Introduction to Encryption Technology Mort Anvari Encryption What
- Slides: 18
Introduction to Encryption Technology Mort Anvari
Encryption What is it? - The conversion of data into a form that cannot be easily understood by unauthorized people - The opposite is decryption, that is, changing the difficult to read form back into the original - It’s usually software, but can be hardware 2
Cryptography - What does it do for me? - Symmetric Encryption - Asymmetric Encryption - One Way Hash - Example: An Encrypted E-Mail 3
What does it do for me? Confidentiality: The data can only be read by the intended recipients Non-Repudiation: The data cannot be forged. If data is “signed” by a person, the data could only have come from them. No more “I didn’t send that!” Data Integrity: The data cannot be modified without detection 4
Symmetric Encryption - Data is encrypted and decrypted with the same key - Fast - Key must be kept secret - Key must be sent Out of Band - DES and IDEA are symmetric 5
Asymmetric Encryption - Uses 2 keys - Data encrypted with one key can only be decrypted with the other - Public key is shared with all - Public key can be sent In Band - Private key must be kept secret - RSA is asymmetric 6
One Way Hash - A “fingerprint” of data - Any size data = same size hash - Tiny changes in data produce a very different hash 7
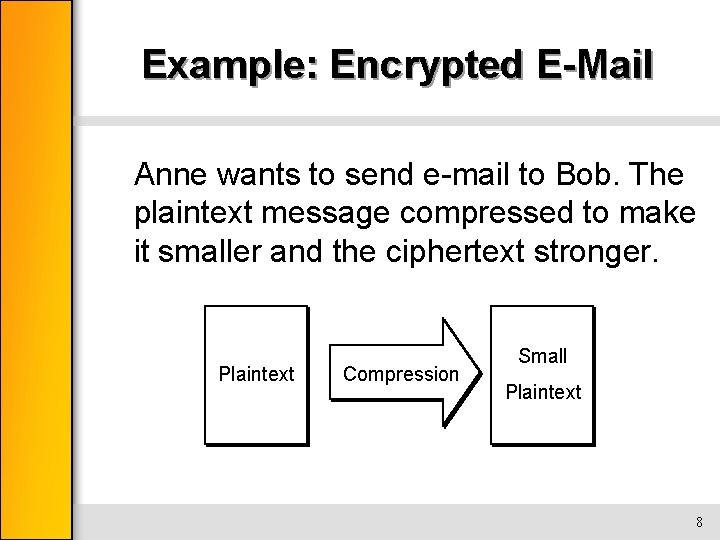
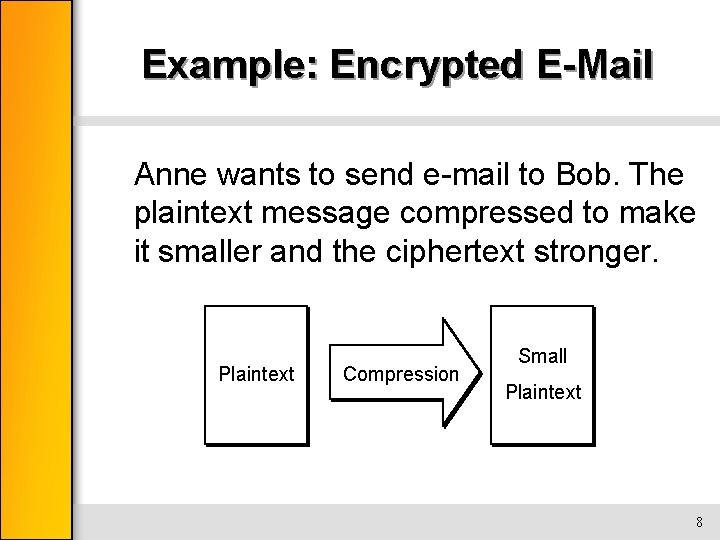
Example: Encrypted E-Mail Anne wants to send e-mail to Bob. The plaintext message compressed to make it smaller and the ciphertext stronger. Plaintext Compression Small Plaintext 8
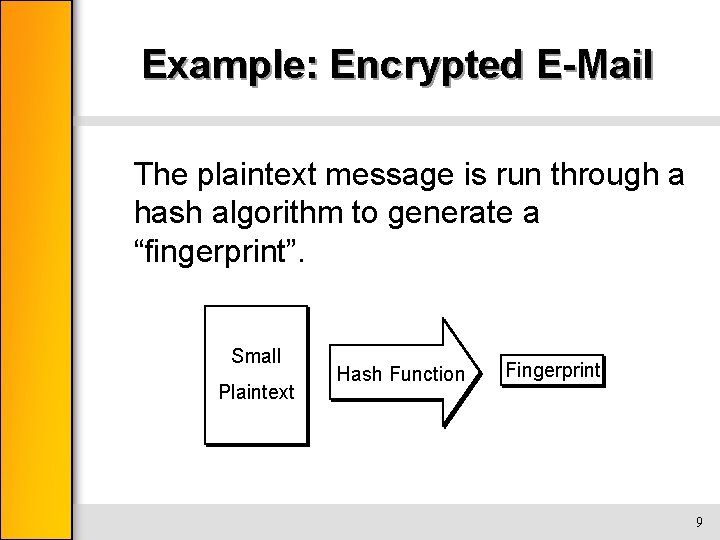
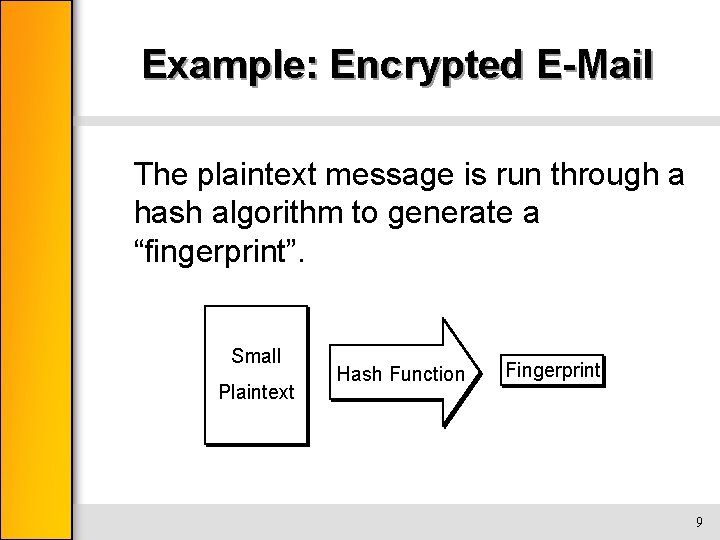
Example: Encrypted E-Mail The plaintext message is run through a hash algorithm to generate a “fingerprint”. Small Plaintext Hash Function Fingerprint 9
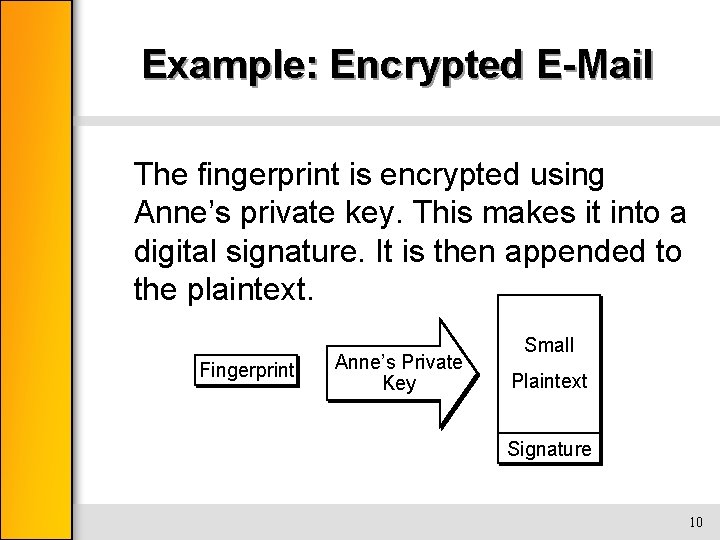
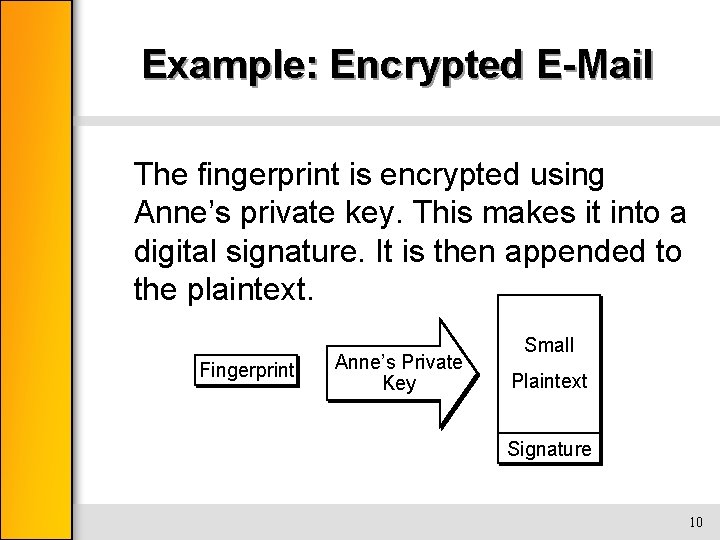
Example: Encrypted E-Mail The fingerprint is encrypted using Anne’s private key. This makes it into a digital signature. It is then appended to the plaintext. Fingerprint Anne’s Private Key Small Plaintext Signature 10
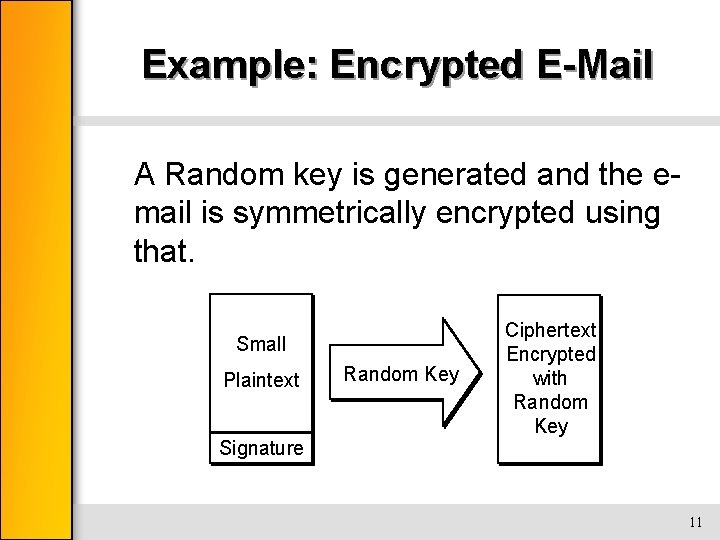
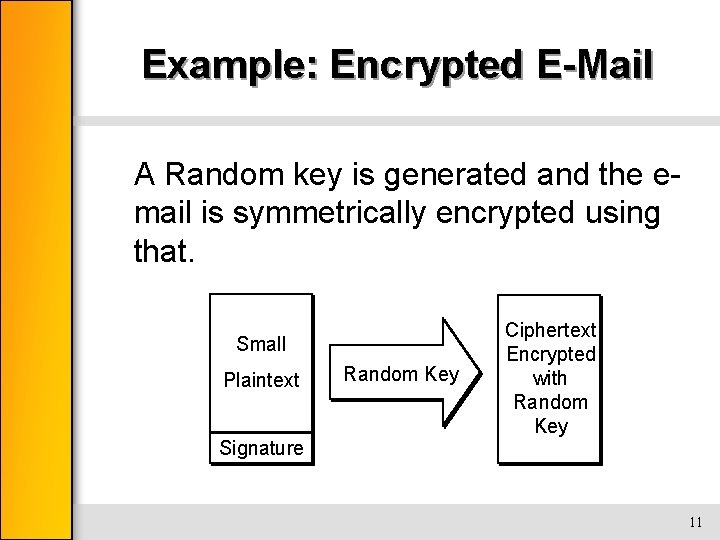
Example: Encrypted E-Mail A Random key is generated and the email is symmetrically encrypted using that. Small Plaintext Signature Random Key Ciphertext Encrypted with Random Key 11
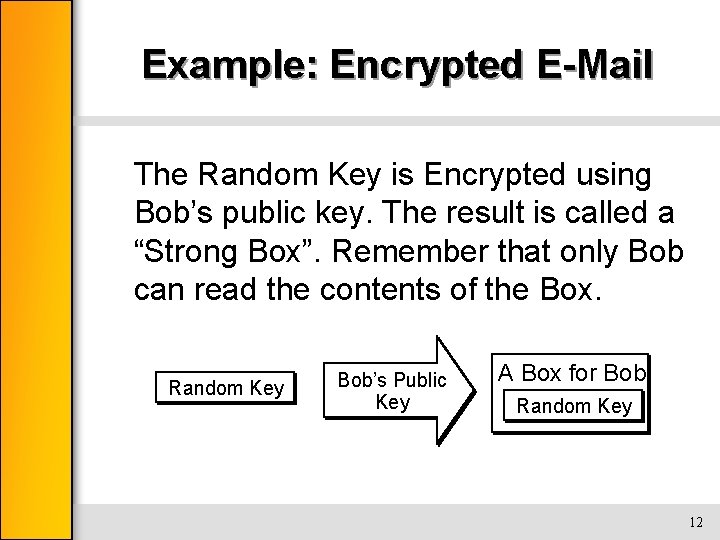
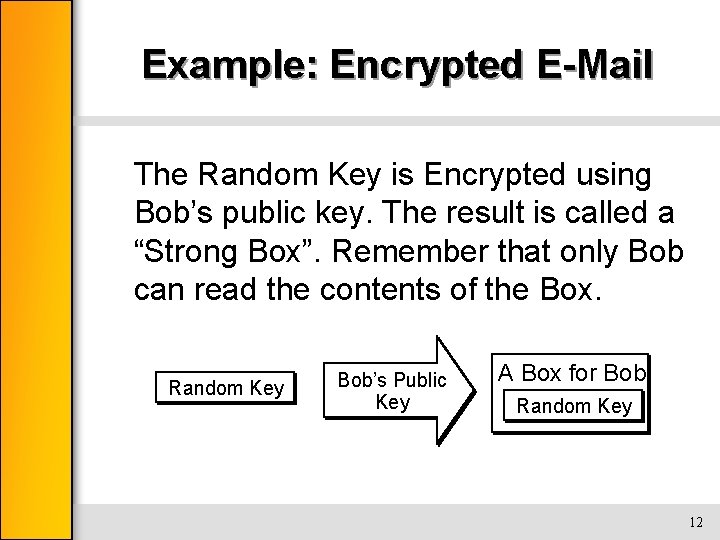
Example: Encrypted E-Mail The Random Key is Encrypted using Bob’s public key. The result is called a “Strong Box”. Remember that only Bob can read the contents of the Box. Random Key Bob’s Public Key A Box for Bob Random Key 12
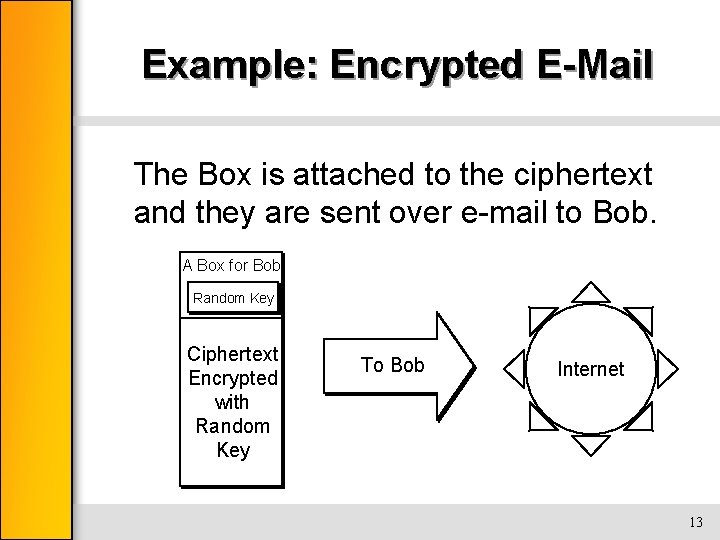
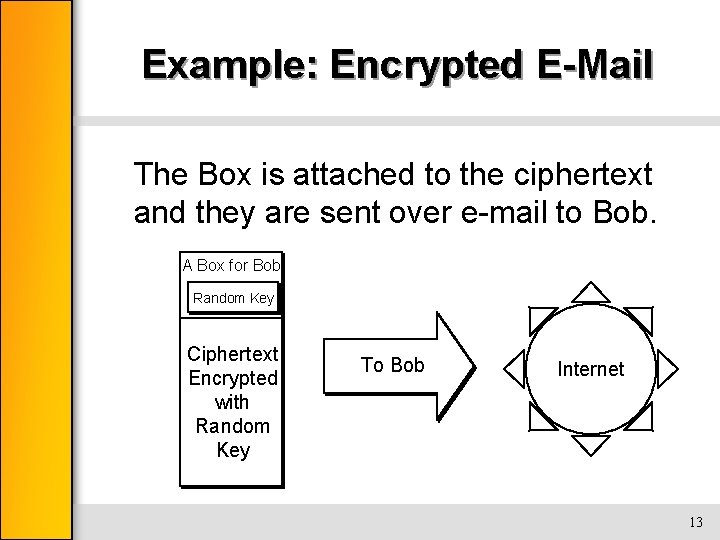
Example: Encrypted E-Mail The Box is attached to the ciphertext and they are sent over e-mail to Bob. A Box for Bob Random Key Ciphertext Encrypted with Random Key To Bob Internet 13
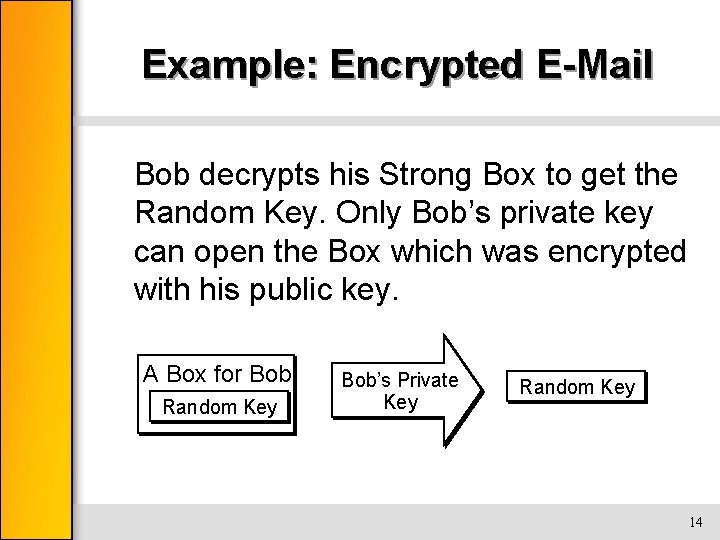
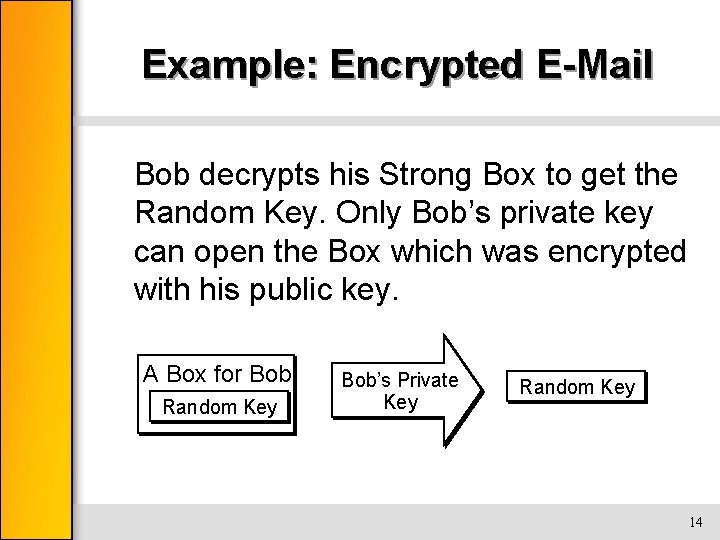
Example: Encrypted E-Mail Bob decrypts his Strong Box to get the Random Key. Only Bob’s private key can open the Box which was encrypted with his public key. A Box for Bob Random Key Bob’s Private Key Random Key 14
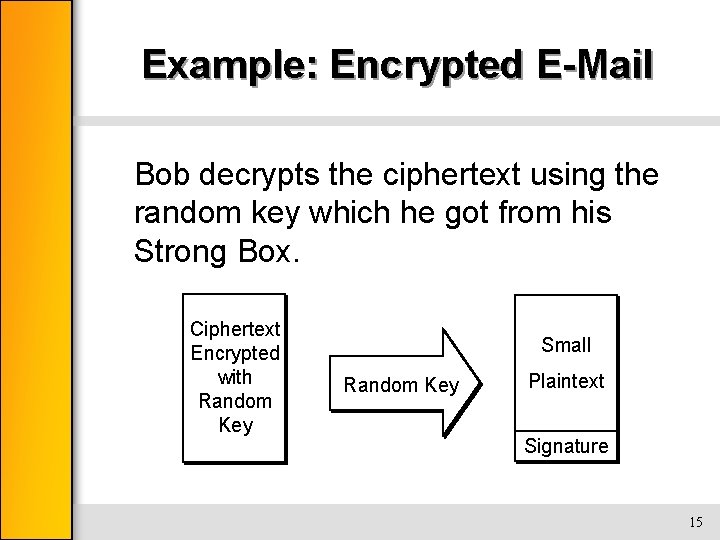
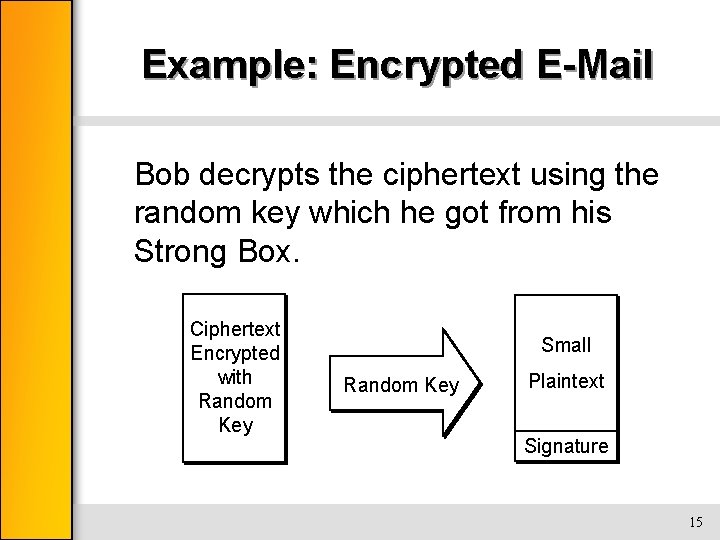
Example: Encrypted E-Mail Bob decrypts the ciphertext using the random key which he got from his Strong Box. Ciphertext Encrypted with Random Key Small Random Key Plaintext Signature 15
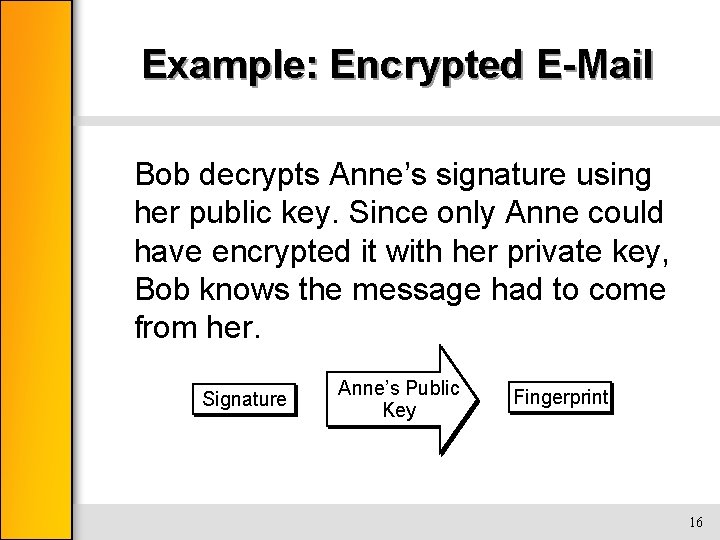
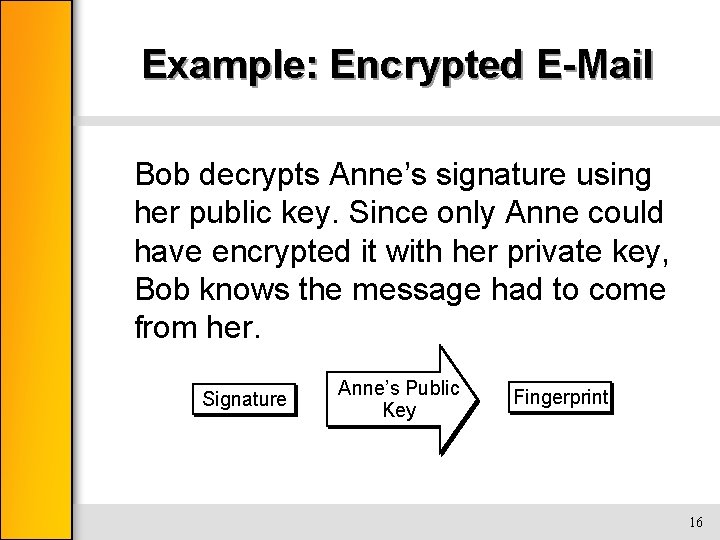
Example: Encrypted E-Mail Bob decrypts Anne’s signature using her public key. Since only Anne could have encrypted it with her private key, Bob knows the message had to come from her. Signature Anne’s Public Key Fingerprint 16
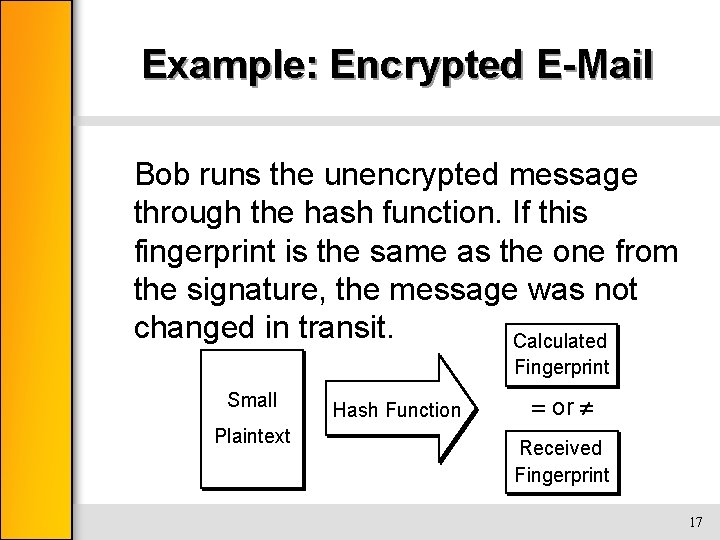
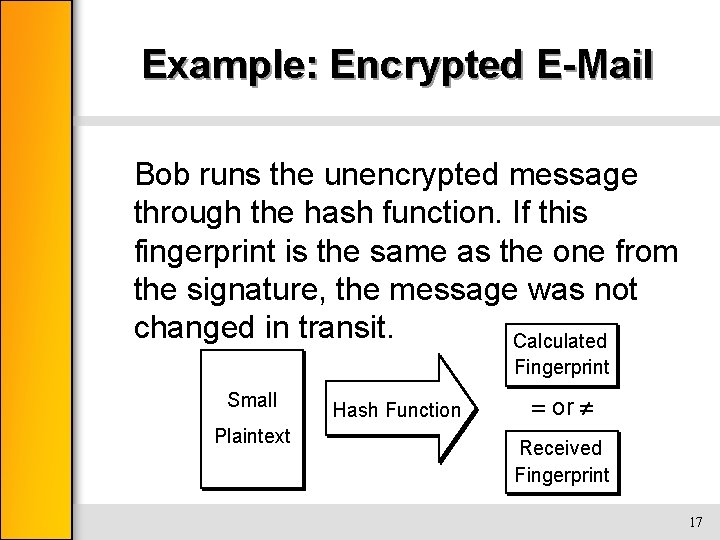
Example: Encrypted E-Mail Bob runs the unencrypted message through the hash function. If this fingerprint is the same as the one from the signature, the message was not changed in transit. Calculated Fingerprint Small Plaintext Hash Function or Received Fingerprint 17
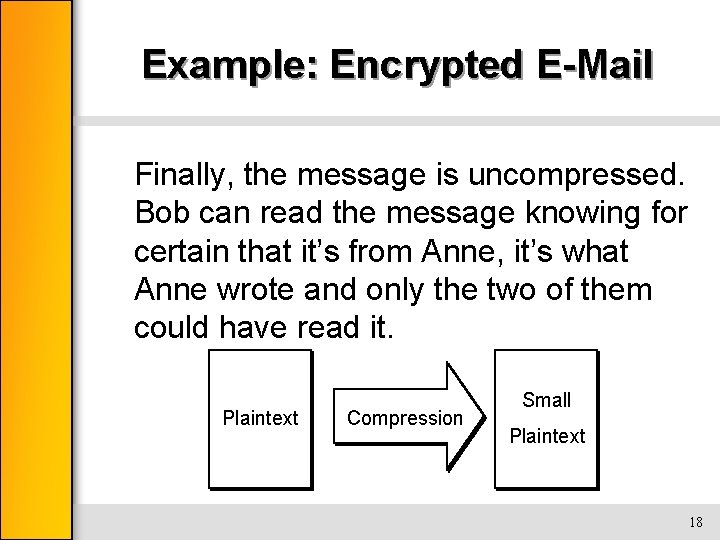
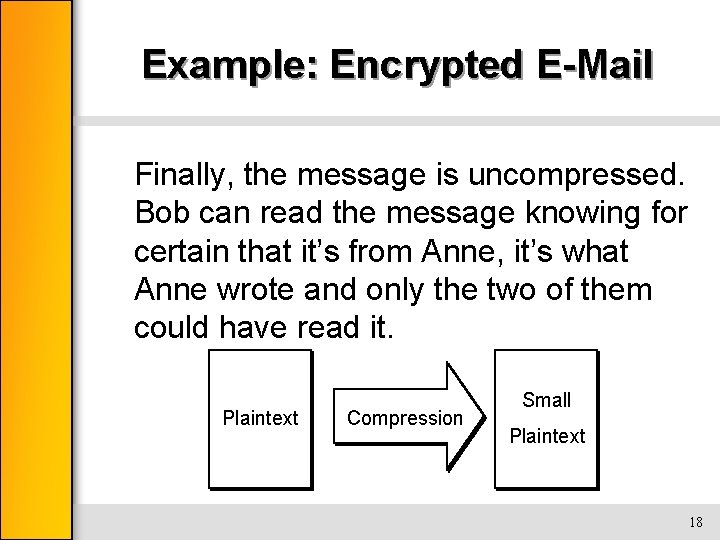
Example: Encrypted E-Mail Finally, the message is uncompressed. Bob can read the message knowing for certain that it’s from Anne, it’s what Anne wrote and only the two of them could have read it. Plaintext Compression Small Plaintext 18