Internet Intranet CIS536 Class 10 Brandeis University InternetIntranet
Internet / Intranet CIS-536 Class 10 Brandeis University Internet/Intranet Spring 2000
Class 10 Agenda Milestone#4 - Discussion Presentations Cookies Misc. Topics Wireless Devices: WAP / WML Wrap-Up 2
Cookies Revisited Cookies Are Name Value Pairs Passed in the HTTP Header Cookies Have Associated Expiration Session (Default) Date / Time Associated With a URL Path, Not a Page! Allows Passing Parameters Between Web Pages Thus Cookies are Used to Provide State Information to a Stateless Protocol 3
Cookie Jar Cookie Storage Internet Explorer c: windowscookies Each Has its Own File Netscape Navigator cookies. txt (all kept in the file) Limits 20 Cookies 4 K Per Name/Value Pair 4
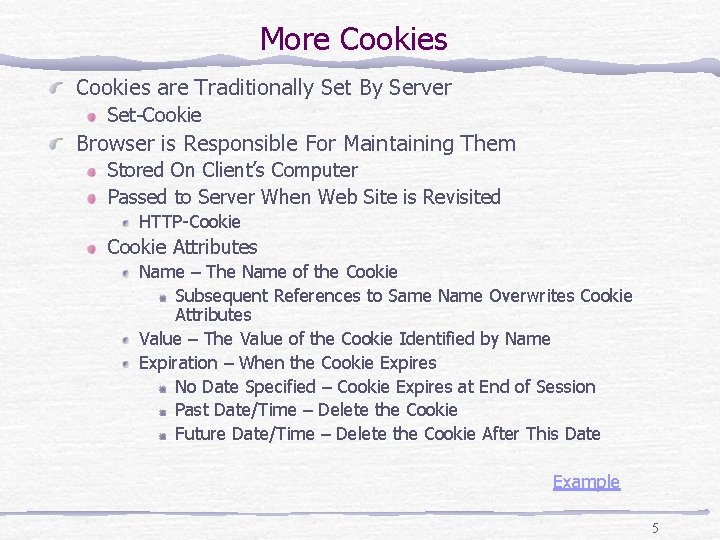
More Cookies are Traditionally Set By Server Set-Cookie Browser is Responsible For Maintaining Them Stored On Client’s Computer Passed to Server When Web Site is Revisited HTTP-Cookie Attributes Name – The Name of the Cookie Subsequent References to Same Name Overwrites Cookie Attributes Value – The Value of the Cookie Identified by Name Expiration – When the Cookie Expires No Date Specified – Cookie Expires at End of Session Past Date/Time – Delete the Cookie Future Date/Time – Delete the Cookie After This Date Example 5
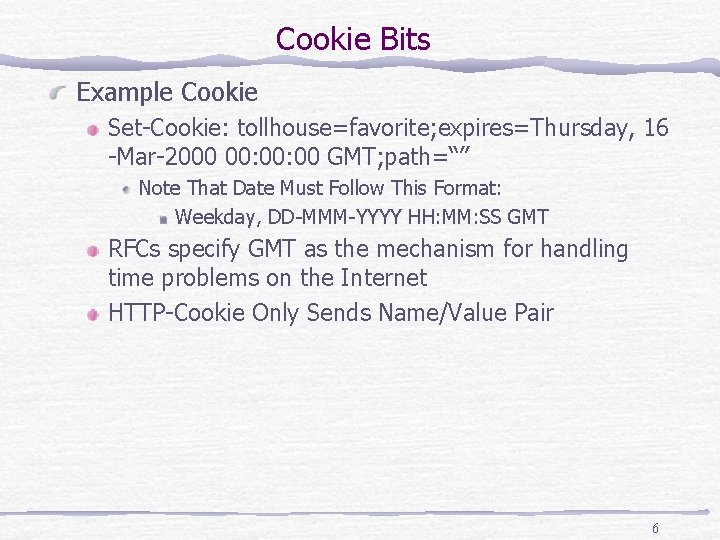
Cookie Bits Example Cookie Set-Cookie: tollhouse=favorite; expires=Thursday, 16 -Mar-2000 00: 00 GMT; path=“” Note That Date Must Follow This Format: Weekday, DD-MMM-YYYY HH: MM: SS GMT RFCs specify GMT as the mechanism for handling time problems on the Internet HTTP-Cookie Only Sends Name/Value Pair 6
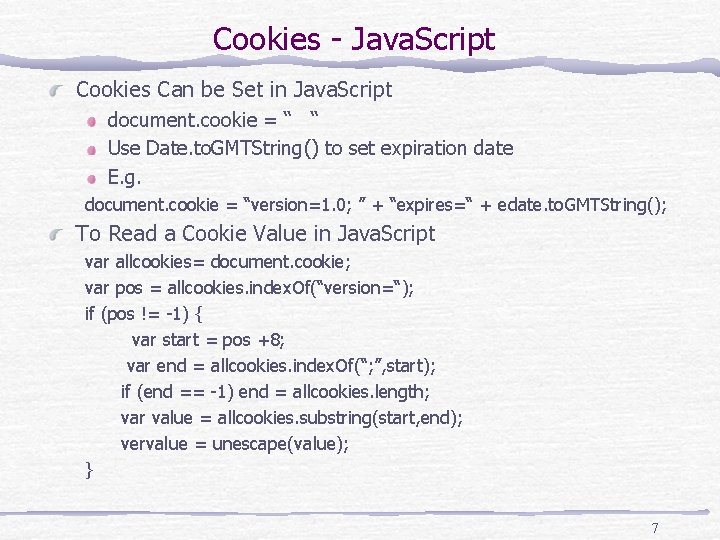
Cookies - Java. Script Cookies Can be Set in Java. Script document. cookie = “ “ Use Date. to. GMTString() to set expiration date E. g. document. cookie = “version=1. 0; ” + “expires=“ + edate. to. GMTString(); To Read a Cookie Value in Java. Script var allcookies= document. cookie; var pos = allcookies. index. Of(“version=“); if (pos != -1) { var start = pos +8; var end = allcookies. index. Of(“; ”, start); if (end == -1) end = allcookies. length; var value = allcookies. substring(start, end); vervalue = unescape(value); } 7
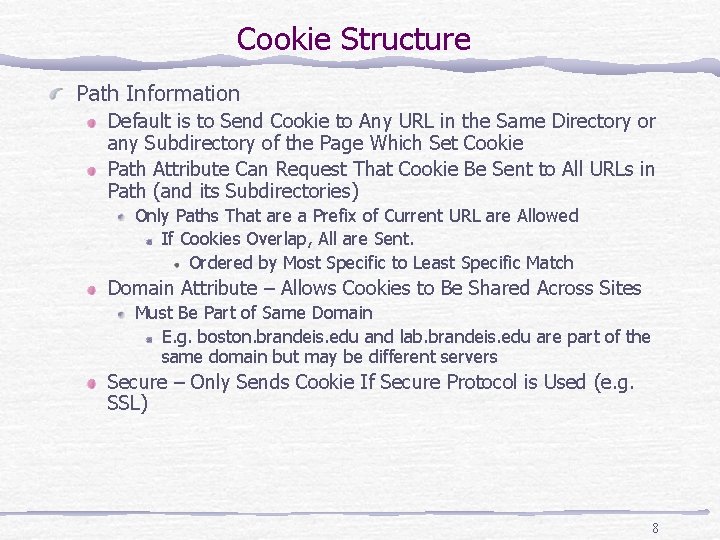
Cookie Structure Path Information Default is to Send Cookie to Any URL in the Same Directory or any Subdirectory of the Page Which Set Cookie Path Attribute Can Request That Cookie Be Sent to All URLs in Path (and its Subdirectories) Only Paths That are a Prefix of Current URL are Allowed If Cookies Overlap, All are Sent. Ordered by Most Specific to Least Specific Match Domain Attribute – Allows Cookies to Be Shared Across Sites Must Be Part of Same Domain E. g. boston. brandeis. edu and lab. brandeis. edu are part of the same domain but may be different servers Secure – Only Sends Cookie If Secure Protocol is Used (e. g. SSL) 8
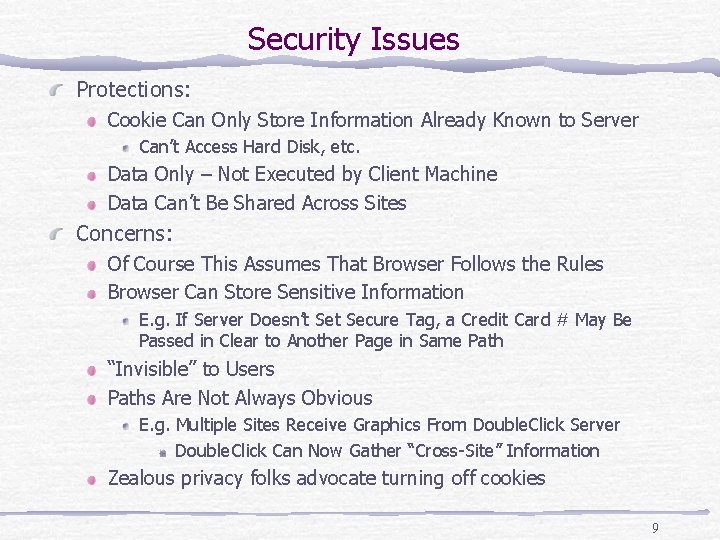
Security Issues Protections: Cookie Can Only Store Information Already Known to Server Can’t Access Hard Disk, etc. Data Only – Not Executed by Client Machine Data Can’t Be Shared Across Sites Concerns: Of Course This Assumes That Browser Follows the Rules Browser Can Store Sensitive Information E. g. If Server Doesn’t Secure Tag, a Credit Card # May Be Passed in Clear to Another Page in Same Path “Invisible” to Users Paths Are Not Always Obvious E. g. Multiple Sites Receive Graphics From Double. Click Server Double. Click Can Now Gather “Cross-Site” Information Zealous privacy folks advocate turning off cookies 9
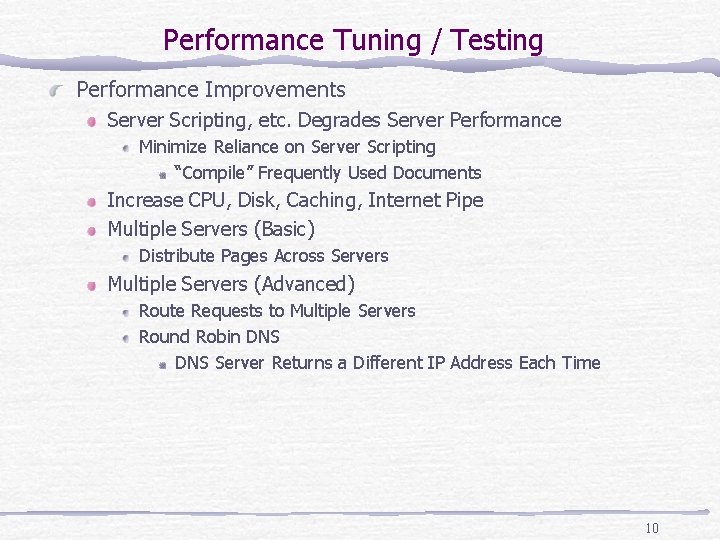
Performance Tuning / Testing Performance Improvements Server Scripting, etc. Degrades Server Performance Minimize Reliance on Server Scripting “Compile” Frequently Used Documents Increase CPU, Disk, Caching, Internet Pipe Multiple Servers (Basic) Distribute Pages Across Servers Multiple Servers (Advanced) Route Requests to Multiple Servers Round Robin DNS Server Returns a Different IP Address Each Time 10
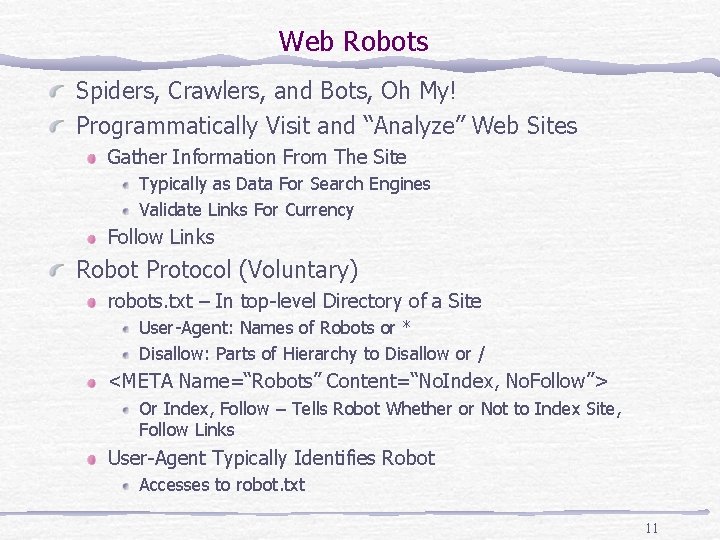
Web Robots Spiders, Crawlers, and Bots, Oh My! Programmatically Visit and “Analyze” Web Sites Gather Information From The Site Typically as Data For Search Engines Validate Links For Currency Follow Links Robot Protocol (Voluntary) robots. txt – In top-level Directory of a Site User-Agent: Names of Robots or * Disallow: Parts of Hierarchy to Disallow or / <META Name=“Robots” Content=“No. Index, No. Follow”> Or Index, Follow – Tells Robot Whether or Not to Index Site, Follow Links User-Agent Typically Identifies Robot Accesses to robot. txt 11
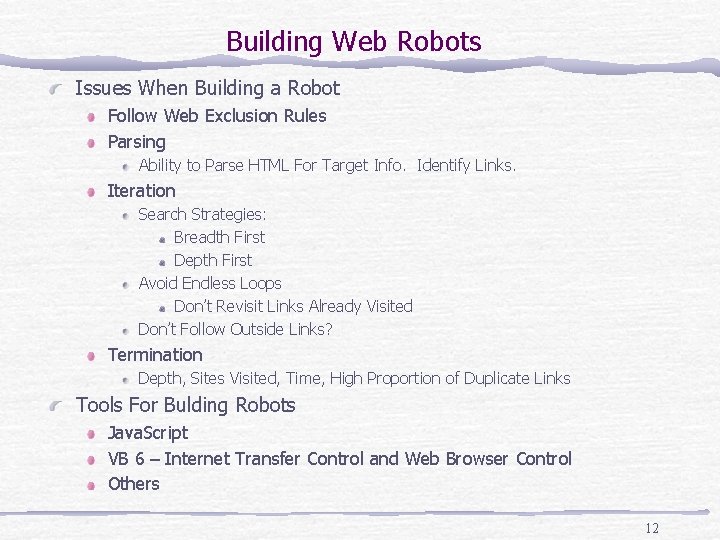
Building Web Robots Issues When Building a Robot Follow Web Exclusion Rules Parsing Ability to Parse HTML For Target Info. Identify Links. Iteration Search Strategies: Breadth First Depth First Avoid Endless Loops Don’t Revisit Links Already Visited Don’t Follow Outside Links? Termination Depth, Sites Visited, Time, High Proportion of Duplicate Links Tools For Bulding Robots Java. Script VB 6 – Internet Transfer Control and Web Browser Control Others 12
Trends toward smaller devices Moore’s law History of Computers trend toward smaller devices trend toward cheaper devices processors in more and more devices TCP/IP can expand well beyond PCs 5 year time frame ( Gartner Group ) a billion mobile phones ( US lags behind Europe and Asia ) over half of Internet access through non-PCs M-Commerce replaces E-Commerce 13
Wireless Internet HDML - 1995 Handheld Device Markup Language subset of HTML I-mode - Japan uses a tag language based on HTML c. HTML 7 million users WAP/ WML currently at 1. 3 ( 1. 1 widely supported ) protocol extends Internet to Phones specialized for smaller screens GPRS general packet radio switching 14
Wireless ‘Non-Internet’ continued investment - limited commercial success Bluetooth develop a wireless standard for all devices low earth orbit satellites must be in low orbit big time failures (Iridium, Globalstar) Teledisic ? ? ( Bill Gates and Craig Mc. Caw ) Many premature predictions about wireless 1993 was supposed to be the year of wireless issues of latency, reliability, security, processing power 15
WAP Application Architecture WAP Gateways connect Wireless Messages with Internet Leverage the Internet plumbing Wireless requested converted to HTTP 16
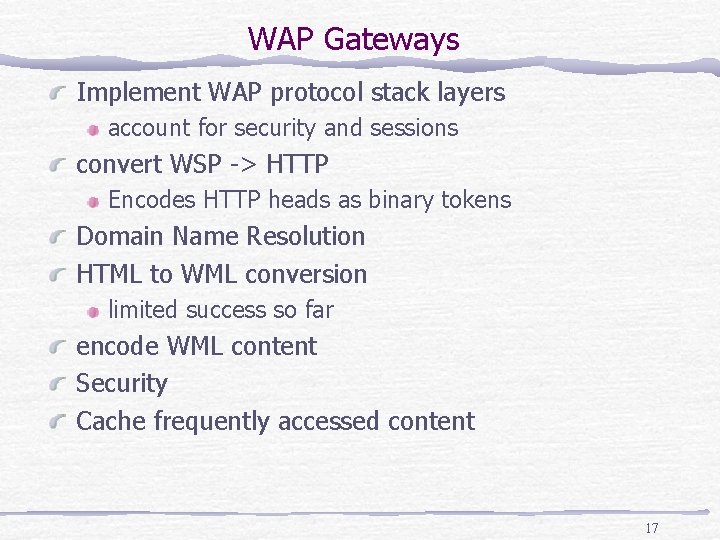
WAP Gateways Implement WAP protocol stack layers account for security and sessions convert WSP -> HTTP Encodes HTTP heads as binary tokens Domain Name Resolution HTML to WML conversion limited success so far encode WML content Security Cache frequently accessed content 17
WAP Gateways offered by all major vendors Noika Motorola Ericsson Kannel ( Open-Source WAP Gateway ) 18
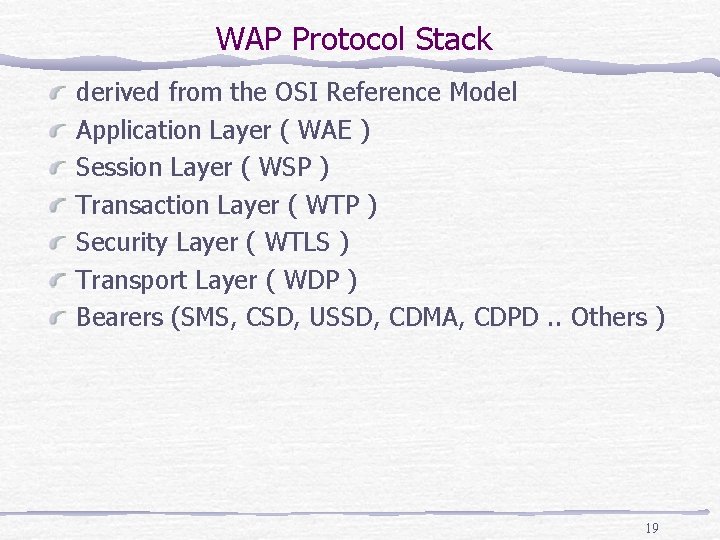
WAP Protocol Stack derived from the OSI Reference Model Application Layer ( WAE ) Session Layer ( WSP ) Transaction Layer ( WTP ) Security Layer ( WTLS ) Transport Layer ( WDP ) Bearers (SMS, CSD, USSD, CDMA, CDPD. . Others ) 19
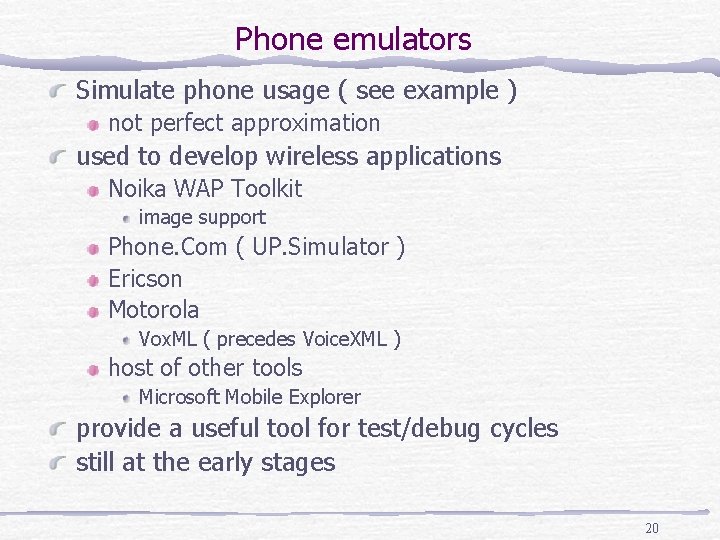
Phone emulators Simulate phone usage ( see example ) not perfect approximation used to develop wireless applications Noika WAP Toolkit image support Phone. Com ( UP. Simulator ) Ericson Motorola Vox. ML ( precedes Voice. XML ) host of other tools Microsoft Mobile Explorer provide a useful tool for test/debug cycles still at the early stages 20
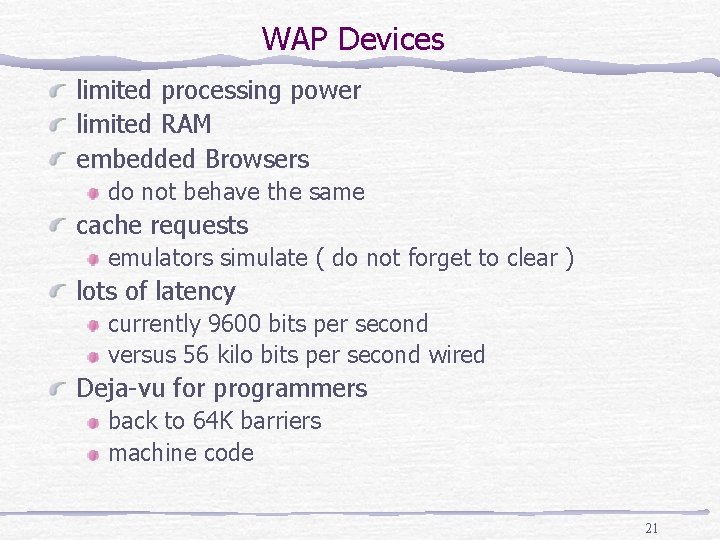
WAP Devices limited processing power limited RAM embedded Browsers do not behave the same cache requests emulators simulate ( do not forget to clear ) lots of latency currently 9600 bits per second versus 56 kilo bits per second wired Deja-vu for programmers back to 64 K barriers machine code 21
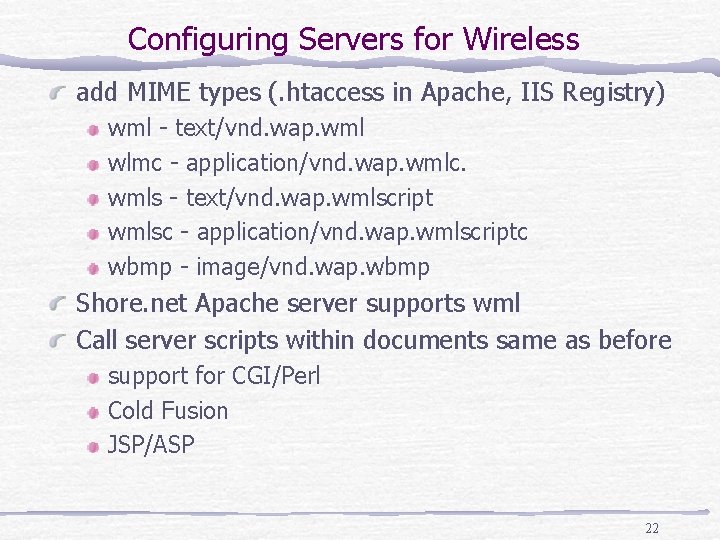
Configuring Servers for Wireless add MIME types (. htaccess in Apache, IIS Registry) wml - text/vnd. wap. wml wlmc - application/vnd. wap. wmlc. wmls - text/vnd. wap. wmlscript wmlsc - application/vnd. wap. wmlscriptc wbmp - image/vnd. wap. wbmp Shore. net Apache server supports wml Call server scripts within documents same as before support for CGI/Perl Cold Fusion JSP/ASP 22
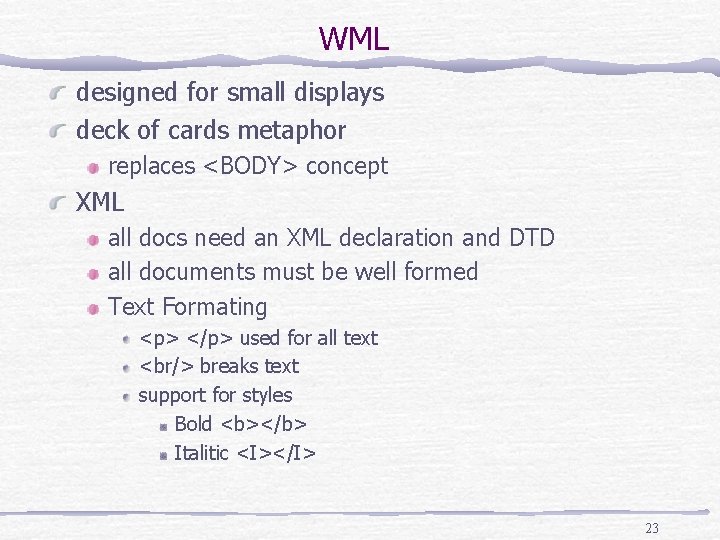
WML designed for small displays deck of cards metaphor replaces <BODY> concept XML all docs need an XML declaration and DTD all documents must be well formed Text Formating <p> </p> used for all text <br/> breaks text support for styles Bold <b></b> Italitic <I></I> 23
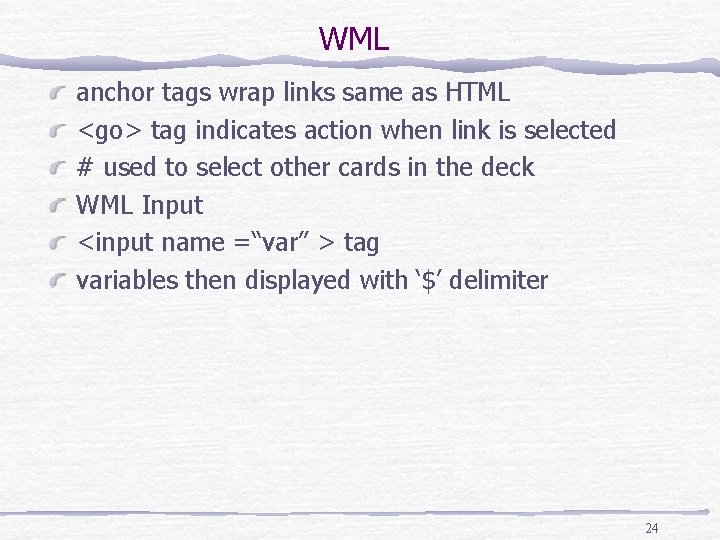
WML anchor tags wrap links same as HTML <go> tag indicates action when link is selected # used to select other cards in the deck WML Input <input name =“var” > tag variables then displayed with ‘$’ delimiter 24
More WML <prev> tag sends the user back to the previous document <do> associates an action with a given element <do type=“prev” label=“Previous”> <prev/> </do> Creates a Previous operation for a softkey <select> element 25
Wireless Scripting WMLScript - based on ECMAscript useful for validation WML tags support events timers card supports three main events onenterforward onenterbackward on. Timer 26
WML GET/POST request WML supports HTTP Get & Post GET Request append data as parameter to the URL use WMLScript POST Request specify as an attribute in the <go> tag <go method=“post” href=“somescript. pl”> <postfield name=“product” value=“$(product)”/> </go> 27
WML Images wireless bitmaps (WBMP) monochrome initially needed to convert bits in GIF and JPG files tools are emerging Nokia toolkit supports plug-ins exist for most major tools ( Photoshop, Paintshop) watch out for latency !!! Large bitmaps 28
Usability Terse documents WML apps need to deliver bullet points short text labels minimize data entry sites need high personalization NOT the Internet on a cell-phone New applications will be created Still significant browser differences tags do not work in a uniform way significant differences in screen size 29
WAP Resources WAP FAQ http: //www. wap. com WAP forum http: //www. wapforum. org Professional WAP ( Wrox Press ) ISDN 1 -861004 -04 -4 30
Presentations Mirrors Real Life Situations Co. Workers, Audience Have Different Backgrounds Relevance to Audience Varies Some With Lots of Experience – Want Details Management vs. Technical Personnel Strategy: Give Enough Background to Identify Key Issue Most Will File it Away for Future Reference Identify Target Audience Give “Meaty” Info Be Judicious With Time Can’t Cover Everything Provide Reference Material Those Who Want to Learn More Can Most Will Want Info at Some Point in Future 31
Career Advice Software Engineering Growth Paths Require Ability to Bridge Gap Between Management and Technical Management Concerned With Practical Implications, Not Technical Details Technical Knowledge and Ability to Implement Task “Political” Different Personalities Have Different Expectations Valuable Skills Technical Knowledge Customer Requirements Development Schedule / Quality / Maintenance / Cost Mentorship Communication 32
Wrap-Up Ongoing Resource: evan@mkat. com General Questions Jobs, etc. Grading Shore. Net Accounts Class Web Site Enjoy Your Break! 33
- Slides: 33