Internet Intranet CIS536 Class 5 Web Server Security
Internet / Intranet CIS-536 Class 5 Web Server Security Intro Javascript Brandeis University Internet/Intranet Spring 2000
Class 5 Agenda Web Security Presentations Intro Java. Script Next Week: More Javascript DHTML, DOM Forms 2
Practical Internet Security Analogous to “Real-Life” Security (e. g. a Bank) Like Software, Security Must Be Well-Designed Implementing Security Requires Trade-Offs Ease of Use is Affected Business Processes are Affected Business Culture is Affected Affects Both Users and Employees Security is Expensive Time, Effort, Lost Productivity Enforcement Physical Security is Only Half the Story Implementation/Enforcement is Just as Important 3
Security Design Issues Know the Threats You are Protecting Against What are the Probabilities? What is the Cost if it Happens? Dollars Customer/Employee Confidence Know Your Environment What are the Customer/User Requirements? What are the Budget Constraints? What is the Culture/Attitude of Those Affected? What is the Probability That Policies Will Be Followed Enforced? 4

Security Sermon Security is Often Mis-Used in Technology Environments Provides Peace of Mind Not Necessarily Real Security Often Avoids the Real Issues Appeases Management Common Security Mistakes (Analogies) Using an Expensive/High Security Safe But Leaving the Key/Combination Where it Can Be Stolen Leaving the Safe Unlocked Little Professional Enforcement/Review of Procedures Storing a Dime in a Safe Cost of Security Exceeds Risk of Stolen Dime High-Tech Solution Instead of Low-Tech Common Sense E. g. Convenience Store Having a Safe vs. Nightly Bank Deposits Security Has Consequences on Human Perceptions E. g. Installing a Metal Detector May Make Employees Feel Less Secure 5
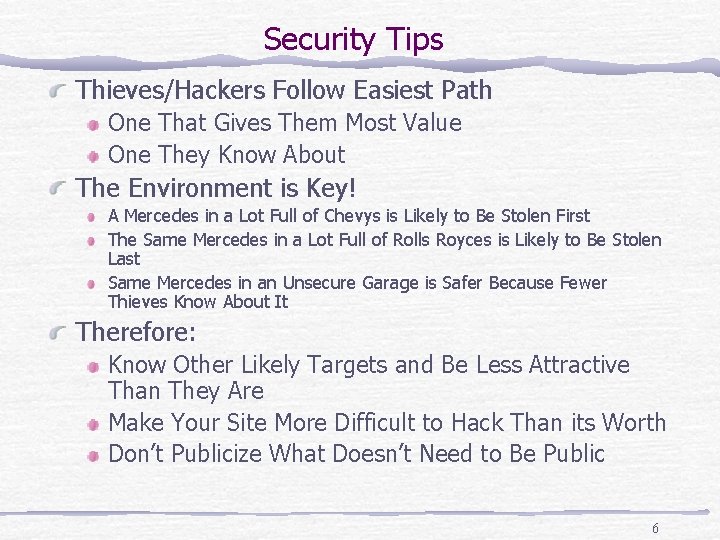
Security Tips Thieves/Hackers Follow Easiest Path One That Gives Them Most Value One They Know About The Environment is Key! A Mercedes in a Lot Full of Chevys is Likely to Be Stolen First The Same Mercedes in a Lot Full of Rolls Royces is Likely to Be Stolen Last Same Mercedes in an Unsecure Garage is Safer Because Fewer Thieves Know About It Therefore: Know Other Likely Targets and Be Less Attractive Than They Are Make Your Site More Difficult to Hack Than its Worth Don’t Publicize What Doesn’t Need to Be Public 6
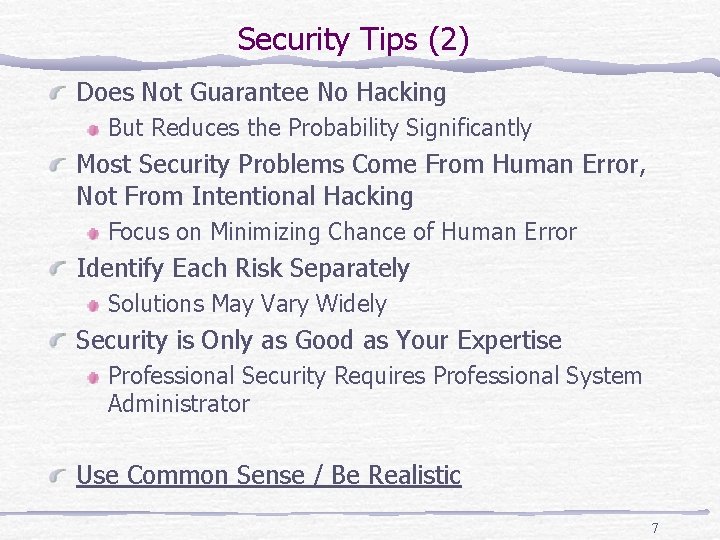
Security Tips (2) Does Not Guarantee No Hacking But Reduces the Probability Significantly Most Security Problems Come From Human Error, Not From Intentional Hacking Focus on Minimizing Chance of Human Error Identify Each Risk Separately Solutions May Vary Widely Security is Only as Good as Your Expertise Professional Security Requires Professional System Administrator Use Common Sense / Be Realistic 7
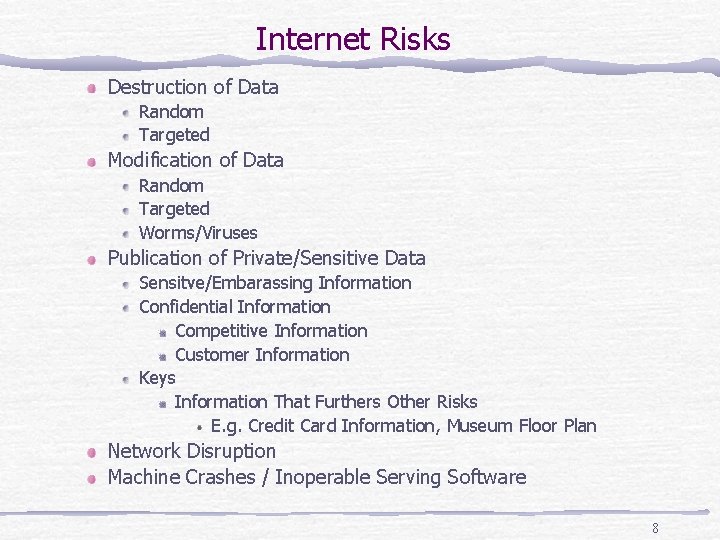
Internet Risks Destruction of Data Random Targeted Modification of Data Random Targeted Worms/Viruses Publication of Private/Sensitive Data Sensitve/Embarassing Information Confidential Information Competitive Information Customer Information Keys Information That Furthers Other Risks E. g. Credit Card Information, Museum Floor Plan Network Disruption Machine Crashes / Inoperable Serving Software 8
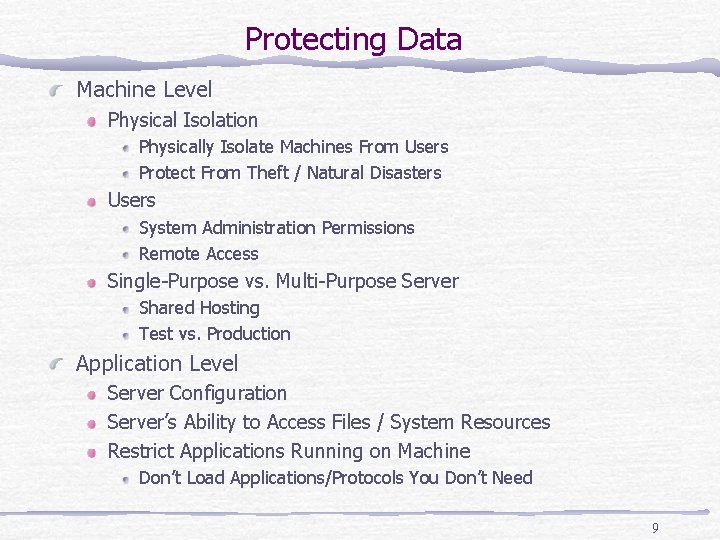
Protecting Data Machine Level Physical Isolation Physically Isolate Machines From Users Protect From Theft / Natural Disasters Users System Administration Permissions Remote Access Single-Purpose vs. Multi-Purpose Server Shared Hosting Test vs. Production Application Level Server Configuration Server’s Ability to Access Files / System Resources Restrict Applications Running on Machine Don’t Load Applications/Protocols You Don’t Need 9
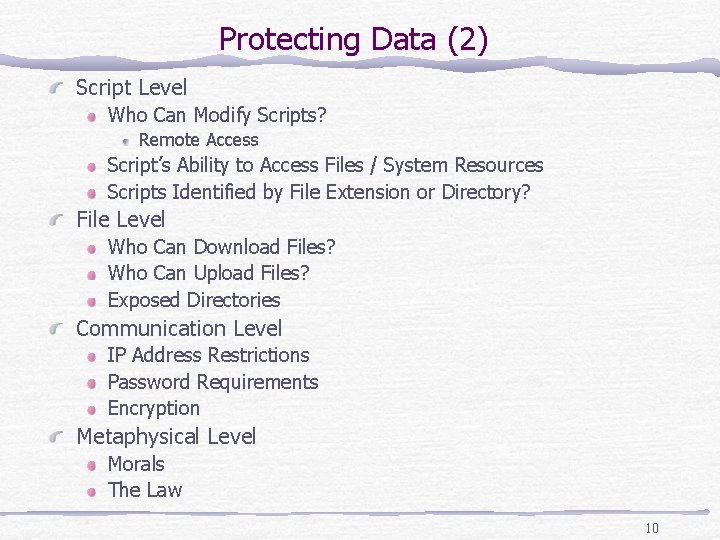
Protecting Data (2) Script Level Who Can Modify Scripts? Remote Access Script’s Ability to Access Files / System Resources Scripts Identified by File Extension or Directory? File Level Who Can Download Files? Who Can Upload Files? Exposed Directories Communication Level IP Address Restrictions Password Requirements Encryption Metaphysical Level Morals The Law 10
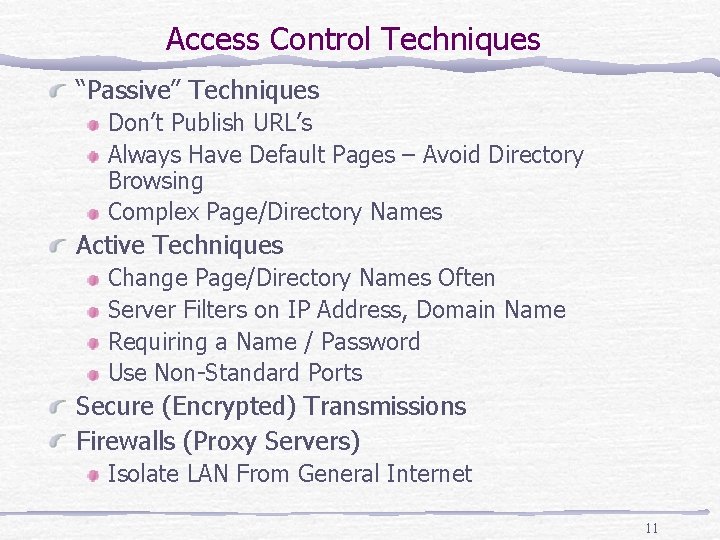
Access Control Techniques “Passive” Techniques Don’t Publish URL’s Always Have Default Pages – Avoid Directory Browsing Complex Page/Directory Names Active Techniques Change Page/Directory Names Often Server Filters on IP Address, Domain Name Requiring a Name / Password Use Non-Standard Ports Secure (Encrypted) Transmissions Firewalls (Proxy Servers) Isolate LAN From General Internet 11
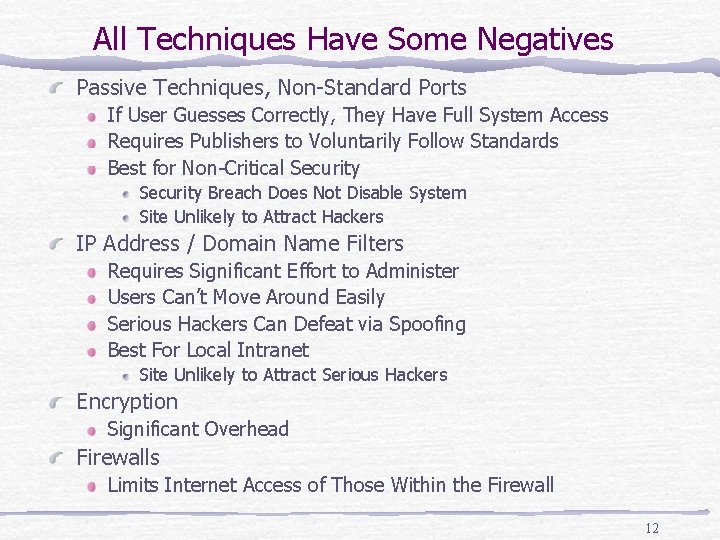
All Techniques Have Some Negatives Passive Techniques, Non-Standard Ports If User Guesses Correctly, They Have Full System Access Requires Publishers to Voluntarily Follow Standards Best for Non-Critical Security Breach Does Not Disable System Site Unlikely to Attract Hackers IP Address / Domain Name Filters Requires Significant Effort to Administer Users Can’t Move Around Easily Serious Hackers Can Defeat via Spoofing Best For Local Intranet Site Unlikely to Attract Serious Hackers Encryption Significant Overhead Firewalls Limits Internet Access of Those Within the Firewall 12
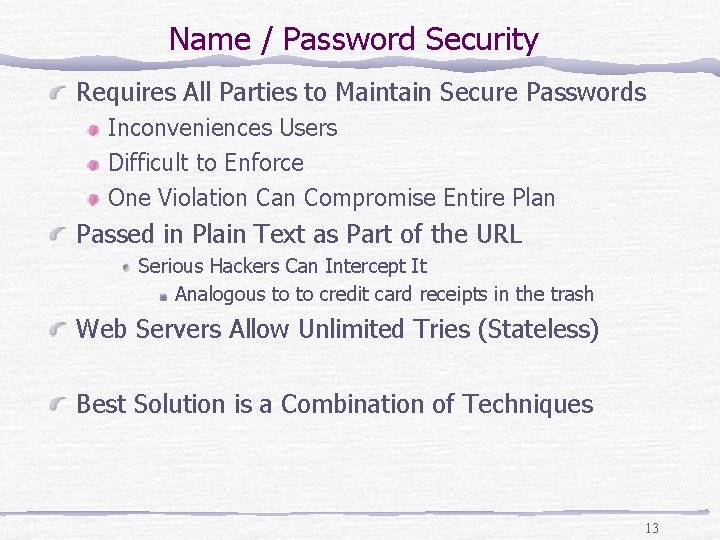
Name / Password Security Requires All Parties to Maintain Secure Passwords Inconveniences Users Difficult to Enforce One Violation Can Compromise Entire Plan Passed in Plain Text as Part of the URL Serious Hackers Can Intercept It Analogous to to credit card receipts in the trash Web Servers Allow Unlimited Tries (Stateless) Best Solution is a Combination of Techniques 13
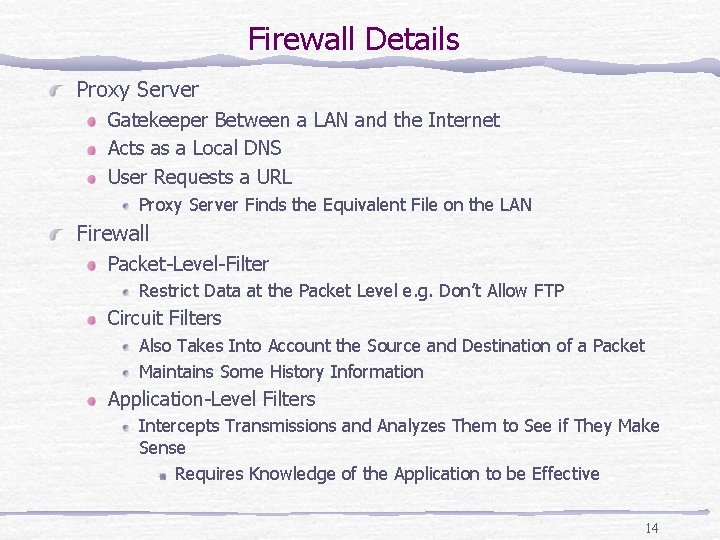
Firewall Details Proxy Server Gatekeeper Between a LAN and the Internet Acts as a Local DNS User Requests a URL Proxy Server Finds the Equivalent File on the LAN Firewall Packet-Level-Filter Restrict Data at the Packet Level e. g. Don’t Allow FTP Circuit Filters Also Takes Into Account the Source and Destination of a Packet Maintains Some History Information Application-Level Filters Intercepts Transmissions and Analyzes Them to See if They Make Sense Requires Knowledge of the Application to be Effective 14
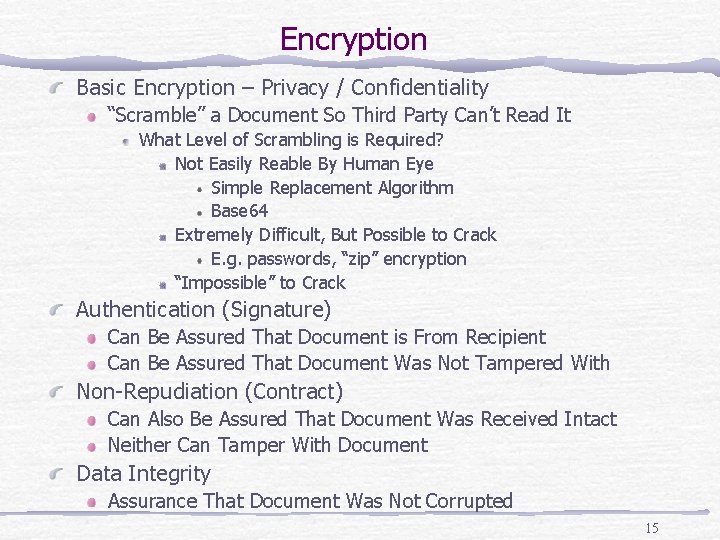
Encryption Basic Encryption – Privacy / Confidentiality “Scramble” a Document So Third Party Can’t Read It What Level of Scrambling is Required? Not Easily Reable By Human Eye Simple Replacement Algorithm Base 64 Extremely Difficult, But Possible to Crack E. g. passwords, “zip” encryption “Impossible” to Crack Authentication (Signature) Can Be Assured That Document is From Recipient Can Be Assured That Document Was Not Tampered With Non-Repudiation (Contract) Can Also Be Assured That Document Was Received Intact Neither Can Tamper With Document Data Integrity Assurance That Document Was Not Corrupted 15
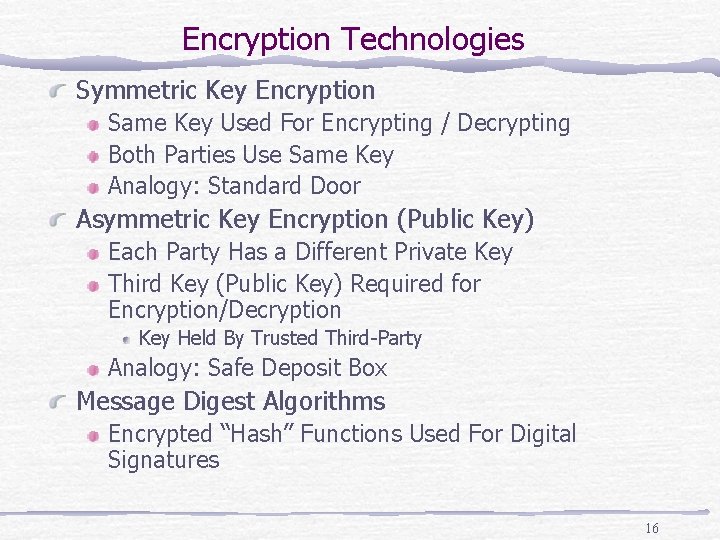
Encryption Technologies Symmetric Key Encryption Same Key Used For Encrypting / Decrypting Both Parties Use Same Key Analogy: Standard Door Asymmetric Key Encryption (Public Key) Each Party Has a Different Private Key Third Key (Public Key) Required for Encryption/Decryption Key Held By Trusted Third-Party Analogy: Safe Deposit Box Message Digest Algorithms Encrypted “Hash” Functions Used For Digital Signatures 16
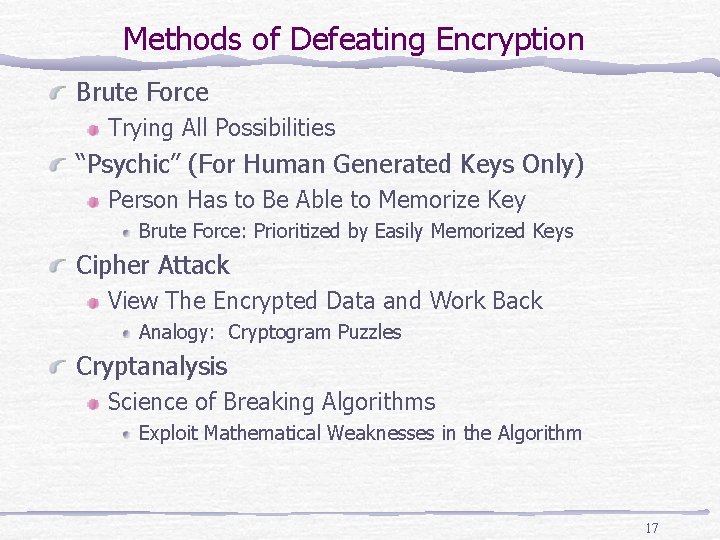
Methods of Defeating Encryption Brute Force Trying All Possibilities “Psychic” (For Human Generated Keys Only) Person Has to Be Able to Memorize Key Brute Force: Prioritized by Easily Memorized Keys Cipher Attack View The Encrypted Data and Work Back Analogy: Cryptogram Puzzles Cryptanalysis Science of Breaking Algorithms Exploit Mathematical Weaknesses in the Algorithm 17
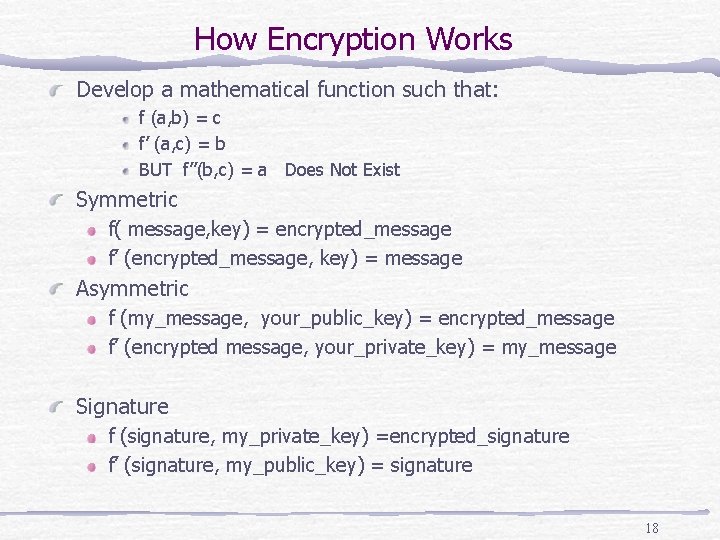
How Encryption Works Develop a mathematical function such that: f (a, b) = c f’ (a, c) = b BUT f’’(b, c) = a Does Not Exist Symmetric f( message, key) = encrypted_message f’ (encrypted_message, key) = message Asymmetric f (my_message, your_public_key) = encrypted_message f’ (encrypted message, your_private_key) = my_message Signature f (signature, my_private_key) =encrypted_signature f’ (signature, my_public_key) = signature 18
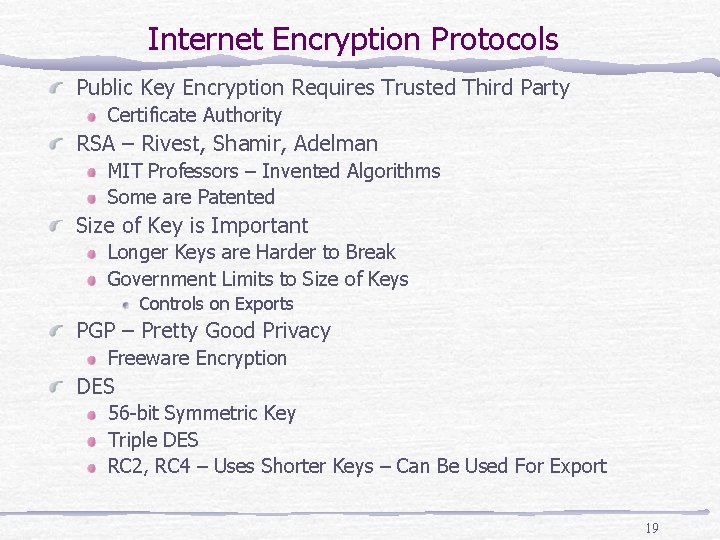
Internet Encryption Protocols Public Key Encryption Requires Trusted Third Party Certificate Authority RSA – Rivest, Shamir, Adelman MIT Professors – Invented Algorithms Some are Patented Size of Key is Important Longer Keys are Harder to Break Government Limits to Size of Keys Controls on Exports PGP – Pretty Good Privacy Freeware Encryption DES 56 -bit Symmetric Key Triple DES RC 2, RC 4 – Uses Shorter Keys – Can Be Used For Export 19
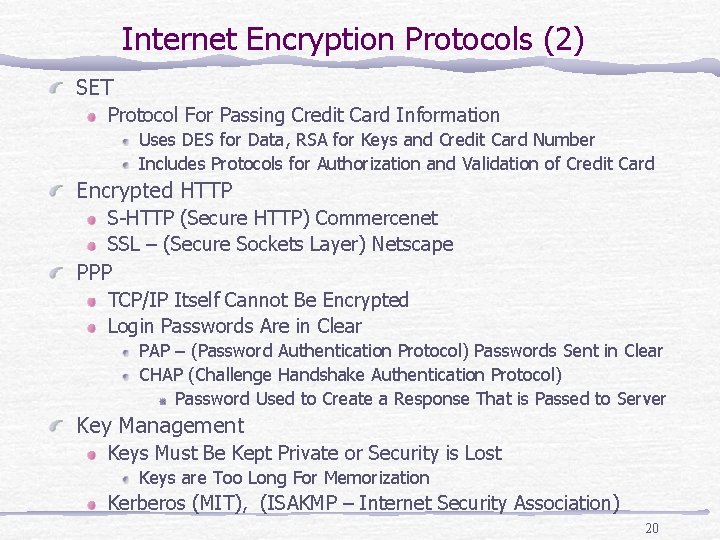
Internet Encryption Protocols (2) SET Protocol For Passing Credit Card Information Uses DES for Data, RSA for Keys and Credit Card Number Includes Protocols for Authorization and Validation of Credit Card Encrypted HTTP S-HTTP (Secure HTTP) Commercenet SSL – (Secure Sockets Layer) Netscape PPP TCP/IP Itself Cannot Be Encrypted Login Passwords Are in Clear PAP – (Password Authentication Protocol) Passwords Sent in Clear CHAP (Challenge Handshake Authentication Protocol) Password Used to Create a Response That is Passed to Server Key Management Keys Must Be Kept Private or Security is Lost Keys are Too Long For Memorization Kerberos (MIT), (ISAKMP – Internet Security Association) 20
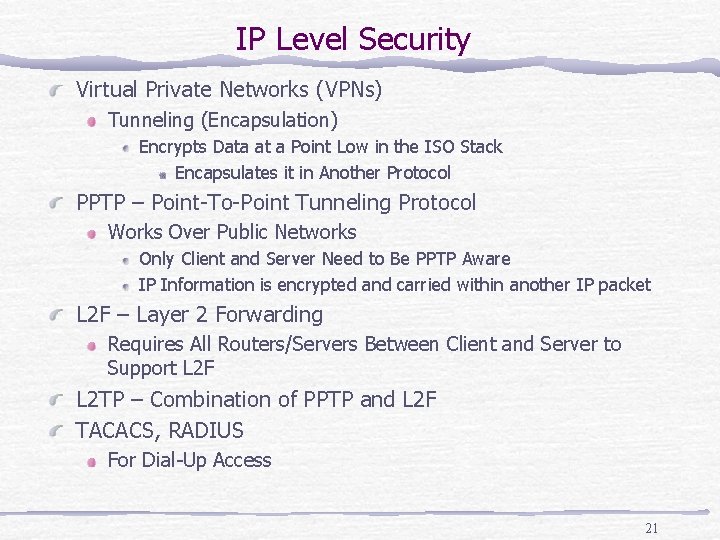
IP Level Security Virtual Private Networks (VPNs) Tunneling (Encapsulation) Encrypts Data at a Point Low in the ISO Stack Encapsulates it in Another Protocol PPTP – Point-To-Point Tunneling Protocol Works Over Public Networks Only Client and Server Need to Be PPTP Aware IP Information is encrypted and carried within another IP packet L 2 F – Layer 2 Forwarding Requires All Routers/Servers Between Client and Server to Support L 2 F L 2 TP – Combination of PPTP and L 2 F TACACS, RADIUS For Dial-Up Access 21
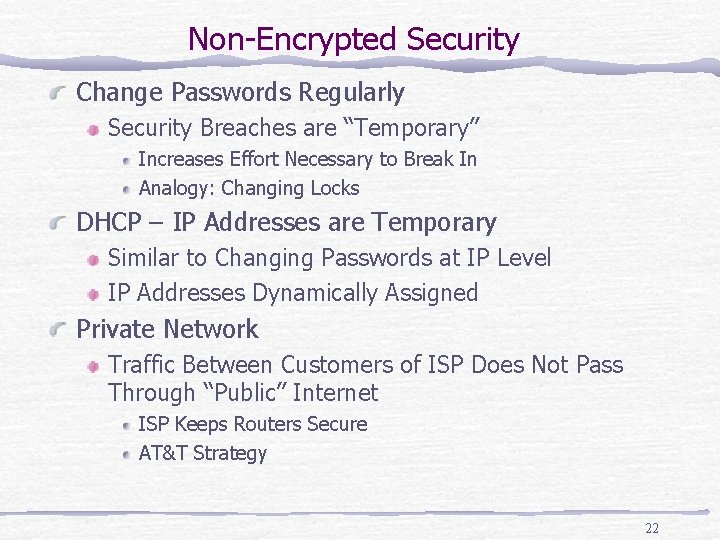
Non-Encrypted Security Change Passwords Regularly Security Breaches are “Temporary” Increases Effort Necessary to Break In Analogy: Changing Locks DHCP – IP Addresses are Temporary Similar to Changing Passwords at IP Level IP Addresses Dynamically Assigned Private Network Traffic Between Customers of ISP Does Not Pass Through “Public” Internet ISP Keeps Routers Secure AT&T Strategy 22
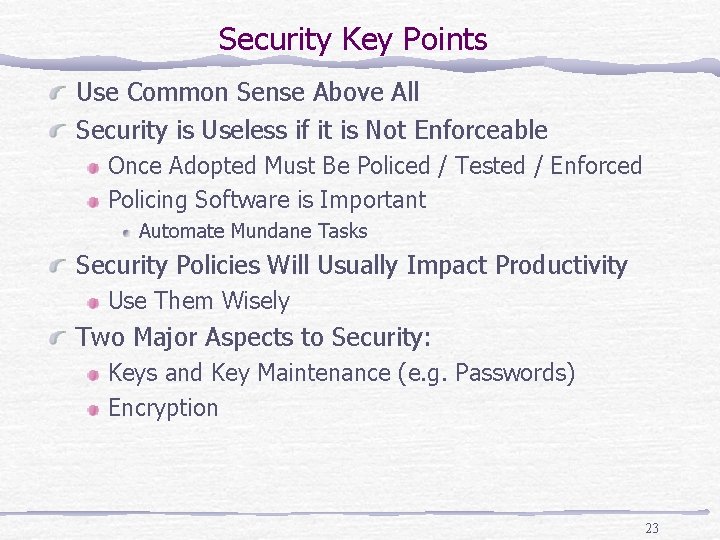
Security Key Points Use Common Sense Above All Security is Useless if it is Not Enforceable Once Adopted Must Be Policed / Tested / Enforced Policing Software is Important Automate Mundane Tasks Security Policies Will Usually Impact Productivity Use Them Wisely Two Major Aspects to Security: Keys and Key Maintenance (e. g. Passwords) Encryption 23
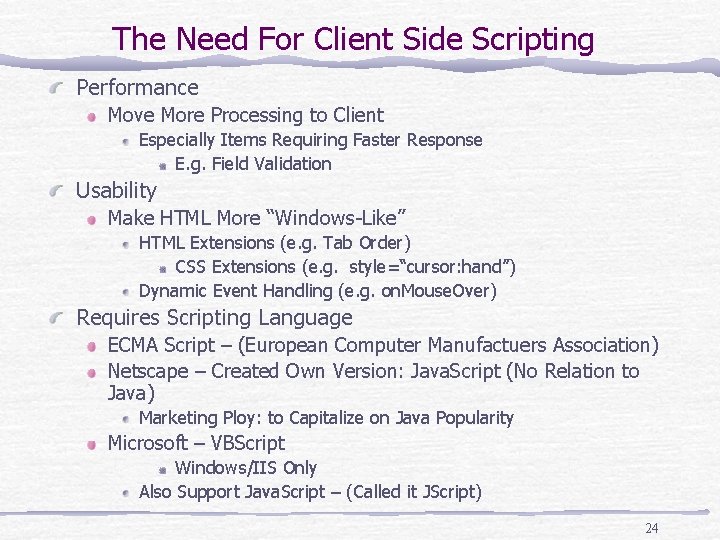
The Need For Client Side Scripting Performance Move More Processing to Client Especially Items Requiring Faster Response E. g. Field Validation Usability Make HTML More “Windows-Like” HTML Extensions (e. g. Tab Order) CSS Extensions (e. g. style=“cursor: hand”) Dynamic Event Handling (e. g. on. Mouse. Over) Requires Scripting Language ECMA Script – (European Computer Manufactuers Association) Netscape – Created Own Version: Java. Script (No Relation to Java) Marketing Ploy: to Capitalize on Java Popularity Microsoft – VBScript Windows/IIS Only Also Support Java. Script – (Called it JScript) 24
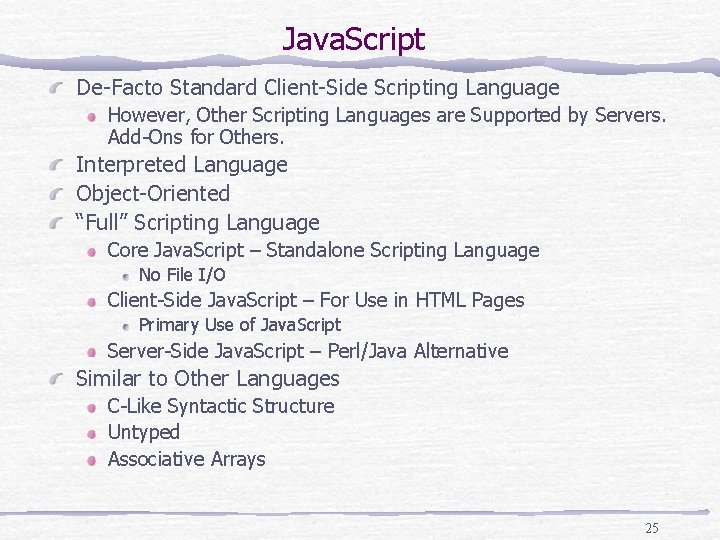
Java. Script De-Facto Standard Client-Side Scripting Language However, Other Scripting Languages are Supported by Servers. Add-Ons for Others. Interpreted Language Object-Oriented “Full” Scripting Language Core Java. Script – Standalone Scripting Language No File I/O Client-Side Java. Script – For Use in HTML Pages Primary Use of Java. Script Server-Side Java. Script – Perl/Java Alternative Similar to Other Languages C-Like Syntactic Structure Untyped Associative Arrays 25
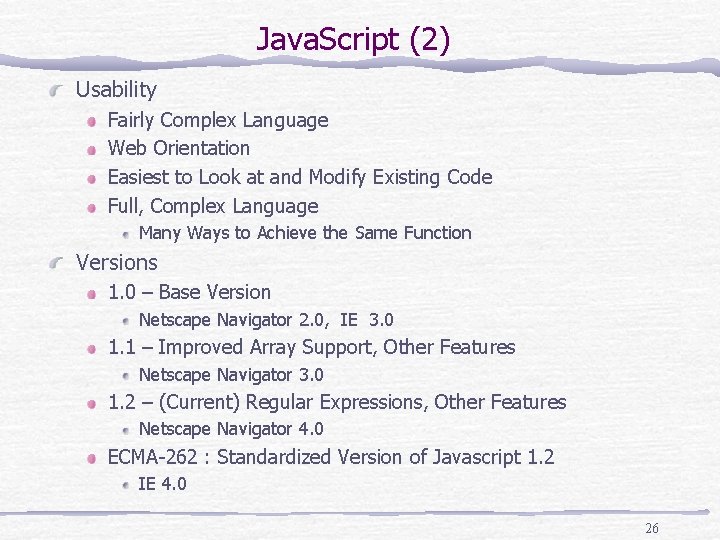
Java. Script (2) Usability Fairly Complex Language Web Orientation Easiest to Look at and Modify Existing Code Full, Complex Language Many Ways to Achieve the Same Function Versions 1. 0 – Base Version Netscape Navigator 2. 0, IE 3. 0 1. 1 – Improved Array Support, Other Features Netscape Navigator 3. 0 1. 2 – (Current) Regular Expressions, Other Features Netscape Navigator 4. 0 ECMA-262 : Standardized Version of Javascript 1. 2 IE 4. 0 26
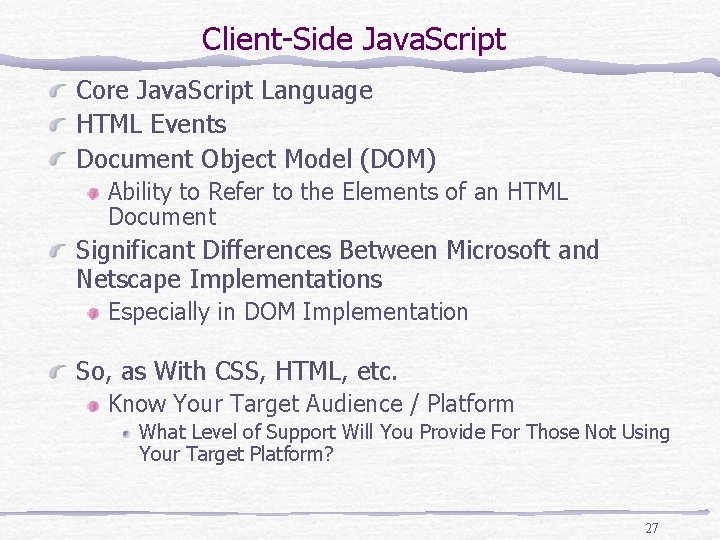
Client-Side Java. Script Core Java. Script Language HTML Events Document Object Model (DOM) Ability to Refer to the Elements of an HTML Document Significant Differences Between Microsoft and Netscape Implementations Especially in DOM Implementation So, as With CSS, HTML, etc. Know Your Target Audience / Platform What Level of Support Will You Provide For Those Not Using Your Target Platform? 27
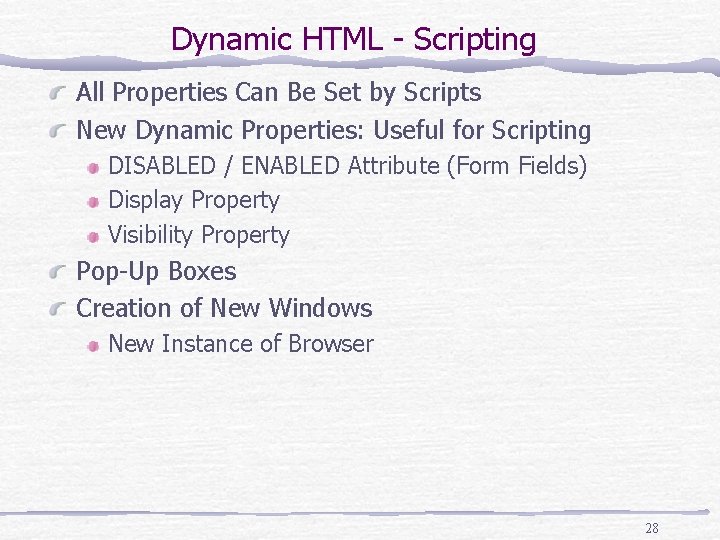
Dynamic HTML - Scripting All Properties Can Be Set by Scripts New Dynamic Properties: Useful for Scripting DISABLED / ENABLED Attribute (Form Fields) Display Property Visibility Property Pop-Up Boxes Creation of New Windows New Instance of Browser 28
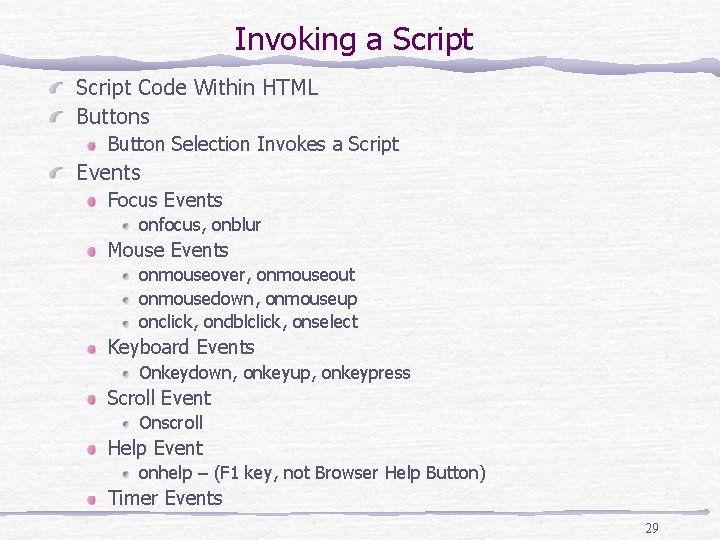
Invoking a Script Code Within HTML Buttons Button Selection Invokes a Script Events Focus Events onfocus, onblur Mouse Events onmouseover, onmouseout onmousedown, onmouseup onclick, ondblclick, onselect Keyboard Events Onkeydown, onkeyup, onkeypress Scroll Event Onscroll Help Event onhelp – (F 1 key, not Browser Help Button) Timer Events 29
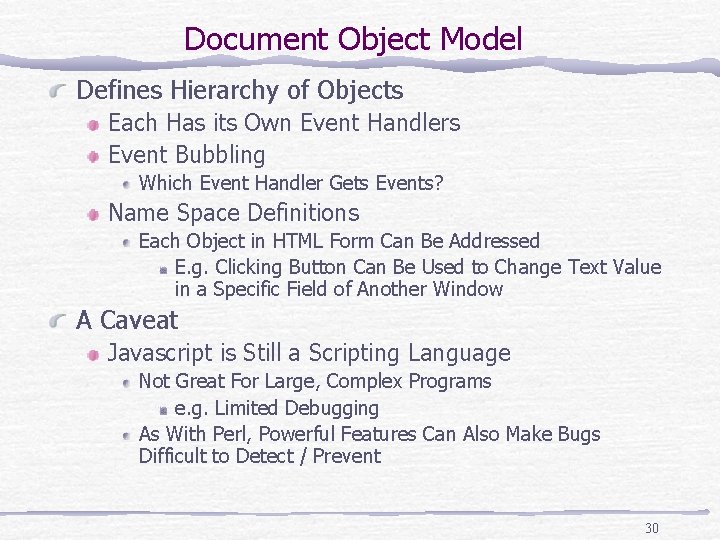
Document Object Model Defines Hierarchy of Objects Each Has its Own Event Handlers Event Bubbling Which Event Handler Gets Events? Name Space Definitions Each Object in HTML Form Can Be Addressed E. g. Clicking Button Can Be Used to Change Text Value in a Specific Field of Another Window A Caveat Javascript is Still a Scripting Language Not Great For Large, Complex Programs e. g. Limited Debugging As With Perl, Powerful Features Can Also Make Bugs Difficult to Detect / Prevent 30
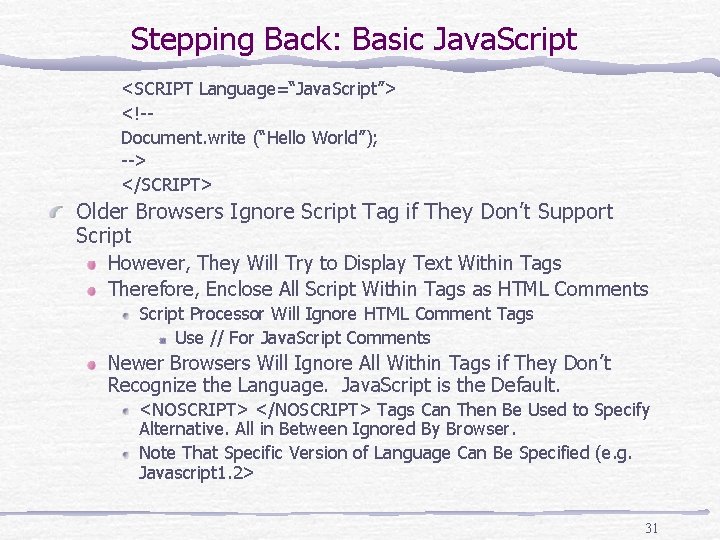
Stepping Back: Basic Java. Script <SCRIPT Language=“Java. Script”> <!-Document. write (“Hello World”); --> </SCRIPT> Older Browsers Ignore Script Tag if They Don’t Support Script However, They Will Try to Display Text Within Tags Therefore, Enclose All Script Within Tags as HTML Comments Script Processor Will Ignore HTML Comment Tags Use // For Java. Script Comments Newer Browsers Will Ignore All Within Tags if They Don’t Recognize the Language. Java. Script is the Default. <NOSCRIPT> </NOSCRIPT> Tags Can Then Be Used to Specify Alternative. All in Between Ignored By Browser. Note That Specific Version of Language Can Be Specified (e. g. Javascript 1. 2> 31
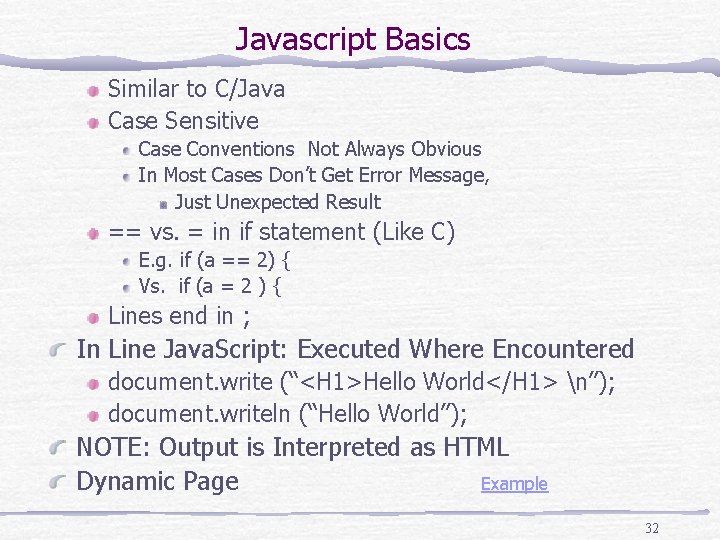
Javascript Basics Similar to C/Java Case Sensitive Case Conventions Not Always Obvious In Most Cases Don’t Get Error Message, Just Unexpected Result == vs. = in if statement (Like C) E. g. if (a == 2) { Vs. if (a = 2 ) { Lines end in ; In Line Java. Script: Executed Where Encountered document. write (“<H 1>Hello World</H 1> n”); document. writeln (“Hello World”); NOTE: Output is Interpreted as HTML Dynamic Page Example 32
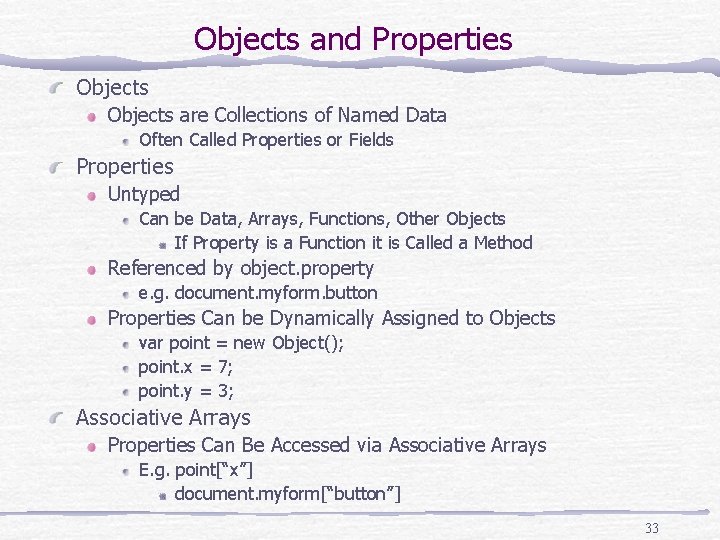
Objects and Properties Objects are Collections of Named Data Often Called Properties or Fields Properties Untyped Can be Data, Arrays, Functions, Other Objects If Property is a Function it is Called a Method Referenced by object. property e. g. document. myform. button Properties Can be Dynamically Assigned to Objects var point = new Object(); point. x = 7; point. y = 3; Associative Arrays Properties Can Be Accessed via Associative Arrays E. g. point[“x”] document. myform[“button”] 33
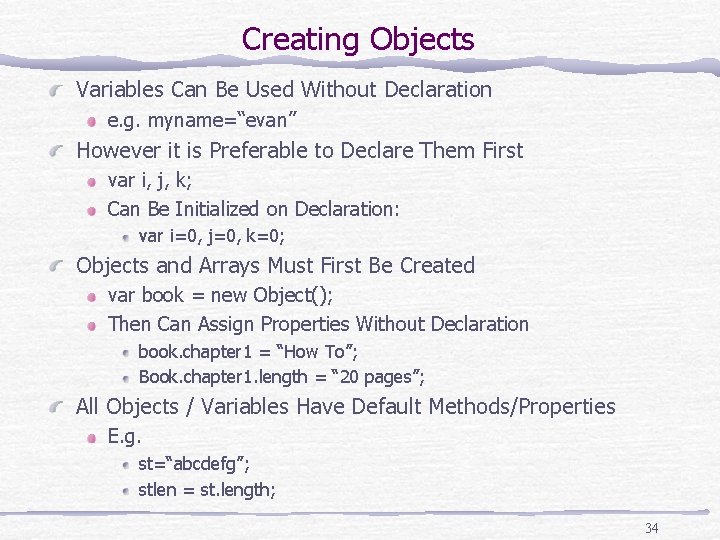
Creating Objects Variables Can Be Used Without Declaration e. g. myname=“evan” However it is Preferable to Declare Them First var i, j, k; Can Be Initialized on Declaration: var i=0, j=0, k=0; Objects and Arrays Must First Be Created var book = new Object(); Then Can Assign Properties Without Declaration book. chapter 1 = “How To”; Book. chapter 1. length = “ 20 pages”; All Objects / Variables Have Default Methods/Properties E. g. st=“abcdefg”; stlen = st. length; 34
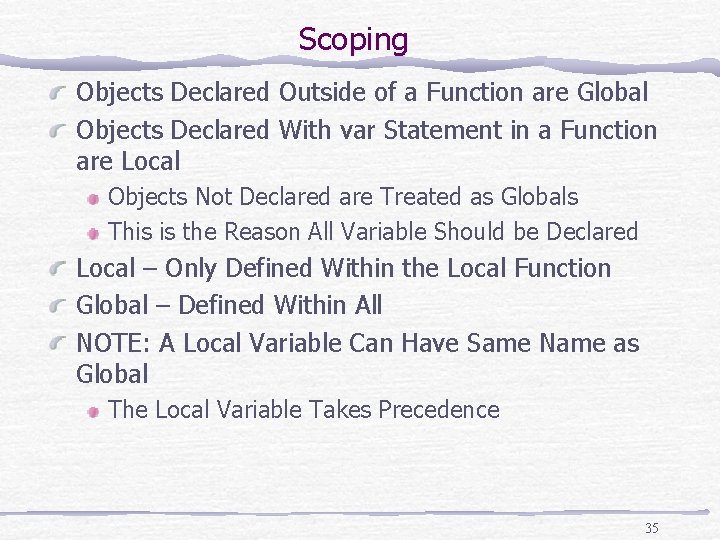
Scoping Objects Declared Outside of a Function are Global Objects Declared With var Statement in a Function are Local Objects Not Declared are Treated as Globals This is the Reason All Variable Should be Declared Local – Only Defined Within the Local Function Global – Defined Within All NOTE: A Local Variable Can Have Same Name as Global The Local Variable Takes Precedence 35
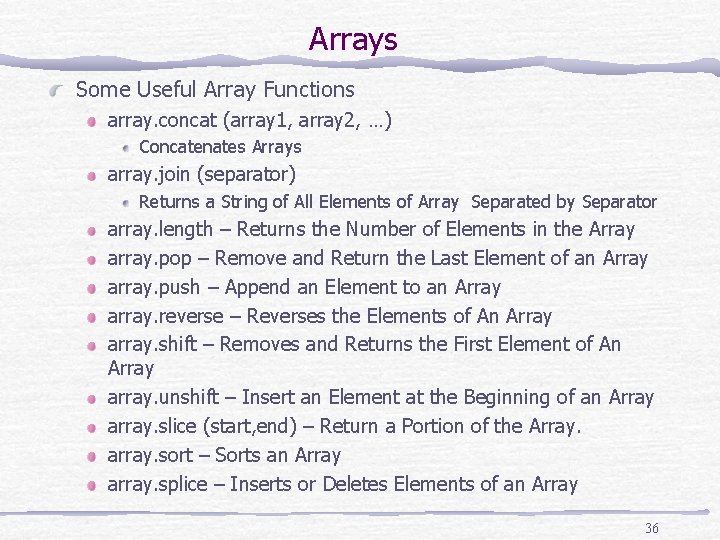
Arrays Some Useful Array Functions array. concat (array 1, array 2, …) Concatenates Arrays array. join (separator) Returns a String of All Elements of Array Separated by Separator array. length – Returns the Number of Elements in the Array array. pop – Remove and Return the Last Element of an Array array. push – Append an Element to an Array array. reverse – Reverses the Elements of An Array array. shift – Removes and Returns the First Element of An Array array. unshift – Insert an Element at the Beginning of an Array array. slice (start, end) – Return a Portion of the Array. array. sort – Sorts an Array array. splice – Inserts or Deletes Elements of an Array 36
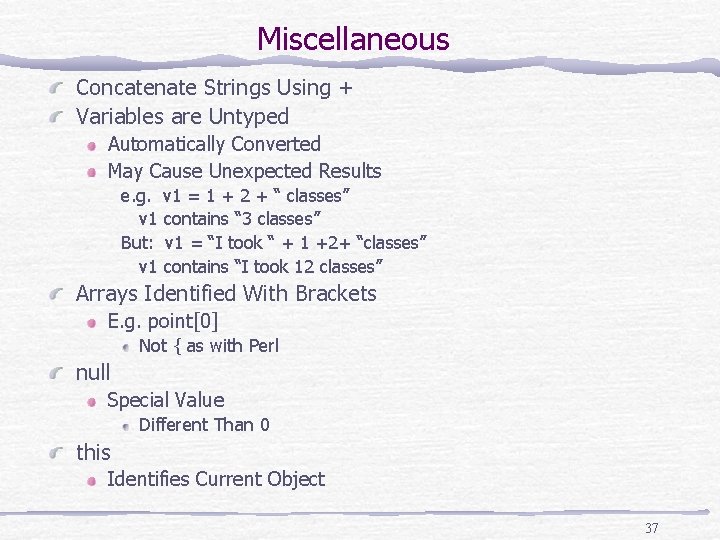
Miscellaneous Concatenate Strings Using + Variables are Untyped Automatically Converted May Cause Unexpected Results e. g. v 1 = 1 + 2 + “ classes” v 1 contains “ 3 classes” But: v 1 = “I took “ + 1 +2+ “classes” v 1 contains “I took 12 classes” Arrays Identified With Brackets E. g. point[0] Not { as with Perl null Special Value Different Than 0 this Identifies Current Object 37
Functions Use return Statement to Return a Value from a Function E. g. return (3); arguments is a Special Object Available in a Function arguments[] Holds the Argument Values Passed In Arguments. length – The Number of Arguments Passed 38
More Java. Script Comments are // or /* */ Strings concatenated with + Functions Should be Declared Before Being Used Typically Defined in <HEAD> Section alert – Creates a Pop-Up Message Box prompt – Prompts User for Input Buttons - <Input Type = “Button” Value=“Click Here” onclick = “functionname()” window. open – Opens a New Instance of Browser Example 39
More Examples Events Example on. Load on. Unload Environment Information Example HTTP Header Information Cookies 40
In-Class Exercise Create a Java. Script version of your test page <SCRIPT LANGUAGE = “Java. Script”> myname = “Evan”; Document. writeln(“<H 1>Welcome to “ + myname + “’s Homepage”</H 1>”) </SCRIPT> Add a BUTTON to your Homepage to show this page in a new Browser Window Advanced: Choose the Name at Random. Set this in a function. 41
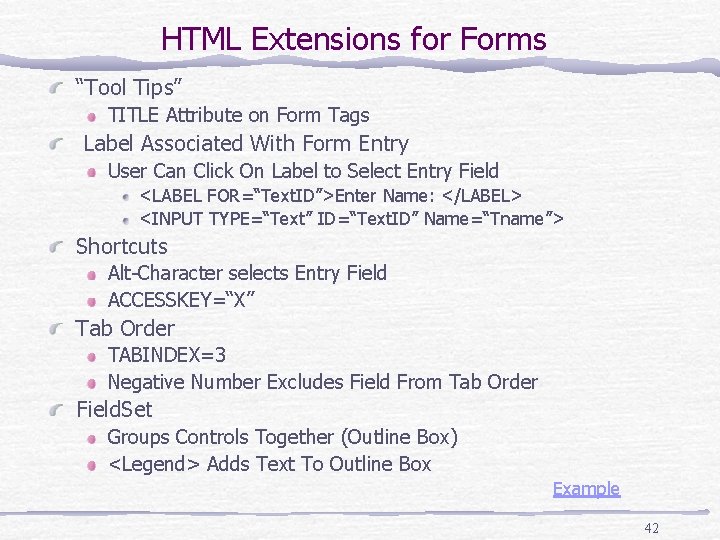
HTML Extensions for Forms “Tool Tips” TITLE Attribute on Form Tags Label Associated With Form Entry User Can Click On Label to Select Entry Field <LABEL FOR=“Text. ID”>Enter Name: </LABEL> <INPUT TYPE=“Text” ID=“Text. ID” Name=“Tname”> Shortcuts Alt-Character selects Entry Field ACCESSKEY=“X” Tab Order TABINDEX=3 Negative Number Excludes Field From Tab Order Field. Set Groups Controls Together (Outline Box) <Legend> Adds Text To Outline Box Example 42
- Slides: 42