Cookies Privacy Good Cookie or Bad Cookie By
Cookies & Privacy Good Cookie or Bad Cookie? By Ravi Panandiker November 21, 2002 IST 497 E/Giles
Overview n Introduction n What is a Cookie? Basic Facts n Cookies & Paranoia n Getting Creative with Cookies n Scope of Cookies n Cookie Fixes n Cookie Taxonomy n Anatomy of a Cookie n Working with Cookies: Code & Demo n Cookie based Marketing n Cookies, Privacy & Legislation n Conclusion
What is a Cookie? n Short pieces of text generated during web activity and stored in the user’s machine for future reference n Instructions for reading and writing cookies are coded by website authors and executed by user browsers n Developed for user convenience to allow customization of sites without need for repeating preferences
Cookie Facts n Most Cookies store just 1 data value n A Cookie may not exceed 4 Kb in size n Browsers are preprogrammed to allow a total of 300 Cookies, after which automatic deletion based on expiry date and usage n Cookies have 3 key attributes: name, value and expiry date
Cookies & Paranoia n Why are Cookies notorious? n Most Cookie activity is transparent to the user n Most people do not understand what Cookies can and cannot do n People do not know how to protect themselves from Cookies n Valid reason: There are organizations out there using Cookies to track your activities (More later)
Darwinian Evolution: Getting Creative with Cookies n Basic cookie mechanism: Place a piece of information, retrieve it for customization on subsequent visits n Functions available: read, write, delete n Creative application 1: Initialize a cookie called counter to 1. Every time user visits, retrieve counter, increment by 1 and re-write. n Creative application 2: When a user visits, write system date/time in a cookie. Next visit get cookie for last visit. Overwrite with current date/time.
Cookie Scope: Cannot Do n Have automatic access to personal information like name, address, email n Read or write data to hard disk n Read or write information in cookies placed by other sites n Run programs on your computer
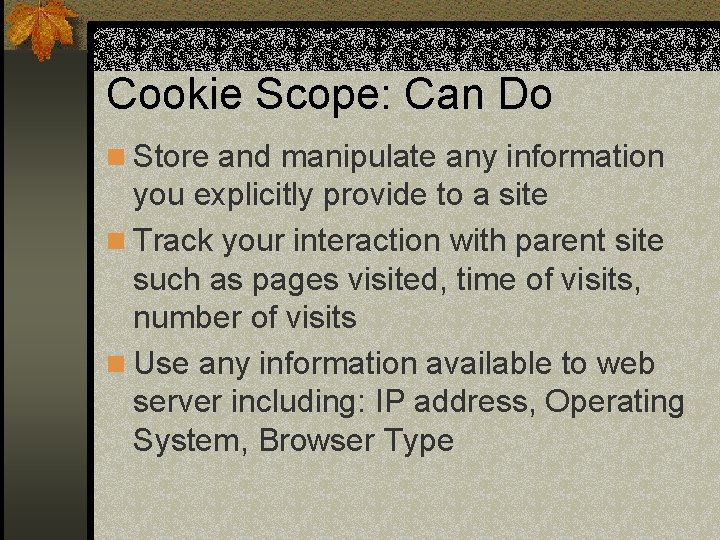
Cookie Scope: Can Do n Store and manipulate any information you explicitly provide to a site n Track your interaction with parent site such as pages visited, time of visits, number of visits n Use any information available to web server including: IP address, Operating System, Browser Type
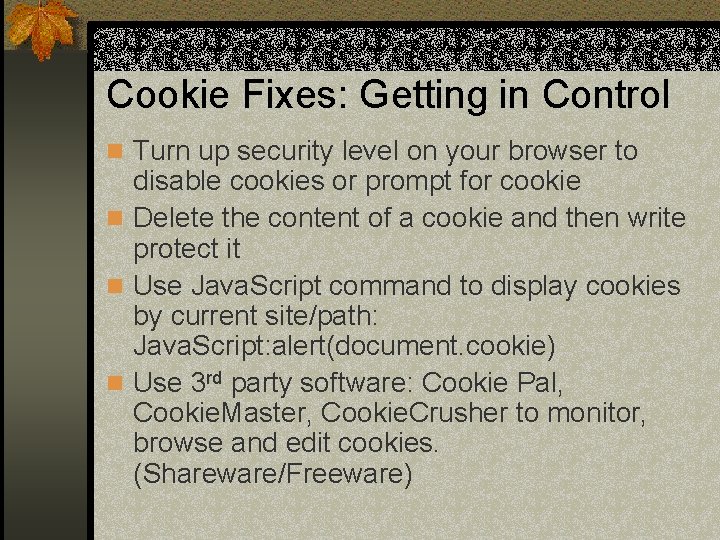
Cookie Fixes: Getting in Control n Turn up security level on your browser to disable cookies or prompt for cookie n Delete the content of a cookie and then write protect it n Use Java. Script command to display cookies by current site/path: Java. Script: alert(document. cookie) n Use 3 rd party software: Cookie Pal, Cookie. Master, Cookie. Crusher to monitor, browse and edit cookies. (Shareware/Freeware)
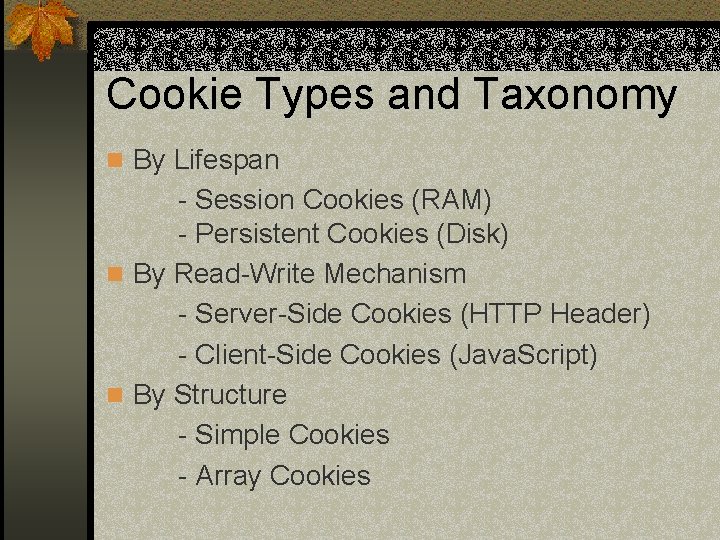
Cookie Types and Taxonomy n By Lifespan - Session Cookies (RAM) - Persistent Cookies (Disk) n By Read-Write Mechanism - Server-Side Cookies (HTTP Header) - Client-Side Cookies (Java. Script) n By Structure - Simple Cookies - Array Cookies
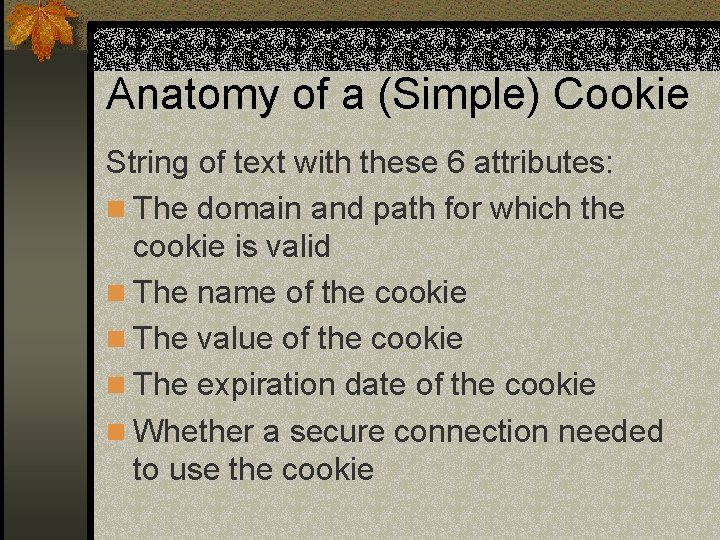
Anatomy of a (Simple) Cookie String of text with these 6 attributes: n The domain and path for which the cookie is valid n The name of the cookie n The value of the cookie n The expiration date of the cookie n Whether a secure connection needed to use the cookie
Working with Cookies n The domain and path are automatically handled by the browser, script author has no control n For a given domain and path, a script may create any number of cookies by specifying a name, value and expiry date n Each (simple) cookie is stored in a separate text file in Temporary Internet Folder, but tagged to a specific domain n Cookies are handled by the browser as an Object called document. cookie and read/written using object dot notation
Cookie Code n Cookies may be read/written by server-side or client-side code n Server-side Cookies are executed by the web server and instructions included in HTTP header for the page n Server-side Cookie languages: Perl/CGI, ASP/VBScript n Client-side scripts: Java. Script embedded in page HTML
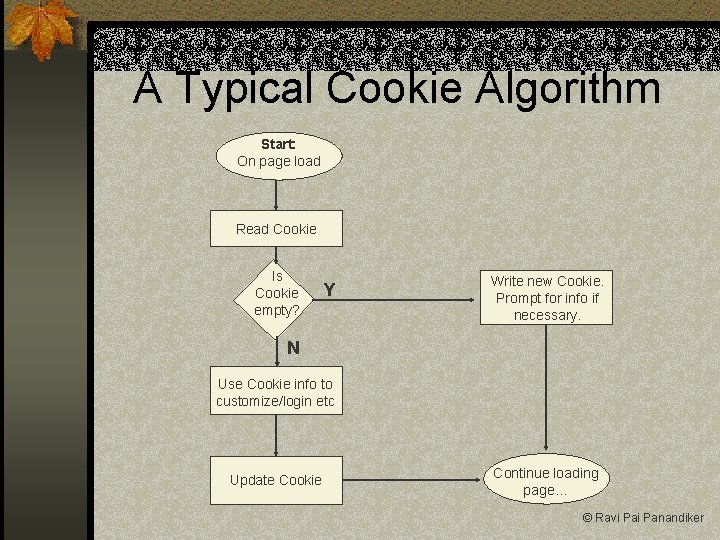
A Typical Cookie Algorithm Start: On page load Read Cookie Is Cookie empty? Y Write new Cookie. Prompt for info if necessary. N Use Cookie info to customize/login etc Update Cookie Continue loading page… © Ravi Panandiker
Cookie Code: Java. Script n Java. Script code uses 3 standard functions that are defined in the HTML <head> tag: get. Cookie(cookie. Name) set. Cookie(cookie. Name, value, exp. Date) del. Cookie(cookie. Name) n All Cookie manipulation is performed using these 3 functions and regular algorithmic constructs n All functions are automatically performed on the cookie object of that domain/path
Cookie Demo: Java. Script n http: //www. personal. psu. edu/ryp 105/cookies
Cookie Based Marketing n What is it? User customized online advertising and marketing system that uses Cookies and databases to create, maintain and utilize consumer profiles and monitor their activity
Cookie based Marketing n How does it work? n Companies like Double. Click. net, adserver. com and adflow. com have developed an innovative system (using standard technologies) for this purpose. n They tie up with popular websites like Yahoo, Amazon to create an extensive data and information sharing network
Cookie based Marketing n How it works contd. n Code developed by the company is placed on these web sites. n When you hit another such site, it sends data placed in your cookies to Double. Click and retrieves marketing information about you enabling them to customize ads etc n Result: One person may see ads for sports goods and another for baby clothes
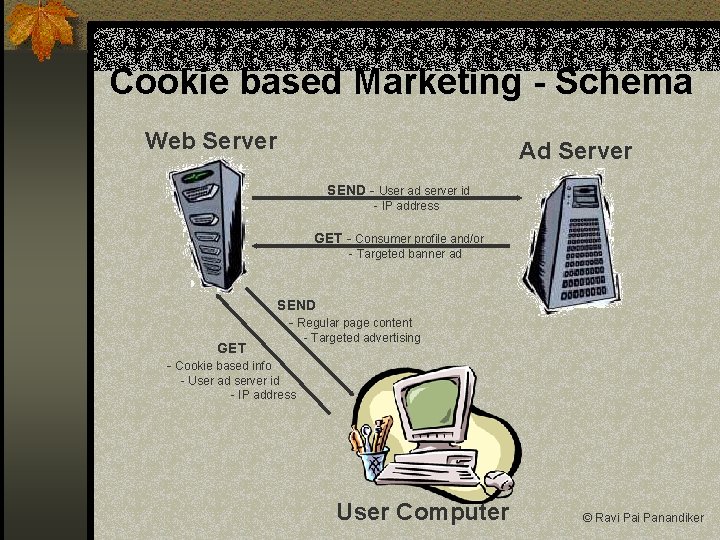
Cookie based Marketing - Schema Web Server Ad Server SEND - User ad server id - IP address GET - Consumer profile and/or - Targeted banner ad SEND - Regular page content GET - Targeted advertising - Cookie based info - User ad server id - IP address User Computer © Ravi Panandiker
Cookie Viruses? n On most platforms, Cookies are stored as text only files. To cause damage the Cookie must be an executable n On Windows, text files are non-executable and would open in a text editor if double clicked n In general, there are easier loopholes for a hacker in Active. X controls, Outlook Express etc n The threat from Cookies is not from what they can do to your computer but what information they may store and pass on
Cookies, Privacy and Legislation n Concern about misuse from Government agencies and non-profit organizations like Internet Engineering Task Force (IETF), Electronic Privacy Information Center (EPIC) n Study by govt. ’s Computer Incident Advisory Committee (CIAC) in 1998 n Bulletin concluded that there was more hype than hazard from Cookies. n Agreed that tracking people’s browsing habits makes many users uncomfortable
Cookies, Privacy & Legislation n New proposal put forward by IETF together n n with Netscape and Microsoft to modify the Cookie standard. Proposal is being backed by leading nonprofit organizations Proposal will limit persistence and make Cookie activity more transparent. Key aspect of proposal is to disallow 3 rd party server access to cookies. Would destroy Cookie based marketing.
Conclusion n Cookies were originally created as harmless pieces of text for user convenience n Along the way, some evil geniuses found a way to exploit them for business n Most studies conclude are not harmful to user: Would you rather see an ad for a product that’s relevant or one you’d never buy? n The paranoia arises from the invisible nature of cookie transactions and inadequate information about their ability.
Sources n www. cookiecentral. com n www. echo. com n www. wmlpulse. com n www. epic. org n www. ciac. org n www. howstuffworks. com n www. webmonkey. com n www. ozemail. com. au
Questions or Comments?
- Slides: 27