Elliptic Curve Cryptography ECC Motivation Basis of modern
Elliptic Curve Cryptography (ECC) 전자부품심사팀 한선경
Motivation Basis of modern cryptosystems Intractability for mathematical strength Excessively long key length • RSA, Diffie-Hellman key exchange, digital signatures • discrete logarithm problem(DLP) • integer factoring • to ensure secure systems, key sizes must be a minimum of 1024 bits Longer key sizes needed to guarantee security • increasing computing power • higher computational costs and low scalability 1
Background EC studied more than 150 years Utilized in devising algorithms for Defined over any field, Only the finite field for cryptographic purposes • factoring integers • primality tests • public-key cipher • real numbers • complex numbers, etc. 2
Background Elliptic Curve Cryptography(ECC) • Proposed independently in 1985 • Neal Koblitz (the University of Washington) • Victor Miller (IBM) Yorktown Heights • Based on the operations on points of a specific elliptic curve in a • • field. Found on mathematical intractability of the elliptic curve discrete logarithm problem (ECDLP) Use smaller key lengths (160 – 256 bits) • Provide faster public key methods • Smaller key sizes reduces disk and bandwidth utilization • Wide range of applicability • e-commerce, smart cards, and small portable devices • No sub-exponential time algorithm to break • The finite field for cryptographic purposes • GF(2 m), GF(pm), etc. 3
Background Easy to Implement Shorter Keys Less Computationally Extensive No Dedicated Processor Patent-Free Secure Content Protection(5 C), Mobile Phone(WAP), Smart Cards, etc 4
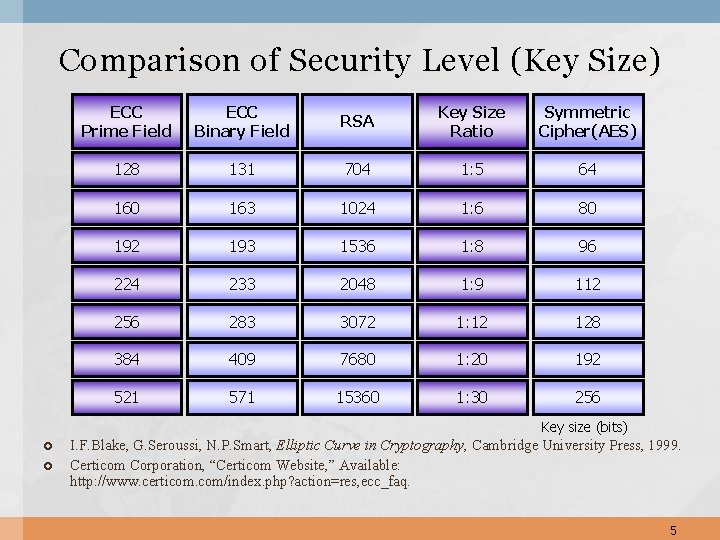
Comparison of Security Level (Key Size) ECC Prime Field ECC Binary Field RSA Key Size Ratio Symmetric Cipher(AES) 128 131 704 1: 5 64 160 163 1024 1: 6 80 192 193 1536 1: 8 96 224 233 2048 1: 9 112 256 283 3072 1: 12 128 384 409 7680 1: 20 192 521 571 15360 1: 30 256 Key size (bits) I. F. Blake, G. Seroussi, N. P. Smart, Elliptic Curve in Cryptography, Cambridge University Press, 1999. Certicom Corporation, “Certicom Website, ” Available: http: //www. certicom. com/index. php? action=res, ecc_faq. 5
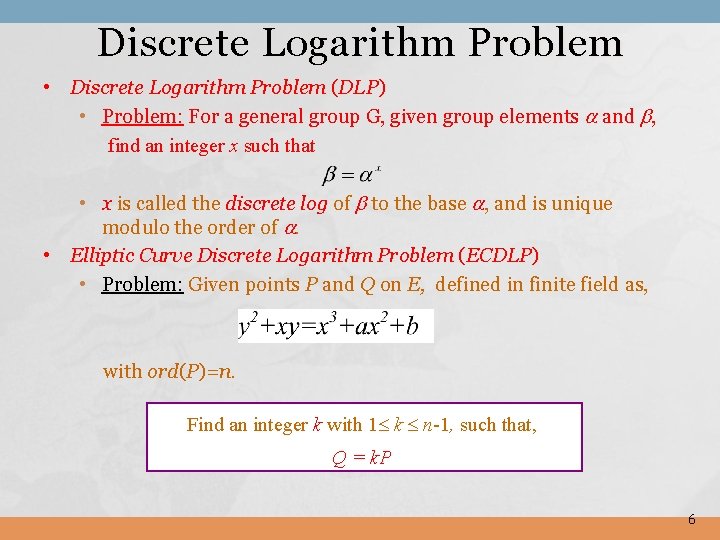
Discrete Logarithm Problem • Discrete Logarithm Problem (DLP) • Problem: For a general group G, given group elements and , find an integer x such that • x is called the discrete log of to the base , and is unique modulo the order of . • Elliptic Curve Discrete Logarithm Problem (ECDLP) • Problem: Given points P and Q on E, defined in finite field as, with ord(P)=n. Find an integer k with 1 k n-1, such that, Q = k. P 6
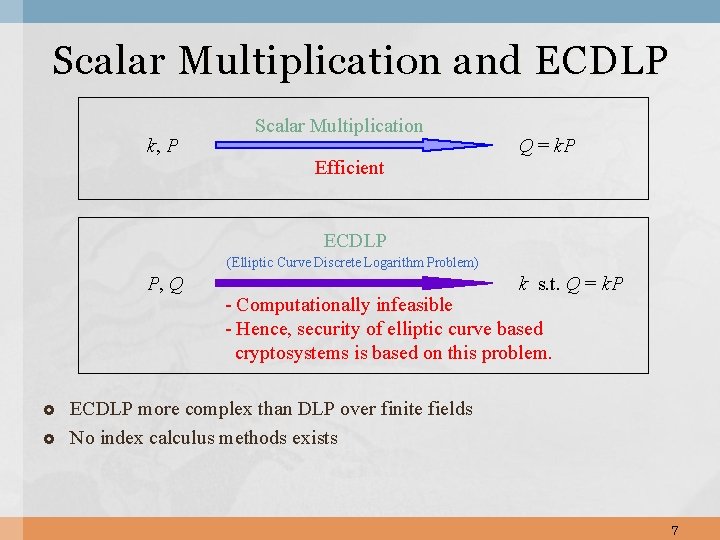
Scalar Multiplication and ECDLP k, P Scalar Multiplication Efficient Q = k. P ECDLP (Elliptic Curve Discrete Logarithm Problem) P, Q k s. t. Q = k. P - Computationally infeasible - Hence, security of elliptic curve based cryptosystems is based on this problem. ECDLP more complex than DLP over finite fields No index calculus methods exists 7
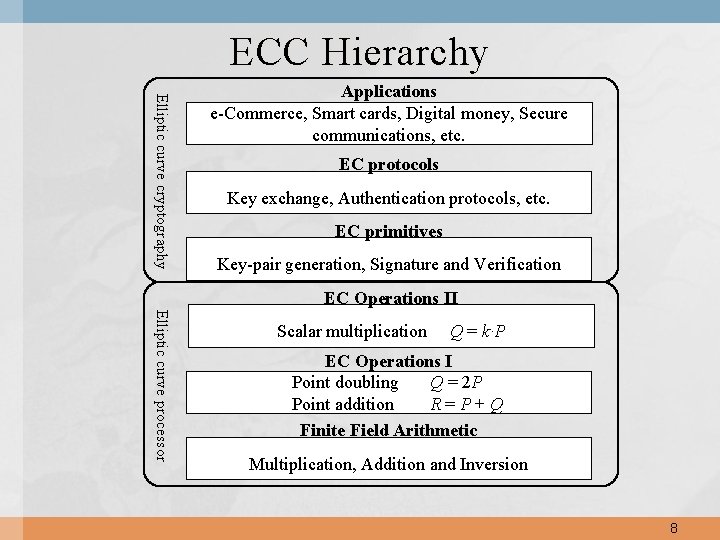
ECC Hierarchy Elliptic curve cryptography Applications e-Commerce, Smart cards, Digital money, Secure communications, etc. EC protocols Key exchange, Authentication protocols, etc. EC primitives Key-pair generation, Signature and Verification EC Operations II Elliptic curve processor Scalar multiplication Q = k·P EC Operations I Point doubling Q = 2 P Point addition R=P+Q Finite Field Arithmetic Multiplication, Addition and Inversion 8
What is Elliptic Curve?
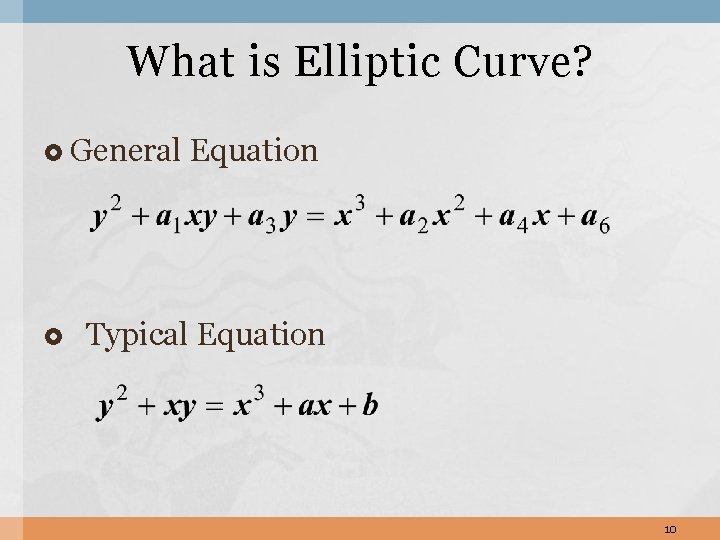
What is Elliptic Curve? General Equation Typical Equation 10
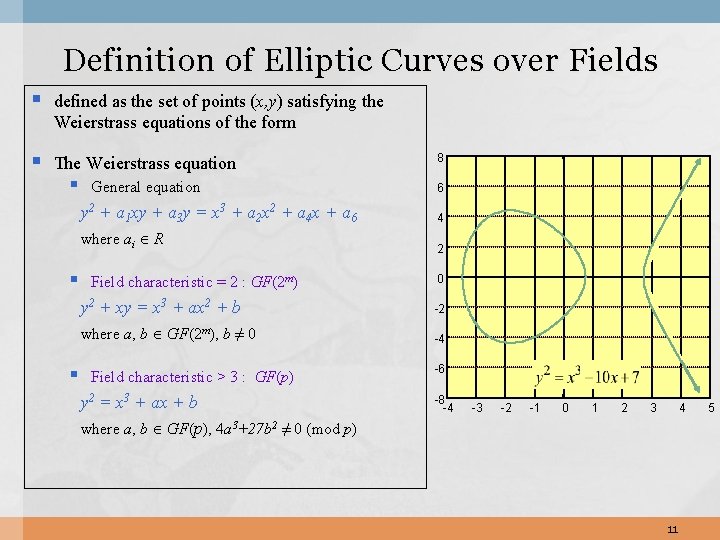
Definition of Elliptic Curves over Fields § defined as the set of points (x, y) satisfying the Weierstrass equations of the form § The Weierstrass equation § § § General equation 8 6 y 2 + a 1 xy + a 3 y = x 3 + a 2 x 2 + a 4 x + a 6 4 where ai R 2 Field characteristic = 2 : GF(2 m) 0 y 2 + xy = x 3 + ax 2 + b -2 where a, b GF(2 m), b ≠ 0 -4 Field characteristic > 3 : GF(p) y 2 = x 3 + ax + b where a, b GF(p), 4 a 3+27 b 2 ≠ 0 (mod p) -6 -8 -4 -3 -2 -1 0 1 2 3 4 11 5
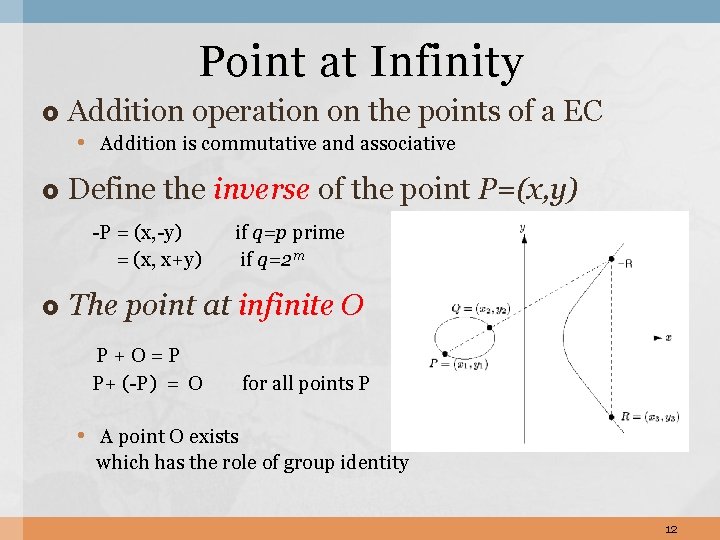
Point at Infinity Addition operation on the points of a EC • Addition is commutative and associative Define the inverse of the point P=(x, y) -P = (x, -y) = (x, x+y) if q=p prime if q=2 m The point at infinite O P+O=P P+ (-P) = O for all points P • A point O exists which has the role of group identity 12
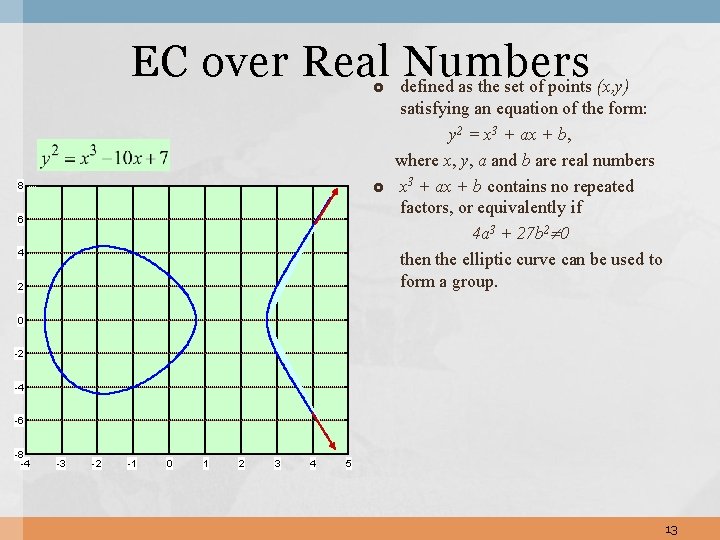
EC over Real defined Numbers as the set of points (x, y) 8 6 4 2 satisfying an equation of the form: y 2 = x 3 + ax + b, where x, y, a and b are real numbers x 3 + ax + b contains no repeated factors, or equivalently if 4 a 3 + 27 b 2 0 then the elliptic curve can be used to form a group. 0 -2 -4 -6 -8 -4 -3 -2 -1 0 1 2 3 4 5 13
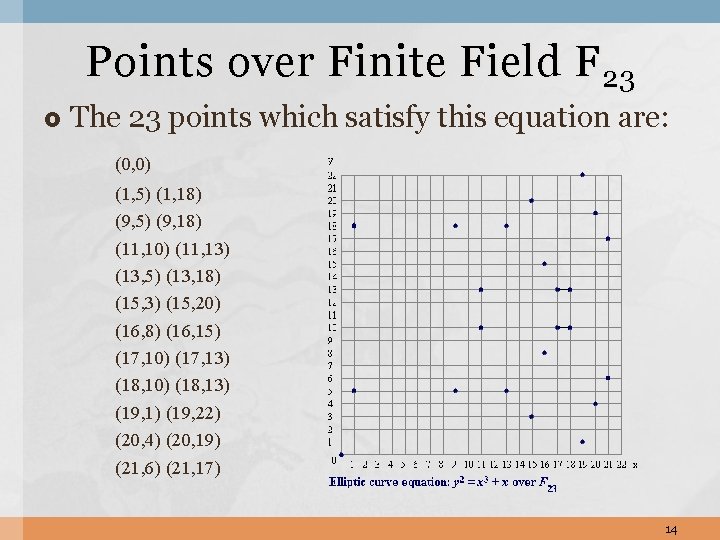
Points over Finite Field F 23 The 23 points which satisfy this equation are: (0, 0) (1, 5) (1, 18) (9, 5) (9, 18) (11, 10) (11, 13) (13, 5) (13, 18) (15, 3) (15, 20) (16, 8) (16, 15) (17, 10) (17, 13) (18, 10) (18, 13) (19, 1) (19, 22) (20, 4) (20, 19) (21, 6) (21, 17) 14
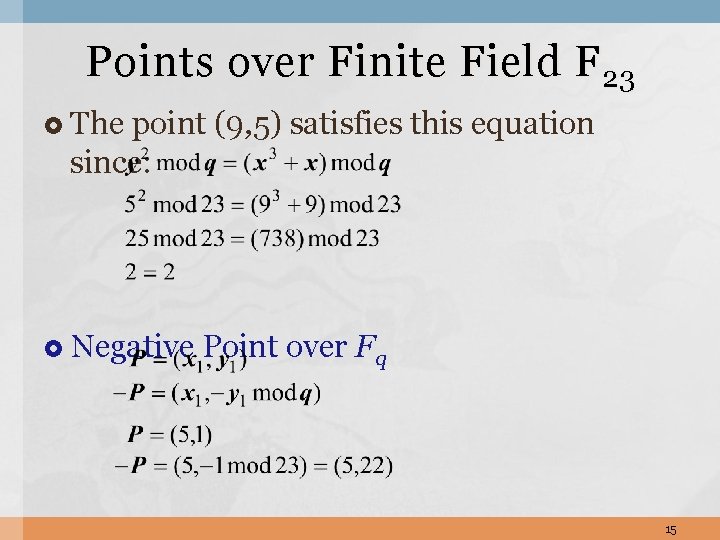
Points over Finite Field F 23 The point (9, 5) satisfies this equation since: Negative Point over Fq 15
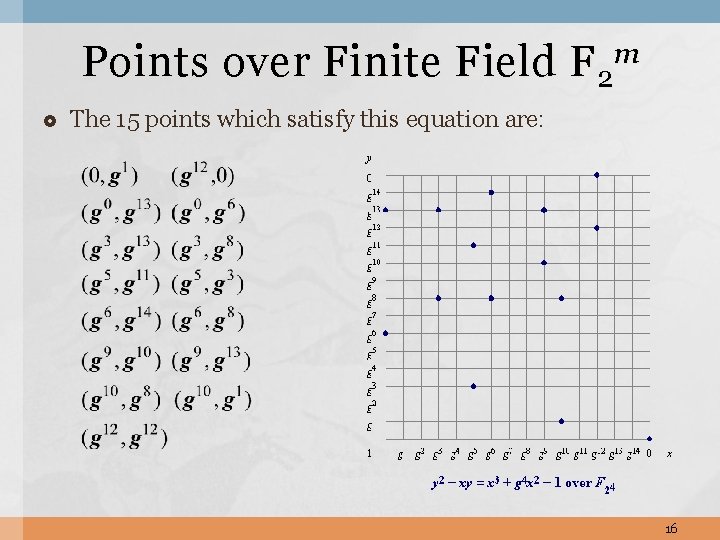
Points over Finite Field F 2 m The 15 points which satisfy this equation are: 16
![Operations on Elliptic Curves[1] Point Addition: R = P +Q • Draw the line Operations on Elliptic Curves[1] Point Addition: R = P +Q • Draw the line](http://slidetodoc.com/presentation_image_h2/e741210e274db194fbfa6d79148403e2/image-18.jpg)
Operations on Elliptic Curves[1] Point Addition: R = P +Q • Draw the line through P and Q. • Then this line intersects the elliptic curve in a third point. • Define R = P + Q as the reflection of this point in the x-axis. • P = (x 1 , y 1) and Q = (x 2 , y 2) , then R = P + Q = (x 3 , y 3) x 3 = 2 - x 1 - x 2 y 3 = (x 1 - x 3) -y 1 where = (y 2 - y 1) / (x 2 - x 1) 17
![Operations on Elliptic Curves[2] Point Doubling: R = 2 P • Draw the tangent Operations on Elliptic Curves[2] Point Doubling: R = 2 P • Draw the tangent](http://slidetodoc.com/presentation_image_h2/e741210e274db194fbfa6d79148403e2/image-19.jpg)
Operations on Elliptic Curves[2] Point Doubling: R = 2 P • Draw the tangent line to the curve at P. • Then this line intersects the curve in a second point. • Define R = 2 P as the reflection of this point in the x-axis. • P = (x 1 , y 1) then R = 2 P = (x 3 , y 3) x 3 = 2 - x 1 - x 2 y 3 = (x 1 - x 3) -y 1 where = (3 x 12 + a) / 2 y 1 18
![Operations on Elliptic Curves[3] Scalar Multiplication : k. P = P +. . + Operations on Elliptic Curves[3] Scalar Multiplication : k. P = P +. . +](http://slidetodoc.com/presentation_image_h2/e741210e274db194fbfa6d79148403e2/image-20.jpg)
Operations on Elliptic Curves[3] Scalar Multiplication : k. P = P +. . + P • For a nonnegative integer k and a point P, scalar multiplication k. P is defined as • k. P = (k-1)P + P for k > 0. • adding k-1 copies of P to itself • where k is a positive integer P is a point on an EC • 0 P = O, for k = 0, where O is the “point at infinity” which is the additive identity element. • (-n)P = n(-P) 19
Efficient Scalar Multiplication Algorithms Primary goal when implementing Methods • Reducing the number of operations • Minimizing the Hamming weight of the digit(multiplier) • • • Binary method Signed binary method M-ary method Modified m-ary method Frobenius method Window method Sliding window method NAF(non-adjacent form) method Signed m-ary windows method Montgomery method (binary case) 20
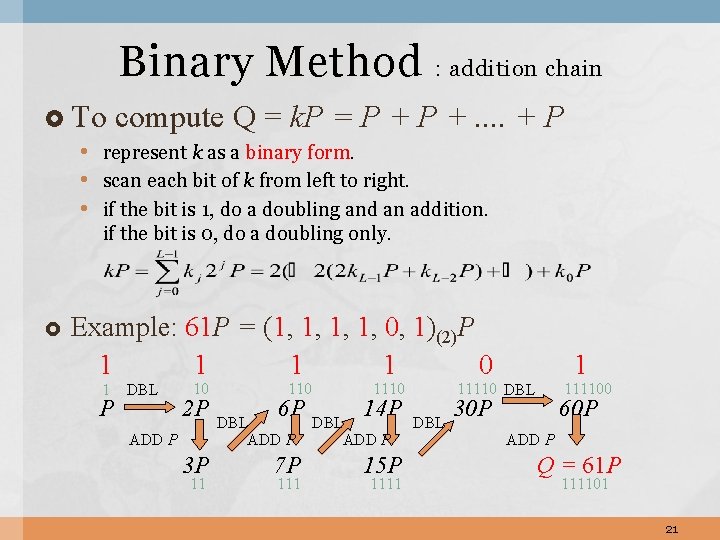
Binary Method : addition chain To compute Q = k. P = P +. . + P • represent k as a binary form. • scan each bit of k from left to right. • if the bit is 1, do a doubling and an addition. if the bit is 0, do a doubling only. Example: 61 P = (1, 1, 0, 1)(2)P 1 1 0 1 P DBL 10 2 P ADD P 3 P 11 110 6 P DBL ADD P 7 P 1110 14 P DBL ADD P 15 P 1111 1 11110 DBL 111100 30 P 60 P ADD P Q = 61 P 111101 21
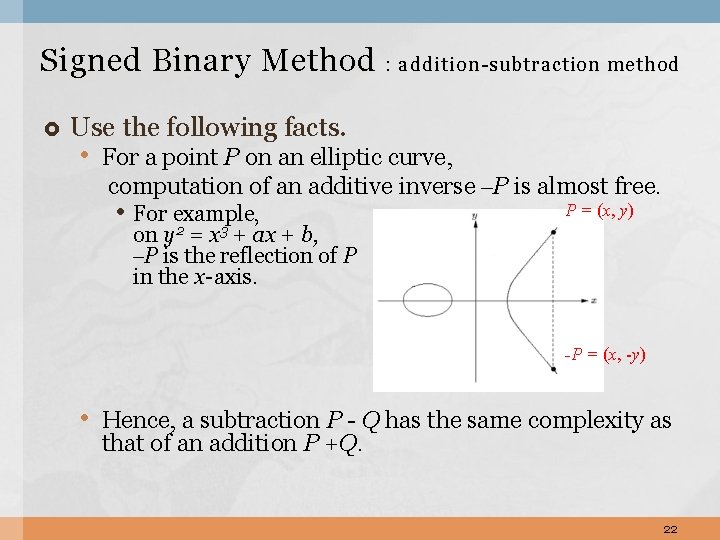
Signed Binary Method : addition-subtraction method Use the following facts. • For a point P on an elliptic curve, computation of an additive inverse –P is almost free. • For example, P = (x, y) on y 2 = x 3 + ax + b, –P is the reflection of P in the x-axis. -P = (x, -y) • Hence, a subtraction P - Q has the same complexity as that of an addition P +Q. 22
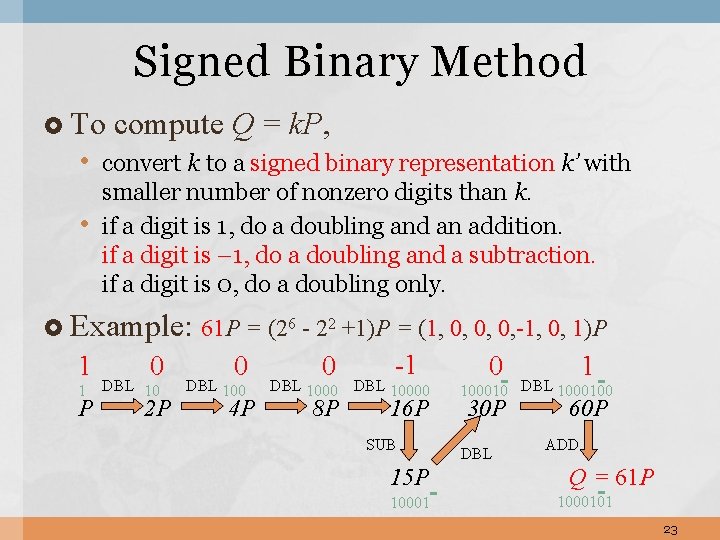
Signed Binary Method To compute Q = k. P, • convert k to a signed binary representation k’ with • smaller number of nonzero digits than k. if a digit is 1, do a doubling and an addition. if a digit is – 1, do a doubling and a subtraction. if a digit is 0, do a doubling only. Example: 61 P = (26 - 22 +1)P = (1, 0, 0, 0, -1, 0, 1)P 1 0 P 2 P 1 DBL 10 0 DBL 100 4 P 0 -1 8 P 16 P DBL 10000 SUB 15 P 10001 0 1 100010 DBL 1000100 30 P DBL 60 P ADD Q = 61 P 1000101 23
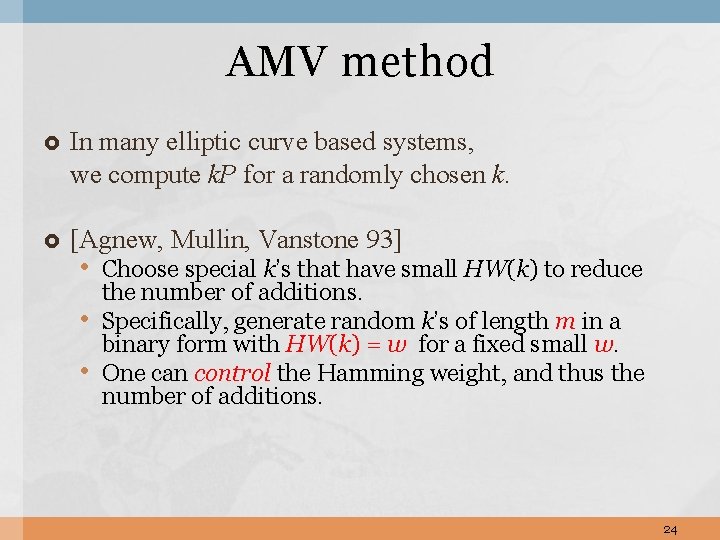
AMV method In many elliptic curve based systems, we compute k. P for a randomly chosen k. [Agnew, Mullin, Vanstone 93] • Choose special k’s that have small HW(k) to reduce • • the number of additions. Specifically, generate random k’s of length m in a binary form with HW(k) = w for a fixed small w. One can control the Hamming weight, and thus the number of additions. 24
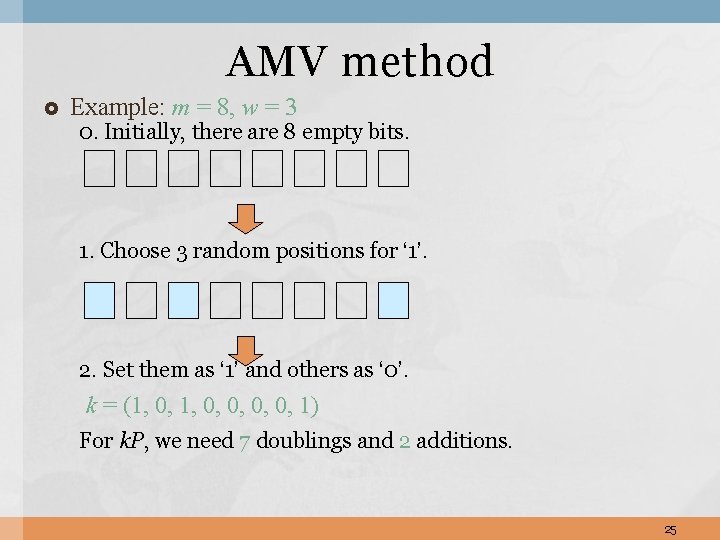
AMV method Example: m = 8, w = 3 0. Initially, there are 8 empty bits. 1. Choose 3 random positions for ‘ 1’. 2. Set them as ‘ 1’ and others as ‘ 0’. k = (1, 0, 0, 1) For k. P, we need 7 doublings and 2 additions. 25
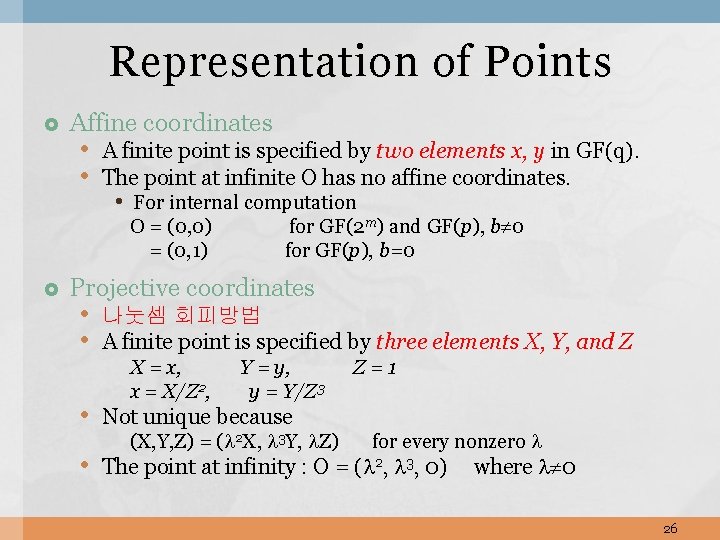
Representation of Points Affine coordinates • A finite point is specified by two elements x, y in GF(q). • The point at infinite O has no affine coordinates. • For internal computation O = (0, 0) = (0, 1) for GF(2 m) and GF(p), b 0 for GF(p), b=0 Projective coordinates • 나눗셈 회피방법 • A finite point is specified by three elements X, Y, and Z X = x, x = X/Z 2, Y = y, y = Y/Z 3 • Not unique because (X, Y, Z) = ( 2 X, 3 Y, Z) Z=1 for every nonzero • The point at infinity : O = ( 2, 3, 0) where 0 26
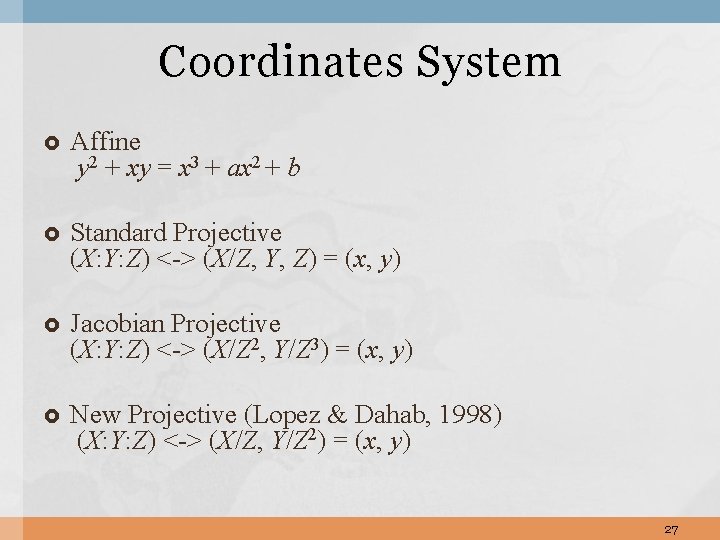
Coordinates System Affine y 2 + xy = x 3 + ax 2 + b Standard Projective (X: Y: Z) <-> (X/Z, Y, Z) = (x, y) Jacobian Projective (X: Y: Z) <-> (X/Z 2, Y/Z 3) = (x, y) New Projective (Lopez & Dahab, 1998) (X: Y: Z) <-> (X/Z, Y/Z 2) = (x, y) 27
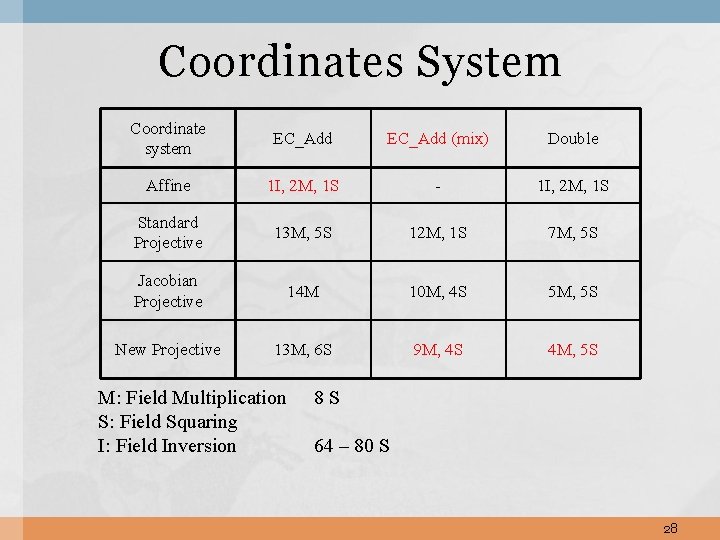
Coordinates System Coordinate system EC_Add (mix) Double Affine 1 I, 2 M, 1 S - 1 I, 2 M, 1 S Standard Projective 13 M, 5 S 12 M, 1 S 7 M, 5 S Jacobian Projective 14 M 10 M, 4 S 5 M, 5 S New Projective 13 M, 6 S 9 M, 4 S 4 M, 5 S M: Field Multiplication S: Field Squaring I: Field Inversion 8 S 64 – 80 S 28
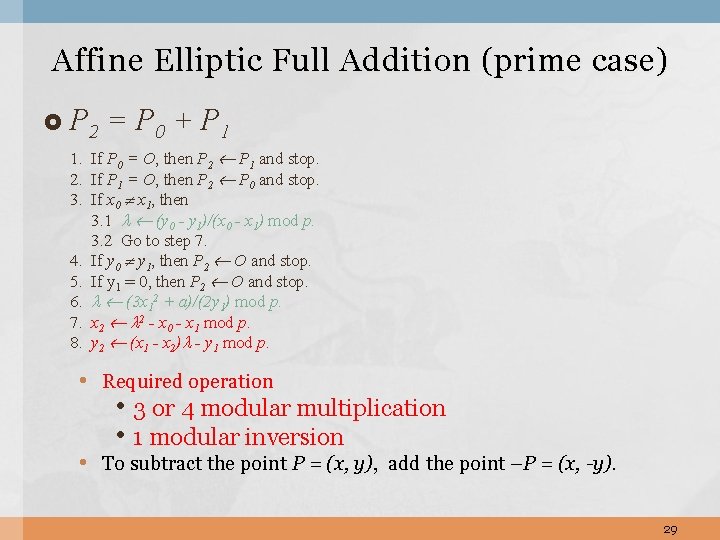
Affine Elliptic Full Addition (prime case) P 2 = P 0 + P 1 1. If P 0 = O, then P 2 P 1 and stop. 2. If P 1 = O, then P 2 P 0 and stop. 3. If x 0 x 1, then 3. 1 (y 0 - y 1)/(x 0 - x 1) mod p. 3. 2 Go to step 7. 4. If y 0 y 1, then P 2 O and stop. 5. If y 1 = 0, then P 2 O and stop. 6. (3 x 12 + a)/(2 y 1) mod p. 7. x 2 2 - x 0 - x 1 mod p. 8. y 2 (x 1 - x 2) - y 1 mod p. • Required operation • 3 or 4 modular multiplication • 1 modular inversion • To subtract the point P = (x, y), add the point –P = (x, -y). 29
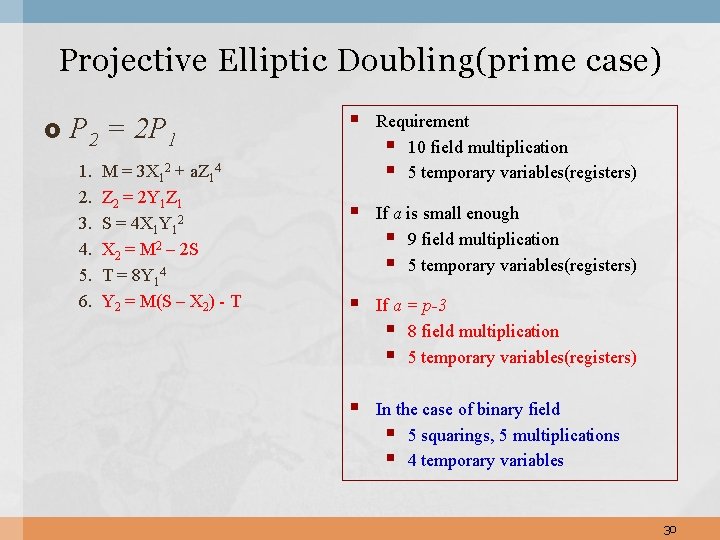
Projective Elliptic Doubling(prime case) P 2 = 2 P 1 1. 2. 3. 4. 5. 6. M = 3 X 12 + a. Z 14 Z 2 = 2 Y 1 Z 1 S = 4 X 1 Y 12 X 2 = M 2 – 2 S T = 8 Y 14 Y 2 = M(S – X 2) - T § Requirement § 10 field multiplication § 5 temporary variables(registers) § If a is small enough § 9 field multiplication § 5 temporary variables(registers) § If a = p-3 § 8 field multiplication § 5 temporary variables(registers) § In the case of binary field § 5 squarings, 5 multiplications § 4 temporary variables 30
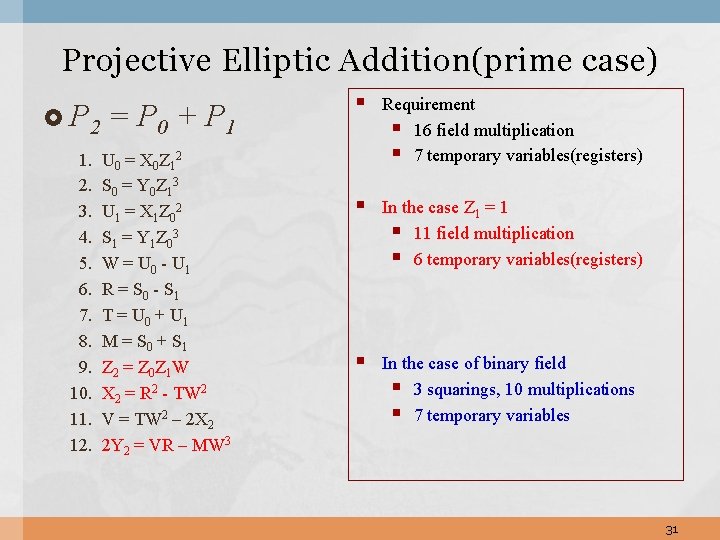
Projective Elliptic Addition(prime case) P 2 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. = P 0 + P 1 U 0 = X 0 Z 1 2 S 0 = Y 0 Z 1 3 U 1 = X 1 Z 0 2 S 1 = Y 1 Z 0 3 W = U 0 - U 1 R = S 0 - S 1 T = U 0 + U 1 M = S 0 + S 1 Z 2 = Z 0 Z 1 W X 2 = R 2 - TW 2 V = TW 2 – 2 X 2 2 Y 2 = VR – MW 3 § Requirement § 16 field multiplication § 7 temporary variables(registers) § In the case Z 1 = 1 § 11 field multiplication § 6 temporary variables(registers) § In the case of binary field § 3 squarings, 10 multiplications § 7 temporary variables 31
- Slides: 32