CSS 432 Shared Access Networks Textbook Ch 2
CSS 432 Shared Access Networks Textbook Ch 2. 6 - 2. 7 Professor: Munehiro Fukuda CSS 432 1
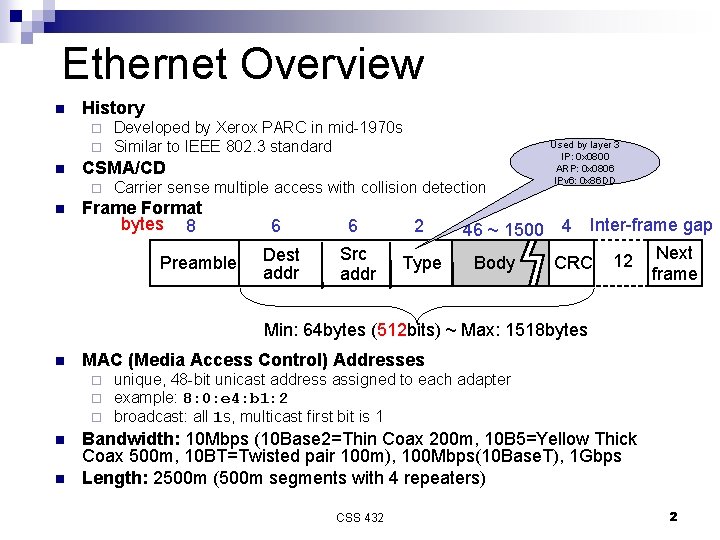
Ethernet Overview n History ¨ ¨ n CSMA/CD ¨ n Developed by Xerox PARC in mid-1970 s Similar to IEEE 802. 3 standard Carrier sense multiple access with collision detection Frame Format bytes 8 Preamble 6 Dest addr 6 2 Src addr Type 46 ~ 1500 Body Used by layer 3 IP: 0 x 0800 ARP: 0 x 0806 IPv 6: 0 x 86 DD 4 Inter-frame gap Next CRC 12 frame Min: 64 bytes (512 bits) ~ Max: 1518 bytes n MAC (Media Access Control) Addresses ¨ ¨ ¨ n n unique, 48 -bit unicast address assigned to each adapter example: 8: 0: e 4: b 1: 2 broadcast: all 1 s, multicast first bit is 1 Bandwidth: 10 Mbps (10 Base 2=Thin Coax 200 m, 10 B 5=Yellow Thick Coax 500 m, 10 BT=Twisted pair 100 m), 100 Mbps(10 Base. T), 1 Gbps Length: 2500 m (500 m segments with 4 repeaters) CSS 432 2
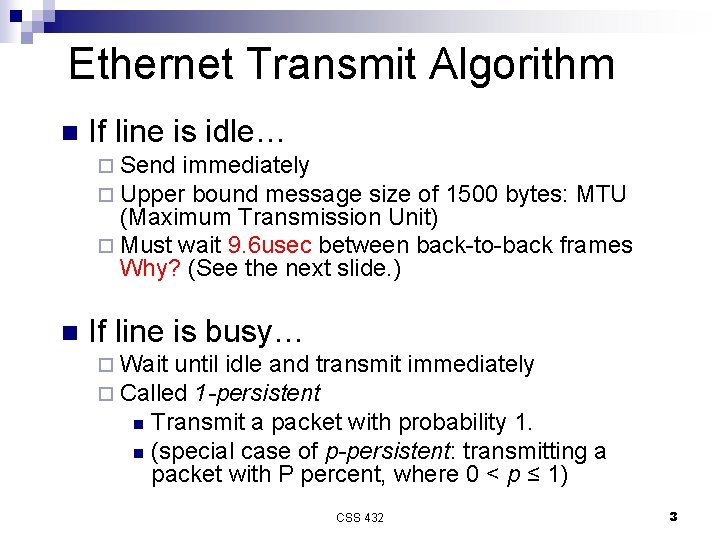
Ethernet Transmit Algorithm n If line is idle… ¨ Send immediately ¨ Upper bound message size of 1500 bytes: MTU (Maximum Transmission Unit) ¨ Must wait 9. 6 usec between back-to-back frames Why? (See the next slide. ) n If line is busy… ¨ Wait until idle and transmit ¨ Called 1 -persistent immediately Transmit a packet with probability 1. n (special case of p-persistent: transmitting a packet with P percent, where 0 < p ≤ 1) n CSS 432 3
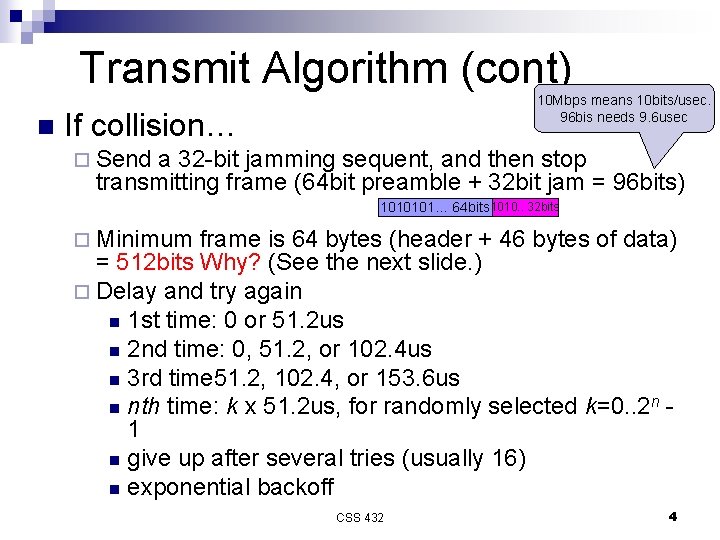
Transmit Algorithm (cont) n 10 Mbps means 10 bits/usec. 96 bis needs 9. 6 usec If collision… ¨ Send a 32 -bit jamming sequent, and then stop transmitting frame (64 bit preamble + 32 bit jam = 96 bits) 1010101… 64 bits 1010. . 32 bits ¨ Minimum frame is 64 bytes (header + 46 bytes of data) = 512 bits Why? (See the next slide. ) ¨ Delay and try again n 1 st time: 0 or 51. 2 us n 2 nd time: 0, 51. 2, or 102. 4 us n 3 rd time 51. 2, 102. 4, or 153. 6 us n nth time: k x 51. 2 us, for randomly selected k=0. . 2 n 1 n give up after several tries (usually 16) n exponential backoff CSS 432 4
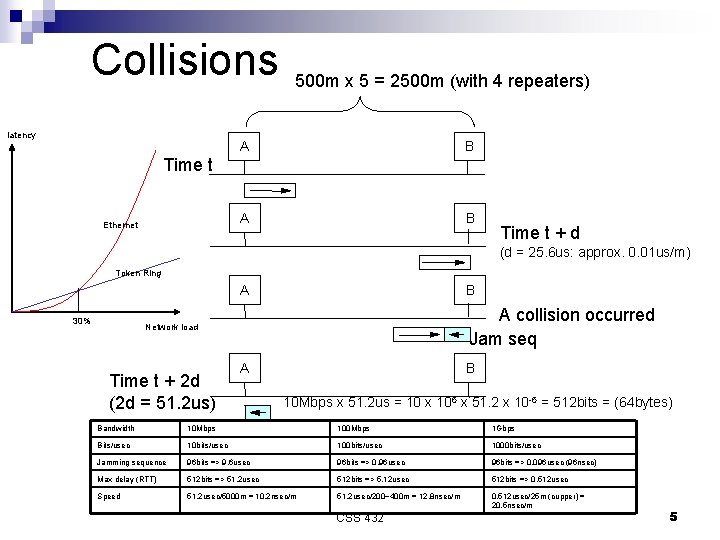
Collisions latency 500 m x 5 = 2500 m (with 4 repeaters) A B Time t Ethernet Time t + d (d = 25. 6 us: approx. 0. 01 us/m) Token Ring A 30% B A collision occurred Jam seq Network load Time t + 2 d (2 d = 51. 2 us) A B 10 Mbps x 51. 2 us = 10 x 106 x 51. 2 x 10 -6 = 512 bits = (64 bytes) Bandwidth 10 Mbps 100 Mbps 1 Gbps Bits/usec 10 bits/usec 1000 bits/usec Jamming sequence 96 bits => 9. 6 usec 96 bits => 0. 96 usec 96 bits => 0. 096 usec (96 nsec) Max delay (RTT) 512 bits => 51. 2 usec 512 bits => 5. 12 usec 512 bits => 0. 512 usec Speed 51. 2 usec/5000 m = 10. 2 nsec/m 51. 2 usec/200~400 m = 12. 8 nsec/m 0. 512 usec/25 m (cupper) = 20. 5 nsec/m CSS 432 5
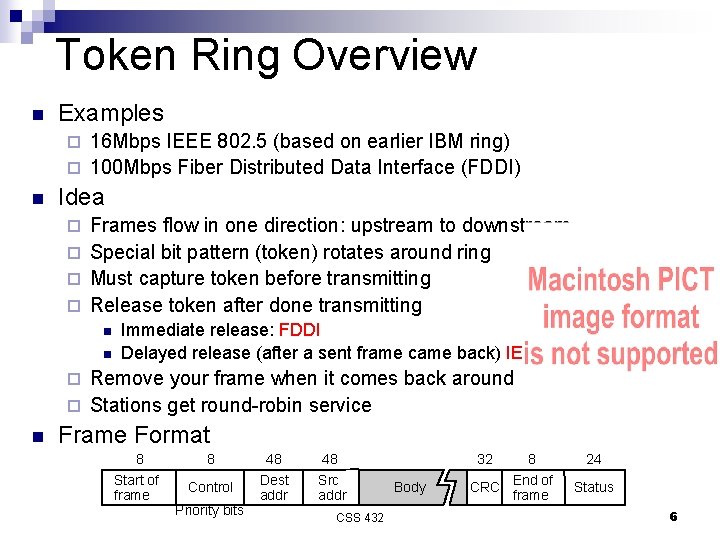
Token Ring Overview n Examples 16 Mbps IEEE 802. 5 (based on earlier IBM ring) ¨ 100 Mbps Fiber Distributed Data Interface (FDDI) ¨ n Idea Frames flow in one direction: upstream to downstream ¨ Special bit pattern (token) rotates around ring ¨ Must capture token before transmitting ¨ Release token after done transmitting ¨ n n Immediate release: FDDI Delayed release (after a sent frame came back) IEE 802. 5 Remove your frame when it comes back around ¨ Stations get round-robin service ¨ n Frame Format 8 8 48 48 Start of frame Control Dest addr Src addr Priority bits CSS 432 32 Body 8 CRC End of frame 24 Status 6
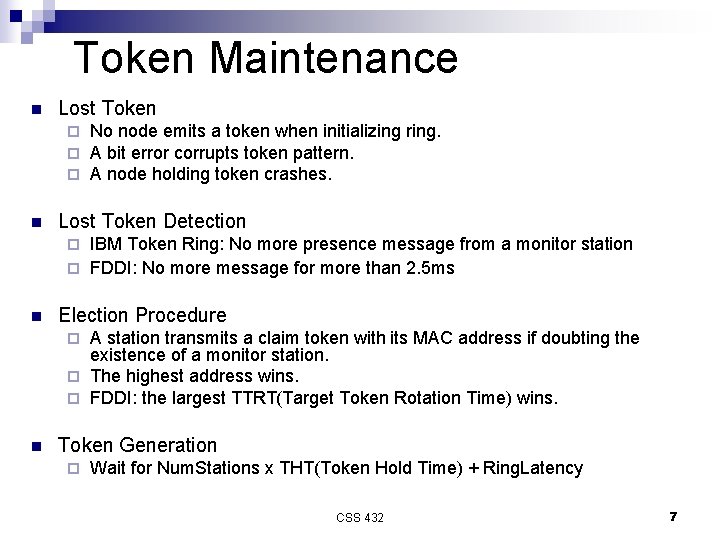
Token Maintenance n Lost Token ¨ ¨ ¨ n No node emits a token when initializing ring. A bit error corrupts token pattern. A node holding token crashes. Lost Token Detection IBM Token Ring: No more presence message from a monitor station ¨ FDDI: No more message for more than 2. 5 ms ¨ n Election Procedure A station transmits a claim token with its MAC address if doubting the existence of a monitor station. ¨ The highest address wins. ¨ FDDI: the largest TTRT(Target Token Rotation Time) wins. ¨ n Token Generation ¨ Wait for Num. Stations x THT(Token Hold Time) + Ring. Latency CSS 432 7
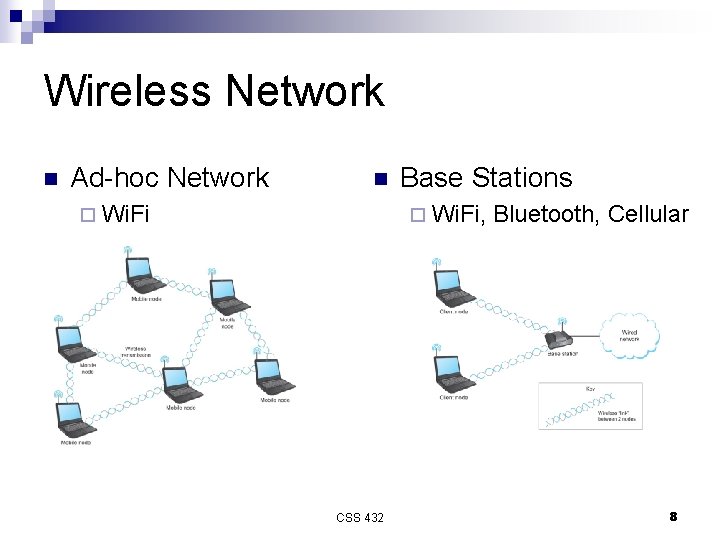
Wireless Network n Ad-hoc Network n ¨ Wi. Fi Base Stations ¨ Wi. Fi, CSS 432 Bluetooth, Cellular 8
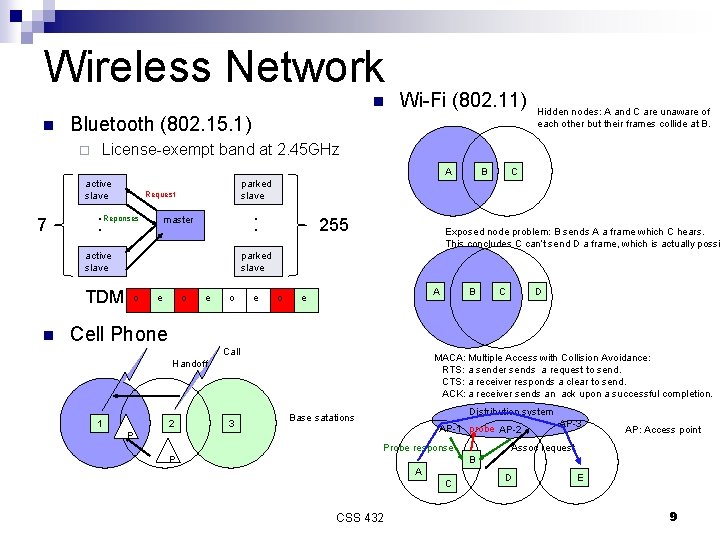
Wireless Network n n Wi-Fi (802. 11) Bluetooth (802. 15. 1) ¨ License-exempt band at 2. 45 GHz A active slave 7 Request : Reponses TDM B C parked slave : master active slave n Hidden nodes: A and C are unaware of each other but their frames collide at B. 255 Exposed node problem: B sends A a frame which C hears. This concludes C can’t send D a frame, which is actually possi parked slave o e o A e B C D Cell Phone Call MACA: Multiple Access with Collision Avoidance: RTS: a sender sends a request to send. CTS: a receiver responds a clear to send. ACK: a receiver sends an ack upon a successful completion. Handoff 1 2 3 Distribution system Base satations AP-1 probe AP-2 P Probe response P AP-3 AP: Access point Assoc request B A C CSS 432 D E 9
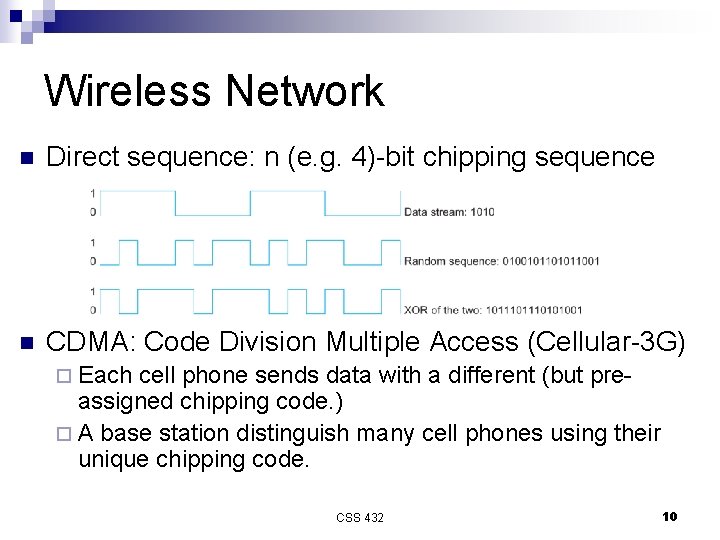
Wireless Network n Direct sequence: n (e. g. 4)-bit chipping sequence n CDMA: Code Division Multiple Access (Cellular-3 G) ¨ Each cell phone sends data with a different (but preassigned chipping code. ) ¨ A base station distinguish many cell phones using their unique chipping code. CSS 432 10
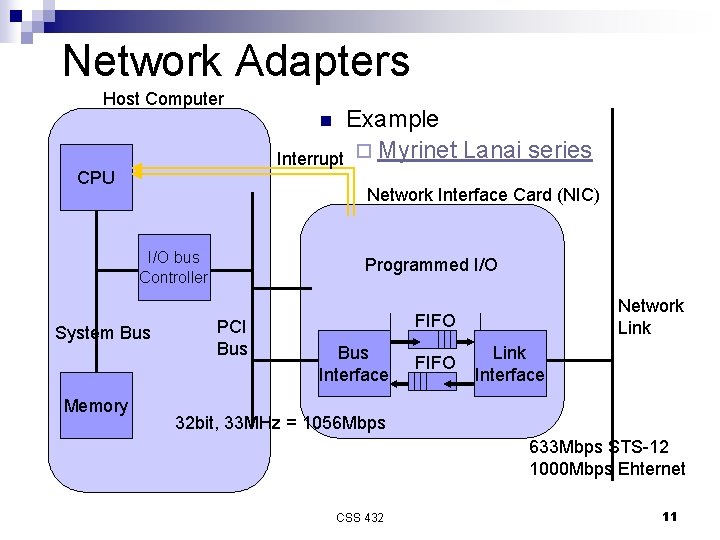
Network Adapters Host Computer Example Interrupt ¨ Myrinet Lanai series n CPU Network Interface Card (NIC) Network Processor I/Omemory Programmed I/O bus Controller System Bus Memory DMA PCI Bus Network Link FIFO Bus Interface FIFO Link Interface 32 bit, 33 MHz = 1056 Mbps 633 Mbps STS-12 1000 Mbps Ehternet CSS 432 11
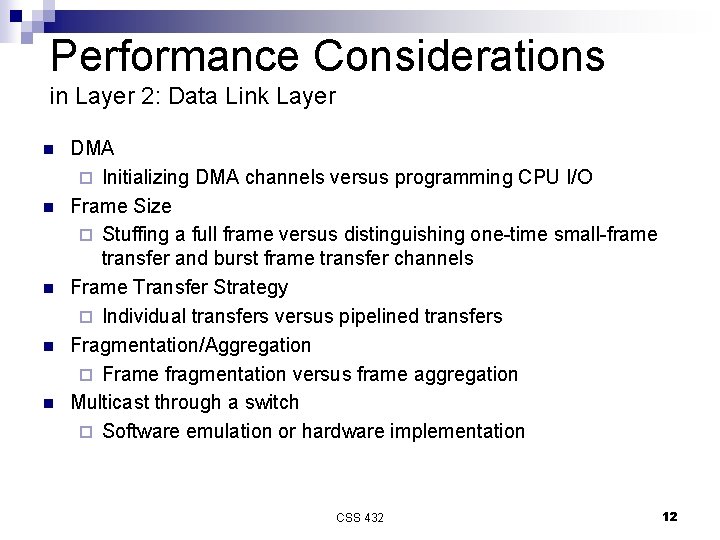
Performance Considerations in Layer 2: Data Link Layer n n n DMA ¨ Initializing DMA channels versus programming CPU I/O Frame Size ¨ Stuffing a full frame versus distinguishing one-time small-frame transfer and burst frame transfer channels Frame Transfer Strategy ¨ Individual transfers versus pipelined transfers Fragmentation/Aggregation ¨ Frame fragmentation versus frame aggregation Multicast through a switch ¨ Software emulation or hardware implementation CSS 432 12
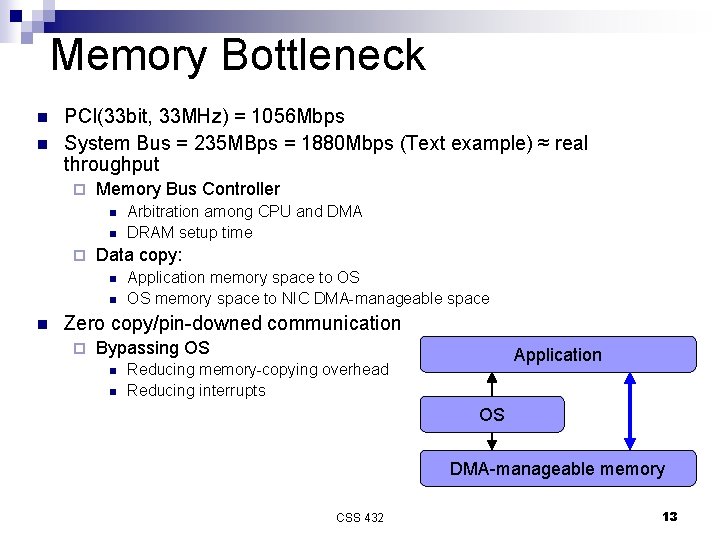
Memory Bottleneck n n PCI(33 bit, 33 MHz) = 1056 Mbps System Bus = 235 MBps = 1880 Mbps (Text example) ≈ real throughput ¨ Memory Bus Controller n n ¨ Data copy: n n n Arbitration among CPU and DMA DRAM setup time Application memory space to OS OS memory space to NIC DMA-manageable space Zero copy/pin-downed communication ¨ Bypassing OS n n Application Reducing memory-copying overhead Reducing interrupts OS DMA-manageable memory CSS 432 13
n Reviews ¨ Ethernet: k-persistent, exponential back off, and the relationship between the minimum frame size and collisions. ¨ Token ring network: immediate/delayed release, THT, TRT, and TTRT ¨ Network adapters: writev/readv and memory bottleneck n Exercises in Chapter 2 ¨ Ex. 42 (Ethernet) ¨ Ex. 46 (Ethernet) ¨ Ex. 53 (Wi-Fi) ¨ Ex. 54 (Wi-Fi) CSS 432 14
- Slides: 14