTED-ACCESS 4. CHANGHUA HE, MUKUND SUNDARARAJAN, ANUPAM DATTA, ANTE DEREK, AND JOHN C MITCHELL. 2005. “A MODULAR CORRECTNESS PROOF OF IEEE 802. 11 I AND TLS”. IN CCS. 5. CHASKA, HEMANT. OCT 16, 2017. “WPA 2 KEY REINSTALLATION VULNERABILITIES (KRACK) EXPLAINED”, HTTPS: //BLOG. MOJONETWORKS. COM/WPA 2 -VULNERABILITY
![GTK Reinstallation Attack [2] GTK Reinstallation Attack [2]](http://slidetodoc.com/presentation_image_h2/681627b972a8bf69cc1628943eef68ca/image-16.jpg)
GTK Reinstallation Attack [2]
- Slides: 16