Introduction to Optimization II Value Numbering Larger Scopes
Introduction to Optimization, II Value Numbering & Larger Scopes Copyright 2003, Keith D. Cooper, Kennedy & Linda Torczon, all rights reserved. Students enrolled in Comp 412 at Rice University have explicit permission to make copies of these materials for their personal use.
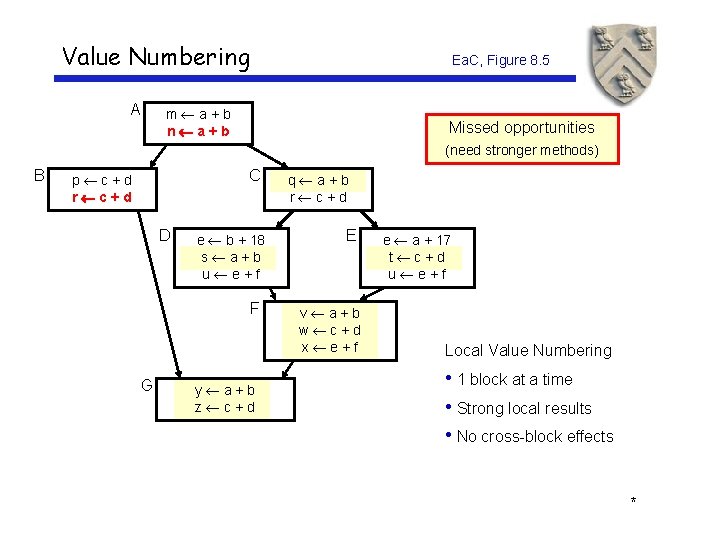
Value Numbering A Ea. C, Figure 8. 5 m a+b n a+b Missed opportunities (need stronger methods) B C p c+d r c+d D e b + 18 s a+b u e+f F G y a+b z c+d q a+b r c+d E v a+b w c+d x e+f e a + 17 t c+d u e+f Local Value Numbering • 1 block at a time • Strong local results • No cross-block effects *
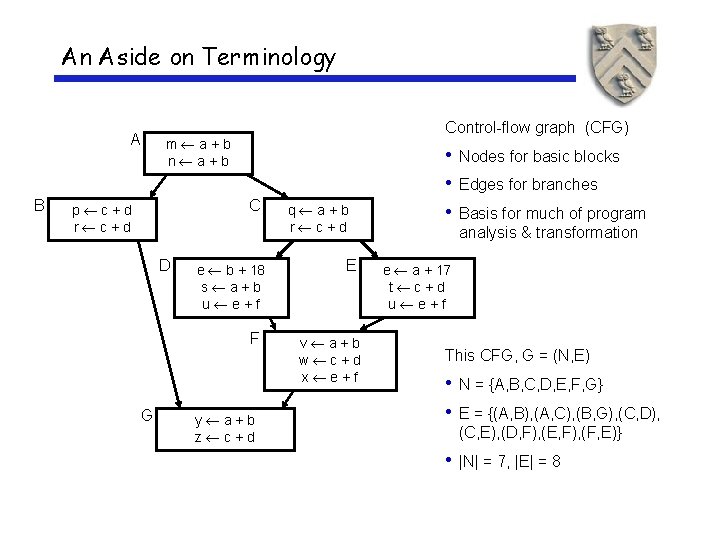
An Aside on Terminology A B Control-flow graph (CFG) m a+b n a+b C p c+d r c+d D e b + 18 s a+b u e+f F G y a+b z c+d q a+b r c+d E v a+b w c+d x e+f • Nodes for basic blocks • Edges for branches • Basis for much of program analysis & transformation e a + 17 t c+d u e+f This CFG, G = (N, E) • N = {A, B, C, D, E, F, G} • E = {(A, B), (A, C), (B, G), (C, D), (C, E), (D, F), (E, F), (F, E)} • |N| = 7, |E| = 8
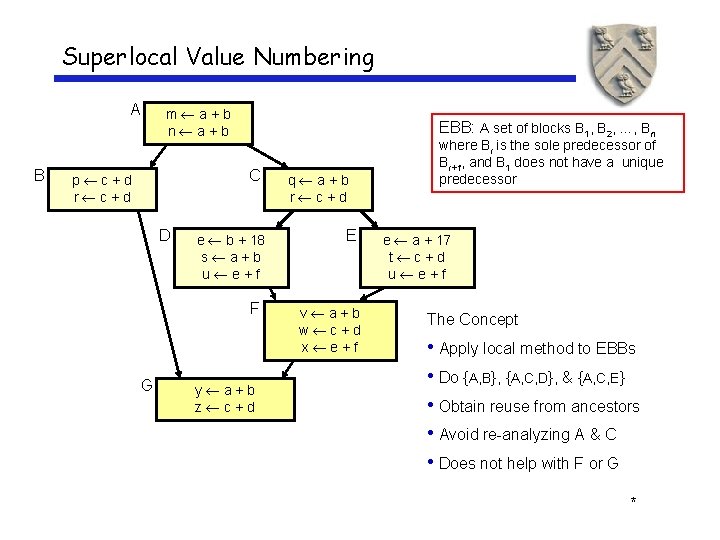
Superlocal Value Numbering A B m a+b n a+b EBB: A set of blocks B 1, B 2, …, Bn C p c+d r c+d D e b + 18 s a+b u e+f F G y a+b z c+d q a+b r c+d E v a+b w c+d x e+f where Bi is the sole predecessor of Bi+1, and B 1 does not have a unique predecessor e a + 17 t c+d u e+f The Concept • Apply local method to EBBs • Do {A, B}, {A, C, D}, & {A, C, E} • Obtain reuse from ancestors • Avoid re-analyzing A & C • Does not help with F or G *
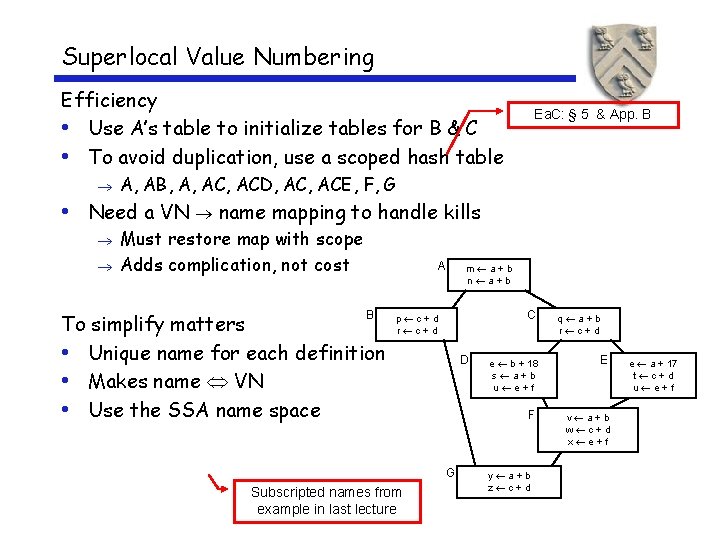
Superlocal Value Numbering Efficiency • Use A’s table to initialize tables for B & C • To avoid duplication, use a scoped hash table Ea. C: § 5 & App. B A, AB, A, ACD, ACE, F, G • Need a VN name mapping to handle kills Must restore map with scope Adds complication, not cost A B To simplify matters • Unique name for each definition • Makes name VN • Use the SSA name space m a+b n a+b C p c+d r c+d D G Subscripted names from example in last lecture q a+b r c+d e b + 18 s a+b u e+f E F v a+b w c+d x e+f y a+b z c+d e a + 17 t c+d u e+f
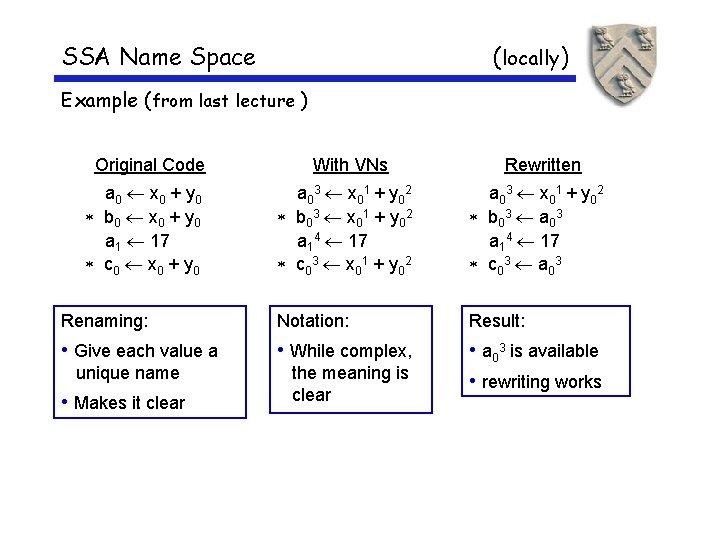
SSA Name Space (locally) Example (from last lecture ) Original Code a 0 x 0 + y 0 b 0 x 0 + y 0 a 1 17 c 0 x 0 + y 0 With VNs Rewritten a 0 3 x 0 1 + y 0 2 b 0 3 x 0 1 + y 0 2 a 14 17 c 0 3 x 0 1 + y 0 2 a 0 3 x 0 1 + y 0 2 b 0 3 a 0 3 a 14 17 c 0 3 a 0 3 Renaming: Notation: Result: • Give each value a • While complex, • a 03 is available • rewriting works unique name • Makes it clear the meaning is clear
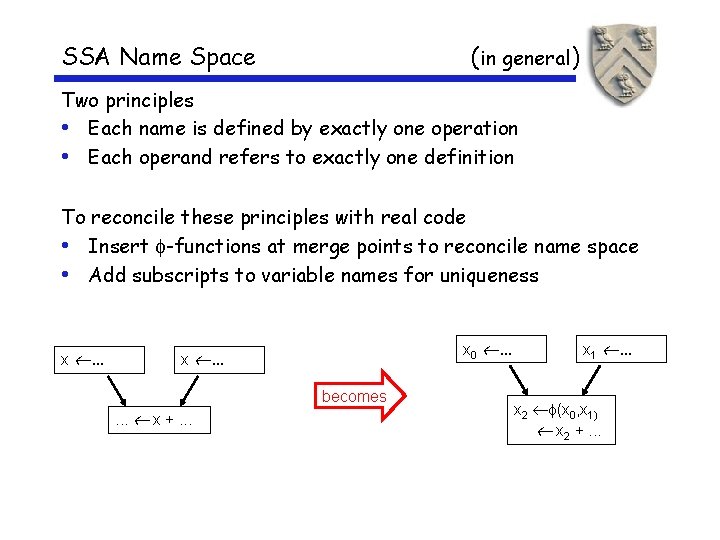
SSA Name Space (in general) Two principles • Each name is defined by exactly one operation • Each operand refers to exactly one definition To reconcile these principles with real code • Insert -functions at merge points to reconcile name space • Add subscripts to variable names for uniqueness x . . . x 0 . . . x . . . becomes. . . x +. . . x 1 . . . x 2 (x 0, x 1) x 2 +. . .
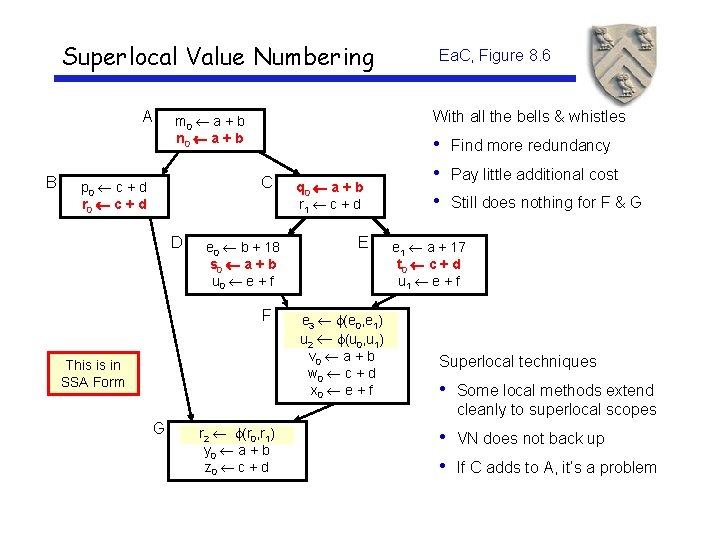
Superlocal Value Numbering A B With all the bells & whistles m 0 a + b n 0 a + b C p 0 c + d r 0 c + d D Ea. C, Figure 8. 6 e 0 b + 18 s 0 a + b u 0 e + f F This is in SSA Form q 0 a + b r 1 c + d E e 3 (e 0, e 1) u 2 (u 0, u 1) v 0 a + b w 0 c + d x 0 e + f • Find more redundancy • Pay little additional cost • Still does nothing for F & G e 1 a + 17 t 0 c + d u 1 e + f Superlocal techniques • Some local methods extend cleanly to superlocal scopes G r 2 (r 0, r 1) y 0 a + b z 0 c + d • VN does not back up • If C adds to A, it’s a problem
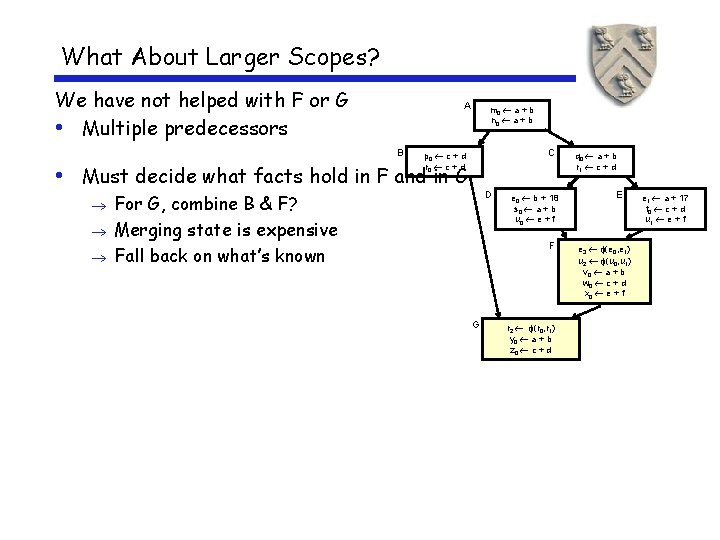
What About Larger Scopes? We have not helped with F or G • Multiple predecessors A B m 0 a + b n 0 a + b C p 0 c + d r 0 c + d • Must decide what facts hold in F and in G D For G, combine B & F? Merging state is expensive Fall back on what’s known e 0 b + 18 s 0 a + b u 0 e + f F G r 2 (r 0, r 1) y 0 a + b z 0 c + d q 0 a + b r 1 c + d E e 3 (e 0, e 1) u 2 (u 0, u 1) v 0 a + b w 0 c + d x 0 e + f e 1 a + 17 t 0 c + d u 1 e + f
Dominators Definitions x dominates y if and only if every path from the entry of the control-flow graph to the node for y includes x • By definition, x dominates x • We associate a Dom set with each node • |Dom(x )| ≥ 1 Immediate dominators • For any node x, there must be a y in Dom(x ) closest to x • We call this y the immediate dominator of x • As a matter of notation, we write this as IDom(x )

Dominators have many uses in analysis & transformation • Finding loops • Building SSA form • Making code motion decisions A B m 0 a + b n 0 a + b C p 0 c + d r 0 c + d D Dominator sets Dominator tree A e 0 b + 18 s 0 a + b u 0 e + f F B C G D E F G q 0 a + b r 1 c + d E e 1 a + 17 t 0 c + d u 1 e + f e 3 (e 0, e 1) u 2 (u 0, u 1) v 0 a + b w 0 c + d x 0 e + f r 2 (r 0, r 1) y 0 a + b z 0 c + d Back to the discussion of We’ll look at how to compute dominators latervalue numbering over larger scopes. . . *
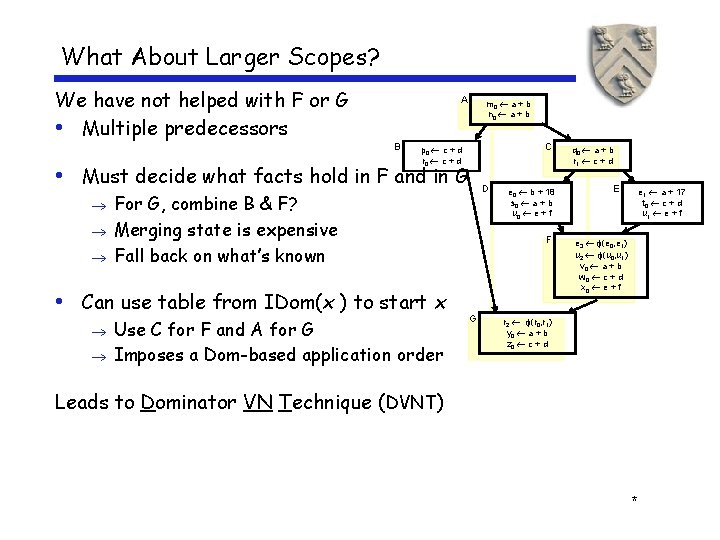
What About Larger Scopes? We have not helped with F or G • Multiple predecessors A B m 0 a + b n 0 a + b C p 0 c + d r 0 c + d • Must decide what facts hold in F and in G D For G, combine B & F? Merging state is expensive Fall back on what’s known • Can use table from IDom(x ) to start x Use C for F and A for G Imposes a Dom-based application order e 0 b + 18 s 0 a + b u 0 e + f F G q 0 a + b r 1 c + d E e 1 a + 17 t 0 c + d u 1 e + f e 3 (e 0, e 1) u 2 (u 0, u 1) v 0 a + b w 0 c + d x 0 e + f r 2 (r 0, r 1) y 0 a + b z 0 c + d Leads to Dominator VN Technique (DVNT) *
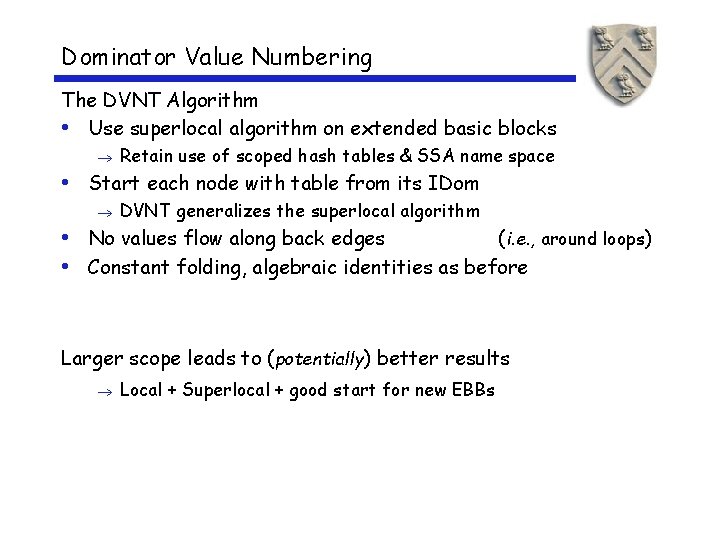
Dominator Value Numbering The DVNT Algorithm • Use superlocal algorithm on extended basic blocks Retain use of scoped hash tables & SSA name space • Start each node with table from its IDom DVNT generalizes the superlocal algorithm • No values flow along back edges ( i. e. , around loops) • Constant folding, algebraic identities as before Larger scope leads to (potentially) better results Local + Superlocal + good start for new EBBs
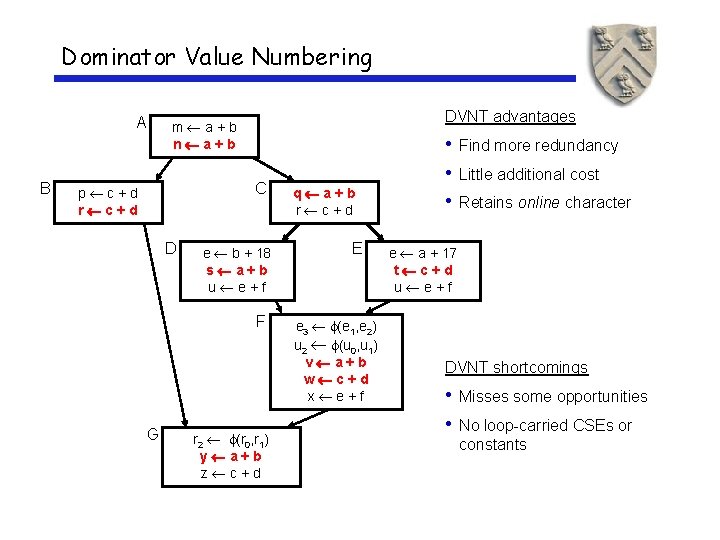
Dominator Value Numbering A B DVNT advantages m a+b n a+b C p c+d r c+d D e b + 18 s a+b u e+f F G r 2 (r 0, r 1) y a+b z c+d q a+b r c+d E e 3 (e 1, e 2) u 2 (u 0, u 1) v a+b w c+d x e+f • Find more redundancy • Little additional cost • Retains online character e a + 17 t c+d u e+f DVNT shortcomings • Misses some opportunities • No loop-carried CSEs or constants
The Story So Far, … • Local algorithm • Superlocal extension of Balke • Dominator VN technique (Balke, 1967) (many) (Simpson, 1996) All these propagate along forward edges Þ None are global methods Þ Global Methods Next lecture • Classic CSE (Cocke 1970) • Partitioning algorithms (Alpern et al. 1988, Click 1995) • Partial Redundancy Elimination (Morel & Renvoise 1979) • SCC/VDCM (Simpson 1996) We will look at several global methods *
Roadmap To recap … • We have seen value numbering Local, superlocal, dominator scopes We may look at global value numbering later We will look at global redundancy elimination today • We have used dominators Chapter 9 in Ea. C shows how to compute dominators Gives world’s fastest algorithm (also simplest) • We have used SSA Chapter 9 in Ea. C shows how to build SSA form & tear it down
- Slides: 16