EEC484584 Computer Networks Lecture 7 Wenbing Zhao wenbingzgmail
EEC-484/584 Computer Networks Lecture 7 Wenbing Zhao wenbingz@gmail. com (Part of the slides are based on Drs. Kurose & Ross’s slides for their Computer Networking book)
Outline n Reminder: q n n No class next Monday (Columbus Day) Reliable data transfer Pipelining protocols UDP TCP (part I) 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
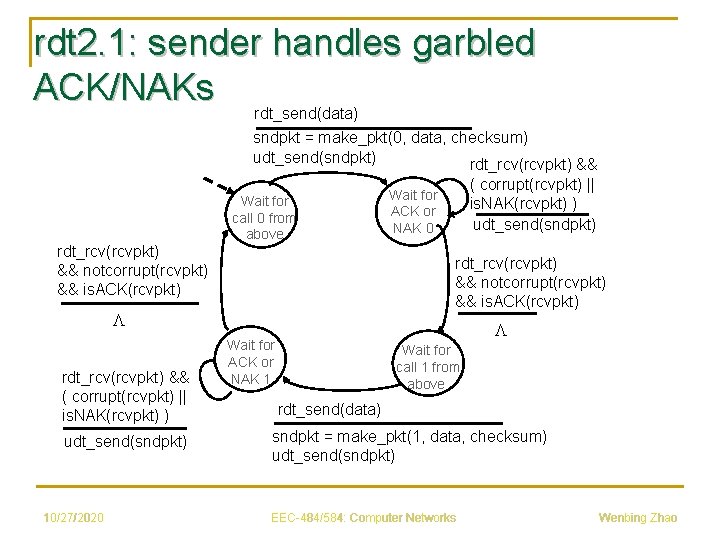
rdt 2. 1: sender handles garbled ACK/NAKs rdt_send(data) sndpkt = make_pkt(0, data, checksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt) Wait for call 0 from above rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt) L rdt_rcv(rcvpkt) && ( corrupt(rcvpkt) || is. NAK(rcvpkt) ) udt_send(sndpkt) 10/27/2020 ( corrupt(rcvpkt) || is. NAK(rcvpkt) ) udt_send(sndpkt) Wait for ACK or NAK 0 L Wait for ACK or NAK 1 Wait for call 1 from above rdt_send(data) sndpkt = make_pkt(1, data, checksum) udt_send(sndpkt) EEC-484/584: Computer Networks Wenbing Zhao
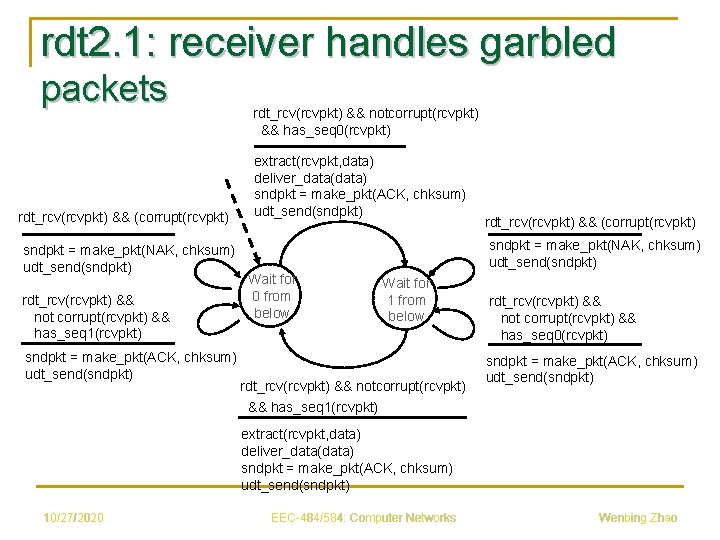
rdt 2. 1: receiver handles garbled packets rdt_rcv(rcvpkt) && (corrupt(rcvpkt) sndpkt = make_pkt(NAK, chksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && not corrupt(rcvpkt) && has_seq 1(rcvpkt) sndpkt = make_pkt(ACK, chksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && has_seq 0(rcvpkt) extract(rcvpkt, data) deliver_data(data) sndpkt = make_pkt(ACK, chksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && (corrupt(rcvpkt) sndpkt = make_pkt(NAK, chksum) udt_send(sndpkt) Wait for 0 from below Wait for 1 from below rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && has_seq 1(rcvpkt) rdt_rcv(rcvpkt) && not corrupt(rcvpkt) && has_seq 0(rcvpkt) sndpkt = make_pkt(ACK, chksum) udt_send(sndpkt) extract(rcvpkt, data) deliver_data(data) sndpkt = make_pkt(ACK, chksum) udt_send(sndpkt) 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
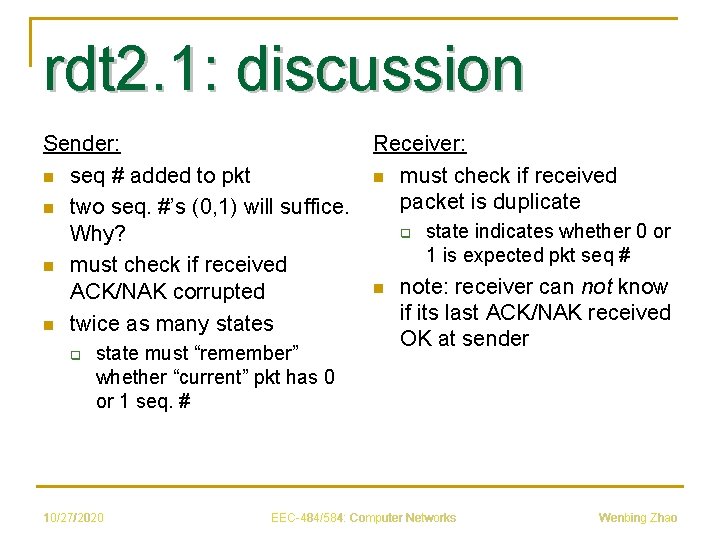
rdt 2. 1: discussion Sender: n seq # added to pkt n two seq. #’s (0, 1) will suffice. Why? n must check if received ACK/NAK corrupted n twice as many states q state must “remember” whether “current” pkt has 0 or 1 seq. # 10/27/2020 Receiver: n must check if received packet is duplicate q n state indicates whether 0 or 1 is expected pkt seq # note: receiver can not know if its last ACK/NAK received OK at sender EEC-484/584: Computer Networks Wenbing Zhao
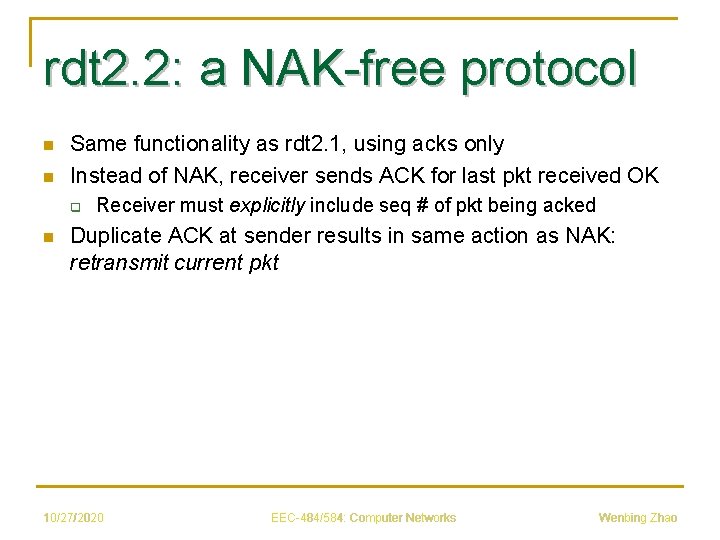
rdt 2. 2: a NAK-free protocol n n Same functionality as rdt 2. 1, using acks only Instead of NAK, receiver sends ACK for last pkt received OK q n Receiver must explicitly include seq # of pkt being acked Duplicate ACK at sender results in same action as NAK: retransmit current pkt 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
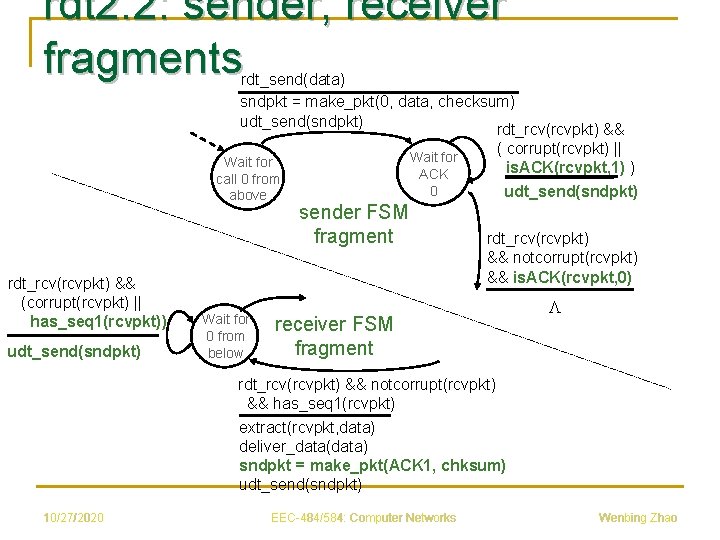
rdt 2. 2: sender, receiver fragments rdt_send(data) sndpkt = make_pkt(0, data, checksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && Wait for call 0 from above rdt_rcv(rcvpkt) && (corrupt(rcvpkt) || has_seq 1(rcvpkt)) udt_send(sndpkt) Wait for 0 from below Wait for ACK 0 sender FSM fragment ( corrupt(rcvpkt) || is. ACK(rcvpkt, 1) ) udt_send(sndpkt) rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt, 0) receiver FSM fragment L rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && has_seq 1(rcvpkt) extract(rcvpkt, data) deliver_data(data) sndpkt = make_pkt(ACK 1, chksum) udt_send(sndpkt) 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
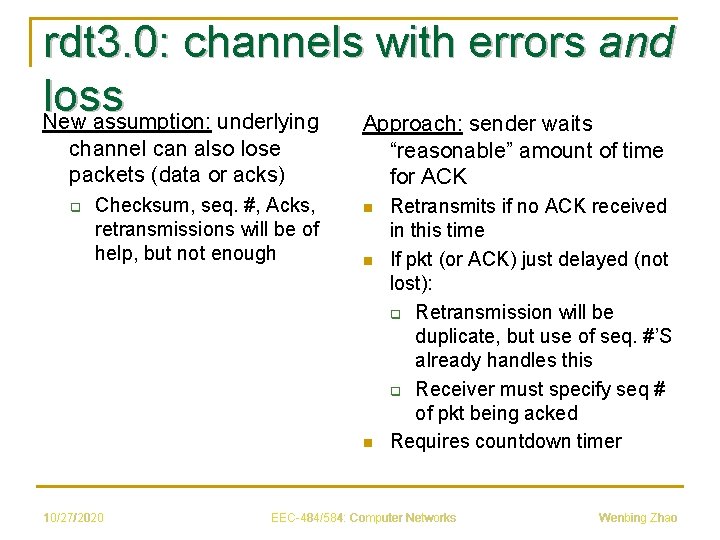
rdt 3. 0: channels with errors and loss New assumption: underlying Approach: sender waits channel can also lose packets (data or acks) q Checksum, seq. #, Acks, retransmissions will be of help, but not enough “reasonable” amount of time for ACK n n n 10/27/2020 Retransmits if no ACK received in this time If pkt (or ACK) just delayed (not lost): q Retransmission will be duplicate, but use of seq. #’S already handles this q Receiver must specify seq # of pkt being acked Requires countdown timer EEC-484/584: Computer Networks Wenbing Zhao
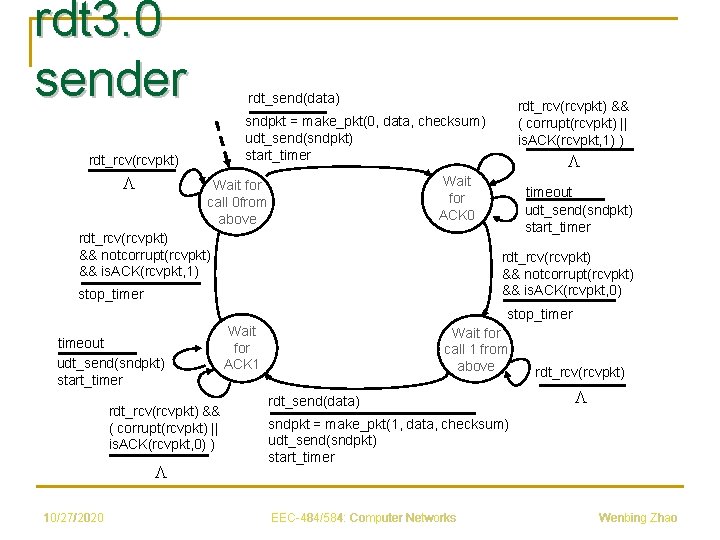
rdt 3. 0 sender rdt_send(data) sndpkt = make_pkt(0, data, checksum) udt_send(sndpkt) start_timer rdt_rcv(rcvpkt) L rdt_rcv(rcvpkt) && ( corrupt(rcvpkt) || is. ACK(rcvpkt, 1) ) L Wait for ACK 0 Wait for call 0 from above rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt, 1) timeout udt_send(sndpkt) start_timer rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt, 0) stop_timer timeout udt_send(sndpkt) start_timer rdt_rcv(rcvpkt) && ( corrupt(rcvpkt) || is. ACK(rcvpkt, 0) ) L 10/27/2020 Wait for ACK 1 Wait for call 1 from above rdt_send(data) rdt_rcv(rcvpkt) L sndpkt = make_pkt(1, data, checksum) udt_send(sndpkt) start_timer EEC-484/584: Computer Networks Wenbing Zhao
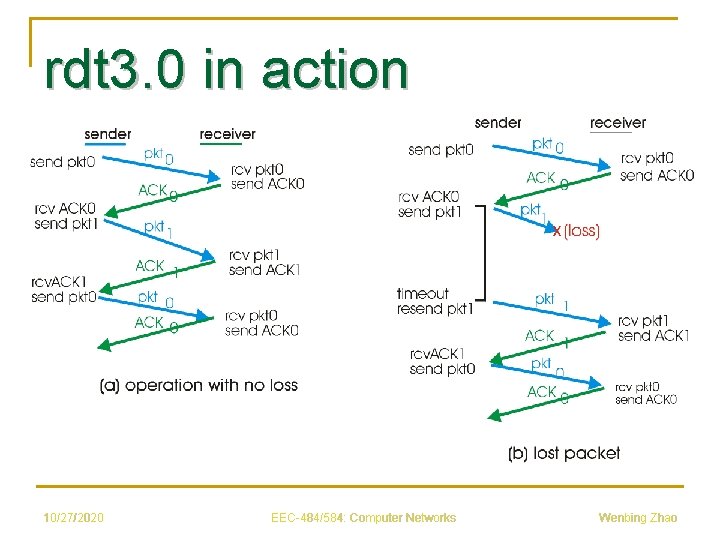
rdt 3. 0 in action 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
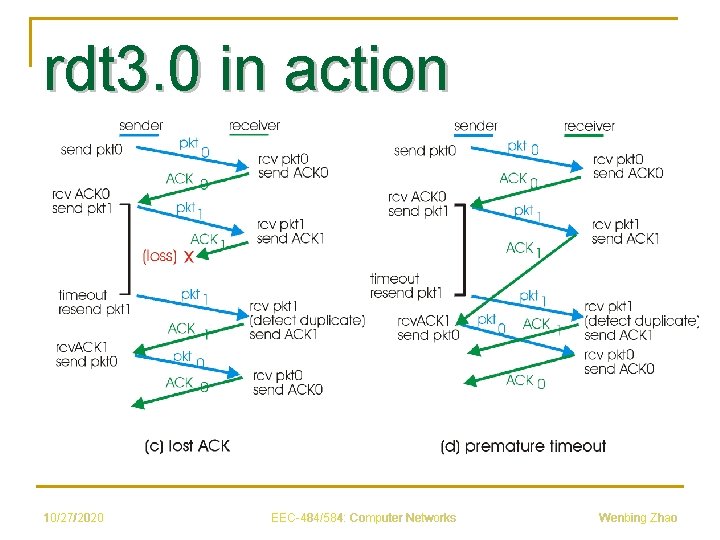
rdt 3. 0 in action 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
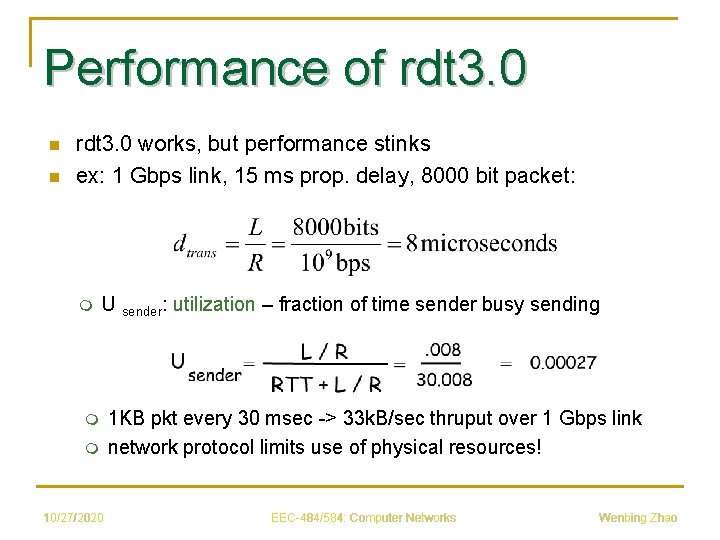
Performance of rdt 3. 0 n n rdt 3. 0 works, but performance stinks ex: 1 Gbps link, 15 ms prop. delay, 8000 bit packet: m U sender: utilization – fraction of time sender busy sending m m 10/27/2020 1 KB pkt every 30 msec -> 33 k. B/sec thruput over 1 Gbps link network protocol limits use of physical resources! EEC-484/584: Computer Networks Wenbing Zhao
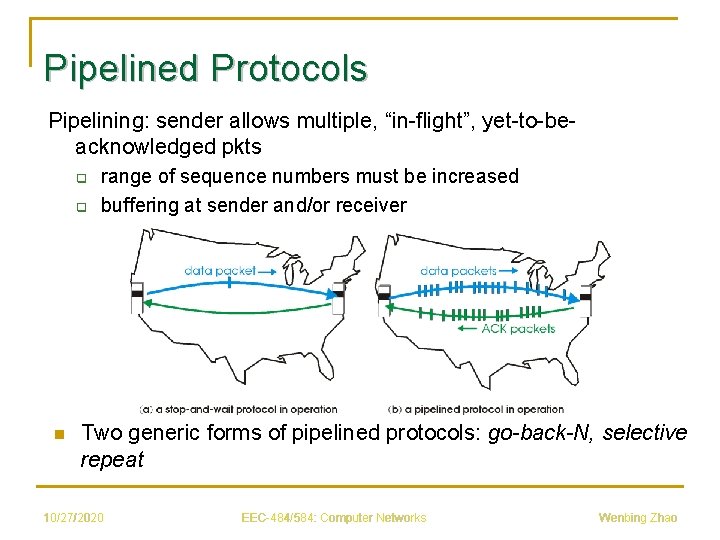
Pipelined Protocols Pipelining: sender allows multiple, “in-flight”, yet-to-beacknowledged pkts q q n range of sequence numbers must be increased buffering at sender and/or receiver Two generic forms of pipelined protocols: go-back-N, selective repeat 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
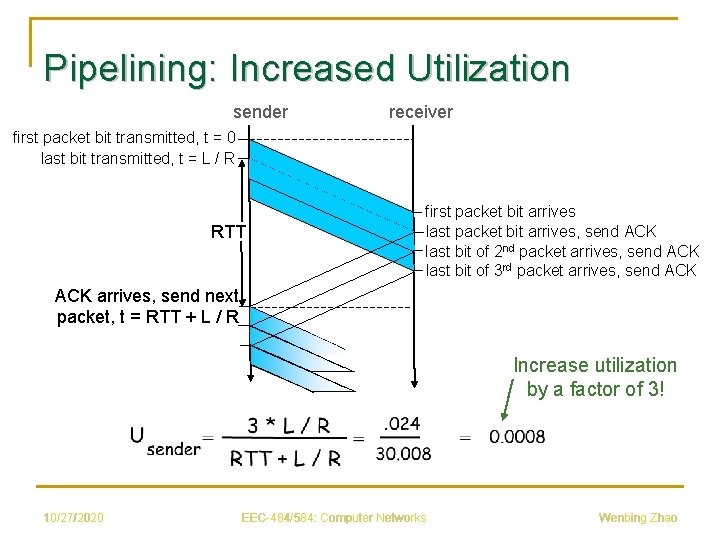
Pipelining: Increased Utilization sender receiver first packet bit transmitted, t = 0 last bit transmitted, t = L / R RTT first packet bit arrives last packet bit arrives, send ACK last bit of 2 nd packet arrives, send ACK last bit of 3 rd packet arrives, send ACK arrives, send next packet, t = RTT + L / R Increase utilization by a factor of 3! 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
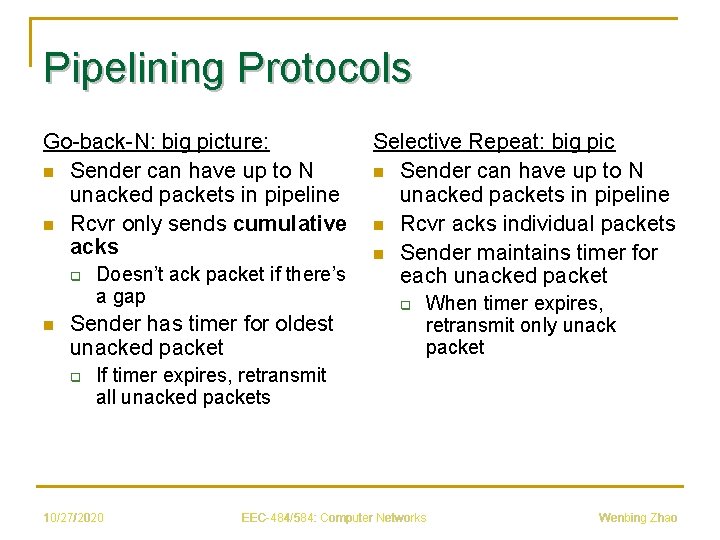
Pipelining Protocols Go-back-N: big picture: n Sender can have up to N unacked packets in pipeline n Rcvr only sends cumulative acks q n Doesn’t ack packet if there’s a gap Sender has timer for oldest unacked packet q Selective Repeat: big pic n Sender can have up to N unacked packets in pipeline n Rcvr acks individual packets n Sender maintains timer for each unacked packet q When timer expires, retransmit only unack packet If timer expires, retransmit all unacked packets 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
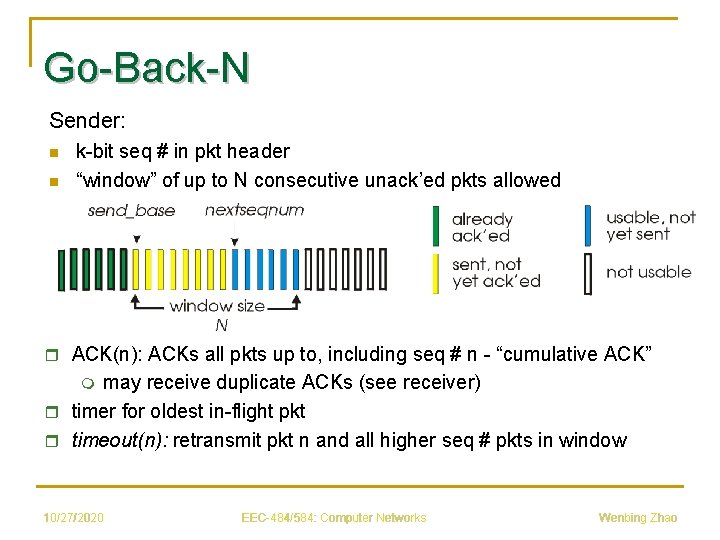
Go-Back-N Sender: n n k-bit seq # in pkt header “window” of up to N consecutive unack’ed pkts allowed r ACK(n): ACKs all pkts up to, including seq # n - “cumulative ACK” may receive duplicate ACKs (see receiver) r timer for oldest in-flight pkt r timeout(n): retransmit pkt n and all higher seq # pkts in window m 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
![GBN: Sender Extended FSM rdt_send(data) L base=1 nextseqnum=1 if (nextseqnum < base+N) { sndpkt[nextseqnum] GBN: Sender Extended FSM rdt_send(data) L base=1 nextseqnum=1 if (nextseqnum < base+N) { sndpkt[nextseqnum]](http://slidetodoc.com/presentation_image/14bb3adb94ffc26e08b07115d7e3bddb/image-17.jpg)
GBN: Sender Extended FSM rdt_send(data) L base=1 nextseqnum=1 if (nextseqnum < base+N) { sndpkt[nextseqnum] = make_pkt(nextseqnum, data, chksum) udt_send(sndpkt[nextseqnum]) if (base == nextseqnum) // start timer if first unacked pkt start_timer nextseqnum++ } else refuse_data(data) Wait rdt_rcv(rcvpkt) && corrupt(rcvpkt) timeout start_timer udt_send(sndpkt[base]) udt_send(sndpkt[base+1]) … udt_send(sndpkt[nextseqnum-1) rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) base = getacknum(rcvpkt)+1 If (base == nextseqnum) // no more unacked pkts stop_timer else start_timer 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
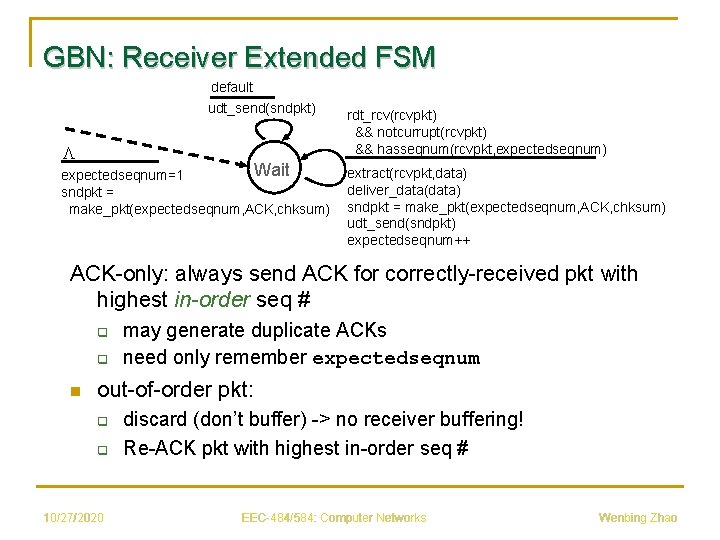
GBN: Receiver Extended FSM default udt_send(sndpkt) L Wait expectedseqnum=1 sndpkt = make_pkt(expectedseqnum, ACK, chksum) rdt_rcv(rcvpkt) && notcurrupt(rcvpkt) && hasseqnum(rcvpkt, expectedseqnum) extract(rcvpkt, data) deliver_data(data) sndpkt = make_pkt(expectedseqnum, ACK, chksum) udt_send(sndpkt) expectedseqnum++ ACK-only: always send ACK for correctly-received pkt with highest in-order seq # q q n may generate duplicate ACKs need only remember expectedseqnum out-of-order pkt: q q 10/27/2020 discard (don’t buffer) -> no receiver buffering! Re-ACK pkt with highest in-order seq # EEC-484/584: Computer Networks Wenbing Zhao
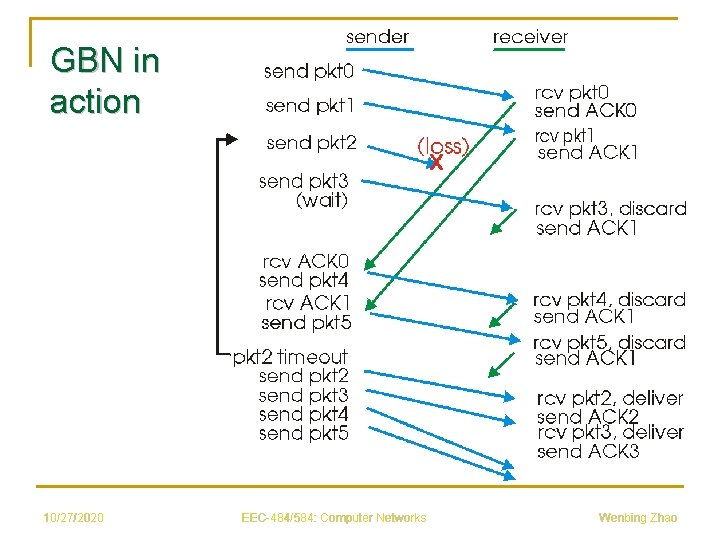
GBN in action 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
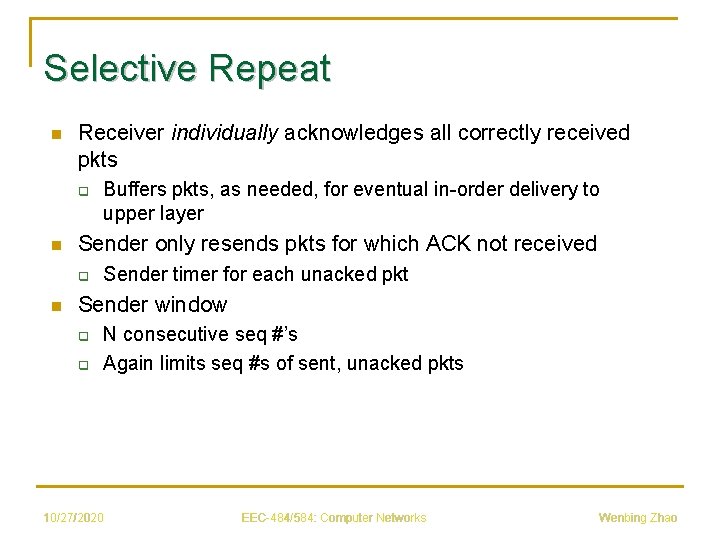
Selective Repeat n Receiver individually acknowledges all correctly received pkts q n Sender only resends pkts for which ACK not received q n Buffers pkts, as needed, for eventual in-order delivery to upper layer Sender timer for each unacked pkt Sender window q q N consecutive seq #’s Again limits seq #s of sent, unacked pkts 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
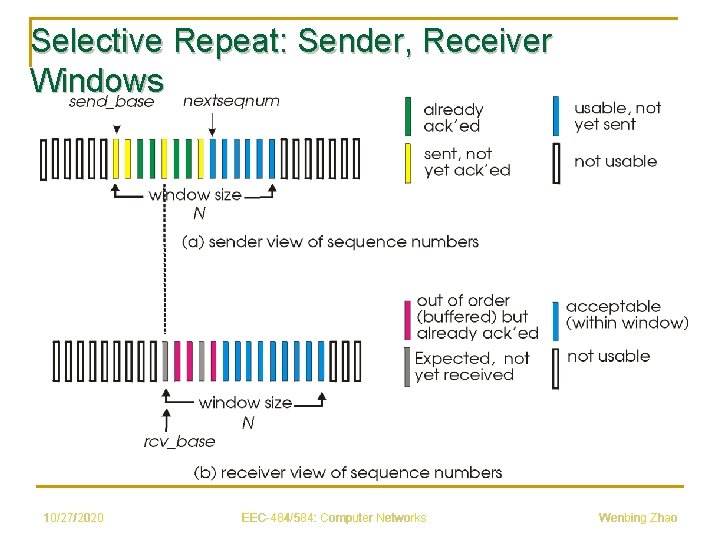
Selective Repeat: Sender, Receiver Windows 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
![Selective Repeat Receiver pkt n in [rcvbase, rcvbase+N-1] Sender data from above : n Selective Repeat Receiver pkt n in [rcvbase, rcvbase+N-1] Sender data from above : n](http://slidetodoc.com/presentation_image/14bb3adb94ffc26e08b07115d7e3bddb/image-22.jpg)
Selective Repeat Receiver pkt n in [rcvbase, rcvbase+N-1] Sender data from above : n if next available seq # in window, send pkt timeout(n): n r send ACK(n) r out-of-order: buffer r in-order: deliver (also deliver buffered, in-order pkts), advance window to next notyet-received pkt resend pkt n, restart timer ACK(n) in [sendbase, sendbase+N-1]: n n mark pkt n as received if n smallest un. ACKed pkt, advance window base to next un. ACKed seq # pkt n in [rcvbase-N, rcvbase-1] r ACK(n) otherwise: r ignore 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
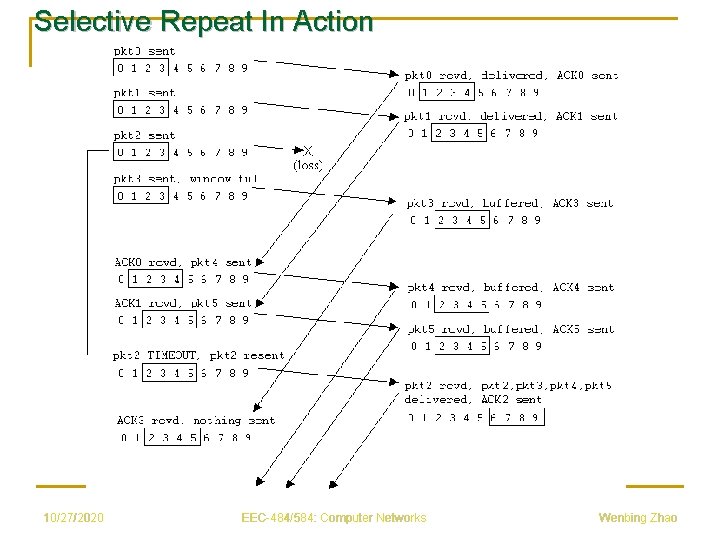
Selective Repeat In Action 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
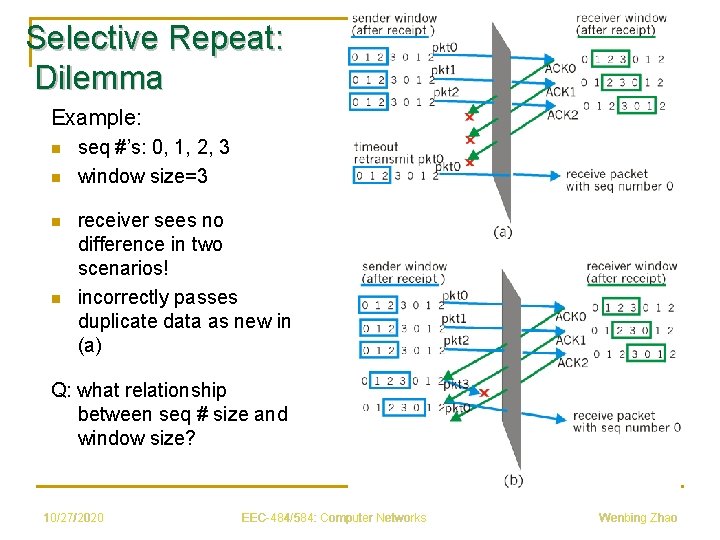
Selective Repeat: Dilemma Example: n n seq #’s: 0, 1, 2, 3 window size=3 receiver sees no difference in two scenarios! incorrectly passes duplicate data as new in (a) Q: what relationship between seq # size and window size? 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
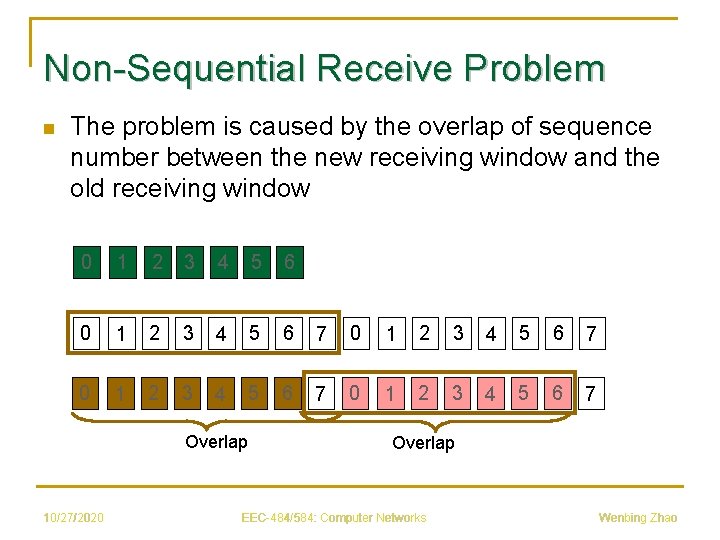
Non-Sequential Receive Problem n The problem is caused by the overlap of sequence number between the new receiving window and the old receiving window 0 1 2 3 4 5 6 7 0 1 2 3 4 5 6 7 Overlap 10/27/2020 Overlap EEC-484/584: Computer Networks Wenbing Zhao
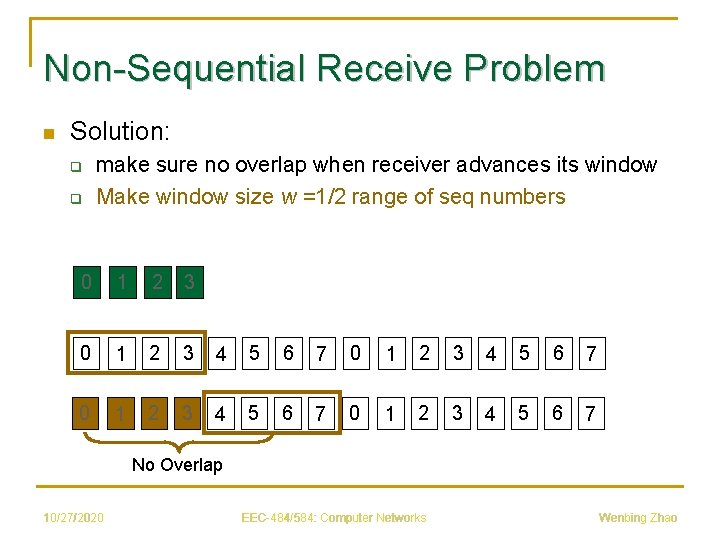
Non-Sequential Receive Problem n Solution: q q make sure no overlap when receiver advances its window Make window size w =1/2 range of seq numbers 0 1 2 3 4 5 6 7 0 1 2 3 4 5 6 7 No Overlap 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
UDP: User Datagram Protocol n n n “No frills, ” “bare bones” Internet transport protocol “Best effort” service, UDP segments may be: q Lost q Delivered out of order to app Connectionless: q No handshaking between UDP sender, receiver q Each UDP segment handled independently of others 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
Why is There a UDP? n n No connection establishment (which can add delay) Simple: no connection state at sender and receiver Small segment header No congestion control: UDP can blast away as fast as desired 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
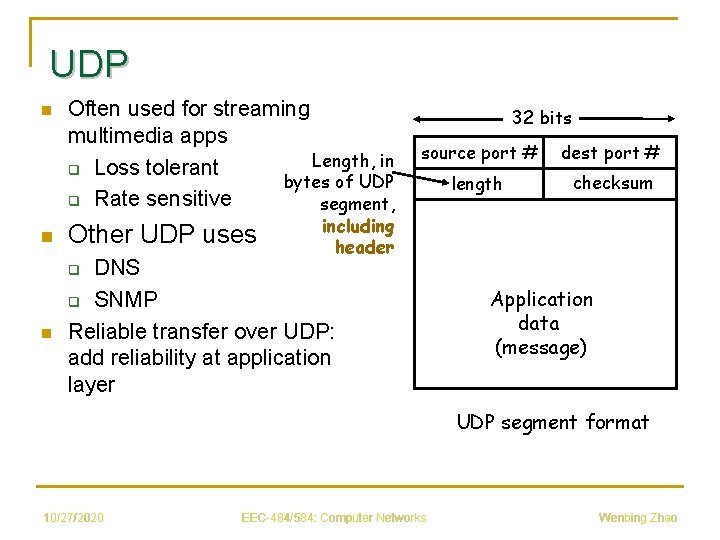
UDP n n Often used for streaming multimedia apps Length, in q Loss tolerant bytes of UDP q Rate sensitive segment, Other UDP uses 32 bits source port # dest port # length checksum including header DNS q SNMP Reliable transfer over UDP: add reliability at application layer q n Application data (message) UDP segment format 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
UDP Checksum Goal: detect “errors” (e. g. , flipped bits) in transmitted segment Receiver: Sender: n n n treat segment contents as sequence of 16 -bit integers checksum: addition (1’s complement sum) of segment contents sender puts checksum value into UDP checksum field 10/27/2020 n n compute checksum of received segment check if computed checksum equals checksum field value: q q EEC-484/584: Computer Networks NO - error detected YES - no error detected. But maybe errors nonetheless? Wenbing Zhao
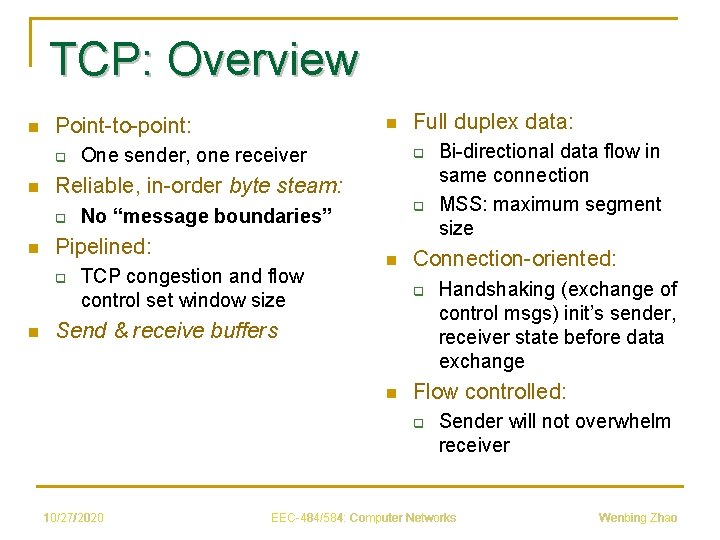
TCP: Overview n Point-to-point: q n q q No “message boundaries” Pipelined: q n One sender, one receiver Full duplex data: Reliable, in-order byte steam: q n n TCP congestion and flow control set window size n Connection-oriented: q Send & receive buffers n Handshaking (exchange of control msgs) init’s sender, receiver state before data exchange Flow controlled: q 10/27/2020 Bi-directional data flow in same connection MSS: maximum segment size Sender will not overwhelm receiver EEC-484/584: Computer Networks Wenbing Zhao
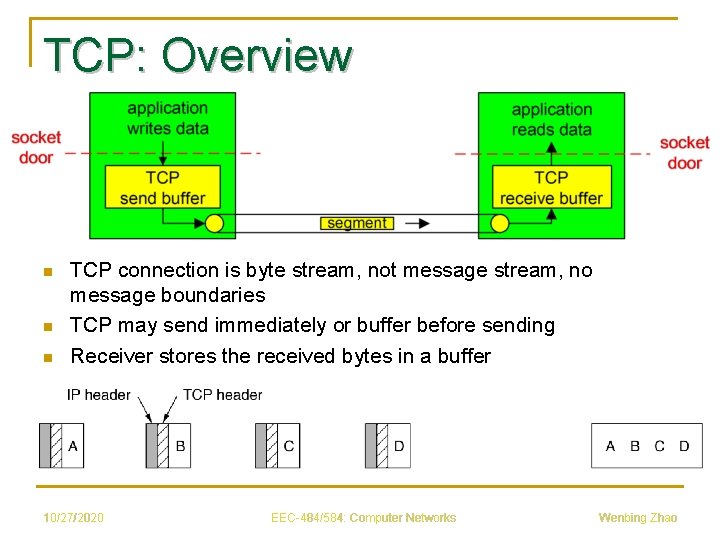
TCP: Overview n n n TCP connection is byte stream, not message stream, no message boundaries TCP may send immediately or buffer before sending Receiver stores the received bytes in a buffer 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
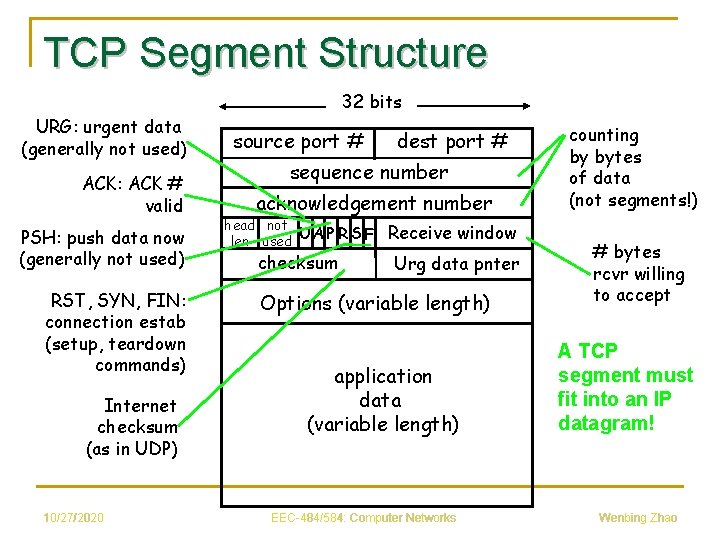
TCP Segment Structure 32 bits URG: urgent data (generally not used) ACK: ACK # valid PSH: push data now (generally not used) RST, SYN, FIN: connection estab (setup, teardown commands) Internet checksum (as in UDP) 10/27/2020 source port # dest port # sequence number acknowledgement number head not UA P R S F len used checksum Receive window Urg data pnter Options (variable length) application data (variable length) EEC-484/584: Computer Networks counting by bytes of data (not segments!) # bytes rcvr willing to accept A TCP segment must fit into an IP datagram! Wenbing Zhao
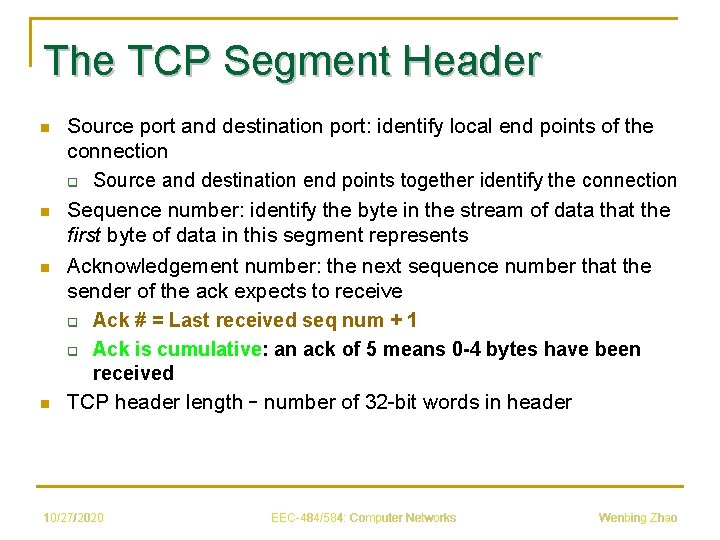
The TCP Segment Header n n Source port and destination port: identify local end points of the connection q Source and destination end points together identify the connection Sequence number: identify the byte in the stream of data that the first byte of data in this segment represents Acknowledgement number: the next sequence number that the sender of the ack expects to receive q Ack # = Last received seq num + 1 q Ack is cumulative: an ack of 5 means 0 -4 bytes have been received TCP header length – number of 32 -bit words in header 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
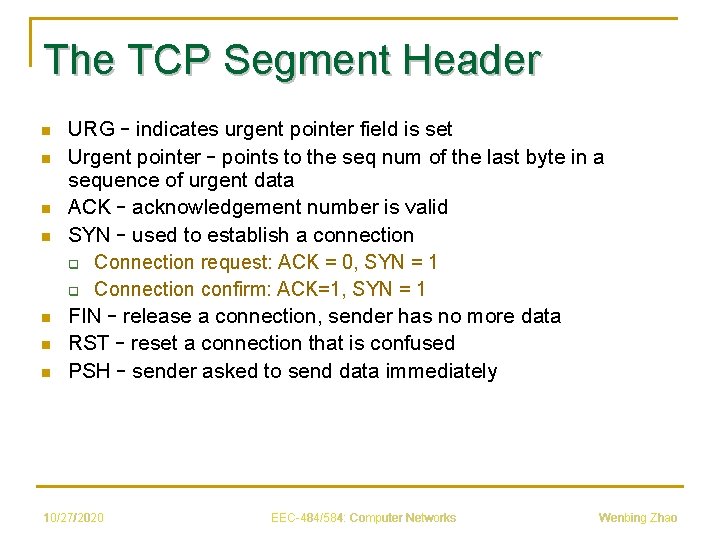
The TCP Segment Header n n n n URG – indicates urgent pointer field is set Urgent pointer – points to the seq num of the last byte in a sequence of urgent data ACK – acknowledgement number is valid SYN – used to establish a connection q Connection request: ACK = 0, SYN = 1 q Connection confirm: ACK=1, SYN = 1 FIN – release a connection, sender has no more data RST – reset a connection that is confused PSH – sender asked to send data immediately 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
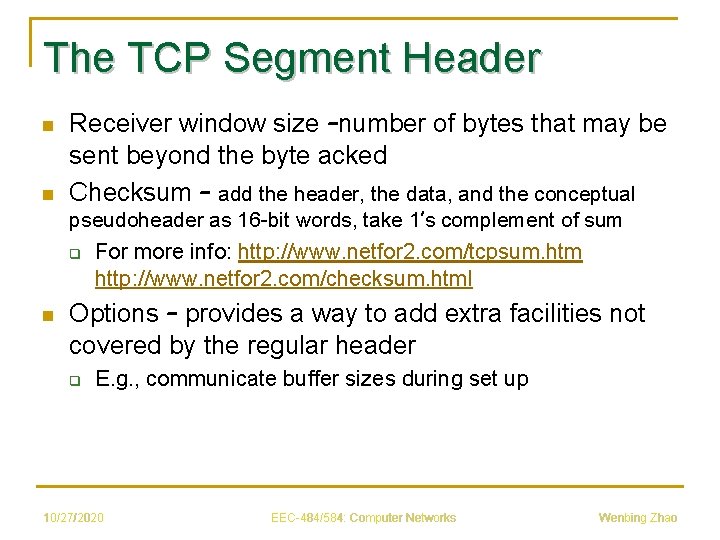
The TCP Segment Header n n Receiver window size –number of bytes that may be sent beyond the byte acked Checksum – add the header, the data, and the conceptual pseudoheader as 16 -bit words, take 1’s complement of sum q n For more info: http: //www. netfor 2. com/tcpsum. htm http: //www. netfor 2. com/checksum. html Options – provides a way to add extra facilities not covered by the regular header q E. g. , communicate buffer sizes during set up 10/27/2020 EEC-484/584: Computer Networks Wenbing Zhao
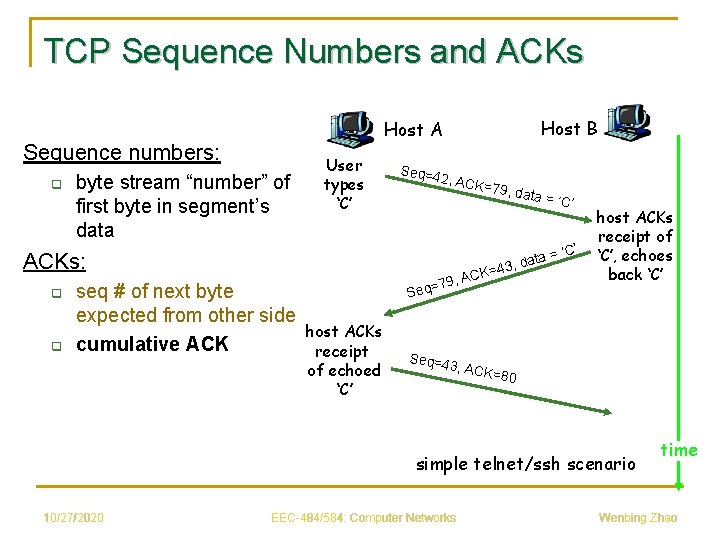
TCP Sequence Numbers and ACKs Sequence numbers: q byte stream “number” of first byte in segment’s data User types ‘C’ Seq=4 2, ACK = ACKs: q q Host B Host A seq # of next byte expected from other side cumulative ACK 79, da ta ata = d , 3 4 K= , AC q=79 Se host ACKs receipt of echoed ‘C’ = ‘C’ host ACKs receipt of ‘C’, echoes back ‘C’ Seq=4 3, ACK =80 simple telnet/ssh scenario 10/27/2020 EEC-484/584: Computer Networks time Wenbing Zhao
- Slides: 37